
Two malicious extensions on Microsoft’s Visible Studio Code Market infect builders’ machines with information-stealing malware that may take screenshots, steal credentials, crypto wallets, and hijack browser periods.
{The marketplace} hosts extensions for the favored VSCode built-in growth surroundings (IDE) to increase performance or add customization choices.
The 2 malicious extensions, referred to as Bitcoin Black and Codo AI, masquerade as a colour theme and an AI assistant, respectively, and have been revealed underneath the developer title ‘BigBlack.’
On the time of writing, Codo AI was nonetheless current within the market, though it counted fewer than 30 downloads. Bitcoin Black’s counter confirmed just one set up.

Supply: BleepingComputer.com
Based on Koi Safety, the Bitcoin Black malicious extension contains a “*” activation occasion that executes on each VSCode motion. It might probably additionally run PowerShell code, one thing {that a} theme doesn’t want and ought to be a crimson flag.
In older variations, Bitcoin Black used a PowerShell script to obtain a password-protected archived payload, which created a visual PowerShell window and will have warned the consumer.
In newer variations, although, the method switched to a batch script (bat.sh) that calls ‘curl’ to obtain a DLL file and an executable, and the exercise happens with the window hidden.

Supply: Koi Safety
Idan Dardikman of Koi Safety says that Codo AI has code help performance through ChatGPT or DeepSeek, but additionally features a malicious part.
Each extensions ship a professional executable of the Lightshot screenshot software and a malicious DLL file that’s loaded through the DLL hijacking approach to deploy the infostealer underneath the title runtime.exe.
The malicious DLL is flagged as a risk by 29 out of the 72 antivirus engines on Virus Whole, the researcher notes in a report as we speak.
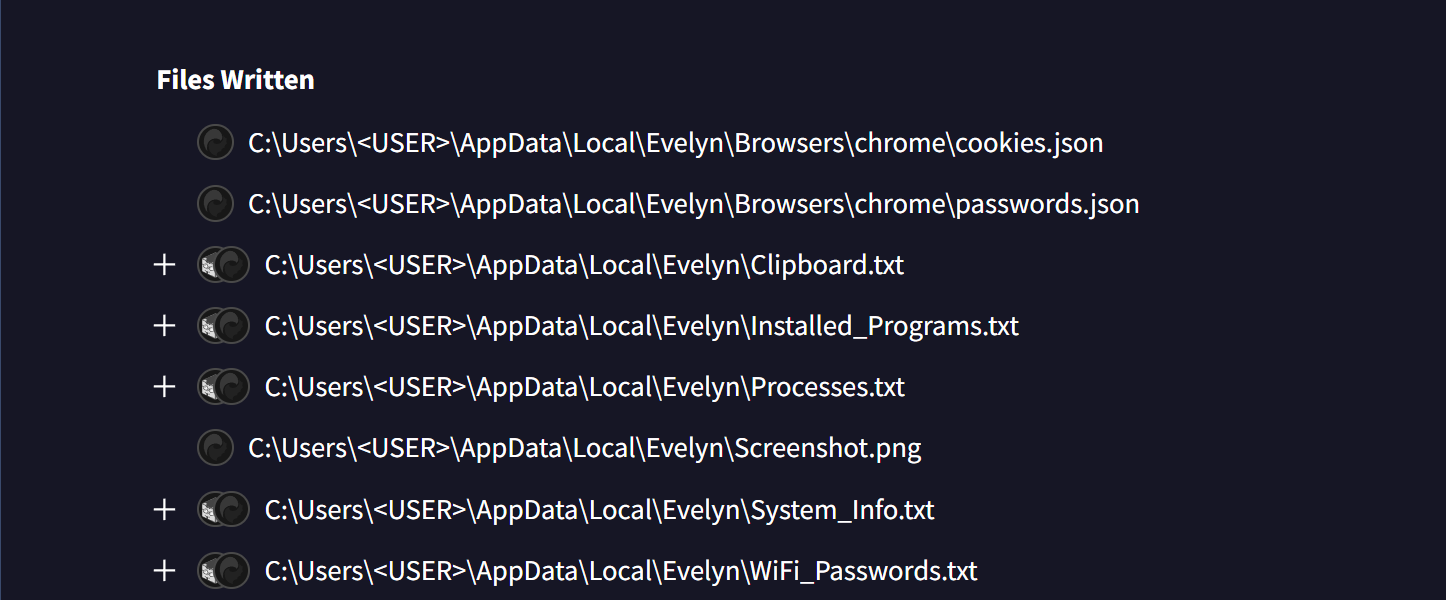
The malware creates a listing in ‘%APPDATApercentLocal‘ and creates a listing referred to as Evelyn to retailer stolen knowledge: particulars about operating processes, clipboard content material, WiFi credentials, system info, screenshots, a listing of put in packages, and operating processes.
supply: BleepingComputer
To steal cookies and hijack consumer periods, the malware launches the Chrome and Edge browsers in headless mode so it will probably snatch saved cookies and hijack consumer periods.
The malware additionally steals cryptocurrency wallets like Phantom, Metamask, Exodus. It appears for passwords and credentials
BleepingComputer has contacted Microsoft in regards to the presence of the extensions within the market, however a remark wasn’t instantly accessible.
Malicious VS Code extensions have been pushed to platforms offering extensions with VS Code IDEs, reminiscent of OpenVSX and Visible Studio Code, one of the crucial notable campaigns being Glassworm.
Builders can reduce the dangers of malicious VSCode extensions by putting in initiatives solely from respected publishers.
Damaged IAM is not simply an IT downside – the affect ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM appears like, and a easy guidelines for constructing a scalable technique.



