Study concerning the several types of VPNs and when to make use of them. Discover out which sort of VPN fits your wants with this complete information.
A digital non-public community (VPN) is a approach so as to add safety to on-line connections and protect privateness by encryption. People and companies that deal in delicate issues and want to conceal their on-line exercise are inclined to make the most of VPNs. By creating an encrypted, point-to-point tunnel on which the info travels, their on-line identities and IP addresses are hidden.VPN connections are usually established between a person system similar to a laptop computer and a VPN server.
This text covers the first varieties of VPNs, what is required for every and their predominant use instances.
Soar to:
Kinds of VPNs: comparability desk
| Private VPN | Distant-Entry VPN | Website-to-Website VPN | Cell VPN | |
|---|---|---|---|---|
| Connection | Web | Web | Web gateway | Web |
| Software program wanted | None | VPN shopper | None | None |
| Use case | Personal and safe connectivity for people. | Worker and department workplaces when safe connectivity is an occasional reasonably than a continuing want. | Everlasting connection to go workplace. | Customers who journey ceaselessly, particularly internationally. |
Private VPN
A private VPN is supposed for private use versus enterprise use. Though some companies attempt to save on funds by using them, they actually solely belong in particular person use instances. These utilizing them enhance web connection safety by cloaking shopping and e mail site visitors in anonymity. It additionally shields site visitors from snoopers, whether or not they’re Web Service Suppliers (ISPs), authorities displays, advertisers or cybercriminals. Like all VPNs, a digital tunnel permits site visitors to go by confidentially. This ensures that information can’t be monitored, intercepted en route or altered in any approach.
Right here’s an inventory of non-public VPNs we’ve examined:
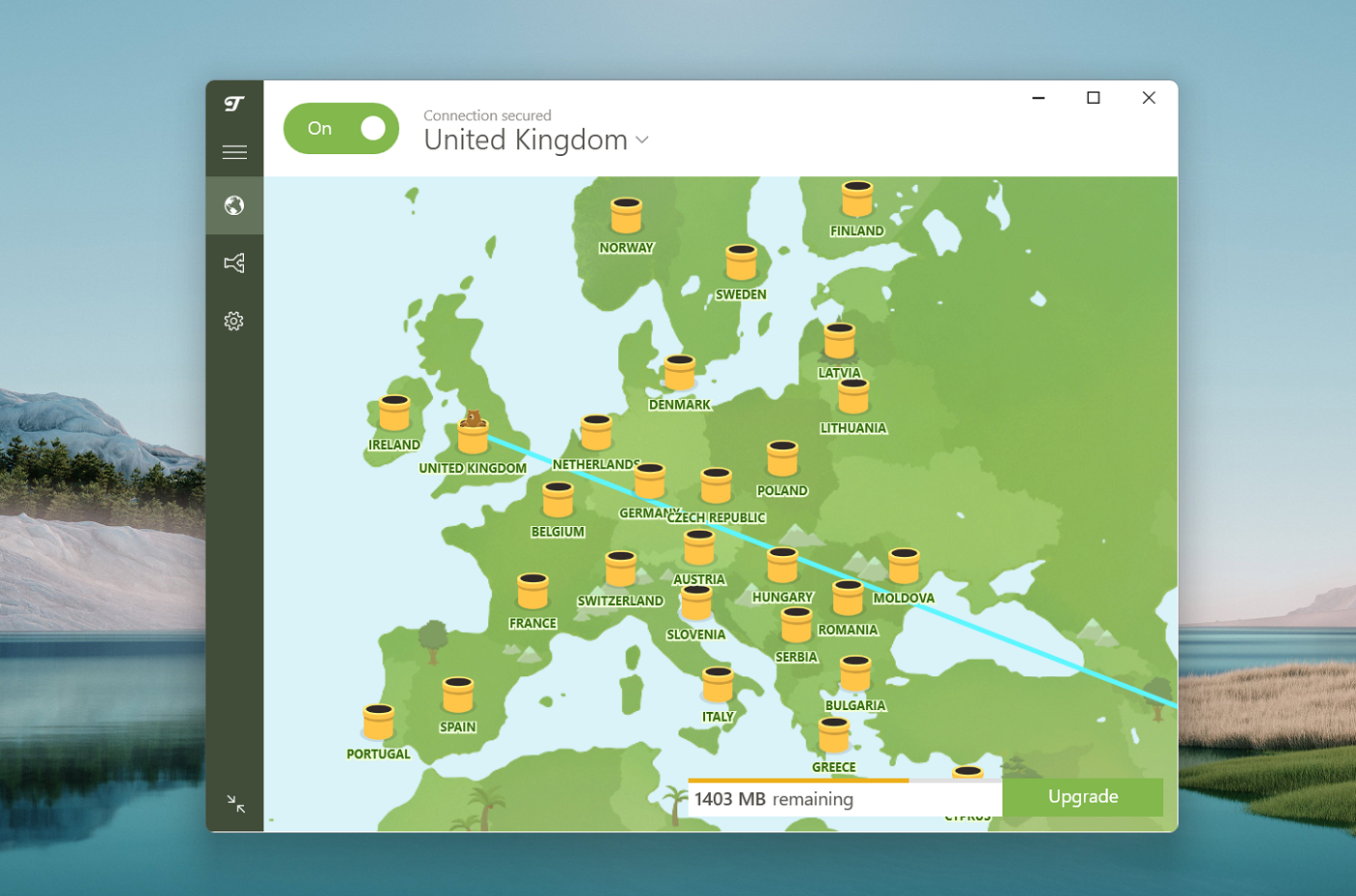
- TunnelBear has a really user-friendly, bear-themed interface; its ease of use and free subscription choice make it enticing to first-time VPN customers.
Learn our full assessment of TunnelBear.
- Proton VPN supplies multi-hop connections—particularly designed to guard in opposition to authorities surveillance.
Learn our full assessment of ProtonVPN.
- Surfshark VPN permits customers to attach an infinite variety of units concurrently—a novel functionality amongst VPNs.
Learn our full assessment of Surfshark.
When to make use of a private VPN:
Private VPN use instances embody:
- Safety of non-public units from exterior assaults or exploitation.
- Safe connectivity between the person’s cellular units and their desktop, server or community.
- Nameless private shopping.
Distant-Entry VPN
A remote-access VPN is designed to determine a safe and encrypted connection between a distant person’s system and a company’s inner community. Firms usually use remote-access VPNs after they have distant workers and want to make sure a secure connection.
Distant-access VPNs are usually cheap and supply a larger degree of safety in comparison with private VPNs. Nevertheless, companies utilizing a remote-access VPN ought to be careful for permissive permission insurance policies. If one person has too many permissions, they are able to entry the info of different customers in that VPN if they’ll acquire one password. Additional, malicious insiders can make the most of the privateness of the VPN to exfiltrate delicate information.

Right here’s an inventory of respected remote-access VPNs:
- NordVPN options embody multi-hop connections, cut up tunneling, site visitors routing and file-sharing and entry to a variety of further safety companies.
Learn our full assessment of NordVPN.
- NordLayer affords third-party authentication, devoted servers and entry and safety for carry your personal system (BYOD) customers.
- Test Level Distant Entry VPN affords multi-factor authentication, auto-connection, centralized administration and compliance scanning.
When to make use of a remote-access VPN
- Distant-access VPNs are primarily used when workers are off-site and need to securely connect with the company community.
- When individuals need to entry a personal community from a public space, generally they select a remote-access VPN.
- Web Protocol safety (IPSec) groups typically make use of remote-access VPNs when compelled to function on public Wi-Fi or much less safe networks.
- These wishing to masks their location when working on public networks ought to contemplate a remote-access VPN.
- Some areas prohibit content material based mostly on location so customers could depend on a remote-access VPN to bypass geographic restrictions.
- Prevention of ISP and different third-party monitoring may be carried out utilizing remote-access VPNs as suppliers aren’t in a position to log and monitor shopping historical past through a tool’s IP handle.
Website-to-Website VPN
A site-to-site VPN makes use of a safe gateway to hyperlink a company community with different networks. Utilizing a site-to-site VPN doesn’t require putting in a VPN shopper on a tool. As a substitute, customers can entry a safe channel within the cloud. In lots of instances, the site visitors is shipped from one router to a different between a number of websites. As such site-to-site VPNs are a semi-permanent connection versus a short lived connection as in a private VPN or remote-access VPN.
Right here’s an inventory of site-to-site VPNs:
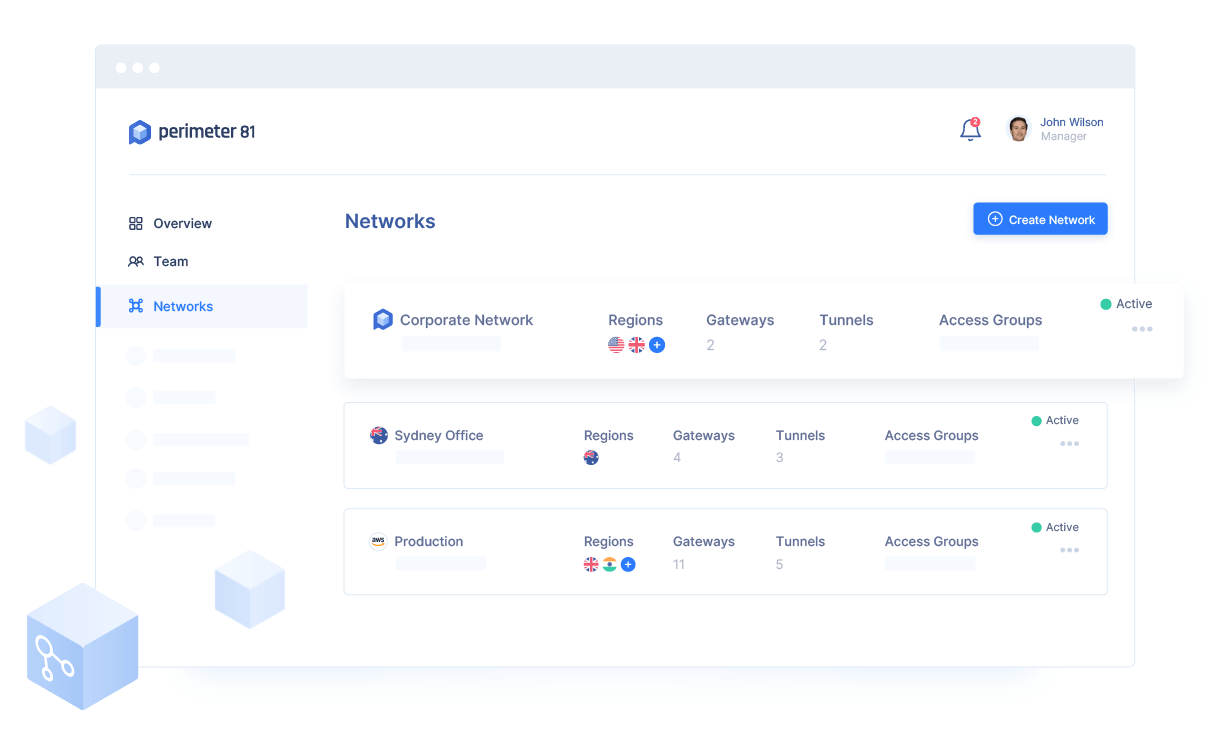
- Perimeter 81 contains options to forestall entry to websites that violate firm insurance policies to manage entry to time-wasting websites and dangerous websites, defend in opposition to malware and block objectionable content material.
Learn our full assessment of Perimeter 81.
- AccessAnywhere Entry supplies a free, easy-to-use VPN router for site-to-site site visitors to journey between workplaces and frequently-used areas.
- AWS site-to-site VPN is a managed service that creates a safe connection between a knowledge middle or department workplace and AWS assets.
When to make use of a site-to-site VPN
- Website-to-site VPNs are good for corporations with a number of workplaces in numerous geographic areas that want ongoing entry to the company community.
- Area workplaces use site-to-site VPNs to determine direct connections to headquarters.
- The place databases, functions and different techniques are operated centrally, department workplaces can use site-to-site VPNs to securely join.
- Some use site-to-site VPNs as an alternative choice to non-public MPLS circuits.
Cell VPN
A cellular VPN is one that may persist throughout periods regardless of adjustments in bodily connectivity similar to a shift within the community entry medium or the purpose of attachment. In different phrases, a cellular VPN shouldn’t be one for cellular customers. It’s a solution to be related always even should you change from one web connection to a different. Regardless of such adjustments, the VPN can keep the session with out interrupting person apps.
Cell VPN choices embody:
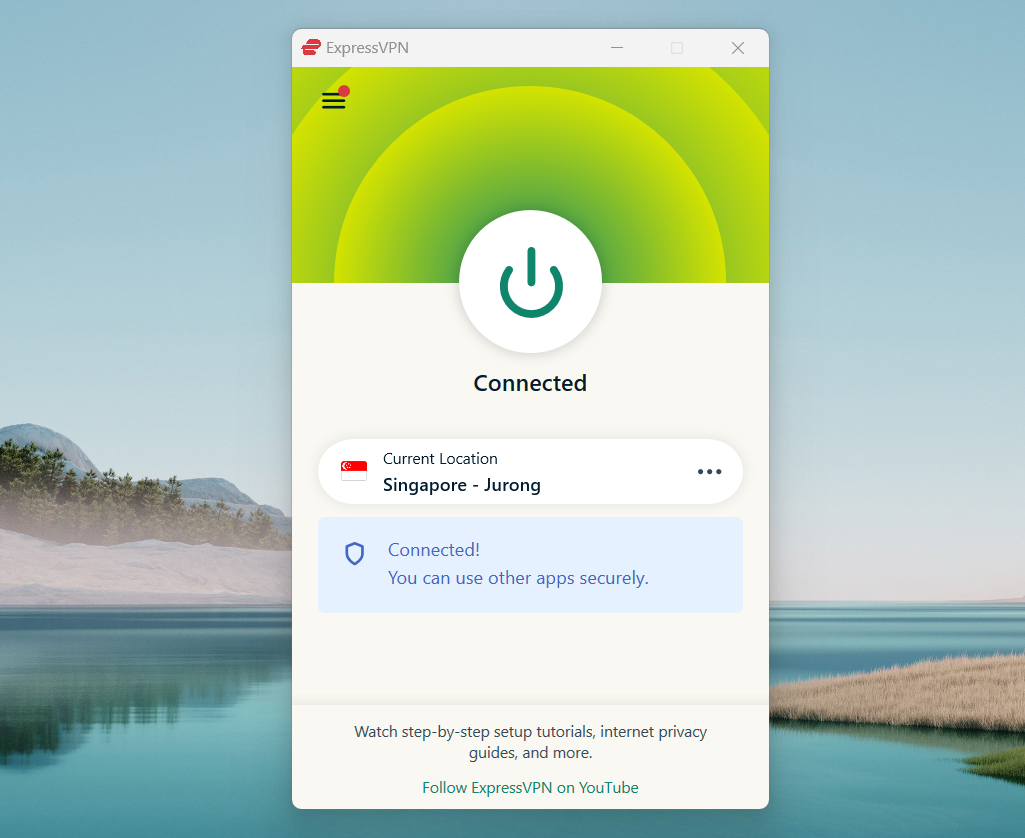
- ExpressVPN has a broad worldwide presence, utilizing the open-source OpenVPN protocol and is good for these wishing to spoof their location to have the ability to entry companies usually obtainable solely at dwelling, in addition to anybody touring exterior of the USA who needs to remain safe.
Learn our full assessment of ExpressVPN.
- CyberGhost VPN has an enormous assortment of VPN servers and a number of choices for spoofing, permitting as much as seven simultaneous connections and comes with antivirus.
Learn our full assessment of CyberGhost VPN.
- TotalVPN provides secure shopping, encryption, anonymizing and prevention of lack of service on account of spotty web or Wi-Fi.
When to make use of a cellular VPN:
- Once you typically swap from Wi-Fi to cellular information or between Wi-Fi hotspots with out having your functions or streaming channels cease.
- For vacationers or commuters who should take care of spotty and variable community efficiency.
- Distant employees who want fixed entry no matter community or Wi-Fi fluctuations.
These contemplating a VPN ought to give cautious thought to the kind of VPN they choose. The totally different VPN sorts listed above match totally different use instances. Some are good for people whereas others are higher match for enterprise use.
Additional, the kind of system and platform play an element. For instance, some VPN options are designed to reinforce browsers—similar to with Chrome extensions—and others are designed particularly for sure cellular units or working techniques.


