Most enterprise work now occurs within the browser. SaaS functions, identification suppliers, admin consoles, and AI instruments have made it the first interface for accessing knowledge and getting work finished.
But the browser stays peripheral to most safety architectures. Detection and investigation nonetheless deal with endpoints, networks, and e-mail, layers that sit across the browser, not inside it.
The result’s a rising disconnect. When employee-facing threats happen, safety groups typically battle to reply a primary query: what really occurs within the browser?
That hole defines a complete class of recent assaults.
At Hold Conscious, we’ve known as this a “protected haven” drawback for attackers, the place the goal has now develop into this central level of failure
Browser Assaults Seen in 2026 Leaving Little Conventional Proof
What makes browser-only assaults onerous to take care of isn’t a single method. It’s that a number of assault sorts all collapse into the identical visibility hole. We proceed to see these assaults into 2026:

ClickFix and UI-Pushed Social Engineering
Presumably the most important browser-driven assault vector in 2025, customers are guided by faux browser messages or prompts to repeat, paste, or submit delicate data themselves. No payload is delivered, no exploit fires, simply regular person actions that go away nearly no investigation path.
Malicious Extensions
Seemingly authentic extensions are put in deliberately after which quietly observe web page content material, intercept kind enter, or exfiltrate knowledge. From an endpoint or community perspective, all the pieces seems to be regular browser conduct. When questions come up later, there’s little document of what the extension really did.
Man-in-the-Browser (and AitB, BitB, …) Assaults
These assaults abuse legitimate browser periods quite than exploiting programs. Credentials are entered accurately, MFA is accepted, and exercise seems approved. Logs verify an actual person and an actual session, however not whether or not the browser interplay was manipulated or replayed.
HTML Smuggling
Malicious content material is assembled immediately contained in the browser utilizing JavaScript, bypassing conventional obtain and inspection factors. The browser renders content material as anticipated, whereas essentially the most vital steps by no means develop into first-class safety occasions.
Why EDR, E-mail, and SASE Miss These Assaults by Design
This isn’t a failure of instruments or groups. It’s a consequence of what these programs have been designed to see, and what they weren’t.
EDR focuses on processes, information, and reminiscence on the endpoint. E-mail safety tracks supply, hyperlinks, and attachments. SASE and proxy applied sciences implement coverage on site visitors transferring throughout the community. Every can block recognized unhealthy exercise, however none are constructed to know person interplay contained in the browser itself.
When the browser turns into the execution atmosphere, the place customers click on, paste, add, and authorize, each prevention and detection lose context. Actions could also be allowed or denied, however with out visibility into what really occurred, controls develop into blunt and investigations incomplete.
When browser interactions are seen, prevention turns into exact and defensible.
See how Hold Conscious permits groups to make use of browser-level knowledge to dam dangerous conduct and repeatedly refine coverage.
What Our Personal the Browser Analysis Reveals
This hole isn’t restricted to 1 browser or deployment mannequin.
As a part of Personal the Browser, a vendor-neutral analysis effort evaluating greater than 20 mainstream, enterprise, and AI-native browsers, we examined how browsers are literally secured and ruled in apply.
What stood out wasn’t a scarcity of controls; it was a scarcity of observable conduct that these controls might study from.
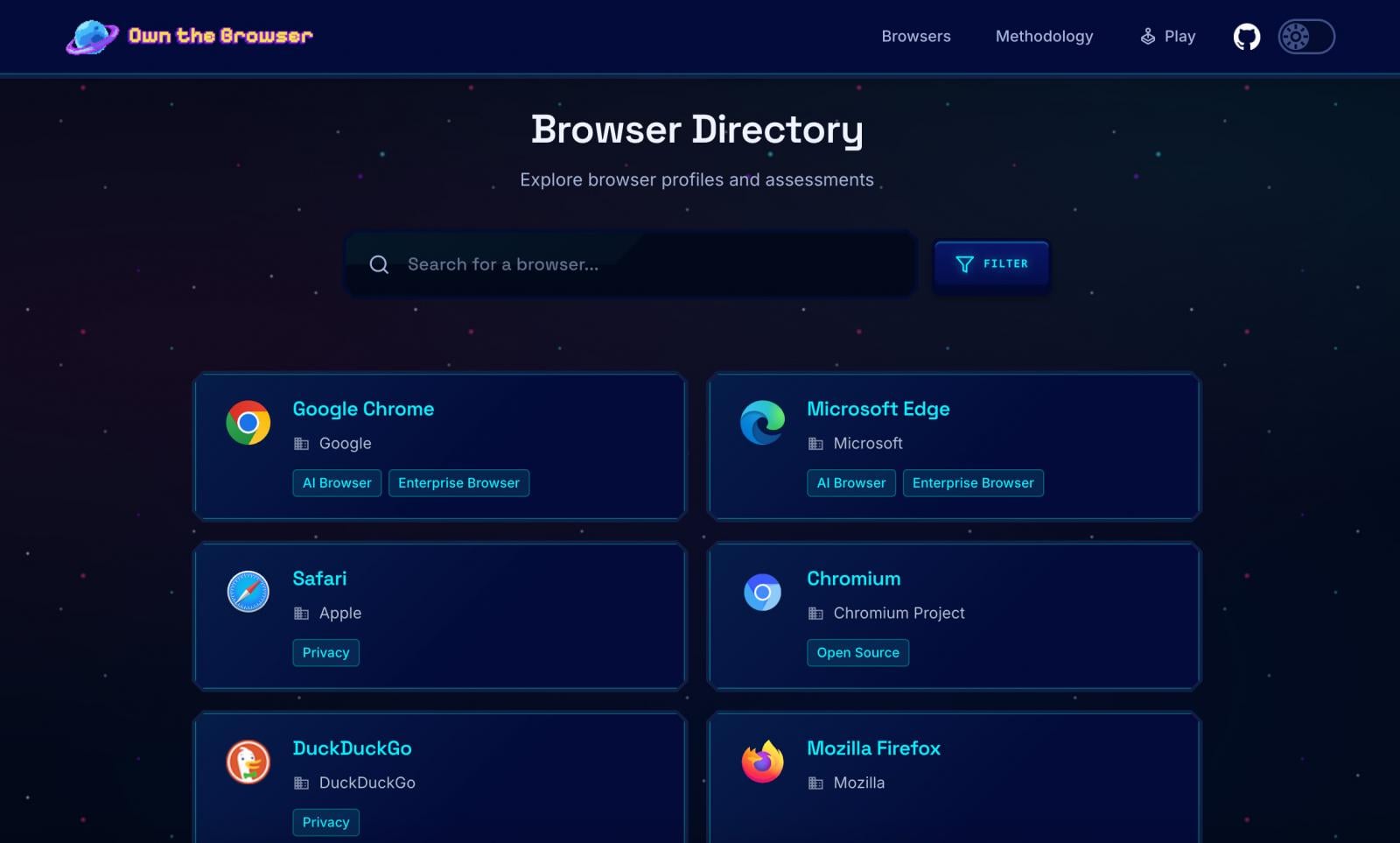
Throughout shopper, enterprise, and rising AI-native browsers, insurance policies are extensively deployed. What’s lacking is structured visibility into how these insurance policies really play out in actual person conduct. With out that perception, prevention stays blunt, and insurance policies not often evolve or enhance.
AI Instruments and AI-Native Browsers Are Widening the Hole
AI is accelerating this drawback by growing each the quantity and subtlety of browser-based knowledge motion.
Instruments like ChatGPT, Claude, and Gemini normalize copying, pasting, importing, and summarizing delicate data immediately within the browser. AI-native browsers, built-in assistants, and extensions streamline these actions even additional.
From a management standpoint, a lot of this exercise seems authentic. From a prevention standpoint, it’s troublesome to judge threat with out context.
Insurance policies can enable or block actions, however with out observability into how knowledge is getting used, groups can’t adapt controls to match actuality.
As AI-driven workflows develop into routine, prevention that isn’t knowledgeable by browser-level conduct rapidly falls behind.
What Browser-Degree Observability Adjustments: Earlier than and After Incidents
When browser exercise turns into observable, safety groups don’t simply examine higher; they forestall extra successfully.
Seeing how knowledge really strikes by the browser permits groups to set smarter, extra focused controls: stopping dangerous actions in the intervening time they happen, whereas preserving proof when one thing does go flawed.
Detection improves as a result of conduct may be evaluated in context. Response improves as a result of incidents are reconstructable. Insurance policies enhance as a result of they’re knowledgeable by actual utilization, not assumptions.
This creates a suggestions loop: observability informs prevention, prevention reduces threat, and each incident, blocked, paused, or allowed, sharpens coverage over time.
That results in a easy query: if this class of assault occurred in your atmosphere at the moment, might you each forestall it and clarify it? If not, that’s the hole Hold Conscious is constructed to shut. See what browser-level visibility permits throughout prevention and response.
Written by Ryan Boerner, CEO of Hold Conscious
Boerner, a pc engineer turned cybersecurity practitioner, started as a SOC analyst tackling community threats throughout Texas companies. Specializing in community and e-mail safety, he later honed his experience at IBM and Darktrace, working with organizations of all sizes. Seeing a vital hole between safety groups and workers—the place sturdy defenses nonetheless let threats by—he based Hold Conscious to make the browser a cornerstone of enterprise safety.
Sponsored and written by Hold Conscious.


