
Menace actors are brazenly promoting entry to hacked web sites as a part of the underground financial system. Probably the most promising merchandise is a compromised cPanel credential. They’re bought within the hundreds throughout fraudulent discussion groups at commodity-level pricing and marketed as plug-and-play infrastructure for phishing and rip-off campaigns.
In new analysis, Flare safety researchers analyzed exercise throughout monitored fraudulent teams over a seven-day interval, displaying a structured ecosystem working at scale.
We analyzed greater than 200,000 posts referencing cPanel entry, and we defined how cPanel has turn out to be a scorching commodity, why it’s desired by menace actors, and the way it matches in all the menace panorama.
cPanel – One Key to Management the Web site
cPanel is likely one of the most generally used Linux-based webhosting management panels on this planet. It offers a structured administration layer on prime of normal system providers. It acts as an orchestration and automation interface for managing internet hosting accounts, domains, mail providers, databases, DNS zones, SSL certificates, and file techniques.
In response to Shodan, there are over 1.5 million internet-connected servers with cPanel software program.
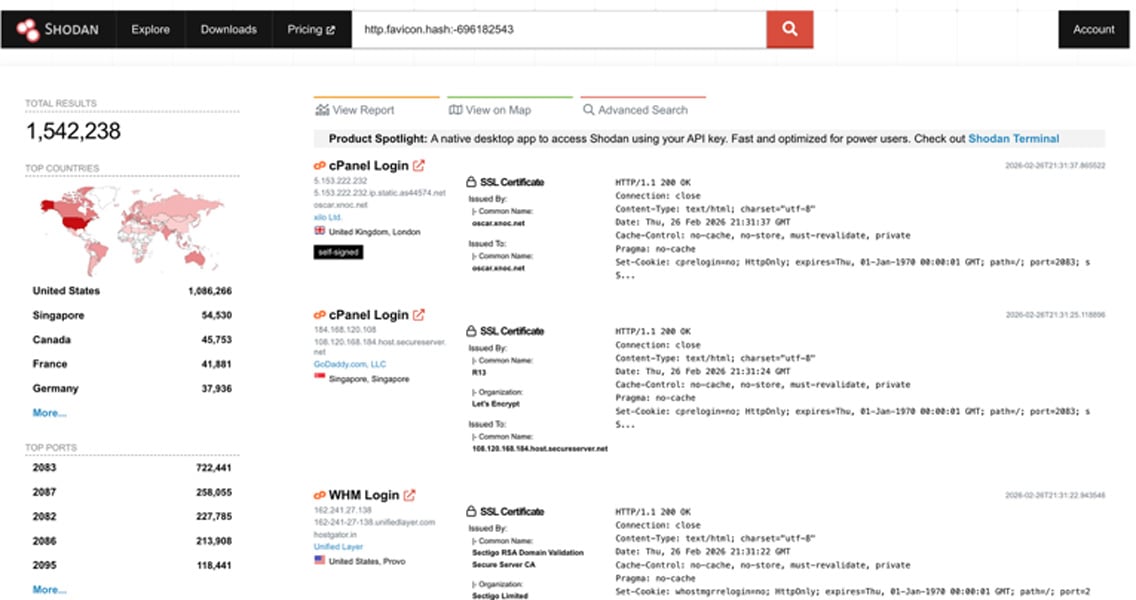
The heatmap beneath illustrates how cPanel is well-liked primarily within the U.S. (over 1 million outcomes).

Compromised cPanels Allow Huge-Scale Assaults
Think about you personal a web site, both for private use, operating a small enterprise, or one in all many in your enterprise’s web-facing belongings. As soon as a menace actor obtains the professional credentials to entry the administration layer, it allows a variety of capabilities:
-
Deploying backdoors for persistence
-
Creating new admin customers for persistence
-
Deploying malware
-
Gaining root entry on the server
-
Deploying phishing kits as a subdomain beneath the professional area identify
-
Creating SMTP accounts beneath the area to disseminate phishing or spam campaigns
-
Stealing and exfiltrating invaluable knowledge (PII, secrets and techniques) from databases
In shared internet hosting environments, a single cPanel can allow entry to dozens of domains, and in an organizational degree, it might compromise all the internet presence.
As a result of attackers use legitimate credentials, conventional safety controls might not instantly flag the exercise or completely miss it. Abuse might start with quiet outbound mail or hidden file uploads earlier than seen exploitation could be detected.
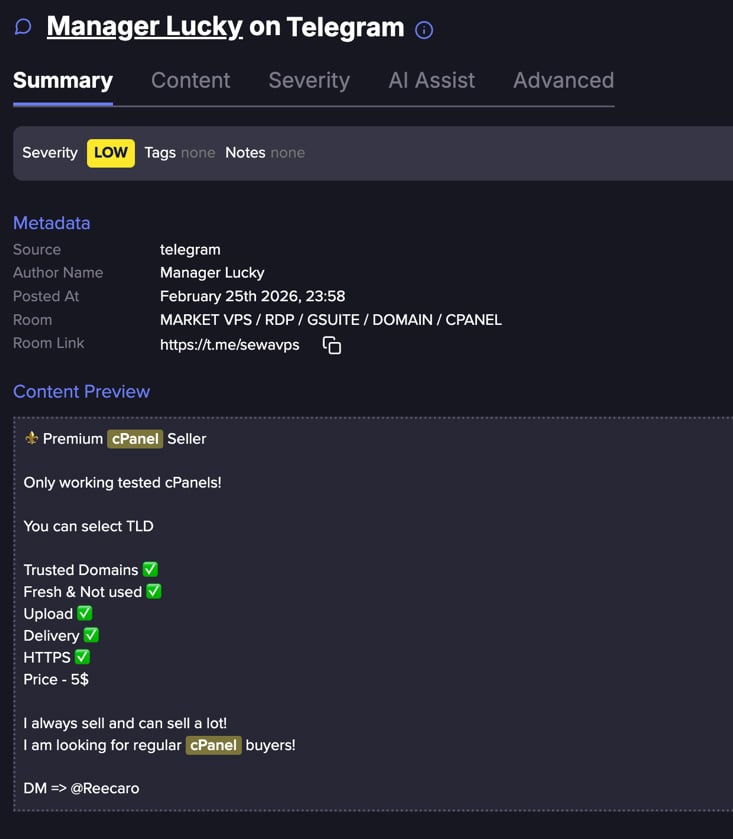
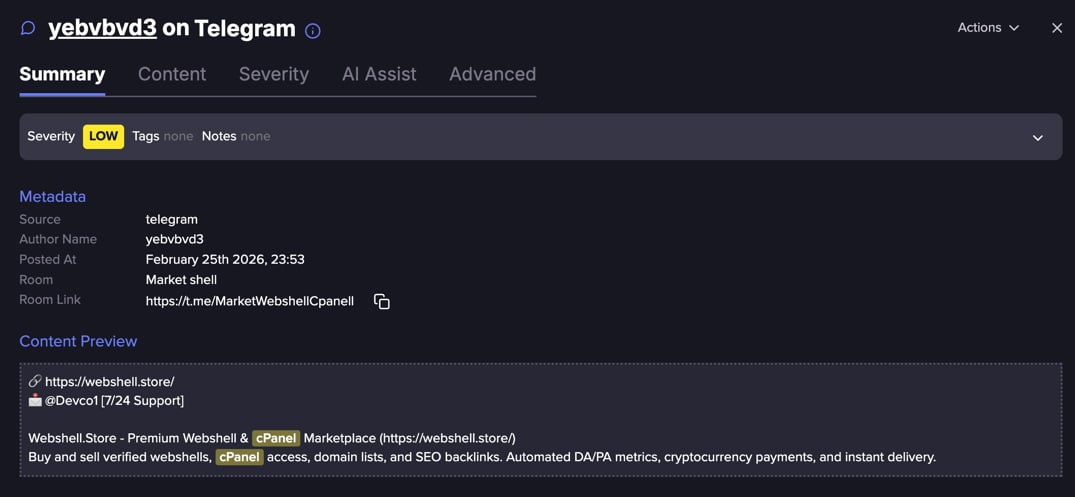
Flare displays underground Telegram channels the place menace actors promote compromised cPanel credentials, SMTP entry, and internet hosting infrastructure.
Get alerts when your domains, internet hosting accounts, or credentials seem in bulk gross sales earlier than they’re exploited.
cPanels are Compromised in Many Methods
Traditionally, menace actors have gained entry to cPanel environments by a mixture of credential abuse, internet software compromise, and server-level exploitation.
The commonest vector has been stolen or brute-forced credentials. Attackers leverage phishing campaigns, password reuse from knowledge breaches, credential stuffing, and automatic brute-force assaults in opposition to uncovered cPanel login portals.
Configuration errors resembling exposing delicate recordsdata (config.yaml, .env) to the web, weak passwords, or the absence of multi-factor authentication have historically made this a beautiful entry level.
One other frequent path has been exploiting susceptible web sites hosted on the identical server. Outdated CMS platforms like WordPress, Joomla, or Drupal, together with susceptible plugins and themes, enable attackers to add internet shells or escalate privileges.
As soon as contained in the internet hosting account, they could pivot laterally, harvest saved credentials, entry configuration recordsdata (resembling wp-config.php), or try privilege escalation to achieve broader cPanel entry.
Over time, automation has amplified these strategies, with botnets constantly scanning for uncovered login panels, recognized CVEs, and misconfigurations to monetize entry by spam, phishing infrastructure, defacement, or resale in underground markets.
Compromised cPanels are a In style Commodity in Underground Markets
Flare researchers collected a seven day pattern with over 200,000 posts. We discovered that 90% of the posts have been duplicates.
This may increasingly point out a extremely commoditized market with a whole lot of distinctive posts that have been amplified hundreds of occasions by way of varied channels.
Pricing tiers differentiate high quality, geography, and infrastructure repute. Bulk reductions incentivize scale.
Flare hyperlink to publish, join the free trial to entry for those who aren’t already a buyer
Commodification
Our evaluation is predicated on hundreds of distinct posts which comprise express worth references. cPanels are sometimes bought in bulk as a result of, in lots of circumstances, the preliminary entry has already been detected, credentials might have been revoked, or the entry is in any other case restricted.
Patrons perceive they’re assuming threat, which is mirrored within the pricing and volume-based gross sales mannequin.
The truth that we discovered over 90% duplication signifies that sellers repeatedly promote the identical stock throughout a number of fraudulent discussion groups, doubtless utilizing templated advertisements and automatic reposting instruments.
Listings regularly embody advertising and marketing language resembling “contemporary,” “top quality,” “spam clear,” or “prepared for mailing,” mirroring industrial gross sales ways.
The cPanels choices behave precisely like common markets:
|
High quality
|
Amount
|
Worth
|
|
Premium
|
100
|
$75
|
|
Premium
|
500
|
$289
|
|
Premium
|
1,000
|
$645
|
|
Common
|
1,000
|
$23
|
|
Common
|
3,000
|
$42
|
|
Common
|
5,000
|
$58
|
The standard differentiation is easy:
-
Excessive-trust top-level domains resembling .gov or .mil carry considerably larger perceived legitimacy. In consequence, phishing or rip-off campaigns leveraging these domains have the next likelihood of success.
-
In distinction, domains like .xyz or .internet are usually seen as lower-value belongings in underground markets, as they provide much less inherent belief and due to this fact decrease anticipated conversion charges.
-
Some posts outlined premium high quality panels nearly as good search engine optimisation metrics, and respected server suppliers.
-
Lively SMTP server will increase the worth of the product. It allows the customer to ship outbound emails from a professional area with out rapid restrictions or blacklisting. This will increase the worth of the compromised cPanel because the menace actor can ship phishing or spam emails straight from a trusted infrastructure, considerably enhancing deliverability and bypass charges.
-
Compromised cPanels of U.S. or EU-based internet hosting firms or domains are dearer, notably when the cPanel is revealed for phishing functions.
Flare hyperlink to publish, join the free trial to entry for those who aren’t already a buyer
Detection and Mitigation
Organizations ought to allow multi-factor authentication (MFA) on all internet hosting management panel accounts, implement sturdy and distinctive passwords, and limit administrative entry by IP tackle wherever attainable.
Outbound SMTP exercise needs to be constantly monitored to detect spam abuse, whereas file integrity monitoring might help determine unauthorized modifications.
Monitoring newly created internet hosting accounts, surprising cron jobs, or configuration modifications can present early indicators of compromise.
It’s equally necessary to observe for credential publicity in stealer logs and underground marketplaces, as internet hosting credentials are regularly traded after preliminary infections.
CMS platforms and their plugins have to be totally patched, unused providers disabled, and the precept of least privilege utilized throughout internet hosting environments.
Harm from Compromised cPanel Account: Account Compromise to Enterprise Disaster
For organizations, the impression of a compromised cPanel account could be rapid and extreme. Menace actors’ actions can result in area and IP blacklisting, resulting in reputational injury and operational disruption. In additional severe circumstances, web site content material could also be stolen, defaced, and even encrypted and held for ransom, turning what started as a easy account compromise right into a full-scale enterprise continuity incident.
When stolen internet hosting credentials are more and more handled as stock – packaged, graded, and bought at scale throughout underground markets – the cybercrime financial system shifts from exploit growth to entry brokerage, defending internet hosting credentials turns into a frontline protection in opposition to being repurposed as infrastructure for phishing, spam, and fraud operations.
On this access-driven ecosystem, internet hosting credentials signify a high-value gateway into company environments. If present tendencies proceed, automated harvesting and bulk redistribution of those credentials will additional industrialize the mannequin, decreasing the barrier to entry for phishing operators searching for trusted domains and IP house.
The result’s a rising provide chain of abuse – the place compromised internet hosting accounts are not incidental, however strategic belongings in cybercriminal operations.
Study extra by signing up for our free trial.
Sponsored and written by Flare.


