
CISA has ordered U.S. federal companies to patch a vital GeoServer vulnerability now actively exploited in XML Exterior Entity (XXE) injection assaults.
In such assaults, an XML enter containing a reference to an exterior entity is processed by a weakly configured XML parser, permitting menace actors to launch denial-of-service assaults, entry confidential knowledge, or carry out Server-Aspect Request Forgery (SSRF) to work together with inside techniques.
The safety flaw (tracked as CVE-2025-58360) flagged by CISA on Thursday is an unauthenticated XML Exterior Entity (XXE) vulnerability in GeoServer 2.26.1 and prior variations (an open-source server for sharing geospatial knowledge over the Web) that may be exploited to retrieve arbitrary information from susceptible servers.
“An XML Exterior Entity (XXE) vulnerability was recognized affecting GeoServer 2.26.1 and prior variations. The applying accepts XML enter by means of a selected endpoint /geoserver/wms operation GetMap,” a GeoServer advisory explains.
“Nonetheless, this enter isn’t sufficiently sanitized or restricted, permitting an attacker to outline exterior entities inside the XML request.”
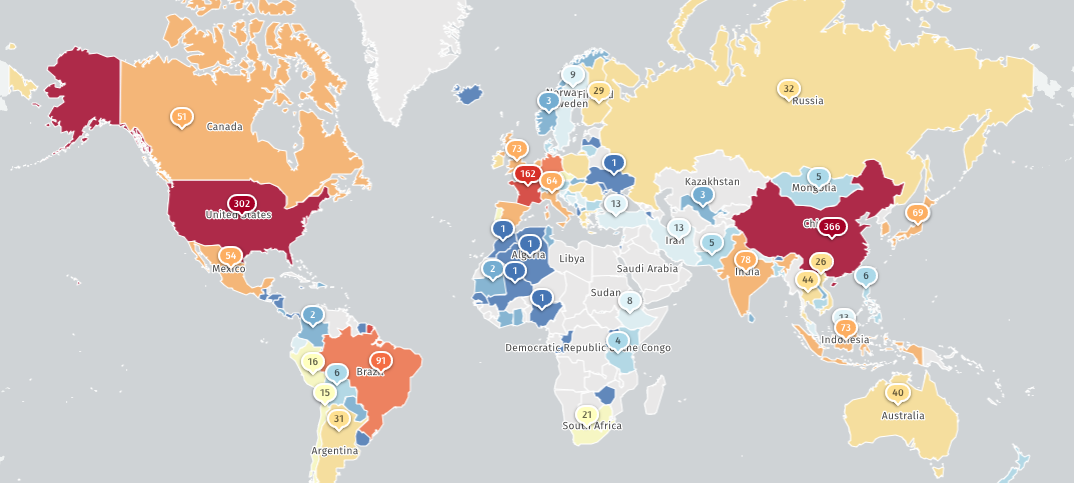
The Shadowserver Web watchdog group now tracks 2,451 IP addresses with GeoServer fingerprints, whereas Shodan experiences over 14,000 situations uncovered on-line.
CISA has now added CVE-2025-58360 to its Identified Exploited Vulnerabilities (KEV) Catalog, warning that the flaw is being actively exploited in assaults and ordering Federal Civilian Government Department (FCEB) companies to patch servers by January 1st, 2026, as mandated by the Binding Operational Directive (BOD) 22-01 issued in November 2021.
FCEB companies are non-military companies inside the U.S. government department, such because the Division of Power, the Division of the Treasury, the Division of Homeland Safety, and the Division of Well being and Human Providers.
Though BOD 22-01 solely applies to federal companies, the U.S. cybersecurity company urged community defenders to prioritize patching this vulnerability as quickly as doable.
“Most of these vulnerabilities are frequent assault vectors for malicious cyber actors and pose important dangers to the federal enterprise,” CISA stated. “Apply mitigations per vendor directions, observe relevant BOD 22-01 steerage for cloud companies, or discontinue use of the product if mitigations are unavailable.”
Final yr, CISA additionally added OSGeo GeoServer JAI-EXT code injection (CVE-2022-24816) and GeoTools eval injection (CVE-2024-36401) vulnerabilities to its record of actively exploited safety flaws.
Because the cybersecurity company revealed in September, the latter was exploited to breach an unnamed U.S. authorities company in 2024 after compromising an unpatched GeoServer occasion.
Damaged IAM is not simply an IT downside – the impression ripples throughout your entire enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM seems like, and a easy guidelines for constructing a scalable technique.



