
Fortra has launched safety updates to patch a most severity vulnerability in GoAnywhere MFT’s License Servlet that may be exploited in command injection assaults.
GoAnywhere MFT is a web-based managed file switch instrument that helps organizations securely switch recordsdata and keep audit logs of who accesses the shared recordsdata.
Tracked as CVE-2025-10035, this safety flaw is brought on by a deserialization of untrusted information weak point and will be exploited remotely in low-complexity assaults that do not require person interplay. Whereas Fortra said that the vulnerability was found over the weekend, it did not specify who reported it or whether or not the flaw has been exploited in assaults.
“A deserialization vulnerability within the License Servlet of Fortra’s GoAnywhere MFT permits an actor with a validly cast license response signature to deserialize an arbitrary actor-controlled object, presumably resulting in command injection,” the corporate mentioned in a safety advisory printed on Thursday.
“Throughout a safety verify carried out September 11, 2025, we recognized that GoAnywhere clients with an Admin Console accessible over the web might be weak to unauthorized third-party publicity,” Fortra informed BleepingComputer immediately. “We instantly developed a patch and supplied clients mitigation steering to assist resolve the difficulty. Clients ought to overview configurations instantly and take away public entry from the Admin Console.”
The corporate has launched GoAnywhere MFT 7.8.4 and Maintain Launch 7.6.3, which embody CVE-2025-10035 patches, and suggested IT directors who cannot instantly improve their software program to safe weak methods by guaranteeing that the GoAnywhere Admin Console cannot be accessed over the web.
“Exploitation of this vulnerability is very dependent upon methods being externally uncovered to the web,” Fortra added.
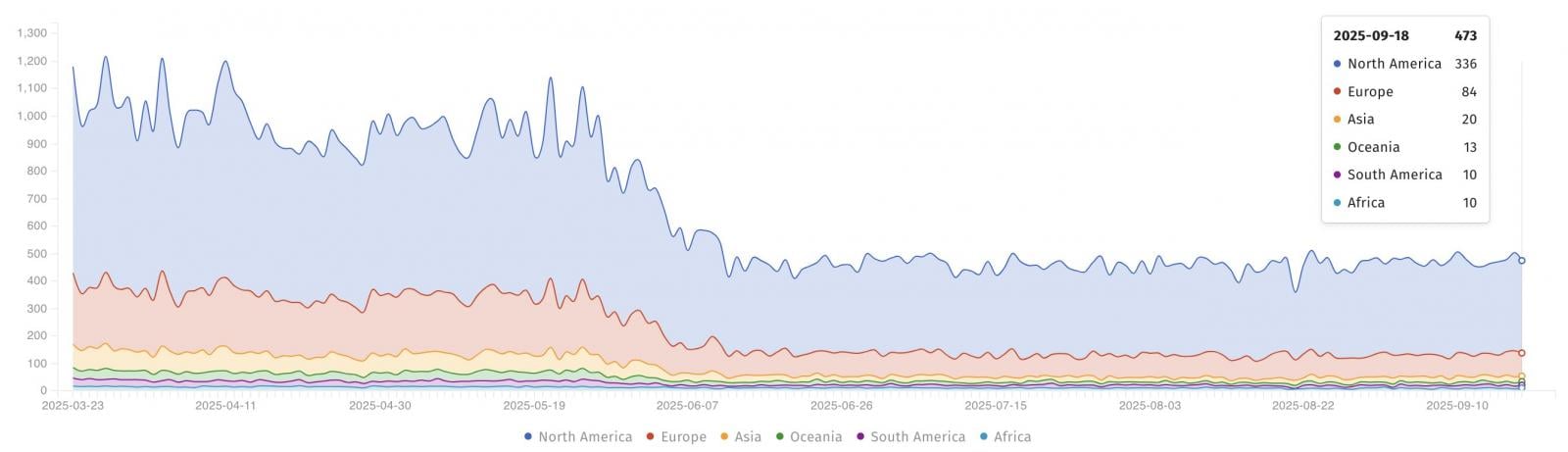
Safety analysts on the nonprofit Shadowserver Basis are monitoring over 470 GoAnywhere MFT situations. Nevertheless, it’s unclear what number of of those have already been patched or have their admin console uncovered on-line.
Whereas CVE-2025-10035 has but to be tagged as actively exploited, admins are nonetheless suggested to patch their GoAnywhere MFT situations, as menace actors think about safe file switch options (comparable to GoAnywhere MFT) a gorgeous goal as a result of they’re usually used to share delicate paperwork.
For example, the Clop ransomware gang claimed that it breached over 130 organizations two years in the past by exploiting a essential distant code execution flaw (CVE-2023-0669) within the GoAnywhere MFT software program in zero-day assaults.
Fortra (previously often called HelpSystems), the cybersecurity firm behind GoAnywhere MFT and the extensively abused Cobalt Strike menace emulation instrument, says it supplies software program and providers to over 9,000 organizations worldwide.



