
At present, at Wild West Hackin’ Fest, safety researcher Wietze Beukema disclosed a number of vulnerabilities in Home windows LK shortcut recordsdata that permit attackers to deploy malicious payloads.
Beukema documented 4 beforehand unknown strategies for manipulating Home windows LNK shortcut recordsdata to cover malicious targets from customers inspecting file properties.
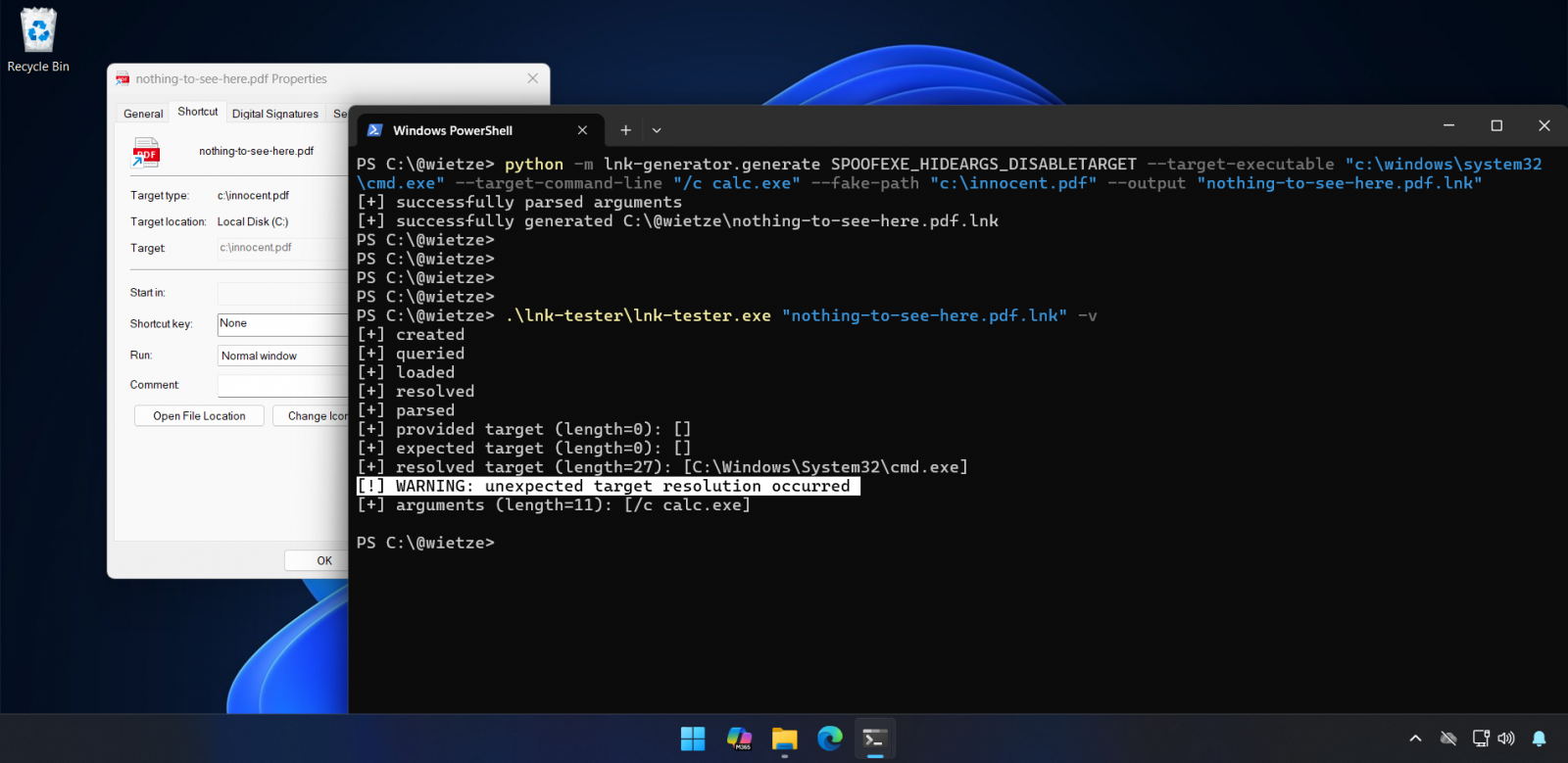
LNK shortcuts had been launched with Home windows 95 and use a fancy binary format that enables attackers to create misleading recordsdata that seem respectable in Home windows Explorer’s properties dialog however execute fully totally different packages when opened.
The found points exploit inconsistencies in how Home windows Explorer prioritizes conflicting goal paths specified throughout a number of non-obligatory knowledge buildings inside shortcut recordsdata.
The simplest variants use forbidden Home windows path characters, resembling double quotes, to create seemingly legitimate however technically invalid paths, inflicting Explorer to show one goal whereas executing one other, whereas one other makes use of non-conforming LinkTargetIDList values to execute a path aside from the one displayed within the LinkInfo discipline.
“This ends in the unusual scenario the place the consumer sees one path within the Goal discipline, however upon execution, a very different path is executed. Because of the discipline being disabled, it’s also potential to “disguise” any command- line arguments which are supplied,” Beukema mentioned.
Essentially the most highly effective method recognized includes manipulating the EnvironmentVariableDataBlock construction inside LNK recordsdata. By setting solely the ANSI goal discipline and leaving the Unicode discipline empty, attackers can show a pretend goal resembling “bill.pdf” within the properties window whereas truly executing PowerShell or different malicious instructions.
“Opening the LNK executes the “precise” goal instantly, not having to open it twice. Moreover, as a result of on this case the spoofed goal is in TargetIdList and the precise goal in EnvironmentVariableDataBlock, the precise goal could utilise surroundings variables,” Beukema defined.
“The goal program/file/listing is totally spoofed,” and “any command-line arguments are hidden,” the researcher additionally famous, which makes detection extraordinarily tough for customers.
That is potential as a result of, as Beukema mentioned, Home windows Explorer will deal with all these malformed LNK shortcuts forgivingly, displaying spoofed info slightly than rejecting invalid recordsdata.
The researcher has additionally launched “lnk-it-up,” an open-source instrument suite that generates Home windows LNK shortcuts utilizing these strategies for testing and might establish doubtlessly malicious LNK recordsdata by predicting what Explorer shows versus what truly executes.
MSRC: Not a vulnerability
When Beukema submitted the EnvironmentVariableDataBlock difficulty to the Microsoft Safety Response Middle in September (VULN-162145), Microsoft declined to categorise it as a safety vulnerability, arguing that exploitation requires consumer interplay and doesn’t breach safety boundaries.
“These strategies don’t meet the bar for rapid servicing underneath our severity classification pointers as they require an attacker to trick a consumer into operating a malicious file,” a Microsoft spokesperson advised BleepingComputer when requested whether or not the corporate plans to deal with any of the failings.
“Microsoft Defender has detections in place to establish and block this menace exercise, and Sensible App Management supplies an extra layer of safety by blocking malicious recordsdata from the Web. As a safety greatest apply, we strongly encourage clients to heed safety warnings and keep away from opening recordsdata from unknown sources.”
Microsoft additionally famous that Home windows identifies shortcut recordsdata (.lnk) as doubtlessly harmful and, when making an attempt to open a .lnk file downloaded from the Web, robotically triggers a safety warning advising customers to not open recordsdata from unknown sources. Microsoft strongly recommends heeding this warning.
Nevertheless, Beukema added that “there’s a cause attackers nonetheless like LNK recordsdata – customers rapidly click on via these kinds of warnings. In any other case, CVE-2025-9491 would not have been as ‘profitable’ because it was both.”
CVE-2025-9491, the safety vulnerability talked about by the safety researchers, is just like the problems Beukema found and might be exploited to cover command-line arguments through the use of extreme whitespace padding. Cybercrime teams and state-backed hacking teams from North Korea, Iran, Russia, and China have been abusing this safety flaw for years in zero-day assaults.
Whereas initially Microsoft mentioned that CVE-2025-9491 does not break safety boundaries and refused to repair the problem, it silently modified LNK recordsdata in June 2025 in an obvious effort to mitigate this actively exploited vulnerability.
As Pattern Micro menace analysts revealed in March 2025, CVE-2025-9491 was already being extensively exploited by no less than 11 state-sponsored teams and cybercrime gangs, together with Evil Corp, Bitter, APT37, APT43 (also called Kimsuky), Mustang Panda, SideWinder, RedHotel, Konni, and others.
Cybersecurity agency Arctic Wolf additionally reported in October that the Mustang Panda Chinese language state-backed hacking group was exploiting this Home windows vulnerability in zero-day assaults focusing on European diplomats in Hungary, Belgium, and different European nations to deploy the PlugX distant entry trojan (RAT) malware.




