
A brand new DDoS (distributed denial of service) method named ‘HTTP/2 Speedy Reset’ has been actively exploited as a zero-day since August, breaking all earlier data in magnitude.
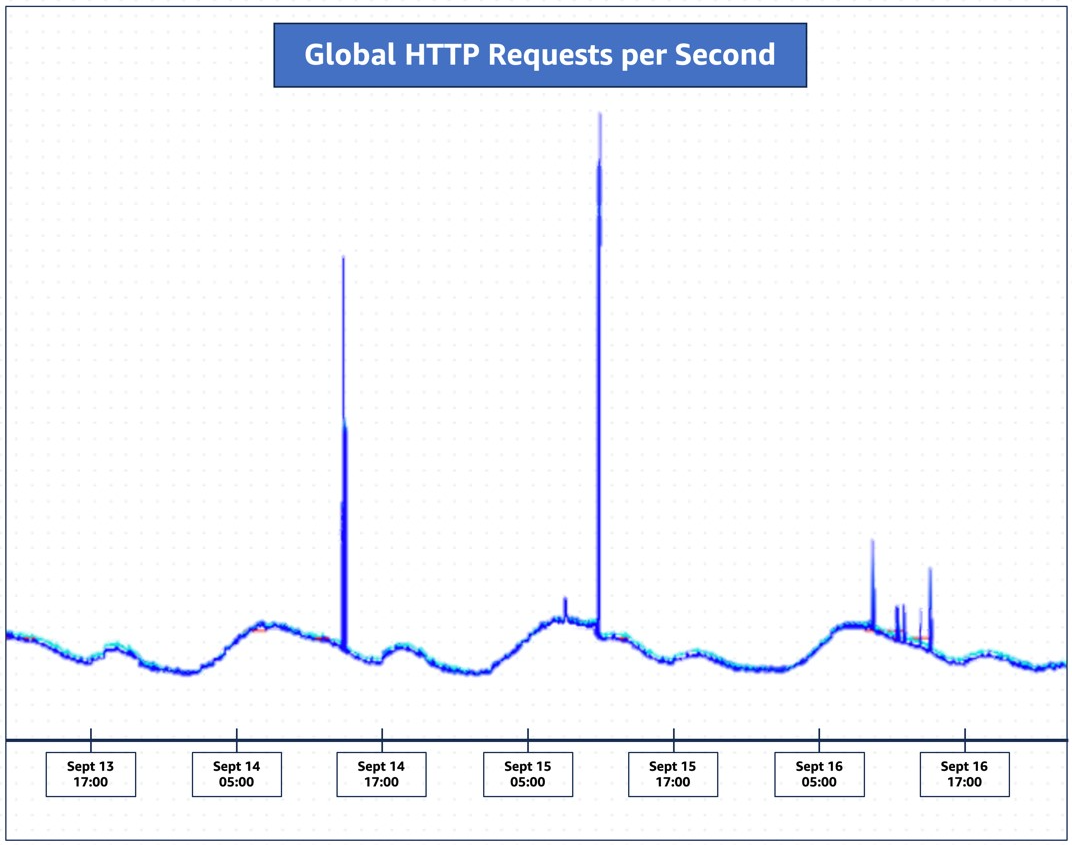
Information of the zero-day method comes as a coordinated announcement in the present day between Amazon Net Providers, Cloudflare, and Google, who report mitigating assaults reaching 155 million requests per second (Amazon) and 201 million rps (Cloudflare).
Cloudflare feedback that the scale of the assault is 3 times greater than its earlier report, from February 2023 (71 million rps), and it is alarming that this was achieved utilizing a comparatively small botnet comprising 20,000 machines.
Since late August, Cloudflare has detected and mitigated over a thousand ‘HTTP/2 Speedy Reset’ DDoS assaults that surpassed 10 million rps, with 184 breaking the earlier 71 million rps report.
Cloudflare is assured that as additional menace actors make use of extra expansive botnets together with this new assault methodology, HTTP/2 Speedy Reset assaults will proceed to interrupt even better data.
“There are botnets in the present day which are made up of lots of of hundreds or hundreds of thousands of machines,” feedback Cloudflare.
“On condition that the whole net sometimes sees solely between 1–3 billion requests per second, it is not inconceivable that utilizing this methodology may focus a complete net’s price of requests on a small variety of targets.”
HTTP/2 Speedy Reset particulars
The novel assault exploits a zero-day vulnerability tracked as CVE-2023-44487, which abuses a weak point within the HTTP/2 protocol.
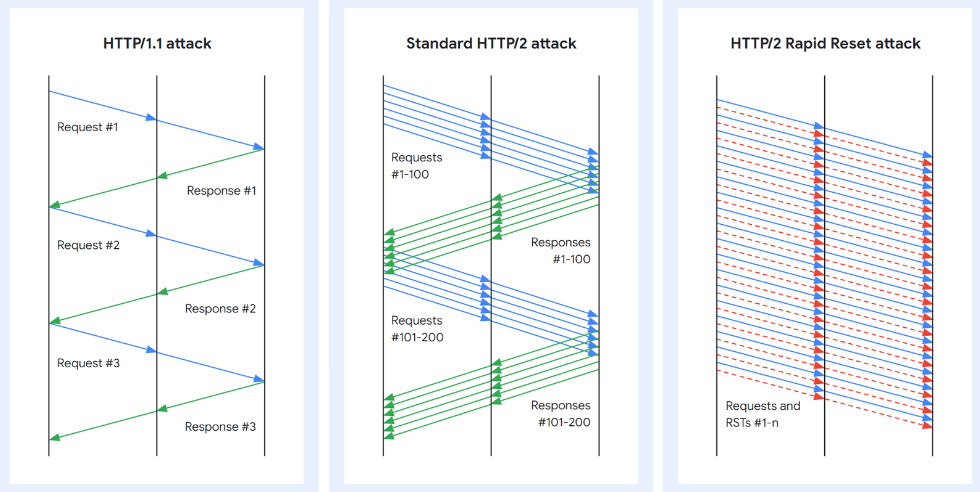
Merely put, the assault methodology abuses HTTP/2’s stream cancellation characteristic to constantly ship and cancel requests, overwhelming the goal server/software and imposing a DoS state.
HTTP/2 contains a safeguard within the type of a parameter that limits the variety of concurrently energetic streams to stop DoS assaults; nevertheless, this is not at all times efficient.
The protocol builders launched a extra environment friendly measure known as “request cancelation,” which does not tear down the entire connection however which may be abused.
Malicious actors have been abusing this characteristic since late August to ship a flurry of HTTP/2 requests and resets (RST_Stream frames) on a server, asking it to course of every of them and carry out fast resets, overwhelming its capability to reply to new incoming requests.
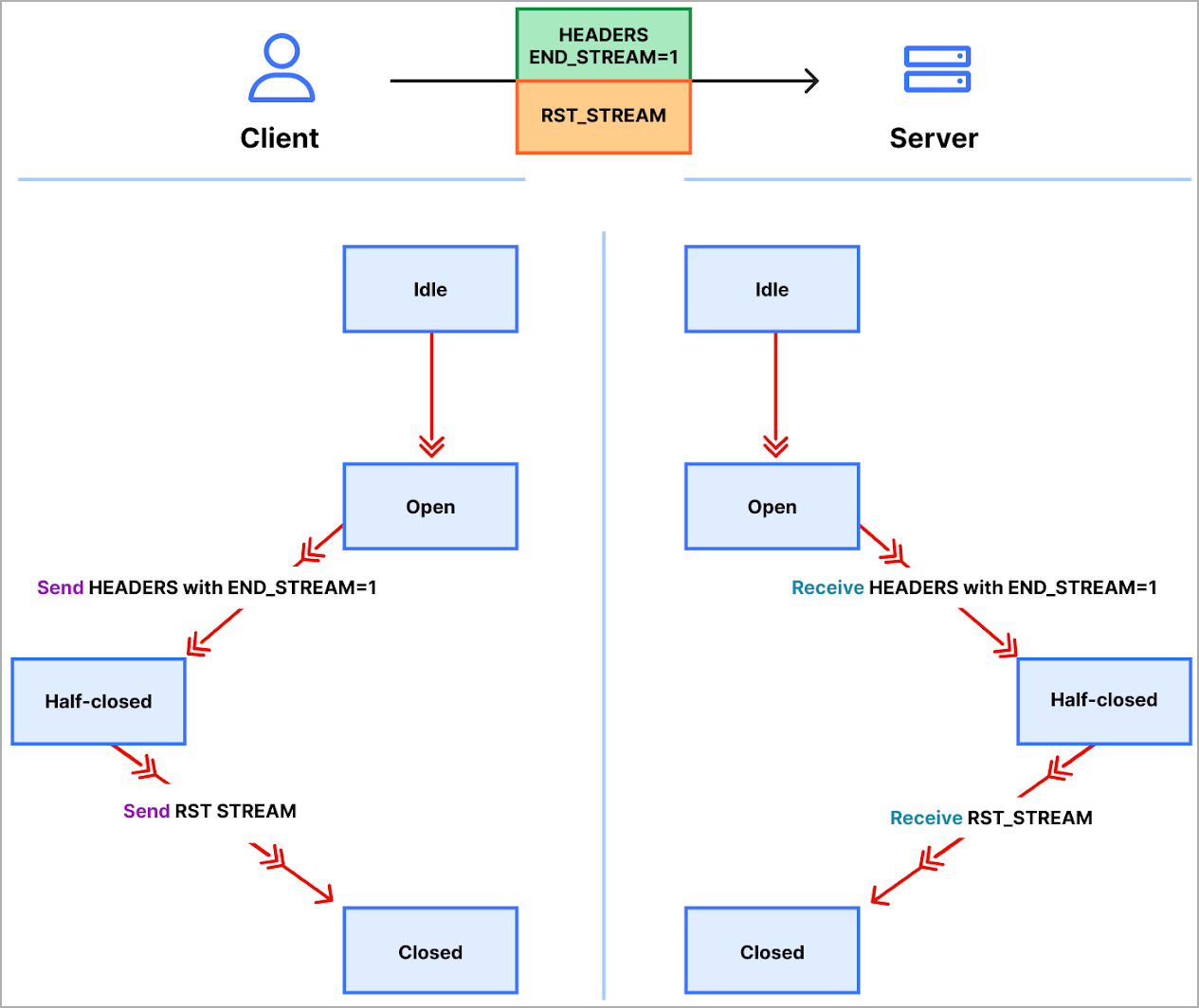
“The protocol doesn’t require the shopper and server to coordinate the cancelation in any means, the shopper might do it unilaterally,” explains Google in its submit on the difficulty.
“The shopper may additionally assume that the cancellation will take impact instantly when the server receives the RST_STREAM body, earlier than every other information from that TCP connection is processed.”
Suppliers develop mitigations
Cloudflare explains that HTTP/2 proxies or load-balancers are significantly inclined to these lengthy strings of reset requests despatched shortly.
The agency’s community was overwhelmed on the level between the TLS proxy and its upstream counterpart, so the injury was carried out earlier than the unhealthy requests reached the block level.
When it comes to real-world affect, these assaults have brought about a rise in 502 error experiences amongst Cloudflare’s shoppers.
Cloudflare says it will definitely mitigated these assaults utilizing a system designed to deal with hyper-volumetric assaults known as ‘IP Jail,’ which the web agency expanded to cowl its whole infrastructure.
This method “jails” offending IPs and bars them from utilizing HTTP/2 for any Cloudflare area for a time frame whereas impacting respectable customers sharing the jailed IP with a minor efficiency drop.
Amazon says it mitigated dozens of those assaults with out offering any particulars on their affect, highlighting that the supply of their buyer providers was maintained.
All three companies conclude that the perfect strategy for shoppers to counter HTTP/2 Speedy Reset assaults is to make use of all obtainable HTTP-flood safety instruments and bolster their DDoS resilience with multifaceted mitigations.
In a separate submit, Cloudflare explains that they needed to preserve the zero-day secret for over a month to permit safety distributors and stakeholders time to react to the menace earlier than it is made recognized to extra menace actors and the “cat and mouse” recreation begins.
“We have saved the knowledge restricted till in the present day to present as many safety distributors as doable the chance to react,” defined Cloudflare
“Nonetheless, sooner or later, the accountable factor turns into to publicly disclose zero-day threats like this. In the present day is that day.”


