
The U.S. Cybersecurity and Infrastructure Safety Company (CISA) ordered federal companies to patch three iOS safety flaws focused in cyberespionage and crypto-theft assaults utilizing the Coruna exploit package.
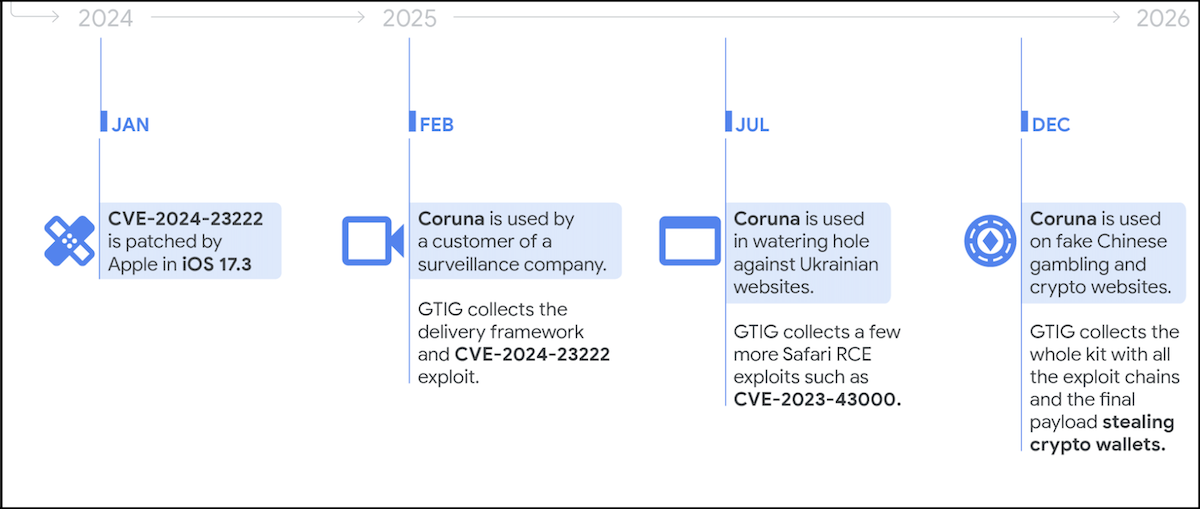
As Google Menace Intelligence Group (GTIG) researchers revealed earlier this week, Coruna makes use of a number of exploit chains concentrating on 23 iOS vulnerabilities, lots of which have been deployed in zero-day assaults.
Nevertheless, the exploits is not going to work on latest variations of iOS and can be blocked if the goal is utilizing personal shopping or has enabled Apple’s Lockdown Mode anti-spyware safety function.
Coruna gives risk actors with Pointer Authentication Code (PAC) bypass, sandbox escape, and PPL (Web page Safety Layer) bypass capabilities, and allows them to realize WebKit distant code execution and escalate permissions to Kernel privileges on susceptible gadgets.
GTIG noticed the exploit package being utilized by a number of risk actors final 12 months, together with a surveillance vendor buyer, a suspected Russian state-backed hacking group (UNC6353), and a financially motivated Chinese language risk actor (UNC6691).
The latter deployed it on faux playing and crypto web sites and used it to ship a malware payload designed to steal contaminated victims’ cryptocurrency wallets.
Cellular safety agency iVerify additionally stated that Coruna is an instance of “subtle spyware-grade capabilities” that migrated “from business surveillance distributors into the arms of nation-state actors and, in the end, mass-scale felony operations.”
On Thursday, CISA added three of the 23 Coruna vulnerabilities to its catalog of Identified Exploited Vulnerabilities, ordering Federal Civilian Government Department (FCEB) companies to safe their gadgets by March 26, as mandated by the Binding Operational Directive (BOD) 22-01.
“Apply mitigations per vendor directions, comply with relevant BOD 22-01 steering for cloud companies, or discontinue use of the product if mitigations are unavailable,” CISA warned.
“All these vulnerabilities are frequent assault vectors for malicious cyber actors and pose important dangers to the federal enterprise.”
Though BOD 22-01 applies solely to federal companies, CISA urged all organizations, together with personal sector firms, to prioritize patching these flaws to safe their gadgets towards assaults as quickly as attainable.



