
Hackers a part of APT28, a state-backed menace group linked to Russia’s army intelligence service (GRU), are exploiting a Zimbra Collaboration Suite (ZCS) vulnerability in assaults concentrating on Ukrainian authorities entities.
This high-severity safety flaw (tracked as CVE-2025-66376 and patched in early November) stems from a saved cross-site scripting (XSS) that unauthenticated attackers can exploit to realize distant code execution (RCE) and compromise the Zimbra server and the goal’s e mail account.
On Wednesday, the Cybersecurity and Infrastructure Safety Company (CISA) added the vulnerability to its catalog of vulnerabilities exploited within the wild. CISA additionally ordered Federal Civilian Govt Department (FCEB) businesses to safe their servers inside two weeks, as mandated by the Binding Operational Directive (BOD) 22-01 issued in November 2021.
Whereas the U.S. cybersecurity company did not present additional particulars on the continued exploitation of CVE-2025-66376, safety researchers at Seqrite Labs reported a day earlier that the Zimbra XSS vulnerability had been exploited by APT28 army hackers in assaults towards Ukraine.
The Ukrainian State Hydrology Company (a vital infrastructure entity underneath the Ministry of Infrastructure that gives navigational, maritime, and hydrographic assist) was one of many targets of this phishing marketing campaign (named Operation GhostMail).
“The phishing e mail has no malicious attachments, no suspicious hyperlinks, no macros. The whole assault chain lives contained in the HTML physique of a single e mail, there aren’t any malicious attachments,” Seqrite Labs stated.
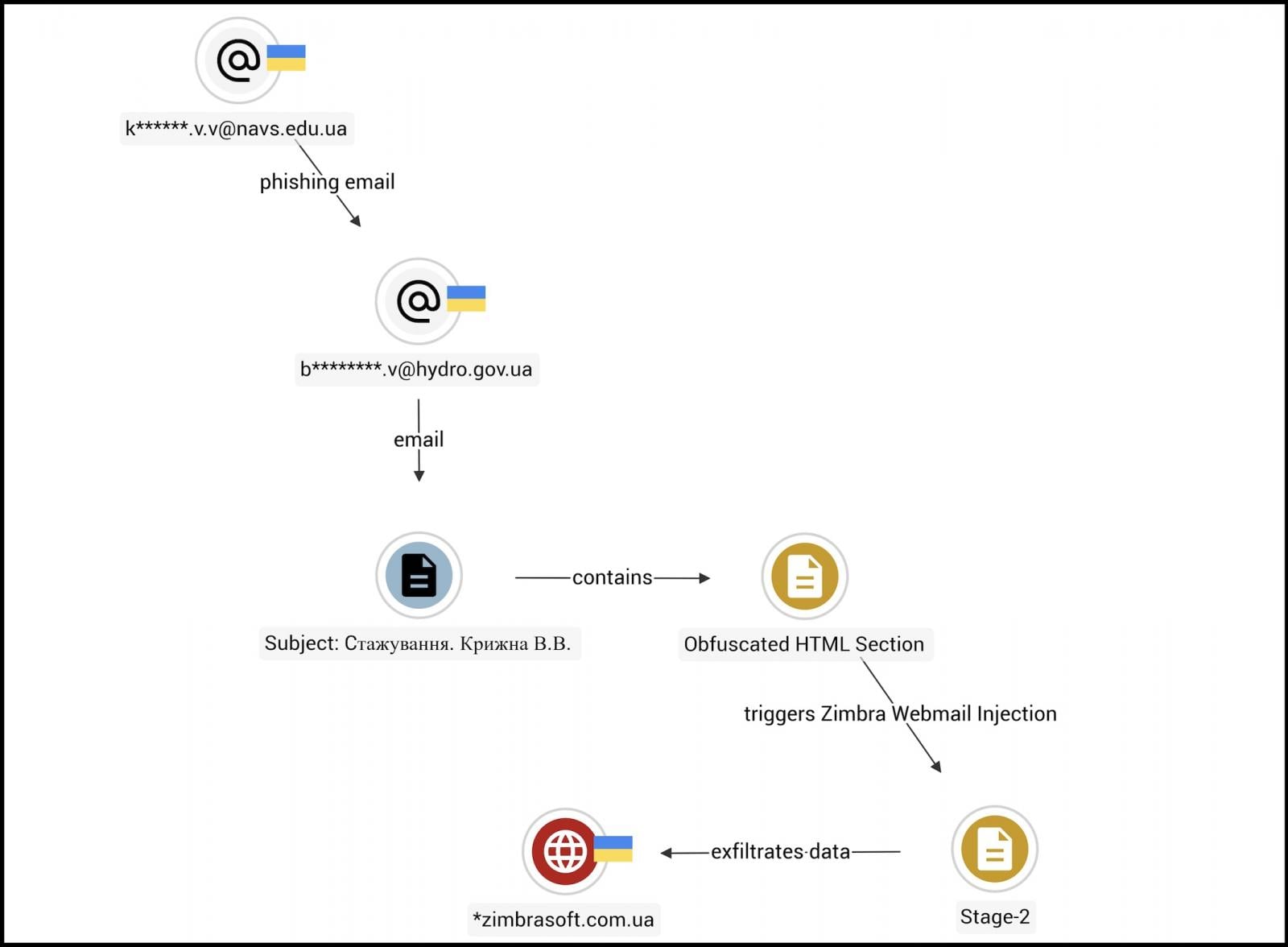
The APT28 (aka Fancy Bear, Strontium) hackers’ malicious messages delivered an obfuscated JavaScript payload that exploits the CVE-2025-66376 vulnerability when the recipient opens the e-mail in a susceptible Zimbra webmail session.
“The script executes silently within the browser and begins harvesting credentials, session tokens, backup 2FA codes, browser-saved passwords, and the contents of the sufferer’s mailbox going again 90 days with all the information exfiltrated over each DNS and HTTPS,” the researchers added.
Zimbra safety flaws are continuously focused in assaults, together with by Russian state-sponsored menace teams, and have been used to breach 1000’s of susceptible e mail servers lately.
As an example, beginning in February 2023, the Russian Winter Vivern cyberespionage group used one other mirrored XSS exploit to breach Zimbra webmail portals and spy on the communications of NATO-aligned organizations and individuals, together with authorities officers, army personnel, and diplomats.
In October 2024, U.S. and U.Ok. cyber businesses additionally warned that APT29 (aka Cozy Bear, Midnight Blizzard) hackers linked to Russia’s Overseas Intelligence Service (SVR) have been attacking susceptible Zimbra servers “at a mass scale,” exploiting a vulnerability beforehand used to steal e mail account credentials.
Zimbra is a broadly well-liked e mail and collaboration software program suite utilized by lots of of hundreds of thousands of individuals, together with lots of of presidency businesses and 1000’s of companies worldwide.



