
The FBI has issued a public service announcement warning that Russian intelligence-linked menace actors are actively concentrating on customers of encrypted messaging apps similar to Sign and WhatsApp in phishing campaigns which have already compromised 1000’s of accounts.
The FBI’s PSA is the primary public attribution linking these campaigns on to Russian intelligence providers, somewhat than a broader description of simply state hackers.
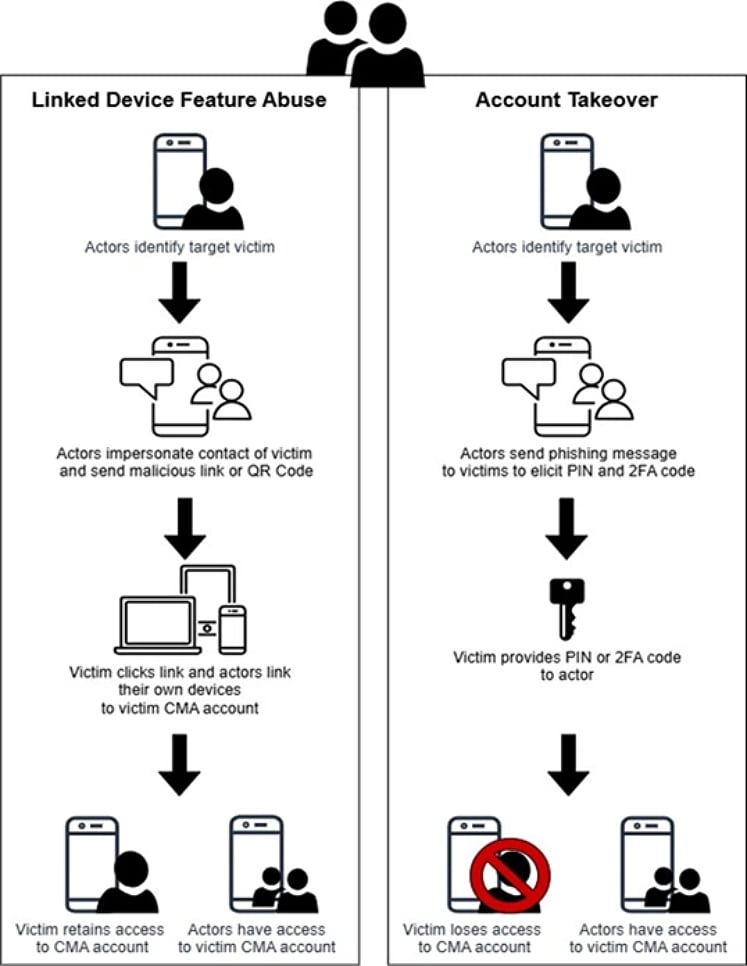
In response to the FBI, the campaigns are designed to bypass the protections of end-to-end encryption in business messaging apps (CMAs), not by breaking encryption, however by way of account hijacks.
The FBI says the methods utilized in these assaults could be utilized to a number of CMAs however predominantly goal Sign customers.
Relying on the entry they acquire, attackers can learn personal messages and contact lists, impersonate victims, and launch extra phishing campaigns as trusted folks.
The FBI says the assaults have affected “1000’s” of accounts worldwide and primarily goal these with entry to delicate data.
“The exercise targets people of excessive intelligence worth, similar to present and former U.S. authorities officers, army personnel, political figures, and journalists,” reads the FBI’s PSA.
The FBI’s attribution comes after earlier advisories from Dutch and French cybersecurity authorities that described comparable account-hijacking operations.
Earlier this month, Dutch intelligence companies warned that state-backed attackers have been concentrating on Sign and WhatsApp customers in phishing campaigns geared toward having access to safe communications.
The advisory highlighted that the assaults relied on tricking customers into permitting attackers so as to add the account to their gadgets or hyperlink attacker-controlled gadgets to the account.
At present, France’s Cyber Disaster Coordination Heart (C4) additionally printed an alert about the identical techniques concentrating on instantaneous messaging platforms, stating the exercise is widespread and ongoing throughout a number of international locations.
Sign phishing assaults
All three advisories state that the phishing assaults observe the identical tactic of bypassing the platform’s encryption by hijacking accounts or linking gadgets to an present account.
Supply: FBI
The FBI says that the majority phishing messages impersonate help accounts, which request that the goal carry out an motion that secretly grants menace actors entry to the account.
Victims are sometimes tricked into sharing verification codes or scanning malicious QR codes that hyperlink their accounts (Sign and WhatsApp) to attacker-controlled gadgets.
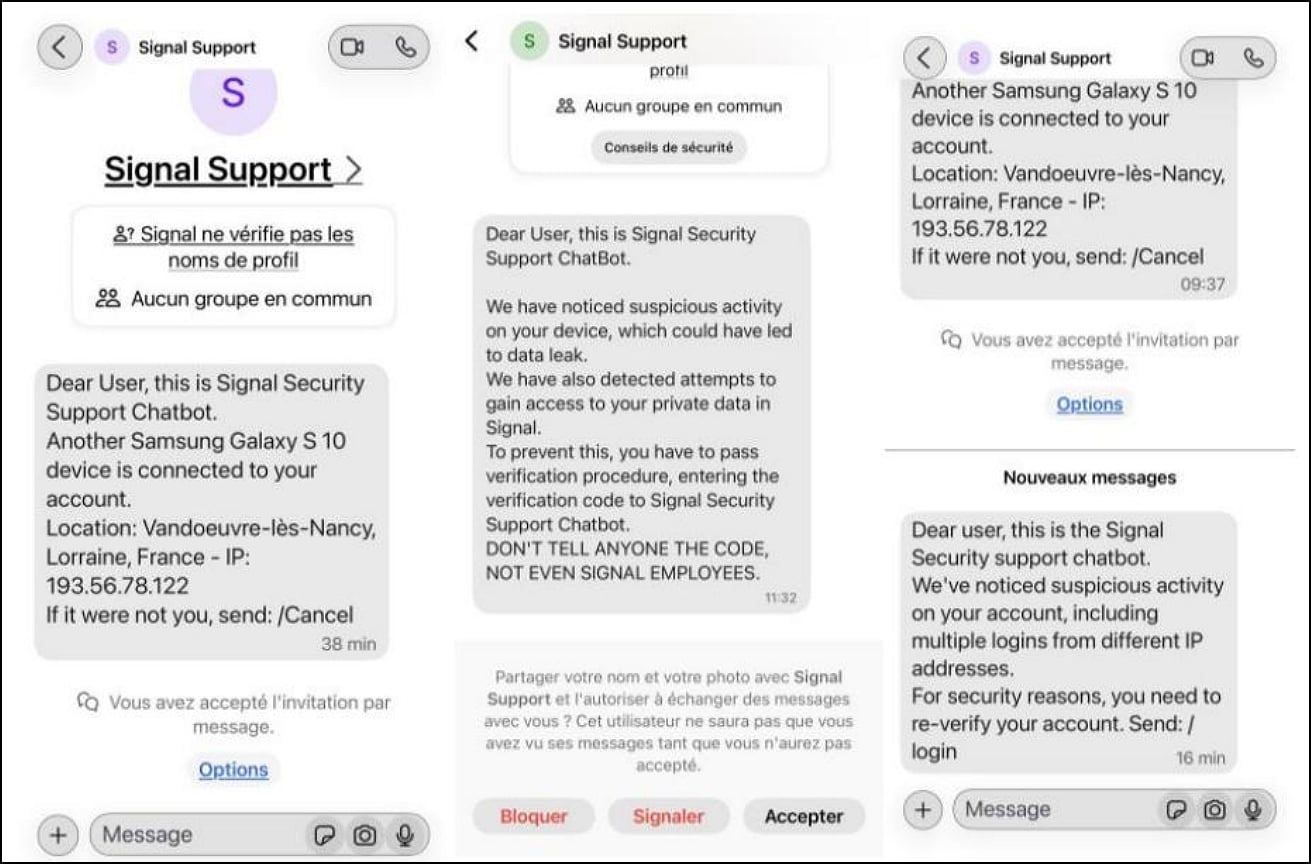
Supply: France’s Cyber Disaster Coordination Heart (C4)
As soon as the menace actors acquire entry to accounts, they’ll silently monitor communications, be a part of group chats, and ship messages because the compromised person, making detection harder and enabling additional phishing campaigns.
The PSA emphasizes that encryption in Sign, WhatsApp, and comparable platforms just isn’t damaged and no vulnerabilities are being exploited.
The FBI says the marketing campaign has already led to unauthorized entry to 1000’s of messaging accounts, which have been then used to focus on extra victims.
Customers are suggested to stay suspicious of sudden messages, be cautious of requests to scan QR codes or hyperlink gadgets to their accounts, and by no means share verification codes with anybody, together with accounts claiming to be a platform’s help personnel.



