The Kimwolf botnet, an Android variant of the Aisuru malware, has grown to greater than two million hosts, most of them contaminated by exploiting vulnerabilities in residential proxy networks to focus on gadgets on inner networks.
Researchers noticed elevated exercise for the malware since final August. Over the previous month, Kimwolf has intensified its scanning of proxy networks, looking for gadgets with uncovered Android Debug Bridge (ADB) companies.
Widespread targets are Android-based TV bins and streaming gadgets that permit unauthenticated entry over ADB. Compromised gadgets are primarily utilized in distributed denial-of-service (DDoS) assaults, proxy resale, and monetizing app installations by way of third-party SDKs like Plainproxies Byteconnect.
The Aisuru botnet is presently answerable for the biggest DDoS assault publicly disclosed, which peaked at 29.7 terabits per second as measured by Cloudflare.
A report from XLab notes that the Kimwolf Android botnet had greater than 1.8 million compromised gadgets on December 4.
Researchers at menace intelligence and anti-fraud cybersecurity firm Synthient have been monitoring Kimwolf exercise. They are saying that the variety of compromised gadgets has climbed to just about two million, and produced round 12 million distinctive IP addresses every week.
Many of the contaminated Android gadgets are in Vietnam, Brazil, India, and Saudi Arabia. In lots of circumstances, the methods have been compromised by proxy SDKs earlier than buy, which was reported up to now.
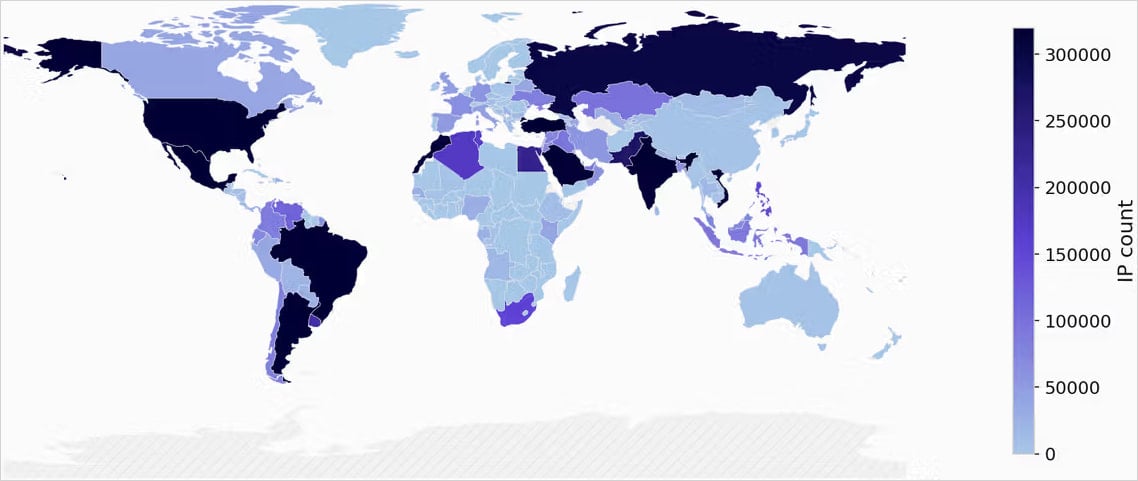
Supply: Synthient
Abusing residential proxies
In accordance with Synthient, Kimwolf’s fast progress is essentially as a result of its abuse of residential proxy networks to achieve weak Android gadgets. Particularly, the malware takes benefit of proxy suppliers that let entry to native community addresses and ports, permitting direct interplay with gadgets working on the identical inner community because the proxy consumer.
Beginning on November 12, 2025, Synthient noticed elevated exercise scanning for unauthenticated ADB companies uncovered by way of proxy endpoints, focusing on ports 5555, 5858, 12108, and 3222.
The Android Debug Bridge (ADB) is a improvement and debugging interface that permits putting in and eradicating apps, working shell instructions, transferring information, and debugging Android gadgets. When uncovered over a community, ADB can permit unauthorized distant connections to change or take management of Android gadgets.
When reachable, botnet payloads have been delivered by way of netcat or telnet, piping shell scripts immediately into the uncovered gadget for native execution, written to /knowledge/native/tmp.
Synthient captured a number of payload variants all through December, however the supply strategies remained unchanged.
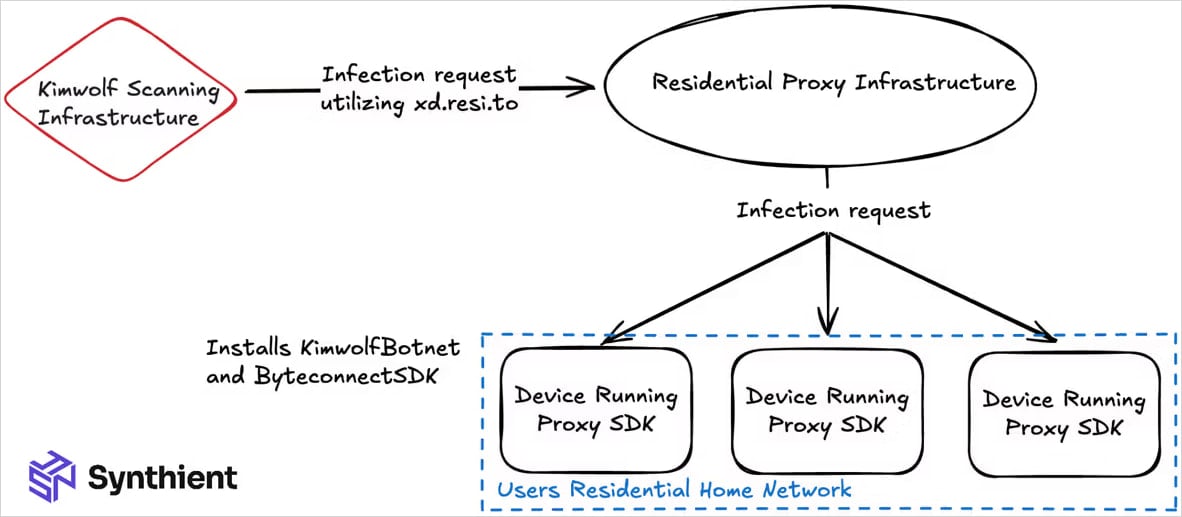
Supply: Synthient
The researchers discovered excessive publicity charges in a single pattern residential proxy pool, underscoring that such gadgets could be exploited inside minutes of becoming a member of these networks.
“Upon analyzing uncovered gadgets a part of IPIDEAs proxy pool, we discovered that 67% of all Android gadgets are unauthenticated, leaving them weak to distant code execution,” Synthient explains.
“From our scans, we discovered roughly 6 million weak IPs […] These gadgets are sometimes shipped pre-infected with SDKs from proxy suppliers,” the researchers say.
IPIDEA, one of many impacted proxy suppliers and a prime Kimwolf goal as a result of it enabled entry to all ports, responded to Synthient’s alert on December 28 by blocking entry to native networks and a broad vary of ports.
In whole, the researchers despatched virtually a dozen vulnerability reviews “to the highest proxy suppliers” noticed in Kimwolf exercise. Nevertheless, researchers can not confidently decide all of the proxy suppliers focused by the malware.
Defending towards Kimwolf
Synthient has revealed an on-line scanner software to assist customers establish if any of their community gadgets are a part of the Kimwolf botnet.
Within the case of a optimistic end result, the researchers counsel that contaminated TV bins must be “wiped or destroyed,” in any other case the botnet will persist.
The final advice is to keep away from low-cost generic Android TV bins and to want ‘Google Play Defend licensed’ gadgets from respected OEMs, equivalent to Google’s Chromecast, NVIDIA Protect TV, and Xiaomi Mi TV Field.




