At Cisco Dwell Melbourne 2025, the SOC noticed many attention-grabbing behaviors from the assorted shoppers of the convention community. One of many extra attention-grabbing ones was observations pertains to the DNS site visitors emitted by Home windows shoppers on the community, searching for their group’s Energetic Listing Area Controllers. With our Endace full packet seize for the occasion, we had been capable of seize DNS site visitors from shoppers on the community and carry out evaluation utilizing Splunk Enterprise.
As a reminder, when a Home windows consumer is in search of to speak to a website controller it’s going to make DNS queries for SRV information for names like _kerberos._tcp.dc._msdcs.DOMAINNAME or _ldap._tcp.dc._msdcs.DOMAINNAME. These DNS requests allow the consumer to seek out close by Kerberos or LDAP servers for his or her area.
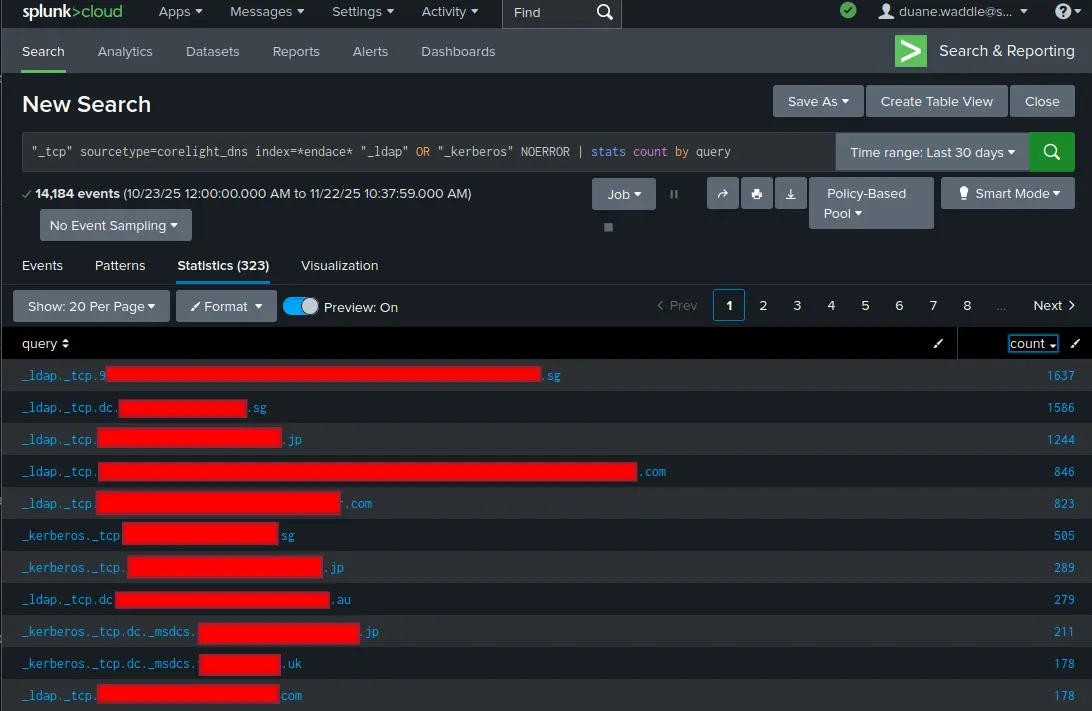
Within the Cisco Dwell Melbourne 2025 SOC, we noticed shoppers ship out DNS queries for about 3,800 distinct names beginning with “_ldap” or “_kerberos”. Whereas most of them returned a failure of some kind (NXDOMAIN or SERVFAIL), roughly 300 had a profitable DNS response. A few of these had been profitable in subsequent makes an attempt to connect with the service (which means the area controllers are accessible in some vogue from the general public web), and some had been adopted up by cleartext LDAP BINDs, leaking credential info throughout the native community and Web. (SEE DANIEL’S BLOG POST)
There are a number of issues to contemplate from this.
First, there may be an open-source intelligence (OSINT) side to this. The operators of any wi-fi community that you just connect with together with your laptop computer achieve telemetry about your group.
Second, a malicious wi-fi community may – relying on how your shoppers are configured – trick the consumer into sharing authentication info with it. Instruments equivalent to Responder are designed for this objective. Correctly configured trendy Home windows shoppers will use SMB signing, LDAP over TLS, LDAP channel binding, and different types of safety towards a hostile community atmosphere. Are you certain your shoppers are configured in a means that makes them strong towards a hostile community?
Third, in case your group has Energetic Listing area controllers on the general public Web, are you taking the required steps to guard them?
Lastly, the Cisco Dwell community is designed to be a protected community for attendees to make use of. However that’s no assure that – elsewhere – the identical SSID couldn’t be used to face up a hostile community. Shoppers will normally auto-connect once they see a wi-fi community they’ve related to earlier than.
One dependable mitigation for all of this can be a VPN consumer. A correctly configured VPN consumer like Cisco Safe Shopper can help each a full tunnel VPN and “Begin Earlier than Login”. With this characteristic, the consumer pc connects to the VPN as early as doable. All site visitors, together with DNS lookups, are despatched over the VPN. Whereas this doesn’t remove all these dangers, it raises the protection bar considerably.
Try the opposite blogs by my colleagues within the Cisco Dwell Melbourne 2026 SOC.
We’d love to listen to what you assume! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media



