
A coordinated reconnaissance marketing campaign concentrating on Citrix NetScaler infrastructure over the previous week used tens of 1000’s of residential proxies to find login panels.
The exercise was noticed between January 28 and February 2, and it additionally centered on enumerating variations of the product, indicating an organized discovery effort.
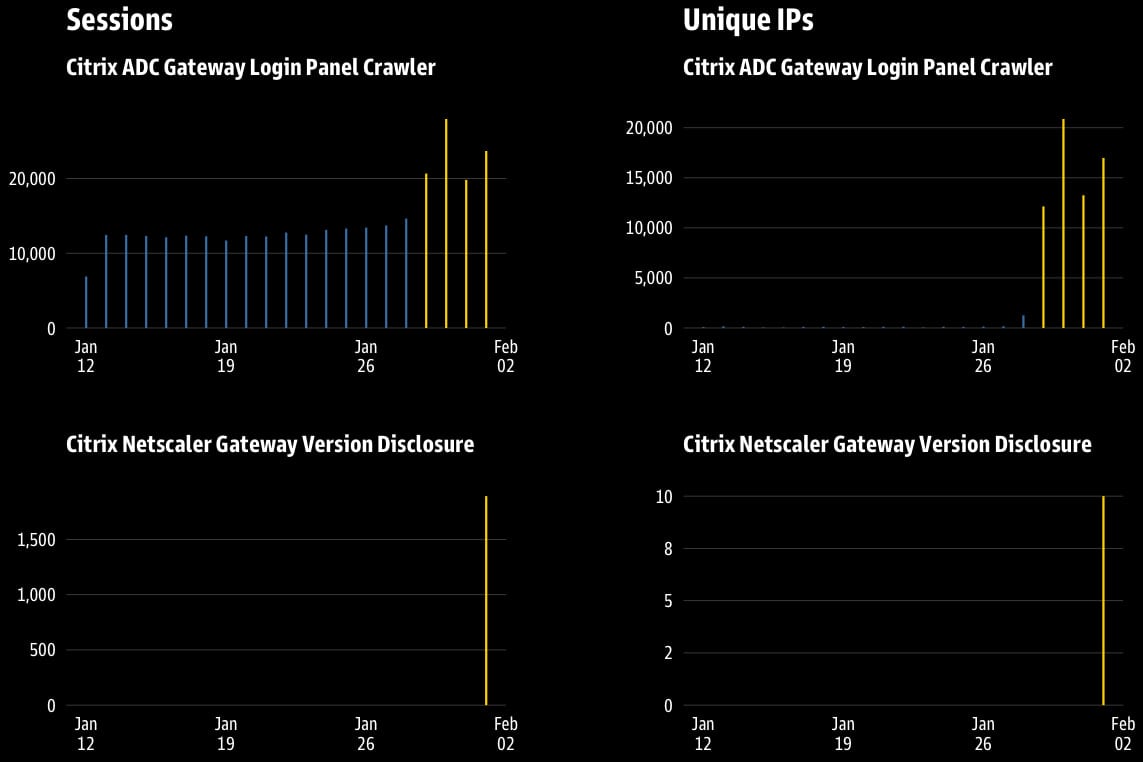
Risk monitoring platform GreyNoise traced the supply of the scanning visitors to greater than 63,000 distinct IPs that launched 111,834 periods. In accordance with the researchers, 79% of the visitors was geared toward Citrix Gateway honeypots.
Roughly 64% of the visitors got here from residential proxies, with IPs unfold throughout the globe, showing as respectable shopper ISP addresses and bypassing reputation-based filtering. The remaining 36% got here from a single Azure IP tackle.
The exercise strongly signifies pre-exploitation infrastructure mapping, slightly than random web scanning, GreyNoise says.
“The precise concentrating on of the EPA [Endpoint Analysis] setup file path suggests curiosity in version-specific exploit growth or vulnerability validation in opposition to recognized Citrix ADC weaknesses.”
Supply: GreyNoise
The 2 indicators of malicious intent are apparent, with probably the most lively one producing 109,942 periods from 63,189 distinctive IPs and concentrating on the authentication interface at ‘/logon/LogonPoint/index.html’ to establish uncovered Citrix login panels at scale.
The second indicator, noticed on February 1st, was a six-hour dash with 10 IPs launching 1,892 periods centered on the URL path ‘/epa/scripts/win/nsepa_setup.exe’ to enumerate Citrix variations through EPA artifacts.
GreyNoise notes that the attacker employed a person agent for Chrome 50, launched in early 2016. Concentrating on the EPA setup file could point out an “curiosity in version-specific exploit growth or vulnerability validation in opposition to recognized Citrix ADC weaknesses.”
“The fast onset and completion counsel a focused scanning dash which will have been triggered by discovery of weak EPA configurations or intelligence about deployment home windows,” GreyNoise says.
The newest critical-severity flaws impacting Citrix merchandise are CVE-2025-5777, aka ‘CitrixBleed 2,’ and CVE-2025-5775, a distant code execution vulnerability that was exploited as a zero-day.
GreyNoise lists a number of detection alternatives for this newest exercise, together with:
- Monitoring for the blackbox-exporter person agent originating from non-authorized sources
- Alerting on exterior entry to /epa/scripts/win/nsepa_setup.exe
- Flagging fast enumeration of /logon/LogonPoint/ paths
- Anticipating HEAD requests in opposition to Citrix Gateway endpoints
- Monitoring outdated browser fingerprints, particularly Chrome 50 (circa 2016)
Moreover, the researchers suggest that system directors assessment the need of internet-facing Citrix Gateways, limit entry to the /epa/scripts/ listing, disable model disclosure in HTTP responses, and monitor for anomalous entry from residential ISPs in surprising areas.
GreyNoise has additionally shared the IP addresses used to launch the scanning exercise.
Fashionable IT infrastructure strikes quicker than guide workflows can deal with.
On this new Tines information, find out how your workforce can cut back hidden guide delays, enhance reliability by means of automated response, and construct and scale clever workflows on prime of instruments you already use.




