
Malware persistence methods allow attackers to take care of entry to compromised endpoints regardless of system reboots, credential modifications, or different disruptions. Widespread strategies embody altering configurations, injecting startup code, and hijacking authentic processes.
These approaches make sure the malware or attacker stays lively, permitting malicious actions to proceed with out the necessity for re-exploitation.
On this article, we are going to study the character of malware persistence methods, their affect, and methods for defending in opposition to them.
Widespread malware persistence methods
The MITRE ATT&CK framework catalogs a spread of methods utilized by menace actors to take care of persistence. Beneath are examples of malware persistence methods from the framework that enable attackers to maintain long-term entry to compromised endpoints:
T1053 – Scheduled Job/Job
Adversaries abuse activity scheduling options to run malicious code repeatedly or at set intervals. Constructed-in utilities akin to Job Scheduler (Home windows), cron (Linux), and launchd (macOS) can execute packages or scripts at specified instances or in response to sure occasions.
T1037 – Boot or Logon Initialization Scripts
Attackers configure scripts to execute throughout system boot or person logon, making certain persistence or privilege escalation. On Linux, mechanisms like rc.native, init.d, or systemd are generally used to launch malicious code at startup.
T1543 – Create or Modify System Course of
System-level processes akin to Home windows companies, Linux daemons, or macOS launchd brokers run robotically within the background. Risk actors can set up or modify these processes to execute malicious payloads on startup or throughout system operation.
T1136 – Create Account
Adversaries could create new native, area, or cloud person accounts on compromised methods to take care of entry. With ample privileges, these accounts can be utilized for ongoing entry with out requiring persistent distant entry instruments.
T1098 – Account Manipulation
Account manipulation allows attackers to take care of or elevate entry by modifying credentials, altering group memberships, or bypassing safety insurance policies. For instance, including an SSH key to ~/.ssh/authorized_keys allows persistent distant entry with no need a password.
Affect of malware persistence methods
Malware persistence methods are designed to make sure attackers preserve long-term entry to compromised methods. Beneath, we discover some impacts of malware persistence methods.
Prolonged dwell time
Malware persistence methods allow attackers to stay in a compromised setting for a protracted interval with out requiring re-exploitation.
This prolonged presence, typically lasting weeks or months, offers them time to discover the community, escalate privileges, and plan their subsequent strikes fastidiously earlier than detection.
Remediation evasion
Even after preliminary removing, attackers can regain entry utilizing persistence mechanisms akin to scheduled duties, malicious companies, or unauthorized person accounts.
This makes cleanup efforts ineffective except all persistence mechanisms are recognized and eliminated.
Knowledge exfiltration
Persistent entry is commonly utilized in Superior Persistent Threats (APTs), the place attackers regularly exfiltrate information over an prolonged interval to take care of long-term infiltration and exploitation.
This enables delicate info, akin to credentials or enterprise information, to be stolen over time.
Deployment of extra malware
With steady entry, attackers can introduce extra malicious instruments, together with ransomware, backdoors, or distant entry trojans.
This may additional compromise the system or increase the assault floor throughout the community.
Compromised regulatory compliance
Malware persistence methods allow attackers to take care of unauthorized entry to methods over an prolonged interval.
This long-term entry can result in violations of regulatory requirements, akin to GDPR, HIPAA, and PCI DSS, which require strict information safety, system integrity, and breach notification.
Defend your methods in opposition to hidden threats. Find out how attackers use malware persistence methods, and the way Wazuh helps you detect and cease them.
Find out how to defend in opposition to malware persistence methods
Defending in opposition to persistence methods requires a layered strategy that mixes detection, prevention, and incident response.
Beneath are some key protection methods:
1. Patch administration: A number of persistence methods exploit recognized vulnerabilities in working methods, functions, or drivers. By frequently making use of patches to those parts, you may considerably scale back the accessible assault floor.
2. File Integrity Monitoring (FIM): FIM helps detect unauthorized modifications to crucial information, akin to startup scripts, scheduled activity configurations, registry keys, or utility binaries. By monitoring these delicate information, you may establish when attackers try to realize persistence.
3. Consumer account monitoring: Persistence typically includes creating new person accounts, modifying current ones, or escalating privileges. Steady monitoring of account creation, deletion, and permission modifications can reveal suspicious habits.
4. Harden system configurations: Securing baseline configurations reduces the danger of attackers abusing system options for persistence. This consists of disabling unused companies, imposing robust password insurance policies, limiting administrative privileges, and utilizing group insurance policies to limit autorun habits.
5. Risk searching: Conducting proactive menace hunts permits safety groups to detect hidden persistence mechanisms that evade automated instruments. This consists of trying to find suspicious habits, akin to uncommon course of executions, scheduled duties, or long-dormant malware.
6. Endpoint safety: Deploying strong endpoint safety instruments akin to XDR allows real-time monitoring of exercise and blocks recognized persistence behaviors. Trendy endpoint instruments can detect and robotically reply to indicators like registry modifications, service installations, and unauthorized script execution.
How Wazuh defends in opposition to malware persistence methods
Wazuh is a free and open supply enterprise-ready safety resolution that gives unified SIEM and XDR safety throughout a number of workloads.
It offers a centralized view for menace detection and safety monitoring throughout virtualized, on-premises, cloud-based, and containerized environments.
Wazuh affords a number of capabilities to defend in opposition to malware persistence methods. These capabilities embody, however aren’t restricted to:
- Lively response
- File Integrity Monitoring (FIM)
- Safety and Configuration Evaluation (SCA)
- Log information evaluation
- Vulnerability detection
Lively response
The Wazuh Lively Response module allows safety groups to automate response actions primarily based on predefined triggers, serving to them effectively handle safety incidents. Automation ensures that high-priority occasions are addressed promptly and constantly.
Wazuh offers a number of built-in response scripts that may carry out actions akin to blocking malicious community visitors or eradicating contaminated information from monitored endpoints.
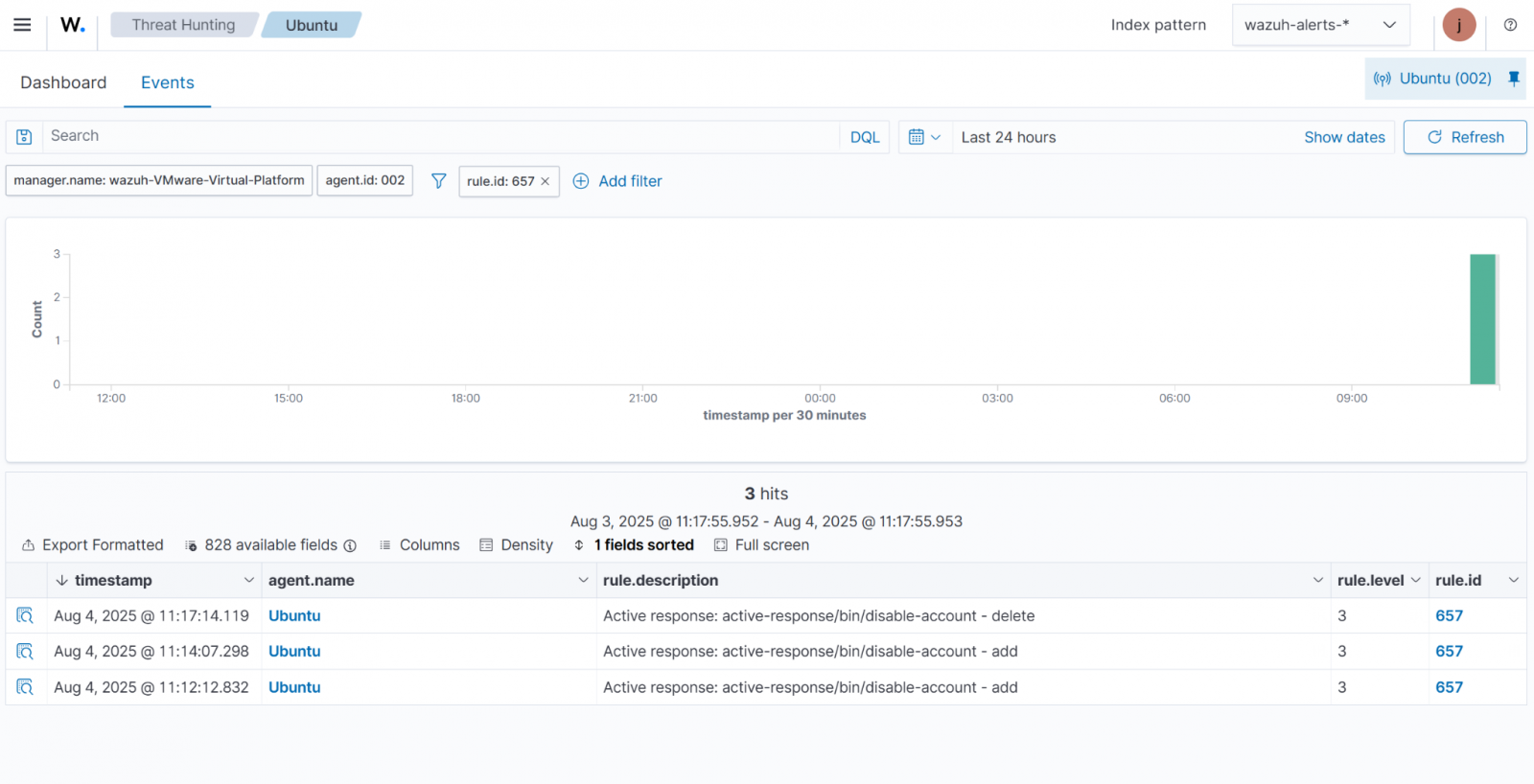
Within the instance under, the Lively Response module disables a Linux account that has been focused by brute-force login makes an attempt.
File Integrity Monitoring (FIM)
The Wazuh FIM module screens information and directories, producing alerts when a person or course of creates, modifies, or deletes monitored information. It builds a baseline by scanning and storing checksums and file attributes.
When a person or course of modifications a file, the module compares its checksum and attributes with the baseline and triggers an alert if a mismatch is detected.
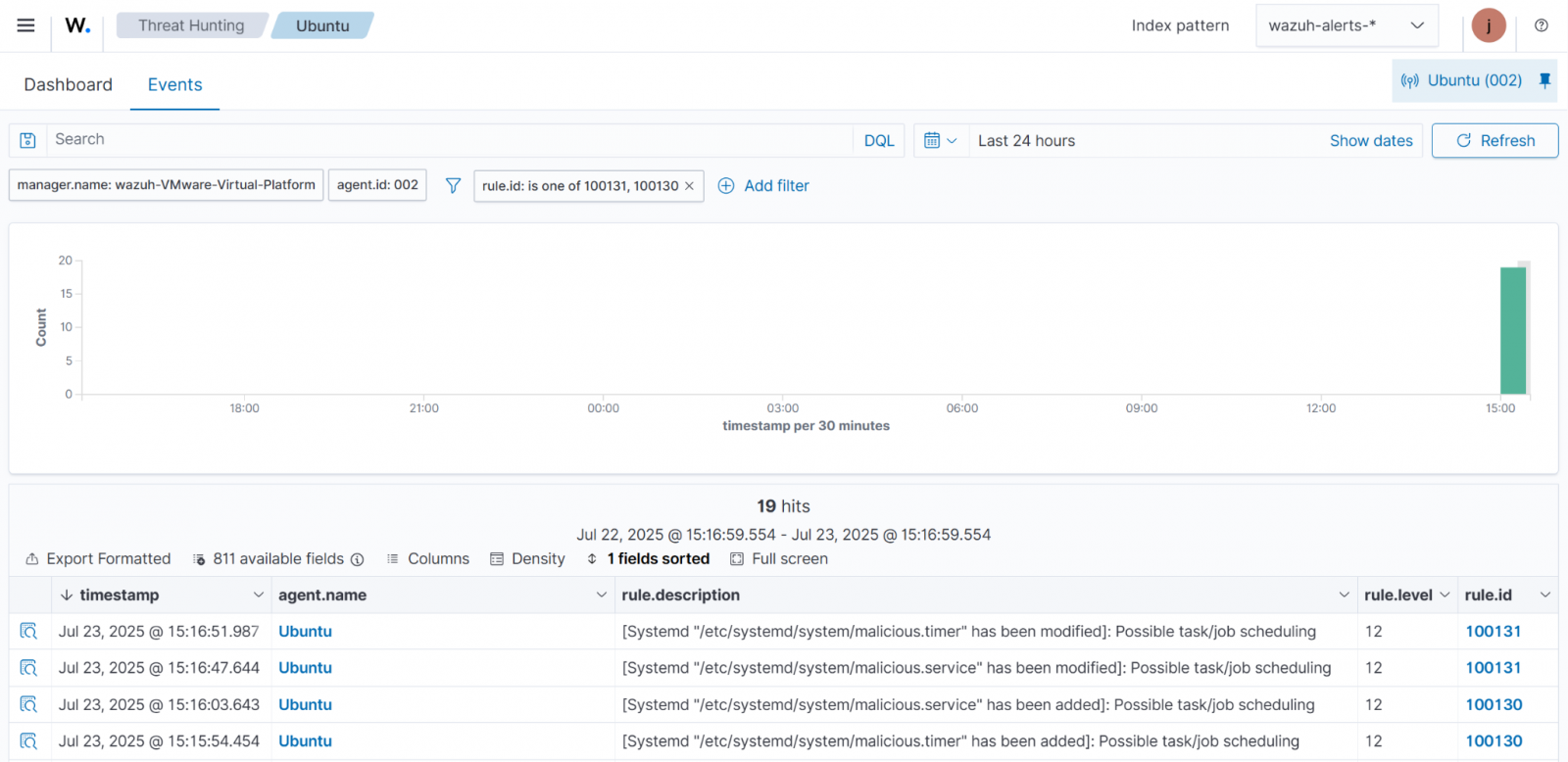
The weblog put up Detecting Widespread Linux Persistence Methods with Wazuh highlights how the Wazuh FIM module detects malware persistence on Linux endpoints.
We use the FIM module to watch modifications to systemd companies and timers on a monitored endpoint. Since systemd manages companies and startup duties, monitoring its configuration information is essential for detecting unauthorized modifications.
Safety and Configuration Evaluation (SCA)
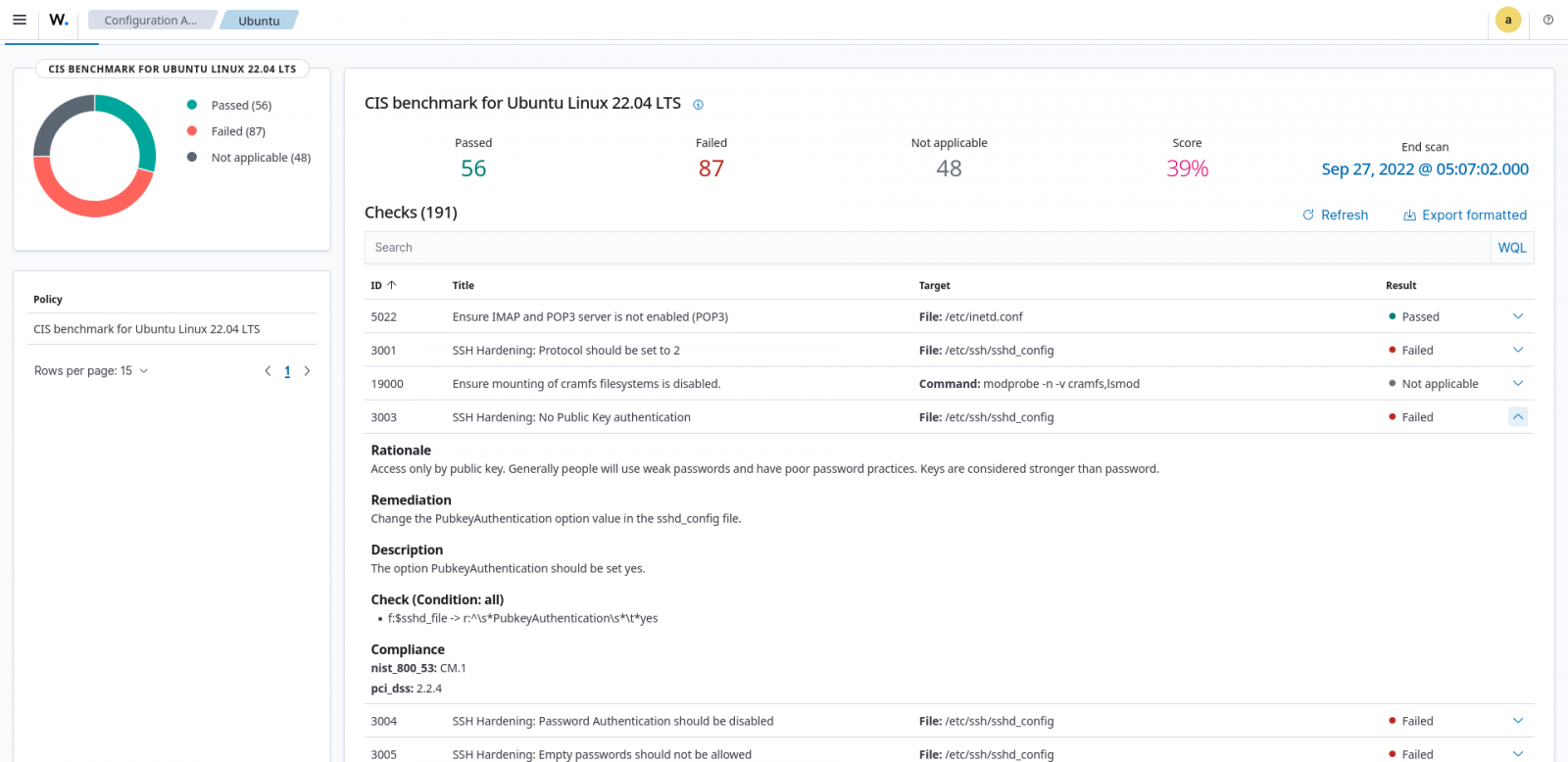
System hardening reduces the assault floor by eliminating misconfigurations and pointless parts. The Wazuh SCA module helps enhance system hardening by scanning monitored endpoints to detect misconfigurations and recommending remediation actions. It makes use of coverage information to examine system settings, information, processes, and registry entries.
For instance, the Wazuh SCA can assess whether or not it’s vital to alter password insurance policies, take away pointless software program, disable pointless companies, or audit the community configurations.
In Determine 3 under, the Wazuh SCA scan end result exhibits failed as a result of the general public key authentication for SSH is just not enabled.
Log information evaluation
Wazuh offers visibility into your IT infrastructure by gathering, analyzing, and storing logs from endpoints, community units, and functions.
The Wazuh agent, operating on a monitored endpoint, collects and forwards system and utility logs to the Wazuh server for evaluation. Log information evaluation allows menace detection, efficiency monitoring, troubleshooting, compliance auditing, and the identification of anomalous actions.
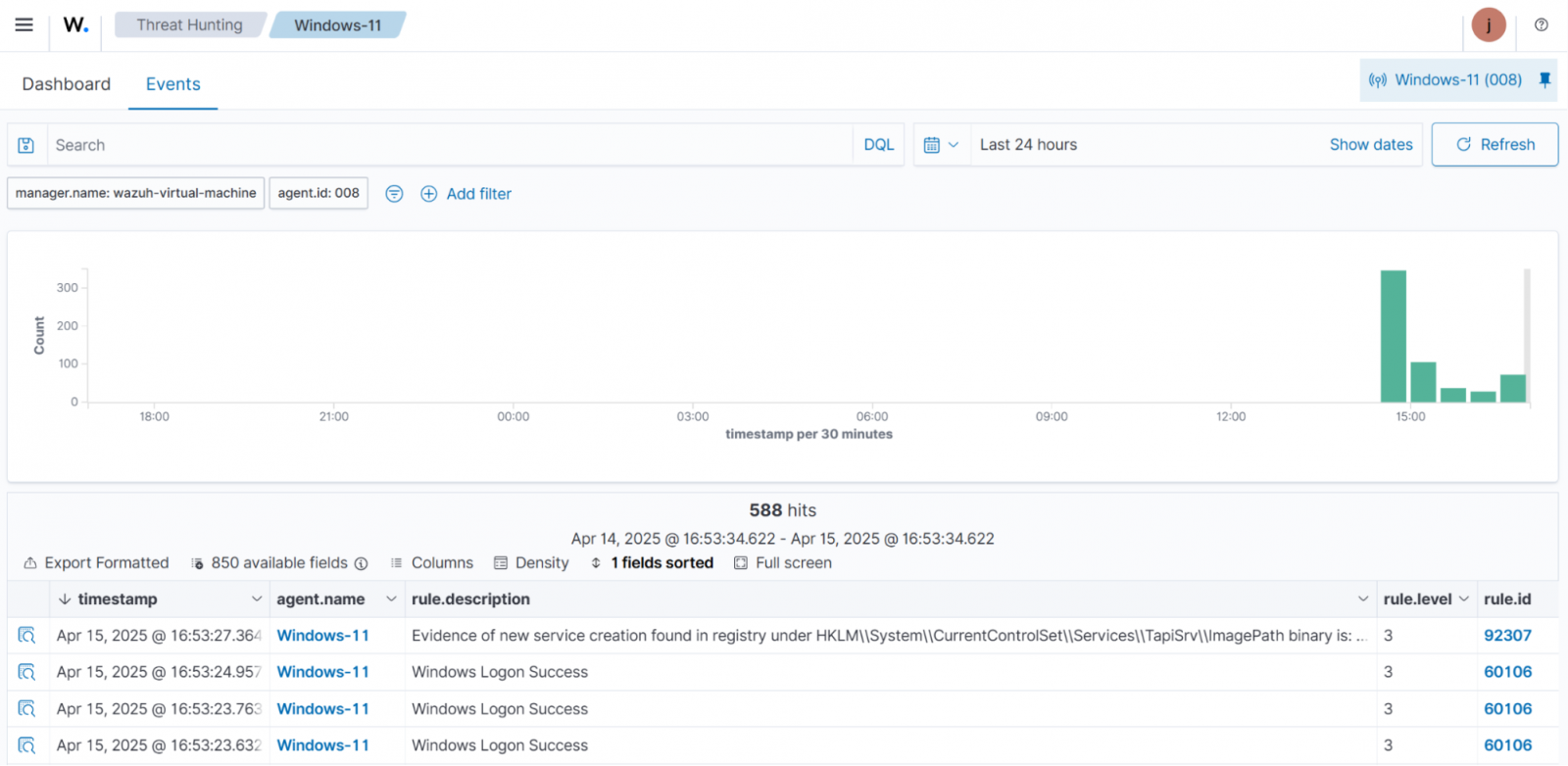
In Detecting Home windows persistence methods with Wazuh, the Wazuh agent collects logs from a Home windows endpoint and forwards them to the Wazuh server for evaluation. This helps establish indicators of malware persistence, akin to unauthorized account creation, modifications to startup folders or registry keys, and modifications to companies.
Determine 4 under illustrates the detection of a modification to a Home windows service.
Vulnerability detection
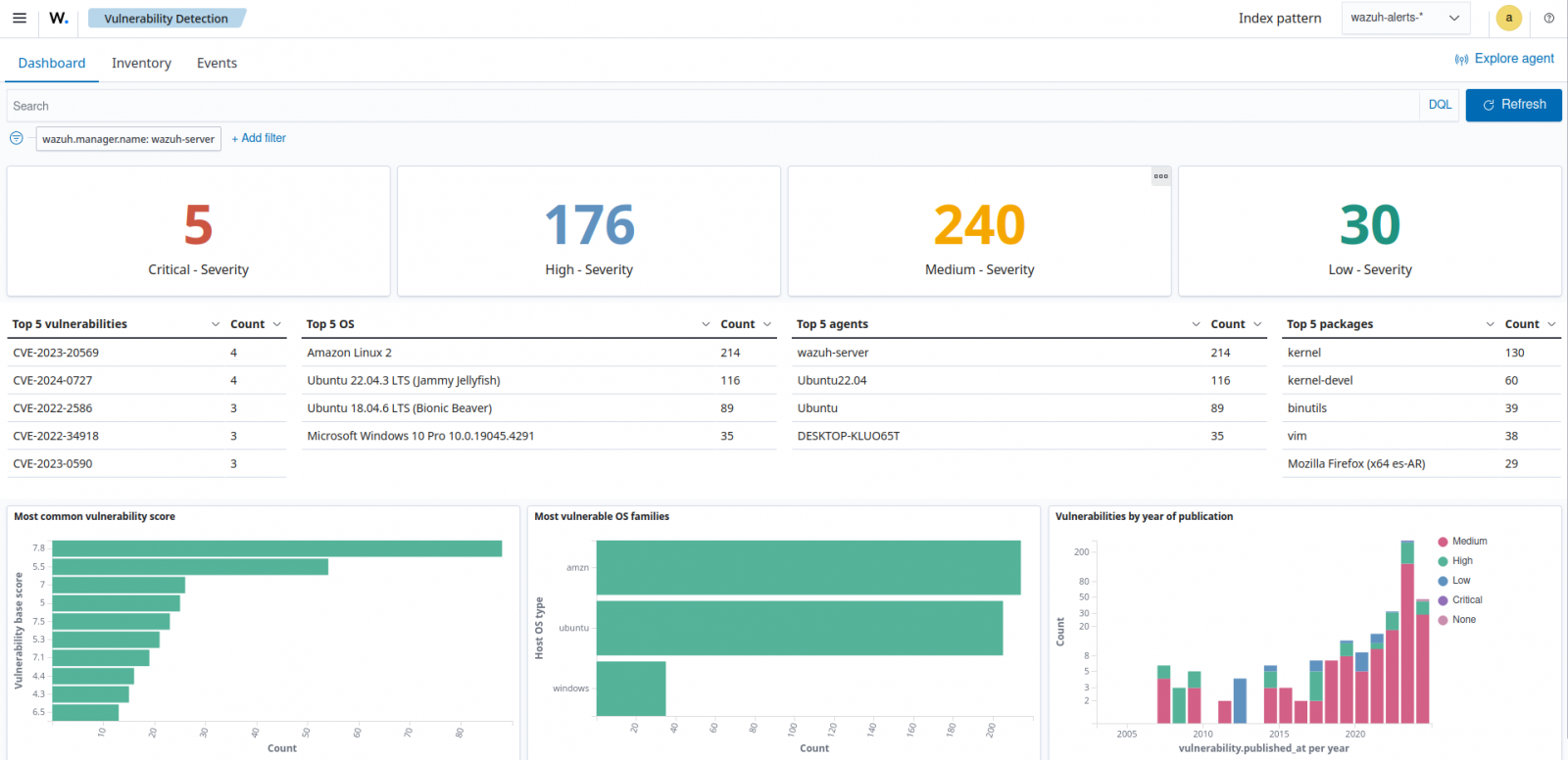
The Wazuh Vulnerability Detection module identifies vulnerabilities within the working system and put in functions by correlating software program stock with recognized vulnerability information within the Wazuh CTI platform. It generates alerts displayed on the Wazuh dashboard, giving a transparent view of vulnerabilities throughout all monitored endpoints.
This helps safety groups take proactive measures to cut back danger and strengthen system defenses earlier than exploitation happens.
The vulnerability detection dashboard in Determine 5 under highlights the package deal title, OS, agent, vulnerability ID, and severity of detected vulnerabilities.
Conclusion
Malware persistence methods allow attackers to take care of long-term entry to compromised methods, posing important dangers to organizational safety.
Defending in opposition to these methods requires a multi-layered strategy that mixes proactive measures, akin to system hardening, FIM, common patching, menace searching, and person monitoring.
Wazuh enhances menace protection by offering a number of capabilities to detect and reply to suspicious exercise throughout monitored endpoints, together with malware persistence methods. It allows safety groups to watch for unauthorized modifications, scheduled duties, uncommon processes, account modifications, and different indicators of compromise.
Begin utilizing Wazuh in the present day to strengthen your group’s protection technique. You can too be part of their group for skilled assist.
Sponsored and written by Wazuh.


