
One other set of 17 malicious extensions linked to the GhostPoster marketing campaign has been found in Chrome, Firefox, and Edge shops, the place they accrued a complete of 840,000 installations.
The GhostPoster marketing campaign was first reported by Koi Safety researchers in December. They discovered 17 extensions that had been hiding malicious JavaScript code of their brand pictures, which monitored browser exercise and planted a backdoor.
The code fetches a closely obfuscated payload from an exterior useful resource, which tracks the sufferer’s shopping exercise, hijacks affiliate hyperlinks on main e-commerce platforms, and injects invisible iframes for advert fraud and click on fraud.
A brand new report from browser safety platform LayerX signifies that the marketing campaign remains to be ongoing regardless of being uncovered, and the next 17 extensions are a part of it:
- Google Translate in Proper Click on – 522,398 installs
- Translate Chosen Textual content with Google – 159,645 installs
- Advertisements Block Final – 48,078 installs
- Floating Participant – PiP Mode – 40,824 installs
- Convert The whole lot – 17,171 installs
- Youtube Obtain – 11,458 installs
- One Key Translate – 10,785 installs
- AdBlocker – 10,155 installs
- Save Picture to Pinterest on Proper Click on – 6,517 installs
- Instagram Downloader – 3,807 installs
- RSS Feed – 2,781 installs
- Cool Cursor – 2,254 installs
- Full Web page Screenshot – 2,000 installs
- Amazon Value Historical past – 1,197 installs
- Coloration Enhancer – 712 installs
- Translate Chosen Textual content with Proper Click on – 283 installs
- Web page Screenshot Clipper – 86 installs
In accordance with the researchers, the marketing campaign originated on Microsoft Edge after which expanded to Firefox and Chrome.
LayerX discovered that a number of the above extensions have been current in browser add-on shops since 2020, indicating a profitable long-term operation.

Supply: LayerX
Though evasion and post-activation capabilities stay largely the identical as beforehand documented by Koi, LayerX has recognized a extra superior variant within the ‘Instagram Downloader’ extension.
The distinction consists of transferring the malicious staging logic into the extension’s background script and utilizing a bundled picture file as a covert payload container moderately than solely an icon.
Supply: LayerX
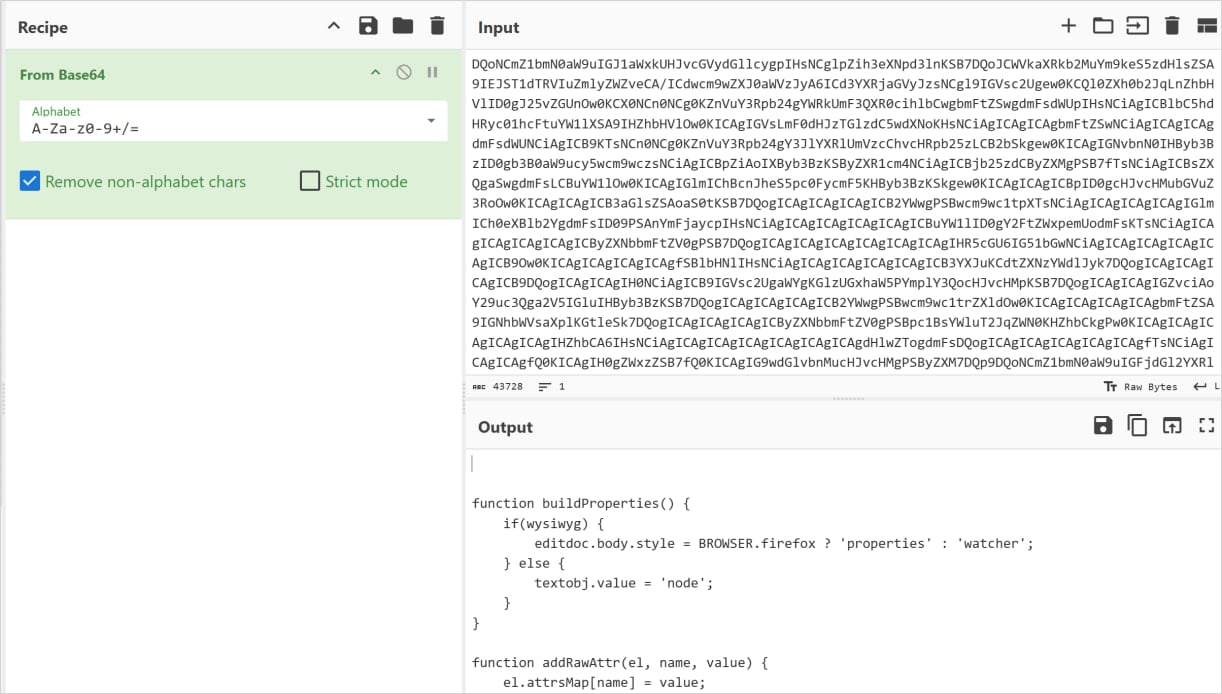
At runtime, the background script scans the picture’s uncooked bytes for a particular delimiter (>>>>), extracts and shops the hidden information in native extension storage, then later Base64-decodes and executes it as JavaScript.
“This staged execution circulate demonstrates a transparent evolution towards longer dormancy, modularity, and resilience towards each static and behavioral detection mechanisms,” feedback LayerX concerning the latest GhostPoster variant.
The researchers mentioned that the newly recognized extensions are now not current in Mozilla’s and Microsoft’s add-on shops. Nonetheless, customers who put in them of their browsers should still be in danger.
BleepingComputer has contacted Google concerning the extensions being current within the Chrome Net Retailer, and a spokesperson confirmed that every one of them have been eliminated.




