
An automatic marketing campaign is focusing on a number of VPN platforms, with credential-based assaults being noticed on Palo Alto Networks GlobalProtect and Cisco SSL VPN.
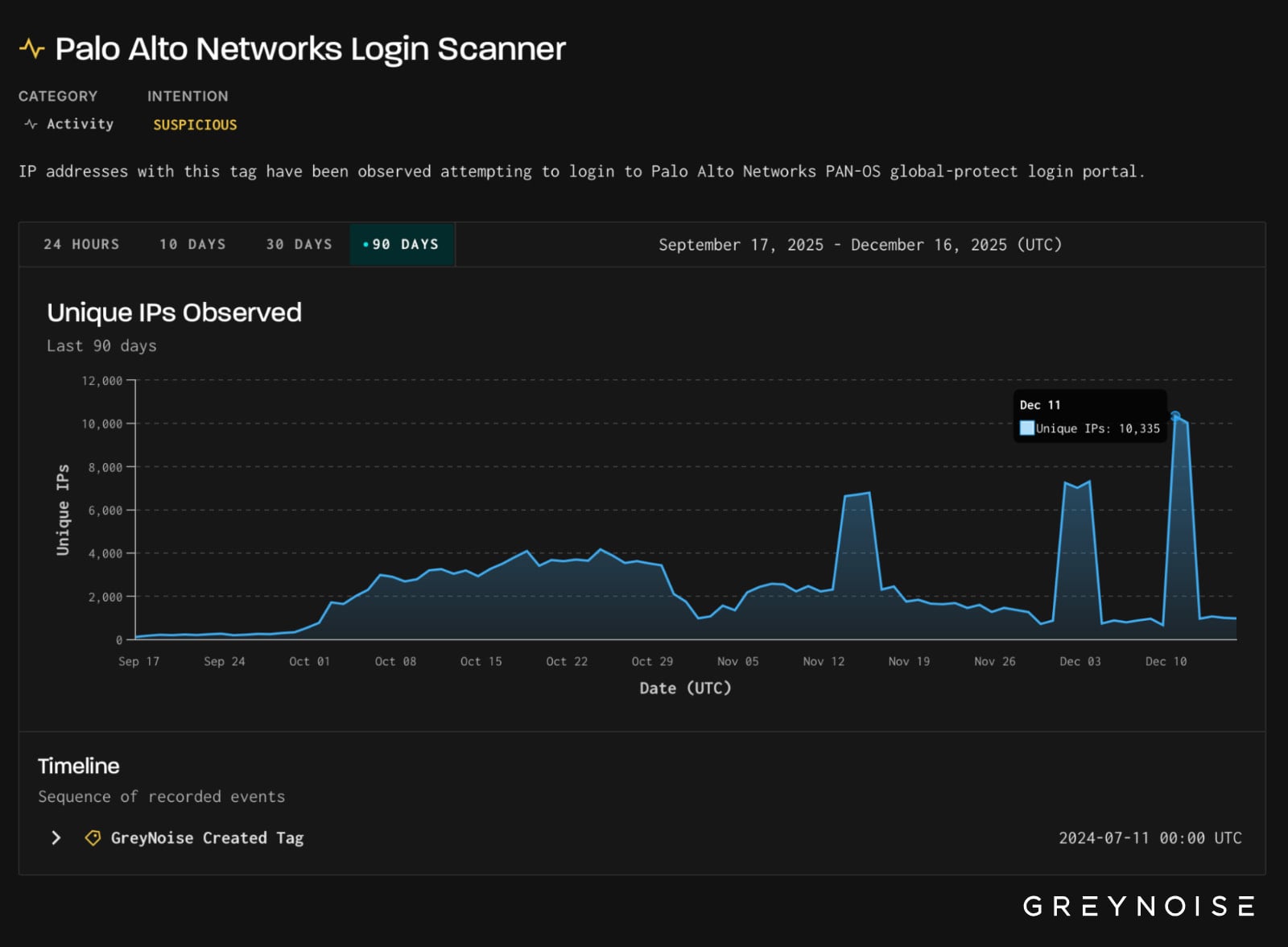
On December 11, risk monitoring platform GreyNoise noticed the variety of login makes an attempt aimed toward GlobalProtect portals peaked at 1.7 million throughout a interval of 16 hours.
Collected knowledge confirmed that the assaults originated from greater than 10,000 distinctive IP addresses and have been aimed toward infrastructure positioned in the USA, Mexico, and Pakistan.
The malicious site visitors originated nearly solely from the 3xK GmbH (Germany) IP house, indicating a centralized cloud infrastructure.
Primarily based on researchers’ observations, the risk actor reused widespread username and password mixtures, and many of the requests have been from a Firefox consumer agent that’s unusual for automated login exercise by way of this supplier.
“The consistency of the consumer agent, request construction, and timing suggests scripted credential probing designed to determine uncovered or weakly protected GlobalProtect portals, relatively than interactive entry makes an attempt or vulnerability exploitation,” GreyNoise explains.
“This exercise displays continued strain towards enterprise VPN authentication endpoints, a sample GreyNoise has noticed repeatedly in periods of heightened attacker exercise.”
Supply: GreyNoise
On December 12, exercise originating from the identical internet hosting supplier utilizing the identical TCP fingerprint began to probe Cisco SSL VPN endpoints.
GreyNoise screens recorded a bounce of distinctive assault IPs to 1,273, from the traditional baseline of lower than 200.
The exercise constitutes the primary large-scale use of 3xK-hosted IPs towards Cisco SSL VPNs prior to now 12 weeks.
On this case, too, the login payloads adopted regular SSL VPN authentication flows, together with CSRF dealing with, indicating automated credential assaults relatively than exploits.

Supply: GreyNoise
Yesterday, Cisco warned clients of a maximum-severity zero-day vulnerability (CVE-2025-20393) in Cisco AsyncOS that’s actively exploited in assaults focusing on Safe E mail Gateway (SEG) and Safe E mail and Net Supervisor (SEWM) home equipment.
Nevertheless, GreyNoise underlines that it discovered no proof linking the noticed exercise to CVE-2025-20393.
A Palo Alto Networks spokesperson confirmed to BleepingComputer that they’re conscious of the exercise. The corporate recommends customers to make use of sturdy passwords and multi-factor authentication safety.
“We’re conscious of the credential-based exercise reported by GreyNoise focusing on VPN gateways, together with GlobalProtect portals. This exercise displays automated credential probing and doesn’t represent a compromise of the environment or an exploitation of any Palo Alto Networks vulnerability,” the Palo Alto Networks spokesperson stated.
“Our investigation confirms that these are scripted makes an attempt to determine weak credentials,” they added.
Other than the really helpful Palo Alto Networks motion, Gray Noise additionally advises directors to audit community home equipment, search for surprising login makes an attempt, and block identified malicious IPs performing these probes.
Damaged IAM is not simply an IT drawback – the affect ripples throughout your entire enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM appears to be like like, and a easy guidelines for constructing a scalable technique.




