
A malvertising marketing campaign is utilizing a pretend ad-blocking Chrome and Edge extension named NexShield that deliberately crashes the browser in preparation for ClickFix assaults.
The assaults had been noticed earlier this month and delivered a brand new Python-based distant entry device known as ModeloRAT that’s deployed in company environments.
The NexShield extension, which has been faraway from the Chrome Net Retailer, was promoted as a privacy-first, high-performance, light-weight advert blocker created by Raymond Hill, the unique developer of the official uBlock Origin advert blocker with greater than 14 million customers.
Supply: Huntress
Researchers at managed safety firm Huntress say that NexShield creates a denial-of-service (DoS) situation within the browser by creating ‘chrome.runtime’ port connections in an infinite loop and exhausting its reminiscence assets.
This leads to frozen tabs, elevated CPU utilization within the Chrome course of, elevated RAM utilization, and basic browser unresponsiveness. Finally, Chrome/Edge hangs or crashes, forcing a kill through the Home windows Process Supervisor.
Due to this, Huntress refers to those assaults as a variant of ClickFix that they named ‘CrashFix’.
When the browser is restarted, the extension shows a misleading pop-up that reveals a pretend warning and suggests scanning the system find the issue.
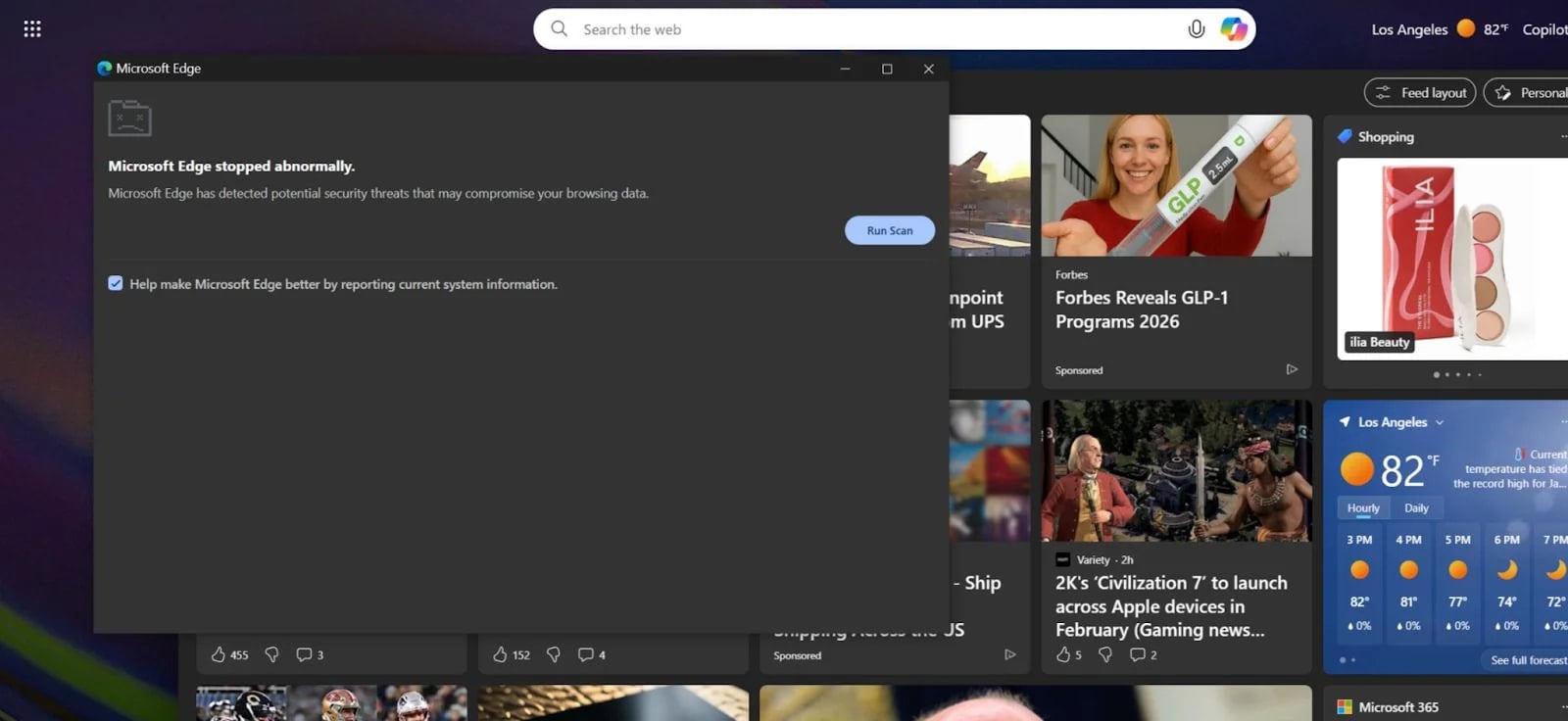
Supply: Huntress
Doing so opens a brand new window with a pretend warning about safety points detected that threaten the person’s knowledge, with directions on the right way to repair the issue, which contain executing malicious instructions within the Home windows command immediate.
In typical ClickFix trend, the malicious extension copies a command to the clipboard and instructs the person to only hit ‘Ctrl+V’ after which run it in Command Immediate.
The ‘fixing’ command is a sequence that triggers an obfuscated PowerShell script through a distant connection, which downloads and executes a malicious script.

Supply: Huntress
In an try to dissociate the extension from the malicious exercise and evade detection, the payload has a 60-minute execution delay after putting in NexShield.
For domain-joined hosts particular to company environments, the risk actor delivers ModeloRAT, which may carry out system reconnaissance, execute PowerShell instructions, modify the Registry, introduce extra payloads, and replace itself.

Supply: Huntress
For non-domain hosts, that are usually dwelling customers, the command and management server returned a “TEST PAYLOAD!!!!” message, indicating both low precedence or work in progress, Huntress researchers say.
Earlier this month, cybersecurity firm Securonix noticed one other ClickFix assault that simulated a Home windows BSOD display screen within the goal browser by abusing the full-screen mode; nonetheless, within the case of CrashFix, the browser crash is actual, making it extra convincing.
The researchers present a correct technical report on all the CrashFix assault and the payloads delivered this manner. They element the a number of levels of the an infection chain and ModeloRAT’s capabilities, from establishing persistence and gathering reconnaissance information to executing instructions, fingerprinting techniques, and figuring out its privileges on the compromised system.
Huntress attributes the analyzed CrashFix assault to a risk actor named ‘KongTuke’, whose operations have been on the corporate’s radar since early 2025.
Based mostly on the current discovery, the researchers imagine that KongTuke is evolving and turning into extra fascinated with enterprise networks, that are extra profitable for cybercriminals.
Falling for ClickFix assaults may be prevented by ensuring that the impact of any exterior command executed on the system is effectively understood. Moreover, putting in browser extensions from trusted publishers or sources ought to maintain you secure from CrashFix assaults or different threats.
Customers who put in NexShield ought to carry out a full system cleanup, as uninstalling the extension doesn’t take away all payloads, resembling ModeloRAT or different malicious scripts.




