Digital Safety
A fast dive into the murky world of cyberespionage and different rising threats dealing with managed service suppliers – and their clients
02 Could 2023
•
,
4 min. learn

ESET telemetry from This autumn 2022 noticed the beginning of a brand new marketing campaign by MuddyWater, a cyberespionage group linked to Iran’s Ministry of Intelligence and Safety (MOIS) and lively since no less than 2017. The group (primarily) targets victims within the Center East, Asia, Africa, Europe, and North America, specializing in telecommunications firms, governmental organizations, and the oil & gasoline and vitality verticals.
For the MSP-interested reader, what stands out of their October 2022 marketing campaign is that 4 victims, three in Egypt and one in Saudi Arabia, have been compromised by way of the abuse of SimpleHelp, a authentic distant entry instrument (RAT) and distant assist software program utilized by MSPs. This improvement alerts the significance of visibility for MSPs. In deploying tons of and even 1000’s of software program varieties don’t have any selection however to make use of automation and make sure that SOC groups, customer-facing safety admins, and detection and response processes are mature and consistently bettering.
Good instruments for unhealthy guys?
ESET Analysis found that when SimpleHelp was current on a sufferer’s disk, MuddyWater operators deployed Ligolo, a reverse tunnel, to attach the sufferer’s system to their Command and Management (C&C) servers. How and when MuddyWater got here into possession of the MSP’s tooling or entered the MSP’s setting is unknown. Now we have reached out to the MSP.
Whereas this marketing campaign continues, MuddyWater’s use of SimpleHelp has, to this point, efficiently obfuscated the MuddyWater C&C servers – the instructions to provoke Ligolo from SimpleHelp haven’t been captured. Regardless, we are able to already word that MuddyWater operators are additionally pushing MiniDump (an lsass.exe dumper), CredNinja, and a brand new model of the group’s password dumper MKL64.
In late October 2022, ESET detected MuddyWater deploying a customized reverse tunneling instrument to the identical sufferer in Saudi Arabia. Whereas its goal was not instantly obvious, the evaluation continues, and progress might be tracked in our non-public APT Reviews.
Alongside utilizing MiniDump to acquire credentials from Native Safety Authority Subsystem Service (LSASS) dumps and leveraging the CredNinja penetration testing instrument, MuddyWater sports activities different techniques and methods, for instance, utilizing well-liked MSP instruments from ConnectWise to achieve entry to victims’ methods.
ESET has additionally tracked different methods linked to the group, resembling steganography, which obfuscates information in digital media resembling photos, audio tracks, video clips, or textual content information. A 2018 report from ClearSky Cyber Safety, MuddyWater Operations in Lebanon and Oman, additionally paperwork this utilization, sharing hashes for malware hidden in a number of pretend resumes – MyCV.doc. ESET detects the obfuscated malware as VBA/TrojanDownloader.Agent.
Whereas 4 years have handed for the reason that publication of the ClearSky report, and the quantity of ESET detections fell from seventh place (with 3.4%) in T3 2021 Risk Report to their most up-to-date rating in “final” place (with 1.8%) in T3 2022 Risk Report, VBA/TrojanDownloader.Agent remained in our high 10 malware detections chart.
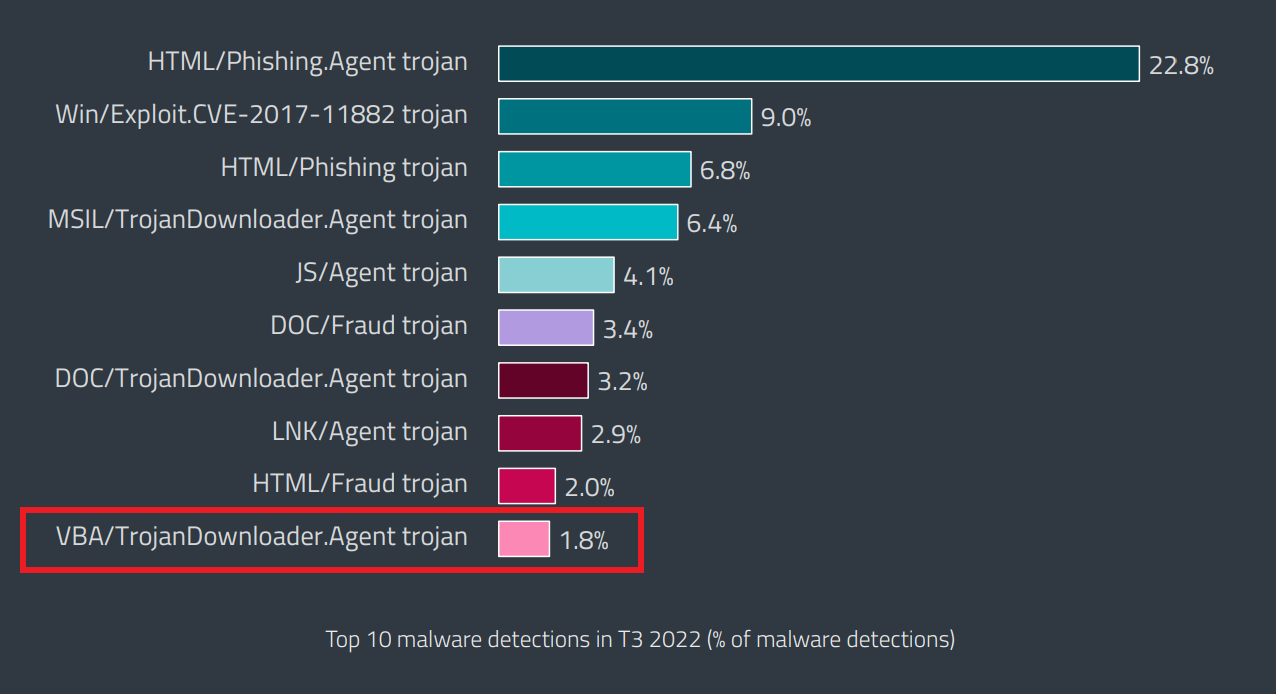
Detections of VBA/TrojanDownloader.Agent within the ESET T3 2022 Risk Report. (Observe: These detections regroup numerous malware households/scripts. As such, VBA/TrojanDownloader.Agent trojan proportion above isn’t an unique detection of MuddyWater’s use of this malware kind.)
VBA macros assaults leverage maliciously crafted Microsoft Workplace information and attempt to manipulate customers (together with MSP workers and shoppers) into enabling the execution of macros. If enabled, the enclosed malicious macro usually downloads and executes further malware. These malicious paperwork are normally despatched as electronic mail attachments disguised as necessary info related to the recipient.
A name to motion for MSPs and enterprises
MSP Admins, who configure main productiveness instruments like Microsoft Phrase/Workplace 365/Outlook, run their arms over the very risk vectors carrying threats to the networks they handle. Concurrently, SOC crew members could or could not have their very own EDR/XDR instruments properly configured to establish whether or not APTs like MuddyWater or prison entities try to leverage methods, together with steganography, to entry their very own or shoppers’ methods.
MSPs require each trusted community connectivity and privileged entry to buyer methods as a way to present providers; this implies they accumulate threat and duty for big numbers of shoppers. Importantly, shoppers also can inherit dangers from their chosen MSP’s exercise and setting. This has proven XDR to be a important instrument in supplying visibility into each their very own environments and buyer endpoints, units, and networks to make sure that rising threats, dangerous worker habits, and undesirable functions don’t threat their earnings or repute. The mature operation of XDR instruments by MSPs additionally communicates their lively position in offering a selected layer of safety for the privileged entry granted to them by shoppers.
When mature MSPs handle XDR, they’re in a significantly better place to counter a range of threats, together with APT teams which may search to leverage their shoppers’ place in each bodily and digital provide chains. As defenders, SOC groups and MSP admins carry a double burden, sustaining inside visibility and visibility into shoppers’ networks. Shoppers ought to be involved in regards to the safety stance of their MSPs and perceive the threats they face, lest a compromise of their supplier results in a compromise of themselves.
RELATED READING:
Selecting your MSP: What the Kaseya incident tells us about third‑occasion cyber‑threat
Legal hacking hits Managed Service Suppliers: Causes and responses




