An unknown risk actor has been noticed publishing typosquat packages to the Python Bundle Index (PyPI) repository for almost six months with an intention to ship malware able to gaining persistence, stealing delicate knowledge, and accessing cryptocurrency wallets for monetary acquire.
The 27 packages, which masqueraded as common authentic Python libraries, attracted 1000’s of downloads, Checkmarx stated in a brand new report. A majority of the downloads originated from the U.S., China, France, Hong Kong, Germany, Russia, Eire, Singapore, the U.Okay., and Japan.
“A defining attribute of this assault was the utilization of steganography to cover a malicious payload inside an innocent-looking picture file, which elevated the stealthiness of the assault,” the software program provide chain safety agency stated.
A number of the packages are pyefflorer, pyminor, pyowler, pystallerer, pystob, and pywool, the final of which was planted on Might 13, 2023.
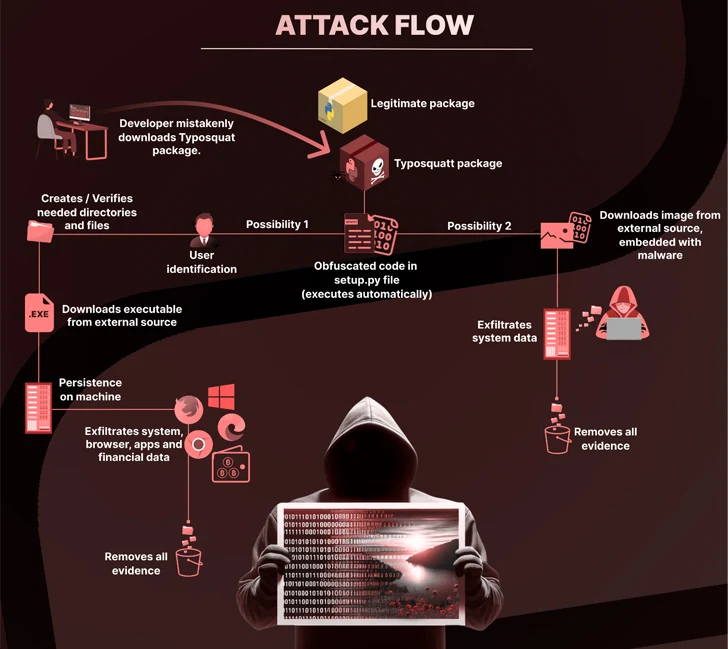
A typical denominator to those packages is using the setup.py script to incorporate references to different malicious packages (i.e., pystob and pywool) that deploy a Visible Primary Script (VBScript) with the intention to obtain and execute a file named “Runtime.exe” to realize persistence on the host.
Embedded inside the binary is a compiled file that is able to gathering info from net browsers, cryptocurrency wallets, and different functions.
An alternate assault chain noticed by Checkmarx is alleged to have hidden the executable code inside a PNG picture (“uwu.png”), which is subsequently decoded and run to extract the general public IP deal with and the universally distinctive identifier (UUID) of the affected system.
Pystob and Pywool, specifically, have been revealed underneath the guise of instruments for API administration, solely to exfiltrate the information to a Discord webhook and try to take care of persistence by inserting the VBS file within the Home windows startup folder.
“This marketing campaign serves as one other stark reminder of the ever-present threats that exist in at present’s digital panorama, significantly in areas the place collaboration and open trade of code are foundational,” Checkmarx stated.
The event comes as ReversingLabs uncovered a brand new wave of protestware npm packages that “disguise scripts broadcasting messages of peace associated to the conflicts in Ukraine and in Israel and the Gaza Strip.”
One of many packages, named @snyk/sweater-comb (model 2.1.1), determines the geographic location of the host, and if it is discovered to be Russia, shows a message criticizing the “unjustified invasion” of Ukraine by means of one other module referred to as “es5-ext“
One other package deal, e2eakarev, has the outline “free palestine protest package deal” within the package deal.json file, and carries out related checks to see if the IP deal with resolves to Israel, and in that case, log what’s described as a “innocent protest message” that urges builders to boost consciousness in regards to the Palestinian battle.
It isn’t simply risk actors infiltrating open-source ecosystems. Earlier this week, GitGuardian revealed the presence of three,938 complete distinctive secrets and techniques throughout 2,922 PyPI tasks, of which 768 distinctive secrets and techniques have been discovered to be legitimate.
This consists of AWS keys, Azure Lively Listing API keys, GitHub OAuth app keys, Dropbox keys, SSH keys, and credentials related to MongoDB, MySQL, PostgreSQL, Coinbase and Twilio.
What’s extra, many of those secrets and techniques have been leaked greater than as soon as, spanning a number of launch variations, bringing the full variety of occurrences to 56,866.
“Exposing secrets and techniques in open-source packages carries vital dangers for builders and customers alike,” GitGuardian’s Tom Forbes stated. “Attackers can exploit this info to achieve unauthorized entry, impersonate package deal maintainers, or manipulate customers by means of social engineering ways.”
The continual wave of assaults concentrating on the software program provide chain has additionally prompted the U.S. authorities to difficulty new steerage this month for software program builders and suppliers to take care of and supply consciousness about software program safety.
“It is suggested that acquisition organizations assign provide chain threat assessments to their shopping for selections given the current excessive profile software program provide chain incidents,” the Cybersecurity and Infrastructure Safety Company (CISA), Nationwide Safety Company (NSA), and the Workplace of the Director of Nationwide Intelligence (ODNI) stated.
“Software program builders and suppliers ought to enhance their software program improvement processes and scale back the danger of hurt to not simply workers and shareholders, but in addition to their customers.”