OpenClaw began as a aspect undertaking of a developer who needed to make his (and others) life simpler with AI help. Clear mailbox, management schedule, set up ideas and listen to some music whereas his bot is doing all of the soiled jobs for him.
With vibe coding Peter Steinberger developed OpenClaw. Kudus for that. However since then other than altering its title twice it created an enormous chatter round two subjects. The AI hype and its cyber safety implications.
This undertaking has quickly moved from a distinct segment automation framework mentioned in developer communities to a subject showing throughout safety analysis feeds, Telegram channels, boards, and underground-adjacent chatter. Alongside it, names like ClawDBot and MoltBot have appeared in the identical narrative house, typically framed as malicious derivatives, companion tooling, or botnet-like ecosystems.
Nevertheless, when Flare checked out aggregated telemetry throughout open sources, social platforms, and fringe underground discussions, a extra nuanced story emerges.
The information suggests an actual supply-chain safety danger, however one which has not but been totally weaponized right into a mass-exploitation ecosystem. As a substitute, the dialog seems largely pushed by safety analysis amplification, platform hype cycles, and early-stage experimentation.
What OpenClaw Is: AI Automation Framework With Plugin Market
OpenClaw is an AI-powered automation framework that permits customers to handle emails, schedules, and system duties by modular “expertise”—user-installable plugins that execute instructions on behalf of customers.
The platform structure contains:
- Native or distant agent nodes that run automation duties
- A expertise market (ClawHub) the place customers obtain plugins
- API integrations for exterior companies (SSH, cloud platforms, productiveness instruments)
- Centralized orchestration by gateway elements
Conceptually, OpenClaw behaves much less like a single utility and extra like a light-weight automation working setting. That architectural mannequin is highly effective and in addition creates a big assault floor.
The second execution logic turns into modular and user-installable, the platform inherits the identical dangers traditionally seen in:
- Browser extension ecosystems
- Package deal managers (npm, PyPI, RubyGems)
- IDE plugin shops
- CI/CD automation marketplaces
OpenClaw’s expertise ecosystem is the place many of the actual safety dialogue presently lives.
This undertaking has quickly moved from a distinct segment automation framework mentioned in developer communities to a subject showing throughout safety analysis feeds, Telegram channels, boards, and underground-adjacent chatter.
Clawdbot (the unique title) was launched in November 2025, however the true hype started throughout January 2026, as mirrored in Flare’s menace monitoring platform:
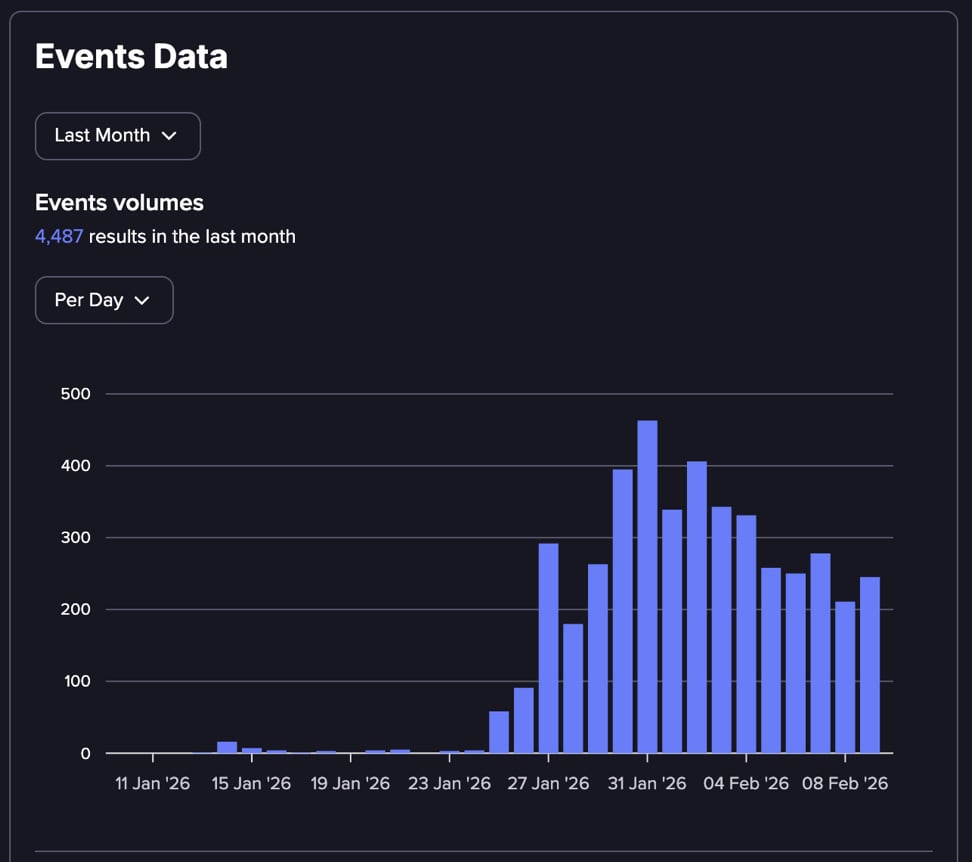
Alongside it, names like ClawdBot and MoltBot have appeared in the identical narrative house, typically framed as malicious derivatives, companion tooling, or botnet-like ecosystems.
Nevertheless, when inspecting aggregated telemetry throughout open sources, social platforms, and underground discussions, a extra nuanced story emerges. The information suggests an actual supply-chain safety danger, however not but a totally weaponized, mass-exploitation ecosystem. As a substitute, the dialog seems largely pushed by safety analysis amplification, platform hype cycles, and early-stage experimentation.
Flare displays Telegram channels and darkish internet boards the place menace actors share malicious automation instruments, poisoned plugins, and credential-stealing exploits.
Detect when your infrastructure seems in attacker discussions earlier than harm happens.
Vital Safety Flaws Allow Distant Code Execution and Credential Theft
Safety researchers recognized a number of vital vulnerabilities that made OpenClaw a lovely goal for provide chain assaults:
Confirmed Vital Vulnerabilities:
CVE-2026-25253 (One-click RCE): Malicious hyperlinks can steal authentication tokens and set off distant code execution with out requiring ability set up—attackers can compromise techniques by a single click on.
Malicious Ability Provide Chain: Lots of of poisoned expertise uploaded to ClawHub delivering infostealers, distant entry trojans (RATs), and backdoors disguised as reputable automation instruments.
No Ability Sandboxing: Expertise execute with full agent and system permissions, permitting malware to entry credentials, information, and community sources with out restriction.
Immediate Injection Assaults: Malicious content material can manipulate AI brokers into executing attacker-controlled workflows by pure language instructions, bypassing conventional software program vulnerabilities.
Token and OAuth Abuse: Attackers leverage stolen or inherited authentication tokens to set off reputable API actions, making malicious exercise seem approved.
Frequent Deployment Misconfigurations:
-
Brokers working with root or extreme system privileges
-
Publicly uncovered OpenClaw situations with weak authentication
-
Expertise dynamically pulling and executing distant code
-
Shadow deployments working exterior safety group visibility
Rising Assault Patterns:
As soon as executed, these malicious expertise harvest credentials, session cookies, and delicate knowledge from the compromised system, packaging them into stealer logs distributed by underground markets.
Underground Boards Present Restricted Exploitation Regardless of Excessive Dialogue Quantity
Flare’s evaluation of underground discussions reveals an rising menace panorama that hasn’t but reached mass felony operationalization:
Dataset Evaluation
Throughout 2,764 collected data from underground boards and Telegram channels:
-
OpenClaw mentions: 3,072
-
ClawDBot mentions: 1,365
-
MoltBot mentions: 864
-
ClawHub market references: 90
Nevertheless, breaking down the dialogue sorts exhibits:
-
Expertise safety discussions: 193 mentions
-
ClawHub ecosystem references: 110 mentions
-
Infostealer references: 53 mentions
-
Botnet orchestration: 8 mentions
-
DDoS infrastructure: 7 mentions
What This Distribution Reveals
If OpenClaw had been already weaponized at scale for mass exploitation, underground boards would sometimes present:
-
Energetic instrument gross sales and entry dealer choices
-
Botnet panel discussions and leaked administration interfaces
-
Established monetization threads with pricing buildings
-
Industrial exploitation companies
As a substitute, the dialog consists primarily of:
-
Safety analysis experiences and technical evaluation
-
Platform danger hypothesis and proof-of-concept discussions
-
Early-stage experimentation with out business operations
-
Instrument confusion throughout totally different communities (ClawDBot vs MoltBot naming)
This provide chain poisoning method mirrors ways seen in conventional infostealer distribution campaigns, the place attackers disguise malware as reputable software program to compromise consumer techniques at scale.
The One Space That Is Actual: Provide Chain Ability Abuse
The strongest confirmed danger sample presently seen is:
-
Malicious ability distribution.
-
Execution inside trusted automation context.
-
Payload run – Credential / session / knowledge exfiltration.
This is sufficient to be harmful, even with out botnet-scale weaponization.
Automation frameworks collapse the space between preliminary entry and privileged execution. If a malicious ability lands inside a trusted agent, the attacker successfully inherits the permissions of the automation setting.
Why Safety Researchers Are Driving the Dialog
The most definitely clarification for the present OpenClaw hype cycle is timing. OpenClaw sits on the intersection of three main developments:
-
Agentic automation platforms
-
Plugin market belief fashions
-
AI-assisted workflow execution
Safety researchers are likely to detect these dangers early, earlier than felony ecosystems totally monetize them.
Conclusion: Excessive Danger Potential, Early Exploitation Stage
The mixed dataset means that OpenClaw will not be presently exhibiting indicators of mass felony operationalization at scale.
As a substitute, what we see is:
-
An actual supply-chain danger floor (expertise ecosystem)
-
Heavy research-driven dialogue quantity
-
Early experimentation and PoC-level malicious functionality
-
Sturdy narrative amplification throughout social and fringe underground channels
The safety neighborhood is speaking about OpenClaw greater than menace actors are presently exploiting it. Having stated that, this isn’t a motive to disregard it. Traditionally, this part typically precedes actual weaponization by weeks or months.
The lesson from OpenClaw is much less about one framework and extra a few broader shift.
Automation platforms with plugin ecosystems have gotten high-value targets lengthy earlier than organizations understand they’ve deployed them at scale.
Study extra by signing up for our free trial.
Sponsored and written by Flare.


