
A faux 7-Zip web site is distributing a trojanized installer of the favored archiving software that turns the consumer’s laptop right into a residential proxy node.
Residential proxy networks use residence consumer units to route visitors with the objective of evading blocks and performing numerous malicious actions reminiscent of credential stuffing, phishing, and malware distribution.
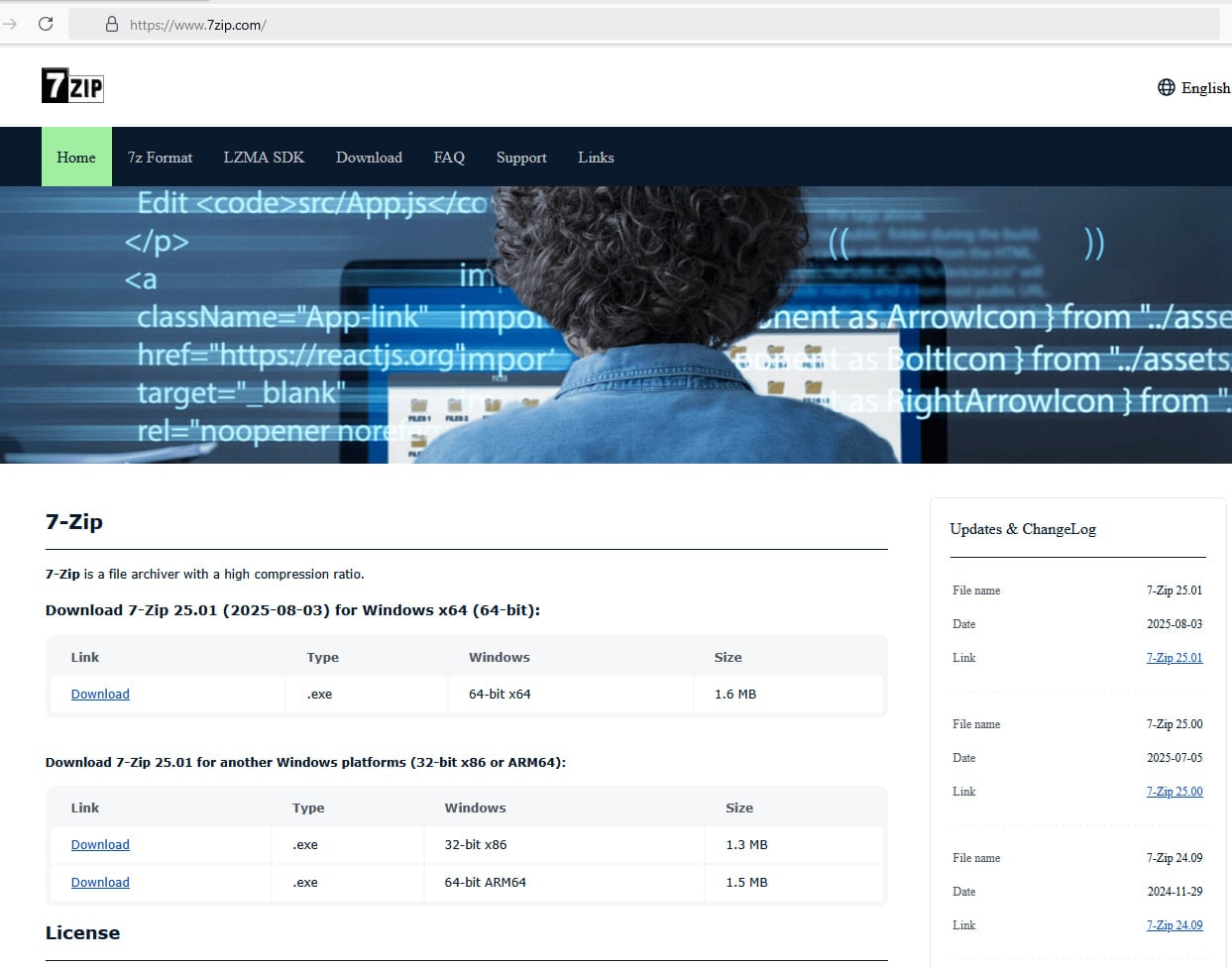
The brand new marketing campaign turned higher recognized after a consumer reported that they downloaded a malicious installer from a web site impersonating the 7-Zip challenge whereas following directions in a YouTube tutorial on constructing a PC system. BleepingComputer can verify that the malicious web site, 7zip[.]com, continues to be stay.
The menace actor registered the area 7zip[.]com (nonetheless stay on the time of writing) that may simply trick customers into considering they landed on the positioning of the reputable software.
Moreover, the attacker copied the textual content and mimicked the construction of the unique 7-Zip web site situated at 7-zip.org.
Supply: BleepingComputer
The installer file was analyzed by researchers at cybersecurity firm Malwarebytes, who discovered that it’s digitally signed with a now-revoked certificates initially issued to Jozeal Community Know-how Co., Restricted.
The malicious copy additionally incorporates the 7-Zip program, thus offering the common features of the software. Nonetheless, the installer drops three malicious recordsdata:
- Uphero.exe – service supervisor and replace loader
- hero.exe – predominant proxy payload
- hero.dll – help library
These recordsdata are positioned within the ‘C:WindowsSysWOW64hero’ listing, and an auto-start Home windows service working as SYSTEM is created for the 2 malicious executables.
Moreover, firewall guidelines are modified utilizing ‘netsh’ to permit the binaries to ascertain inbound and outbound connections.
Finally, the host system is profiled with Microsoft’s Home windows Administration Instrumentation (WMI) and Home windows APIs to find out the {hardware}, reminiscence, CPU, disk, and community traits. The collected information is then despatched to ‘iplogger[.]org.’
“Whereas preliminary indicators instructed backdoor‑model capabilities, additional evaluation revealed that the malware’s main operate is proxyware,” Malwarebytes explains in regards to the malware’s operational objective.
“The contaminated host is enrolled as a residential proxy node, permitting third events to route visitors by means of the sufferer’s IP deal with.”
In response to the evaluation, hero.exe pulls config from rotating “smshero”-themed C2 domains, then opens outbound proxy connections on non-standard ports reminiscent of 1000 and 1002. Management messages are obfuscated utilizing a light-weight XOR key.
Malwarebytes discovered that the marketing campaign is bigger than the 7-Zip lure and in addition makes use of trojanized installers for HolaVPN, TikTok, WhatsApp, and Wire VPN.
The malware makes use of a rotating C2 infrastructure constructed round hero/smshero domains, with visitors going by means of the Cloudflare infrastructure and carried over TLS-encrypted HTTPs.
It additionally depends on DNS-over-HTTPS through Google’s resolver, which reduces visibility for defenders monitoring normal DNS visitors.
The malware additionally checks for virtualization platforms reminiscent of VMware, VirtualBox, QEMU, Parallels, in addition to for debuggers, to determine when it’s being analyzed.
Malwarebytes’ investigation began after noticing analysis from impartial safety researchers who analyzed the malware and uncovered its true function. Researcher Luke Acha found the aim of the Uphero/hero malware.
The xor-based communication protocol was reverse-engineered and decoded by s1dhy, who confirmed the proxy conduct. Digital forensics and incident response (DFIR) engineer Andrew Danis linked the faux 7-Zip installer to the bigger marketing campaign impersonating a number of software program manufacturers.
Malwarebytes lists indicators of compromise (domains, file paths, IP addresses) and host-related information noticed throughout their evaluation.
Customers are really useful to keep away from following URLs from YouTube movies or promoted search outcomes, and as an alternative bookmark the obtain portal domains for the software program they use usually.
Trendy IT infrastructure strikes quicker than guide workflows can deal with.
On this new Tines information, learn the way your staff can scale back hidden guide delays, enhance reliability by means of automated response, and construct and scale clever workflows on high of instruments you already use.




