
Ransomware operators are internet hosting and delivering malicious payloads at scale by abusing digital machines (VMs) provisioned by ISPsystem, a respectable digital infrastructure administration supplier.
Researchers at cybersecurity firm Sophos noticed the tactic whereas investigating latest ‘WantToCry’ ransomware incidents. They discovered the attackers used Home windows VMs with an identical hostnames, suggesting default templates generated by ISPsystem’s VMmanager.
Diving deeper, the researchers found that the identical hostnames have been current within the infrastructure of a number of ransomware operators, together with LockBit, Qilin, Conti, BlackCat/ALPHV, and Ursnif, in addition to numerous malware campaigns involving RedLine and Lummar info-stealers.
Supply: Sophos
ISPsystem is a respectable software program firm that develops management panels for internet hosting suppliers, used for the administration of digital servers, OS upkeep, and many others. VMmanager is the corporate’s virtualization administration platform used to spin up Home windows or Linux VMs for purchasers.
Sophos discovered that VMmanager’s default Home windows templates reuse the identical hostname and system identifiers each time they’re deployed.
Bulletproof internet hosting suppliers that knowingly help cybercrime operations and ignore takedown requests make the most of this design weak point. They permit malicious actors to spin up VMs by way of VMmanager, used for command-and-control (C2) and payload-delivery infrastructure.
This primarily hides malicious methods amongst hundreds of innocuous ones, complicates attribution, and makes fast takedowns unlikely.
The vast majority of the malicious VMs have been hosted by a small cluster of suppliers with a nasty repute or sanctions, together with Stark Industries Options Ltd., Zomro B.V., First Server Restricted, Companion Internet hosting LTD, and JSC IOT.
Sophos has additionally found a supplier with direct management of bodily infrastructure named MasterRDP, which makes use of VMmanager for evasion and provides VPS and RDP companies that don’t adjust to authorized requests.
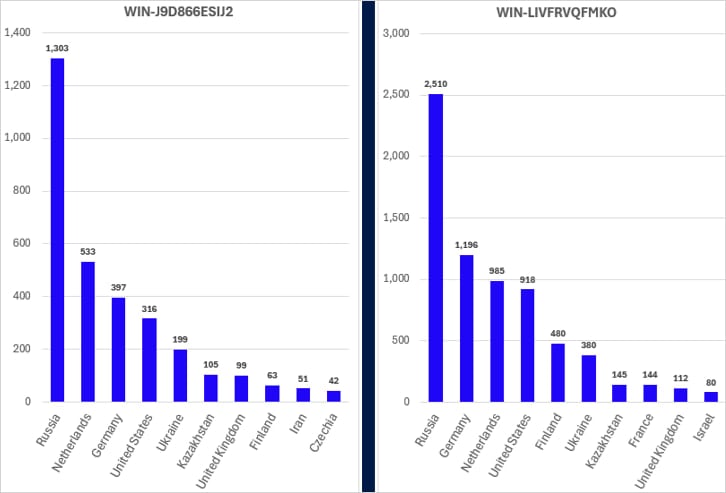
In response to Sophos, 4 of probably the most prevalent ISPsystem hotnames “account for over 95% of the whole variety of internet-facing ISPsystem digital machines:”
- WIN-LIVFRVQFMKO
- WIN-LIVFRVQFMKO
- WIN-344VU98D3RU
- WIN-J9D866ESIJ2
All of them have been current both in buyer detection or telemetry information linked to cybercriminal exercise.
The researchers be aware that whereas ISPsystem VMmanager is a respectable platform for virtualization administration, it is usually engaging to cybercriminals as a result of “its low value, low barrier to entry, and turnkey deployment capabilities.”
BleepingComputer has contacted ISPsystem to ask if they’re conscious of the large-scale abuse of VM templates and their plans to deal with the difficulty, however a press release wasn’t obtainable by publishing time.




