We’ve all misplaced depend of what number of instances we’ve entered our e mail handle and cellphone quantity to enroll in a web based service, entry a web site or an app, learn the information or log into any of the social media accounts most of us have. Put bluntly, our contact info is everywhere in the web.
On the similar time, being secure and personal on-line might be laborious work and time-consuming, primarily if we’ve to consider managing settings and what info we need to share each single time we join a brand new service or make a web based buy. It turns into overwhelming and will positively be made extra environment friendly.
Can we make it simpler? Identical to taking Sunday night to prep some meals for the week, we will spend a while at the moment to guard our on-line privateness for the months forward!
Disposable and non permanent: the artwork of on-line camouflage
Short-term e mail handle and a secondary inbox
As most web sites require an e mail handle to register, most of us will merely enter our main e mail handle. Why would we want multiple inbox anyway? The truth, nonetheless, suggests in any other case. Once we register a brand new account and even simply enter our e mail to entry restricted content material, we’re most frequently additionally agreeing to the switch of our contact info from a sure service to a different for advertising and marketing functions.
But it surely doesn’t must be that means. What to do as a substitute?
Technique 1: Use a disposable e mail handle – for belongings you don’t actually care that a lot about.
Various disposable e mail companies allow you to use a short lived e mail that self-destructs after a set time period. This is available in significantly helpful for one-time use, for instance if you find yourself requested to submit an e mail handle to entry restricted content material, however don’t essentially need to run the danger of being bombarded by advertising and marketing communications and spam.
A caveat applies, nonetheless, and we will’t stress this sufficient: it’s not a good suggestion to make use of these companies for any communications that will contain really delicate knowledge.
Technique 2: Create a secondary e mail handle for logins and essential newsletters.
For all authorities, banking and different key contacts, use an end-to-end encrypted e mail service as ProtonMail. Don’t use your main e mail handle for something aside from staying in contact together with your family and friends. This can preserve your inbox organized, freed from spam and shielded from knowledge leaks in case a service you’re registered with suffers an information breach.
Alternatively, you may also use a function resembling Apple’s Conceal My E-mail to enroll in a service with out gifting away your actual e mail. Apple creates a singular handle that masks your actual handle and supplies it to the service you’re signing as much as. All emails will then be forwarded mechanically from the masked account to yours. Whereas Android doesn’t but supply the same function, there are a couple of alternate options, resembling Firefox Relay.
The burner cellphone quantity
Together with e mail addresses, your cellphone quantity is a must have to register and log into a lot of web sites, to obtain timed passwords that affirm your id and even for on-line retailers handy over your contact particulars to supply companies.
All in all, your cellphone quantity is in all places, so no marvel most of us already obtain random texts and WhatsApp rip-off makes an attempt.
Technique 3: Get an inexpensive pay as you go SIM card.
Often, this can be a low-cost card that you simply solely must high up with a couple of dollars each few months to maintain it on and, in most international locations, you aren’t required to indicate an ID to make use of it. The aim is to make use of this cellphone quantity for all of your on-line wants: You may hyperlink it to social media accounts, use it for parcel monitoring numbers, share with potential dates you meet on-line and use it for normal anonymity.
In the meantime, your actual main quantity ought to solely be shared with household, mates and authorities or monetary establishments. Since you use the burner quantity on your on-line functions, in the event you get a name, you may instantly assume it’s a rip-off and, probably, some web site you had been registered at suffered an information breach.
Single-use financial institution playing cards
Shopping for on-line might be actually handy, little doubt! We simply must enter the web site, select what we wish and normally we have already got our banking card particulars saved from a earlier buy. All good. Except there’s an information breach affecting the main points saved on that web site that compromises our card particulars or we fall sufferer to a nasty social engineering rip-off!
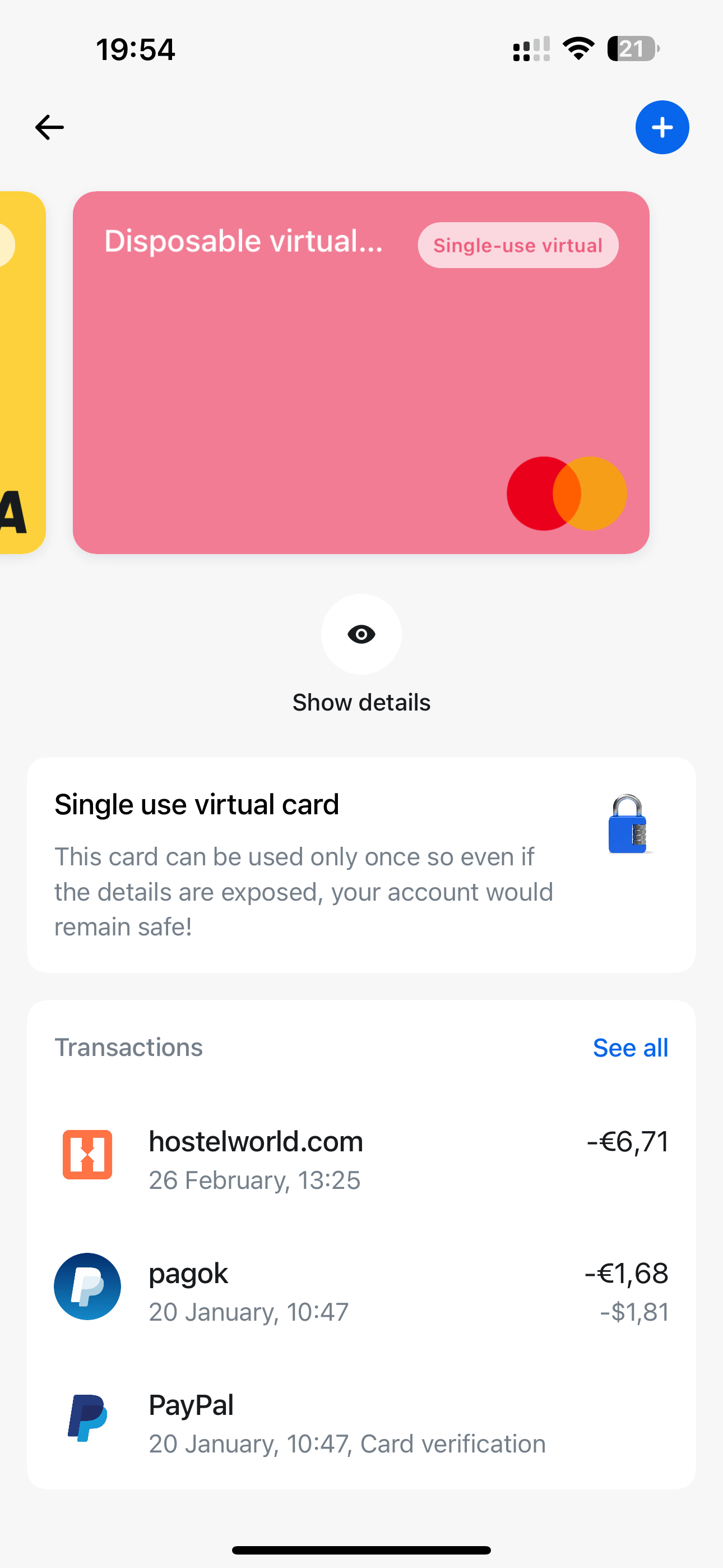
Technique 4: Go for single-use, digital playing cards.
Many banks, primarily these primarily based on cell purposes, supply digital playing cards as a substitute, or as an extra choice on high of the bodily card. And most of those banks may even supply disposable single-use playing cards which can be related to your actual card. When you make a purchase order with a single-use card, the financial institution system will detect the motion, destroy these card particulars and mechanically generate new ones prepared for the subsequent buy. As a result of this can be a randomized card, hackers gained’t have the ability to monitor your actual info.
And in case you’re questioning about refunds, the sellers can nonetheless return the cash by means of the identical single-purchase card particulars to your account.
Two-factor authentication and one-time codes
Most on-line companies nowadays enable – and advocate – using two-factor authentication (2FA). That’s, aside from getting into your password, you may also be required to carry out an additional authentication step. This fashion, if somebody steals your password, they nonetheless gained’t have the ability to log in with out the 2FA code of their palms.
Technique 5: Use app-generated 2FA passcodes.
Most frequently, 2FA includes sending an SMS message to your cellphone quantity (hopefully your burner cellphone) with a one-time passcode (OTP). You solely must kind it in the place requested to show your id. One other – and higher – means depends on utilizing authentication apps resembling Microsoft Authenticator. Below their privateness settings, most web sites supply the chance to generate a QR or alphanumeric code that may be enter on the authenticator app; in flip, the app will generate a short lived code that works similar to an OTP.
This second technique is one thing you would possibly need to get used to – and never simply because Twitter stopped supporting SMS-borne 2FA for non-paying customers not too long ago.
Let’s recap!
- Create non permanent e mail accounts for when it is advisable to cross a restricted content material wall that requests your e mail handle for additional entry.
- Use a good e mail supplier, resembling Gmail or Outlook, to create a secondary account that you simply use for on-line companies and web site signups.
- Get a burner quantity to keep away from getting SMS and rip-off calls.
- Use digital disposable banking playing cards which can be self-destroyed after a single use.
- Use one-time codes for two-factor authentication on high of a sturdy and distinctive password.
Embracing your on-line privateness as a part of your regular routine will make it really feel seamless and pure, taking away the sensation of burden and fixed doubt about whether or not you’re doing sufficient to guard your digital life. Total, utilizing e mail addresses, cellphone numbers and playing cards that aren’t instantly linked to you can be a good way to reduce your digital footprint and slash the danger of being the sufferer of an information breach or rip-off. Lastly, there’s simply as a lot we as customers can do to stop malicious exercise; it’s at all times advisable to make use of digital safety software program that protects you from different potential dangers and assaults.