
Cloudflare’s Firewall and DDoS prevention could be bypassed by means of a selected assault course of that leverages logic flaws in cross-tenant safety controls.
This bypass may put Cloudflare’s prospects beneath a heavy burden, rendering the safety methods of the web agency much less efficient.
To make issues worse, the one requirement for the assault is for the hackers to create a free Cloudflare account, which is used as a part of the assault.
Nevertheless, it must be famous that the attackers should know a focused internet server’s IP deal with to abuse these flaws.
Cloudflare vs Cloudflare
Certitude’s researcher Stefan Proksch found that the supply of the difficulty is Cloudflare’s technique to make use of shared infrastructure that accepts connections from all tenants.
Particularly, the analyst recognized two vulnerabilities within the system impacting Cloudflare’s “Authenticated Origin Pulls” and “Allowlist Cloudflare IP Addresses.”
Authenticated Origin Pulls is a safety characteristic supplied by Cloudflare to make sure that HTTP(s) requests despatched to an origin server come by means of Cloudflare and never from an attacker.
When configuring this characteristic, prospects can add their certificates utilizing an API or generate one by means of Cloudflare, the default and simplest way.
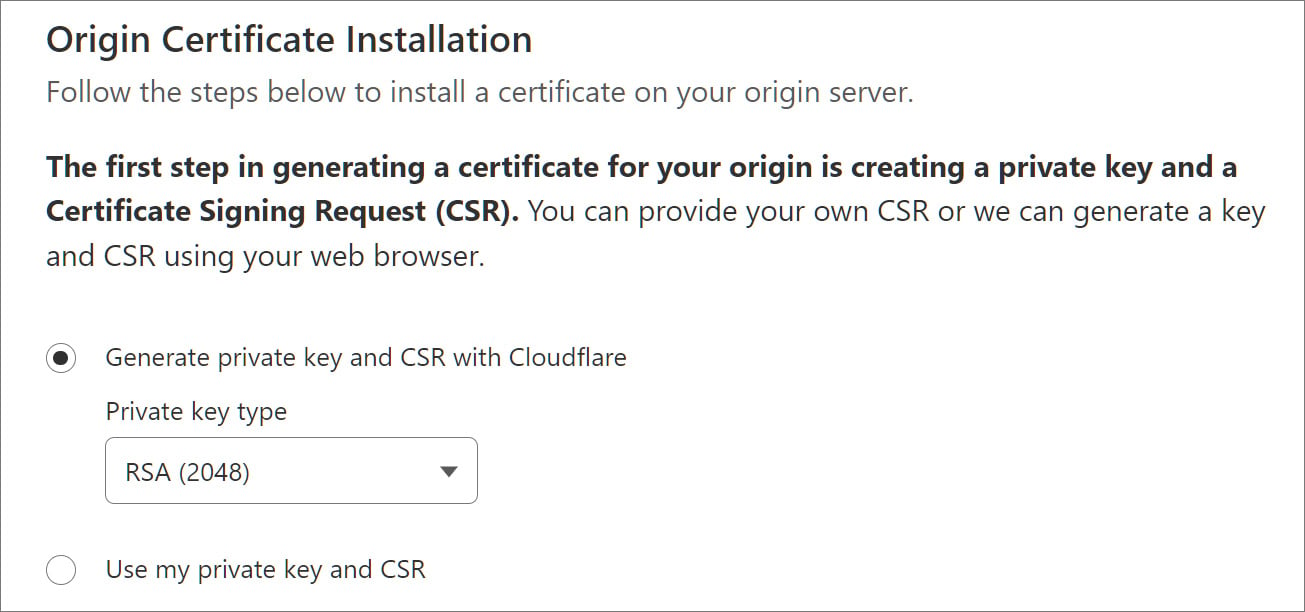
Supply: BleepingComputer
As soon as configured, Cloudflare makes use of the SSL/TLS certificates to authenticate any HTTP(S) requests between the service’s reverse proxies and the shopper’s origin server, stopping unauthorized requests from accessing the web site.
Nevertheless, as Proksch explains, attackers can bypass this safety as Cloudflare makes use of a shared certificates for all prospects as an alternative of a tenant-specific one, inflicting all connections originating from Cloudflare to be permitted.
“An attacker can setup a customized area with Cloudflare and level the DNS A document to victims IP deal with,” explains Proksch.
“The attacker then disables all safety options for that customized area of their tenant and tunnel their assault(s) by means of the Cloudflare infrastructure.”
“This strategy permits attackers to bypass the safety options by the sufferer.”
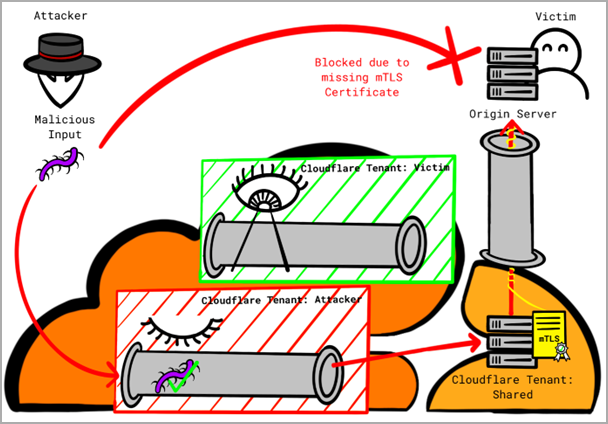
The issue arising from this logic hole is that attackers with a Cloudflare account can direct malicious site visitors to different Cloudflare shoppers or route their assaults by means of the corporate’s infrastructure.
Proksch says the one technique to mitigate this weak spot is to make use of customized certificates reasonably than one generated by Cloudflare.
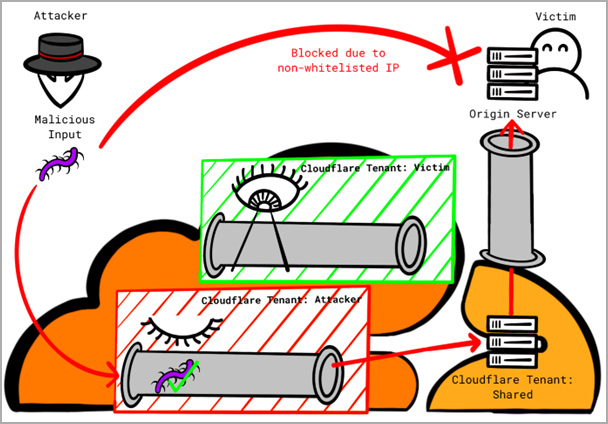
The second problem impacts Cloudflare’s Allowlist Cloudflare IP addresses, a safety measure that solely permits site visitors originating from Cloudflare’s IP deal with vary to succeed in shoppers’ origin servers.
Once more, an attacker can leverage a flaw within the logic by organising a website with Cloudflare and pointing their area’s DNS A document to the IP deal with of the goal sufferer’s server.
Subsequent, they flip off all safety options for the customized area and route the malicious site visitors by means of Cloudflare’s infrastructure, which might be seen as trusted from the sufferer’s perspective and, therefore, permitted.
Proksch has additionally shared a proof-of-concept with configuration particulars to reveal how straightforward it’s to bypass Cloudflare protections by leveraging the failings.
Certitude proposes the next protection measures in opposition to these assaults:
- Use a customized certificates to configure the “Authenticated Origin Pulls” mechanism as an alternative of Cloudflare’s shared certificates.
- Use Cloudflare Aegis (if out there) to outline a extra particular egress IP deal with vary devoted to every consumer.
Researchers Florian Schweitzer and Stefan Proksch, who found the logic flaws, reported it to Cloudflare by way of HackerOne on March 16, 2023, however the problem was closed as “informative.”
BleepingComputer has contacted Cloudflare to ask if there are any plans to implement extra safety mechanisms or warn shoppers with probably dangerous configurations, however now we have but to listen to again.


