When company information is uncovered on a devoted leak web site, the implications linger lengthy after the assault fades from the information cycle
12 Feb 2026
•
,
6 min. learn

Within the realm of cybercrime, change is arguably the one fixed. Whereas cyber-extortion as a broader class of crime has proved its endurance, ransomware – its arguably most damaging ‘taste’ – doesn’t reside or die on encryption alone. The playbook of ‘yore’ largely concerned locking information or programs and demanding fee for a decryption key, however lately campaigns switched to combining encryption with information exfiltration and threats to publish the stolen info.
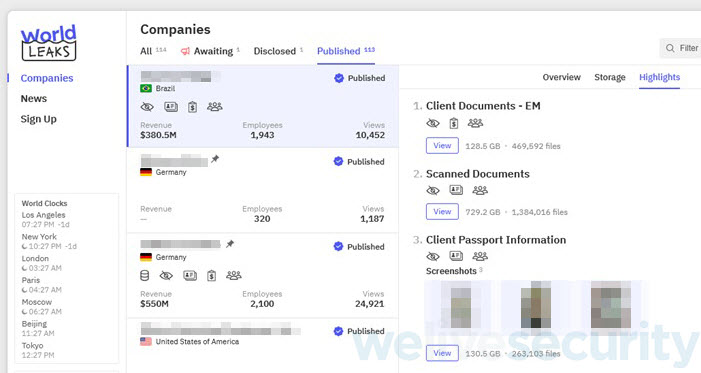
That is the place devoted leak websites, or information leak websites (DLSs), are available in. First showing in late 2019, DLSs have since grow to be the spine of the double extortion technique. Risk actors steal company information (earlier than encrypting it) after which weaponize the loot publicly, successfully turning a safety incident right into a full-blown public disaster.
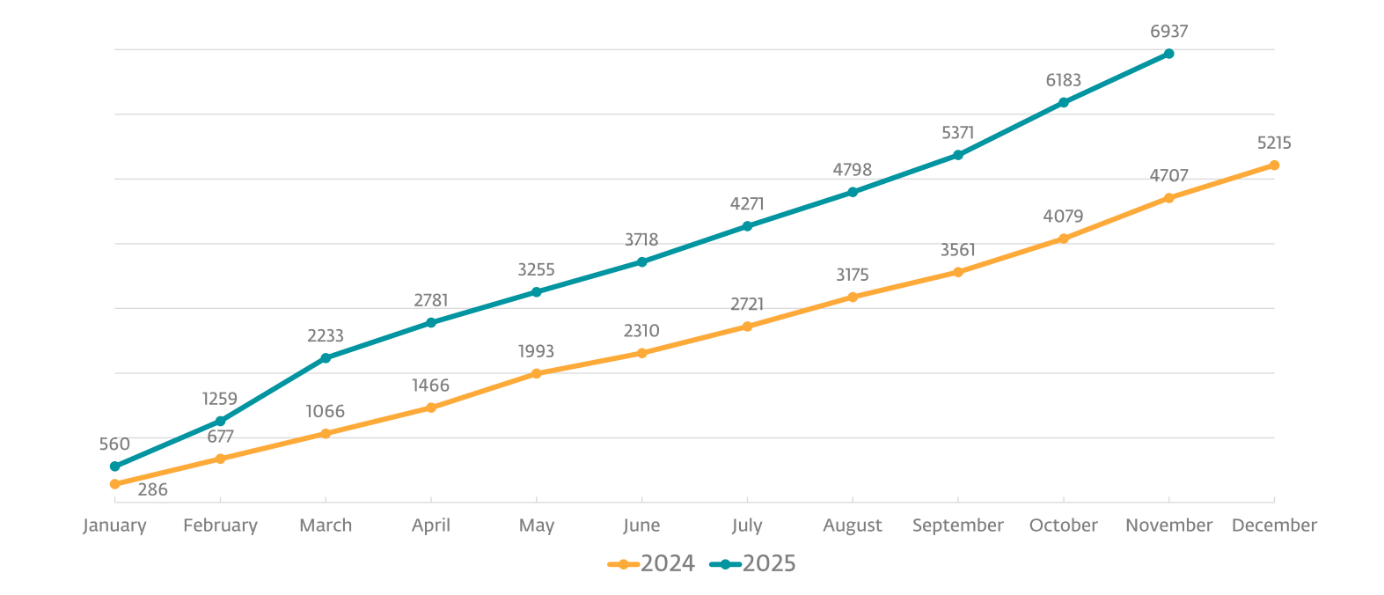
Safety consultants and legislation enforcement have, after all, been monitoring this shift for years. The FBI and CISA now routinely describe ransomware as a “information theft and extortion” drawback. Public monitoring tasks corresponding to Ransomware.reside level in the identical path, even when exact sufferer counts needs to be handled with warning. The leak websites replicate solely what criminals select to ‘promote’, not the total universe of incidents.
Let’s look at the function of DLSs within the ransomware ecosystem and the implications for sufferer organizations.
How do ransomware teams use information leak websites?
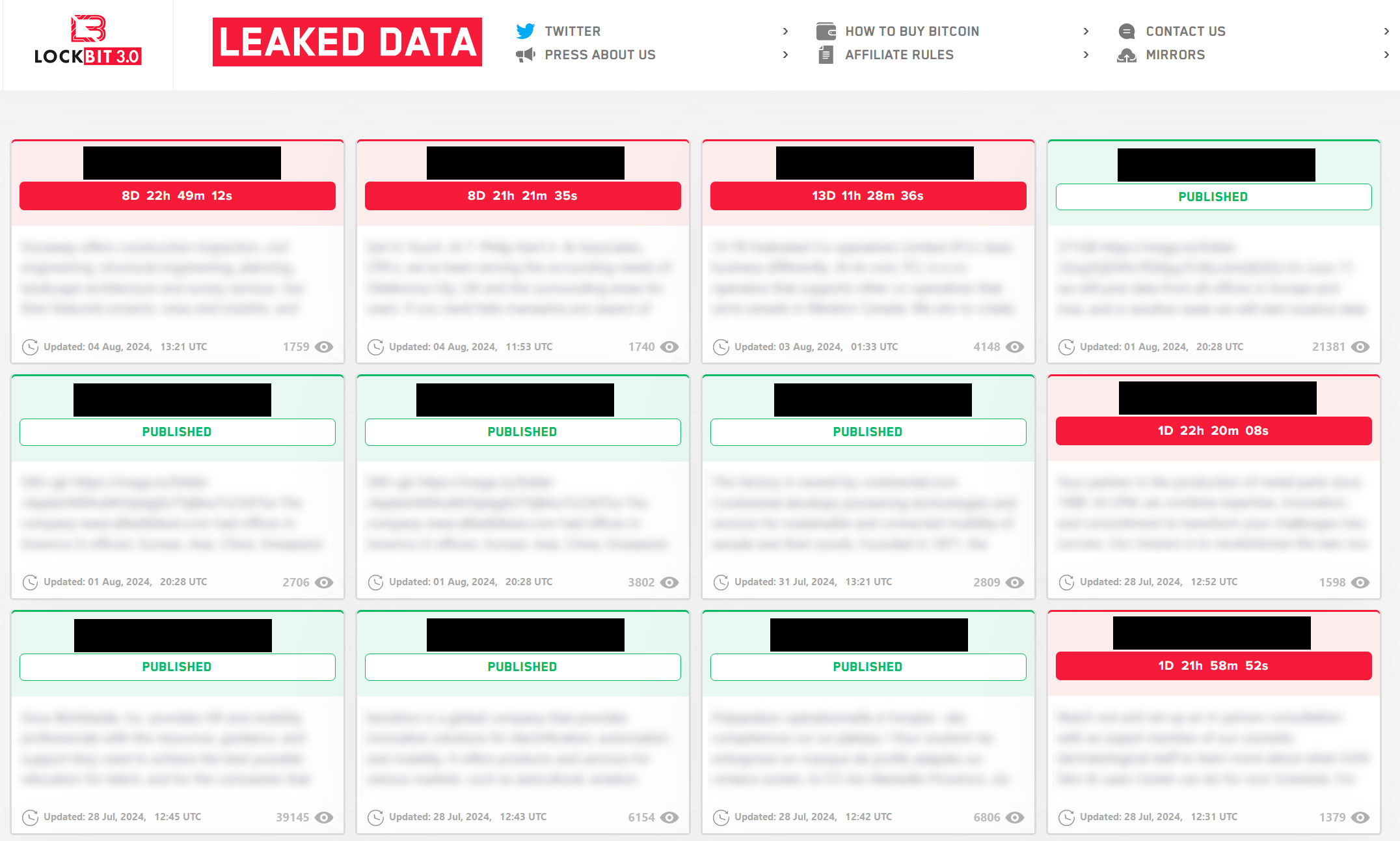
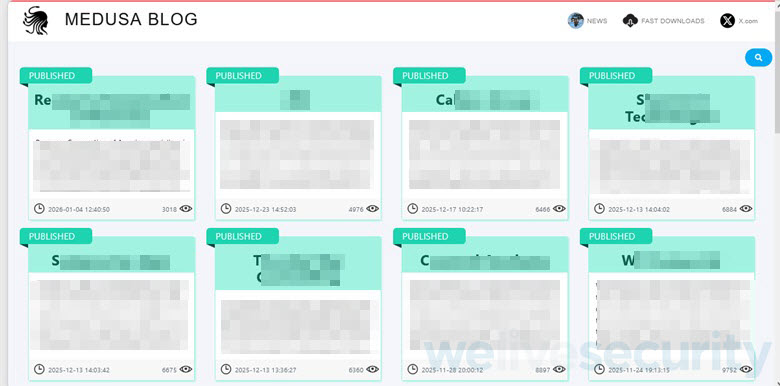
Hosted on the darkish net and accessible by the Tor community, the websites typically publish a pattern of stolen information and threaten victims with full public disclosure except fee is made. Generally the fabric is printed after the sufferer refused to collapse, thus additional turning the screw on them. Details about the victims, the extent of stolen materials and even deadlines that should really feel inexorable are all a part of the technique.
What makes the technique devastating is pace and amplification. As soon as the incident is within the open, a number of dangers are collapsed right into a single, extremely seen second and the sufferer group operates below a cloud of suspicion and uncertainty – typically even earlier than its IT and safety workers have a full image of what was stolen or how far the intrusion unfold. And that’s, after all, the purpose – information leak websites are a coercion instrument.
That is additionally why they’re fastidiously curated. Attackers typically publish simply sufficient materials to point out that they don’t seem to be bluffing: a handful of contracts or a tranche of emails. Extra is coming except the sufferer caves in.
Certainly, the harm not often stops with the preliminary sufferer. The info, as soon as dumped or resold, turns into gas for follow-on crime, and safety groups see it reappear in phishing kits, enterprise electronic mail compromise (BEC) campaigns, and identification fraud schemes. In supply-chain incidents, one breach can ripple outward, exposing the sufferer’s prospects and companions. This cascading impact is partly why authorities deal with ransomware as a systemic threat, relatively than a sequence of remoted mishaps.
Stress by design
Each aspect of a leak web site is designed to maximise psychological stress.
- Proof of unauthorized entry. The gangs put up pattern paperwork, corresponding to contracts and inside emails, to display that the intrusion was actual and the menace is credible.
- Urgency: Timers and countdowns instill the sensation that point is working out as choices made below time stress usually tend to favor the get together that controls the clock.
- Public publicity: Even when the stolen information is rarely launched publicly, the mere affiliation with a breach triggers reputational hurt that may take years to restore.
- Regulatory threat: Underneath frameworks like GDPR, HIPAA, and an increasing patchwork of state-level privateness legal guidelines within the US, a confirmed breach involving private information can set off necessary disclosures, investigations, and fines..
Past extortion
Some ransomware-as-a-service (RaaS) operators have expanded what leak websites do. LockBit, earlier than its infrastructure was seized by legislation enforcement in early 2024, ran a bug bounty program on its leak web site, providing funds to anybody who discovered vulnerabilities of their code.
Others put up ‘gigs’ for company insiders, providing fee to staff prepared to supply login credentials or weaken safety controls. Nonetheless different websites double as onboarding platforms for the subsequent wave of attackers as attackers promote ‘affiliate packages’, explaining the income cut up and the way to apply.

Zooming out
Information leak websites work as a result of they hit corporations’ weak spots that transcend expertise. A possible information leak triggers a number of dangers without delay: reputational harm, misplaced belief amongst prospects and companions, monetary hits, regulatory sanctions, and litigation.
As ransomware gangs additionally promote the stolen info, they feed markets for stolen information and allow follow-on assaults. Some teams have even been noticed skipping encryption totally and as an alternative ‘solely’ seize information and threaten to publish it.
The victims, in the meantime, should make choices with out sufficient time to consider the implications. The individuals whose private info is caught up within the incident face an extended tail of cleanup, attainable account takeovers and identification fraud.
In opposition to that backdrop, paying up would possibly seem like the (comparatively) straightforward means out or the least dangerous choice. It’s neither. Fee doesn’t assure file or system restoration, nor does it assure that the information stays personal. Many organizations that paid up have been hit once more inside months. And each fee helps fund the subsequent assault.
For organizations, the ransomware menace calls for complete defensive measures, which embody:
- Deploying superior safety options with EDR/XDR/MDR capabilities. Amongst different issues, they monitor anomalous habits, corresponding to unauthorized course of execution and suspicious lateral motion, to cease the menace in its tracks. Certainly, the merchandise are a thorn in criminals‘ sides, who more and more deploy EDR killers in an try to terminate or crash safety merchandise, usually by abusing weak drivers.
- Limiting lateral motion by well-defined, stringent entry controls. Zero-Belief rules improve an organization’s safety posture by eliminating default belief assumptions for any entity. Risk actors typically exploit compromised login credentials and distant desktop protocol entry to manually navigate networks.
- Hold all of your software program up-to-date. Recognized vulnerabilities are one of many major entry vectors for ransomware actors.
- Sustaining backups saved in remoted, air-gapped environments that ransomware can not entry or modify. Ransomware’s major goal is to find and encrypt delicate information. Worse, even when victims pay ransoms, flawed decryption processes may end up in everlasting information loss, to not point out different attainable ramifications of paying the ransom. Resilient backups and ransomware remediation capabilities go a great distance in direction of mitigating harm from the menace.
- Human vigilance, additional refined by well-designed safety consciousness coaching, additionally represents a extremely efficient defensive barrier. An worker who can spot a malicious electronic mail early on removes one in every of ransomware actors’ favourite entry factors, and that alone can markedly minimize the danger of an assault victimizing your whole group.
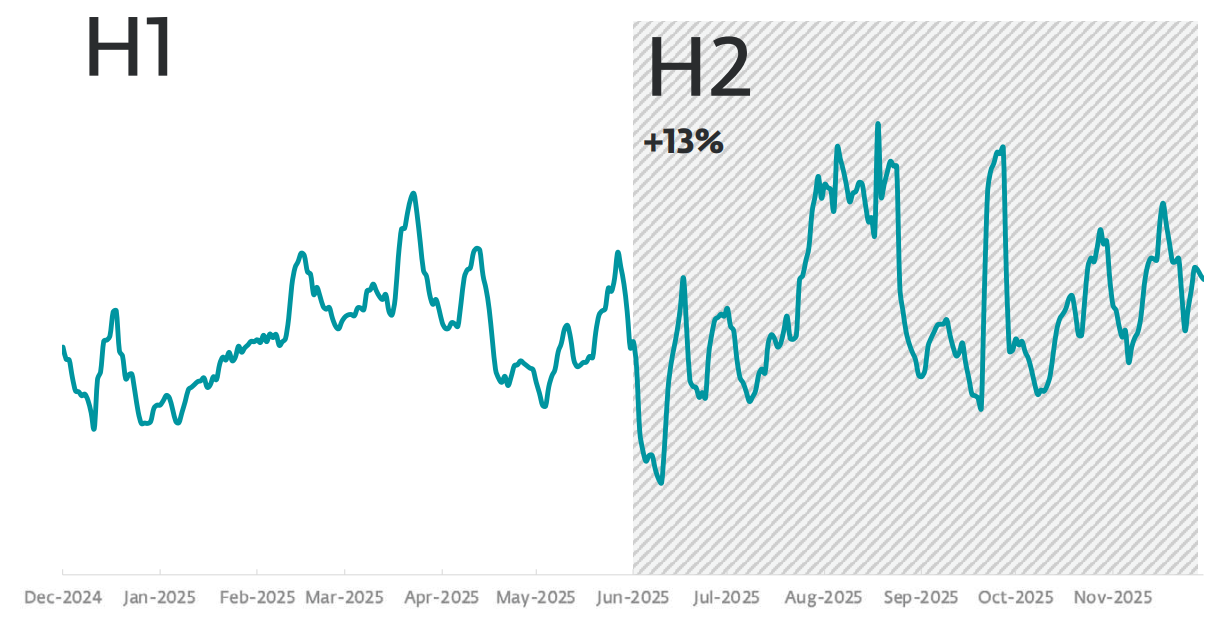
The ransomware evolution continues unabated because the ransomware-as-a-service (RaaS) mannequin continues to draw a large prison person base and grants quite a few threats longevity and adaptableness. So long as criminals can reliably flip stolen information right into a public spectacle, they may preserve doing it and ransomware will stay a cash machine.