
The professional-Russia hacktivist group CyberVolk launched a ransomware-as-a-service (RaaS) known as VolkLocker that suffered from severe implementation flaws, permitting victims to doubtlessly decrypt recordsdata free of charge.
In keeping with SentinelOne researchers who examined the brand new ransomware household, the encryptor makes use of a hardcoded grasp key within the binary, which can be written in plaintext in a hidden file on affected machines.
This permits focused firms to make use of the important thing to decrypt recordsdata free of charge, undermining VolkLocker’s potential within the cybercrime area.
Hacktivism and cybercrime
CyberVolk is reportedly an India-based pro-Russia hacktivist collective that began operations final 12 months, launching distributed denial of service and ransomware assaults towards public and authorities entities opposing Russia or siding with Ukraine.
Whereas the group was disrupted on Telegram, it returned in August 2025 with a brand new RaaS program, VolkLocker (CyberVolk 2.x), which targets each Linux/VMware ESXi and Home windows methods.
An fascinating function of VolkLocker is using a Golang timer perform in its code, which, when it expires or when an incorrect secret’s entered within the HTML ransomware be aware, triggers the wiping of consumer folders (Paperwork, Downloads, Footage, and Desktop).
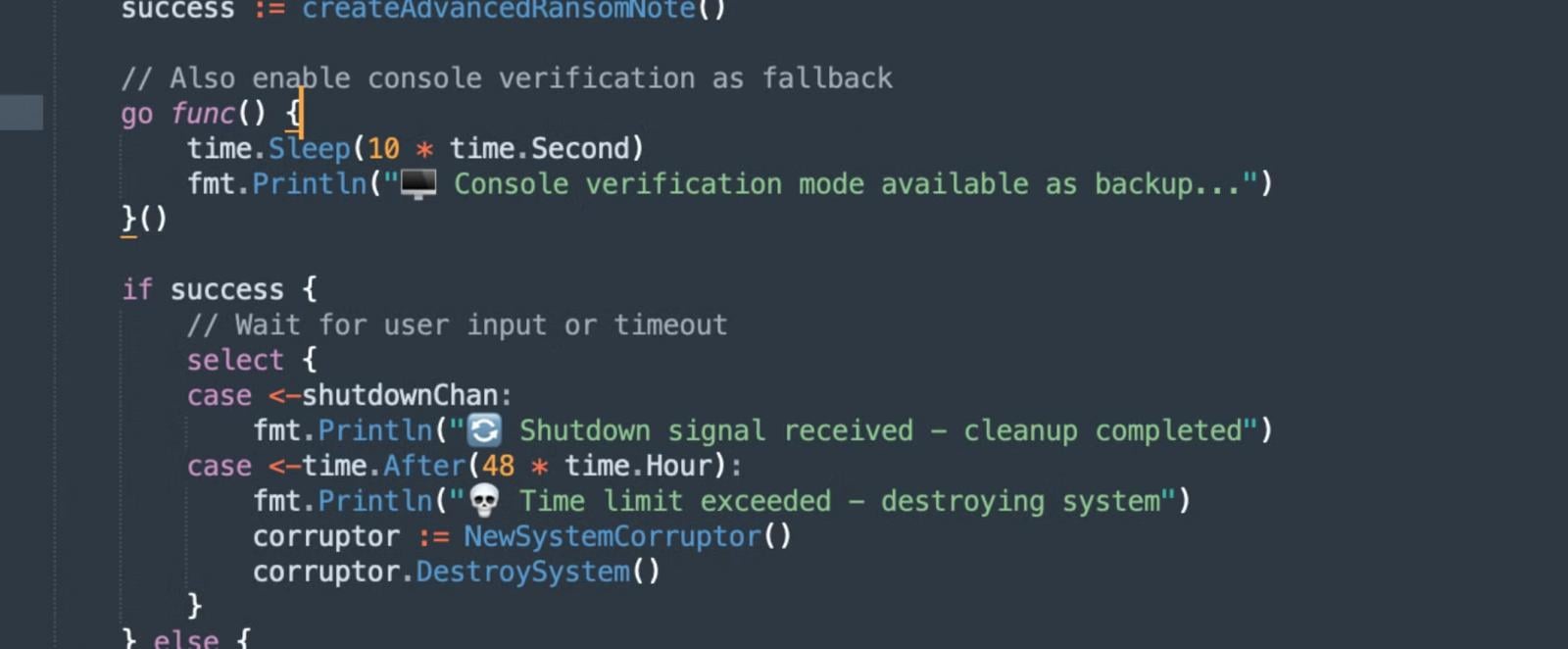
Supply: SentinelOne
Entry to the RaaS prices between $800 and $1,100 for a single OS structure, or $1,600 to $2,200 for each.
Purchasers can entry a builder bot on Telegram to customise the encryptor and obtain the generated payload.
In November 2025, the identical menace group started promoting a distant entry trojan and a keylogger, each priced at $500 every.

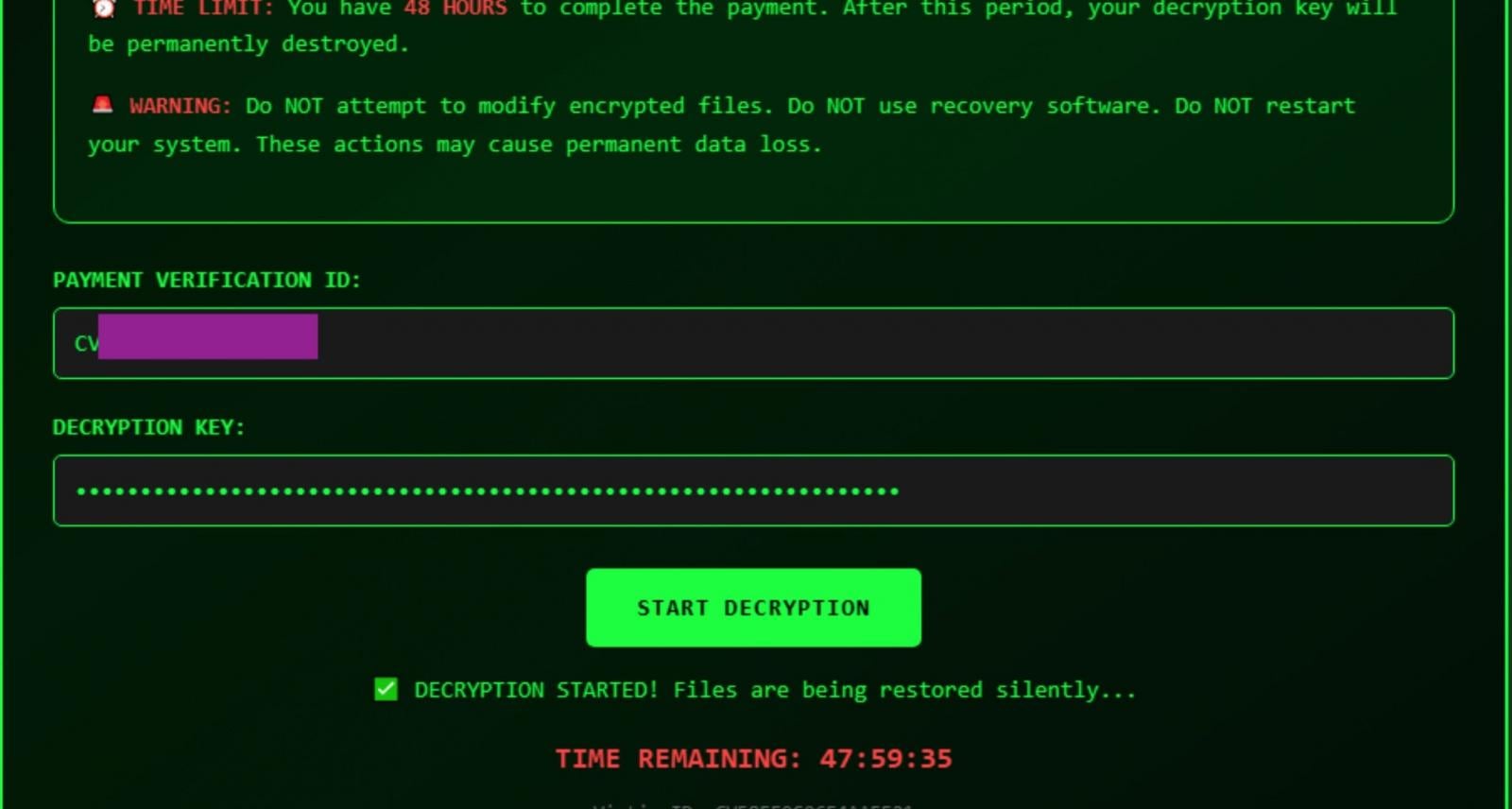
Supply: SentinelOne
Crucial crypto weak spot
VolkLocker makes use of AES-256 in GCM (Galois/Counter Mode) encryption, with a 32-bit grasp key derived from a 64-character hex string embedded within the binary.
A random 12-byte nonce is used because the initialization vector (IV) for every file, deleting the unique file and appending the .locked or .cvolk file extension to the encrypted copy.
The issue is that VolkLocker makes use of the identical grasp key to encrypt all recordsdata on a sufferer system, and that very same key can be written to a plaintext file (system_backup.key) within the %TEMP% folder.
“Because the ransomware by no means deletes this backup key file, victims may try file restoration by extracting the required values from the file,” explains SentinelOne.
“The plaintext key backup seemingly represents a take a look at artifact inadvertently shipped in manufacturing builds.”
Supply: SentinelOne
Whereas this flaw could assist any present victims, the disclosure of VolkLocker’s cryptographic flaw will seemingly immediate menace actors to repair the bug and forestall it from being abused sooner or later.
It’s thought-about a greater apply to not disclose ransomware flaws whereas a menace actor is actively working the operation, and as a substitute to share them privately with legislation enforcement and ransomware negotiation corporations that may privately help victims.
BleepingComputer has contacted SentinelOne to ask about its determination to publicly disclose VolkLocker’s weak spot, and a spokesperson despatched the under rationalization:
“The rationale we didn’t hesitate is that this isn’t a core encryption flaw however somewhat a testing artifact that’s inadvertently getting shipped to some manufacturing builds by incompetent operators and isn’t a dependable decryption mechanism past these circumstances. It’s extra consultant of the ecosystem that CyberVolk is attempting to allow by means of this RaaS providing.” – SentinelOne spokesperson
Damaged IAM is not simply an IT drawback – the affect ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with fashionable calls for, examples of what “good” IAM seems like, and a easy guidelines for constructing a scalable technique.



