Cybercriminals go after folks’s private data throughout each sort of on-line platform, together with WhatsApp, Instagram, LinkedIn, Roblox, YouTube and Spotify, to not point out finance apps. No on-line account is off the desk. If one in every of your individual accounts falls sufferer, the primary precedence is to keep away from shedding your cool and act instantly – the quicker you progress, the extra of the attacker’s work you possibly can interrupt.
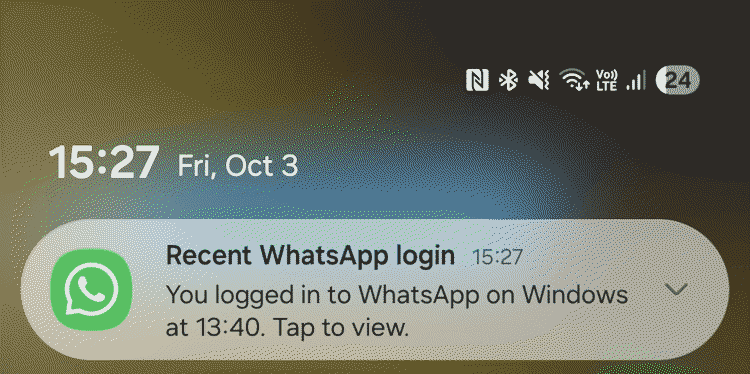
The attacker’s first transfer after gaining entry could possibly be to make that entry (close to)-permanent, together with by altering the restoration electronic mail tackle, including their very own backup codes or organising silent electronic mail forwarding guidelines to allow them to monitor your account even after you’ve got modified your password.
Listed here are a number of sensible steps to take whereas there’s usually nonetheless an opportunity to undo the harm. Importantly, don’t be concerned if you happen to discover it unattainable to get by means of all of the steps within the 15-minute sequence outlined beneath – this framing is extra of a immediate to maneuver quick, not a tough deadline!
Each minute counts
Cease the harm (minutes 0–2)
Test whether or not you continue to have entry to the account and, if you happen to can, think about how the breach most likely occurred.
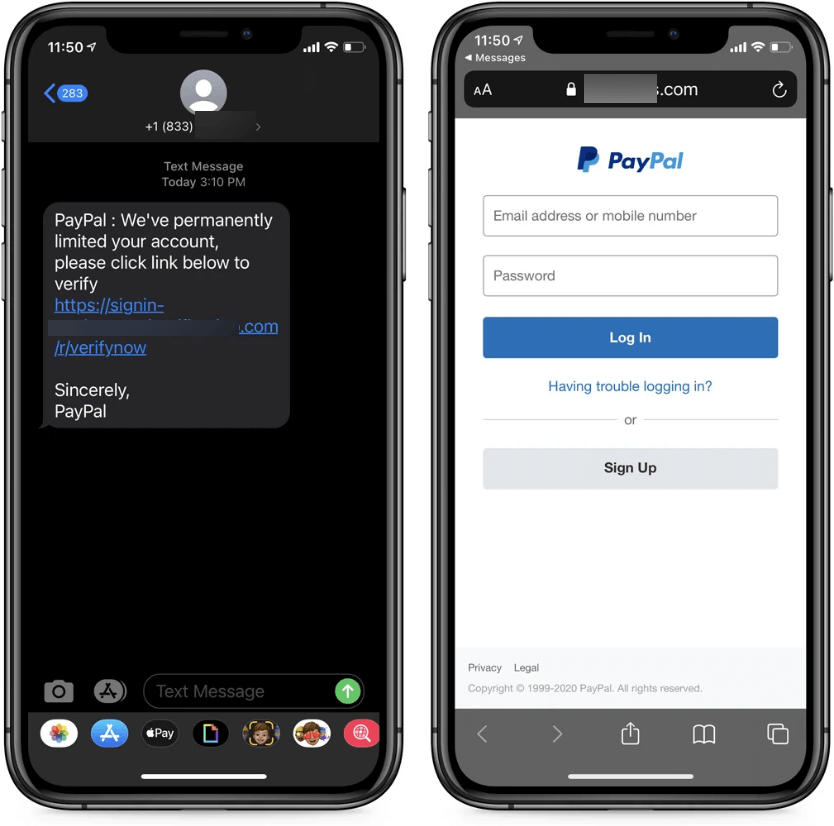
In the event you suspect you will have fallen sufferer to a phishing incident however nonetheless have entry to your account, go on to safe it in step with the steerage beneath. Ideally, use a tool aside from the one the place you first observed one thing was fallacious.
In the event you can not entry the account in any respect, go to the platform’s assist pages and begin the account restoration course of. Do not waste time attempting to log in again and again. If monetary accounts are concerned, name your financial institution or bank card supplier and ask them particularly to dam transactions and flag the account for monitoring.
In the event you suspect malware is concerned – say, you’ve put in software program from sketchy corners of the web or downloaded a suspicious electronic mail attachment – disconnect the gadget from the web. An lively malware compromise could possibly be exfiltrating information or speaking with an attacker in actual time, so that you need to cease that.
In any case, if in case you have up-to-date safety software program on the gadget, provoke a full scan. Do not anticipate it to finish, nonetheless – begin it operating and transfer to the subsequent steps, from a distinct gadget. In the event you don’t have any safety software program and stay on-line, ESET’s on-line scanner can assist. In the meantime, ESET’s hyperlink checker can flag any particular malicious URLs immediately.
Importantly, do not delete something but. On-line companies might ask for suspicious messages and different potential proof in the course of the reporting and account restoration course of.
Safe entry (minutes 3–6)
If the incident hit your electronic mail account, take note of electronic mail forwarding guidelines, which attackers usually configure silently in order that copies of incoming emails attain them even after you’ve got regained management. Most electronic mail shoppers checklist lively forwarding guidelines in settings – verify them and take away something you did not arrange your self.
Test additionally the account’s restoration settings – the backup electronic mail tackle, restoration cellphone quantity and backup codes. Change the password, from a tool you are assured is clear. The password must be sturdy and distinctive – not a variation of one thing you’ve got used earlier than or some place else.
In the event you can, go on to allow two-factor authentication (2FA) even when the service doesn’t immediate you to take action. Within the emergency stage, SMS codes ought to do the job however over the long run an authenticator app, resembling Google Authenticator or Microsoft Authenticator, is a safer alternative. {Hardware} safety keys are stronger nonetheless, although they work finest for long-term safety.
One-time 2FA restoration codes can assist save the day if you happen to lose entry to the gadget to which regular 2FA codes are usually despatched. Retailer the restoration codes someplace protected, presumably offline and as a printed copy. Shedding these codes can lock you out of your account completely.
Lastly, shut all lively classes and revoke entry to linked third-party companies.
Test, verify, verify (minutes 7–10)
In the event you’ve reused the identical password on different platforms, change it in all places. Credential stuffing – which is the place attackers robotically check a stolen username and password mixture throughout plenty of platforms – is essentially automated and takes seconds. If the credentials labored as soon as, they’re going to be tried once more.
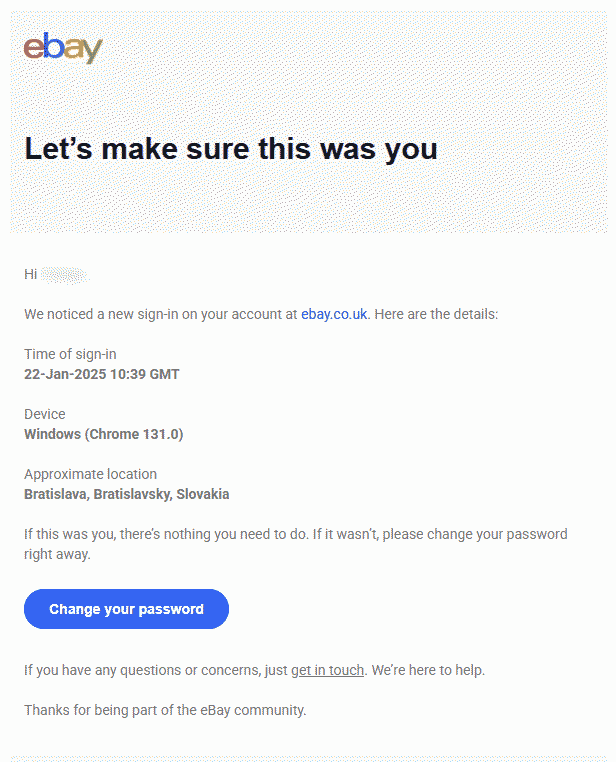
Every time potential, verify the login historical past and up to date exercise to detect unrecognized logins. Additionally, verify for something that appears off: contact particulars you did not modify, despatched messages you do not acknowledge, and unfamiliar purchases or transactions. An electronic mail account deserves specific consideration. Management over your inbox might usually equate to manage over a lot of your whole digital id.
Clear up (minutes 11–13)
Evaluation the checklist of the software program put in and take away something you did not set up or don’t acknowledge. Have a look additionally at internet browser extensions, as these usually fly below the radar. Test that your working system and different software program run their newest model, as malware usually exploits vulnerabilities for which patches can be found.
Warn and report (minutes 14–15 – and past)
Alert your loved ones and associates about what occurred (by means of different channels if you happen to haven’t restored entry to your account). An attacker who has stolen your login credentials can impersonate you and unfold the ‘an infection’ additional, together with by sending malicious hyperlinks to your folks and tricking them into wiring cash. The earlier they know, the much less publicity there may be.
Additionally, report the incident to the platform if you happen to haven’t already. If monetary accounts could also be affected and you have not referred to as your financial institution but, accomplish that now (i.e., don’t simply file a web-based report). Ask particularly about blocking transactions and organising exercise monitoring.
As soon as your safety software program completes the scan, evaluation what it has discovered and act in step with its steerage.
Learn how to cut back the danger of an account compromise
A number of habits could make a significant distinction:
- Use a powerful and distinctive password or passphrase for every on-line account. The commonest passwords are nonetheless strings like ‘123456’ and ‘admin,’ in addition to first names and start dates. They’re all trivially simple to crack and extensively obtainable in leaked credential databases that attackers use routinely.
- A password supervisor solves the sensible drawback above by producing and storing a distinct sturdy password for every service, so there’s nothing to reuse and nothing to recollect. A typical concern is what occurs if the password supervisor itself is compromised. Nevertheless, the danger of utilizing one is significantly decrease than dangers stemming from poor password hygiene.
- Swap on 2FA. Even when a password has been stolen, stable 2FA can cease an attacker from getting any additional. The place the choice exists, an authenticator app is preferable to SMS, as SIM swapping assaults make SMS codes much less dependable than they seem.
- Maintain software program up to date. Updates repair vulnerabilities that attackers learn about and actively exploit. The window between a vulnerability being printed and it getting used within the wild is commonly very quick, so don’t maintain off on putting in the newest updates.
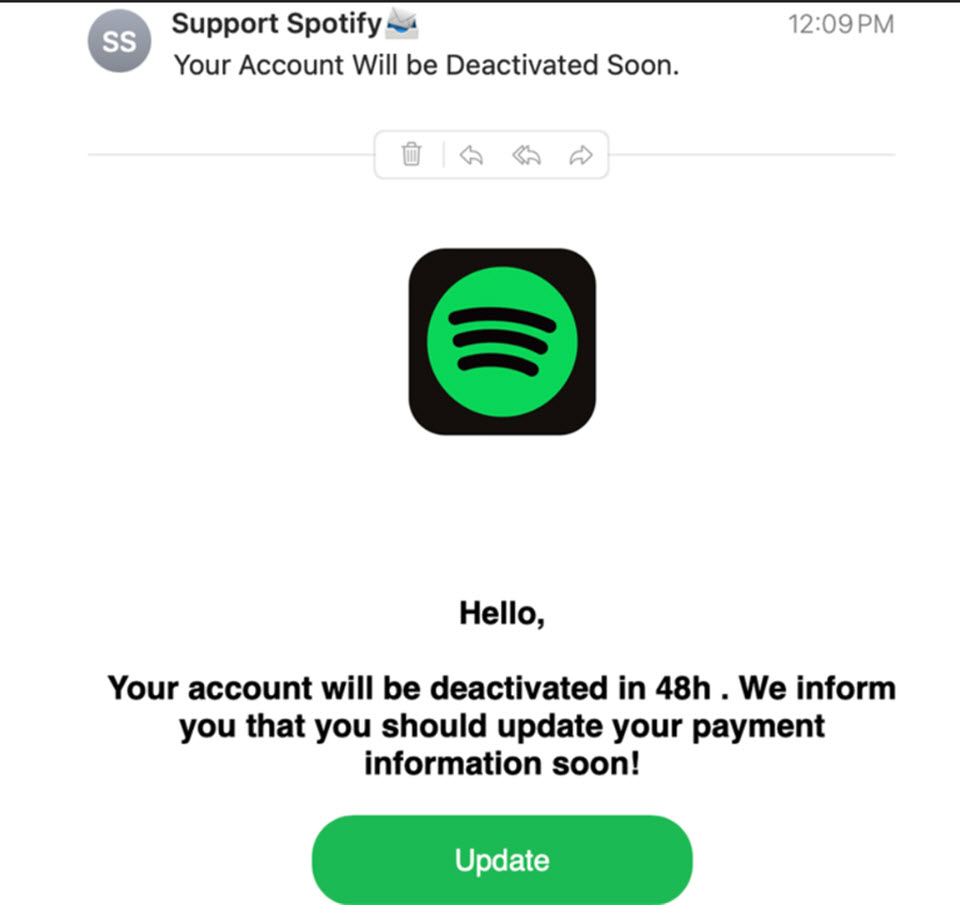
- Look out for phishing, which stays a standard means attackers steal logins. Don’t be duped by credibly-looking branding, actual firm names within the subdomain, and customized particulars scraped from LinkedIn or different public sources. Familiarity alone is not a dependable sign. The very best behavior is to keep away from clicking on hyperlinks in unsolicited emails solely; as an alternative, go on to the service’s web site as an alternative.
- Contemplate shifting previous passwords and enabling passkeys when provided for seamless safe entry to your accounts.
- Use a safety resolution. Respected, multi-layered safety software program goes a great distance towards preserving you protected, together with from phishing makes an attempt.
- Use an id safety service that can warn you to your newly-found private particulars within the web’s seedy underbelly as a way to take motion in time.
Closing ideas
Panic is the primary hurdle to clear when an account will get hacked. A transparent contingency plan helps you progress previous it shortly. It additionally reinforces one thing price preserving in thoughts outdoors of emergencies: the habits that make restoration quicker are largely the identical habits that make the preliminary assault more durable. Along with serving to after one thing goes fallacious, in addition they elevate the price of the assault sufficient that many attackers transfer on to simpler targets.