
North Korean menace actors planted 67 malicious packages within the Node Bundle Supervisor (npm) on-line repository to ship a brand new malware loader known as XORIndex to developer programs.
The packages collectively depend greater than 17,000 downloads and have been found by researchers at bundle safety platform Socket, who assess them to be a part of the continued Contagious Interview operation.
Socket researchers say that the marketing campaign follows menace exercise detected since April. Final month, the identical actor infiltrated npm with 35 packages that dropped data stealers and backdoors onto builders’ units.
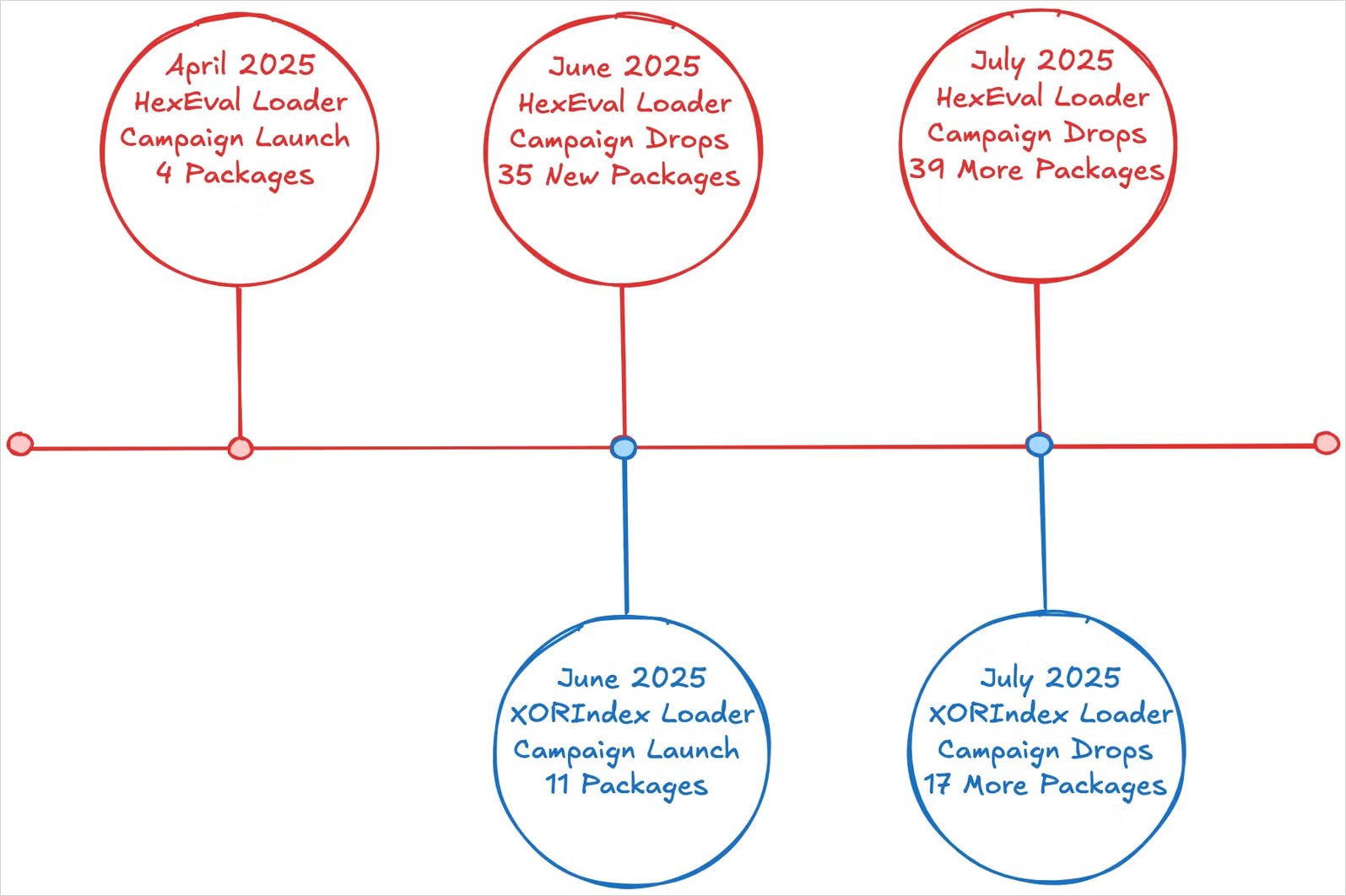
Supply: Socket
Overview of the assaults
Contagious Interview is a North Korean state-backed marketing campaign that targets largely builders with pretend job affords to trick them into working malicious code on their programs.
The aim varies from gathering delicate data that enables breaching firms to stealing cryptocurrency property.
The Node Bundle Supervisor (npm) is the default bundle supervisor for Node.js, a platform the place builders publish and set up JavaScript libraries and instruments. It’s broadly utilized in net growth, but in addition ceaselessly exploited by menace actors for malware distribution.
Out of the 67 packages the menace actors uploaded onto npm this time, there are a number of that seem to imitate or mix the names of professional software program tasks and libraries, like:
- vite-meta-plugin
- vite-postcss-tools
- vite-logging-tool
- vite-proc-log
- pretty-chalk
- postcss-preloader
- js-prettier
- flowframe
- figwrap
- midd-js, middy-js
When victims set up any of those packages, a ‘postinstall’ script executes to launch XORIndex Loader, a novel device that seems for use in parallel with HexEval Loader, a malware dropper noticed in previous assaults.
XORIndex Loader collects host information to profile every sufferer and sends it to a hardcoded command and management (C2) deal with, hosted on infrastructure from Vercel cloud utility firm.
The C2 server responds with a number of JavaScript payloads, that are executed on the sufferer’s system utilizing eval(). These payloads are usually the BeaverTail and the InvisibleFerret backdoor, each attributed to North Korean Contagious Interview operations.
The 2 items of malware present entry to compromised machines, permit information exfiltration, and might obtain extra payloads.
In accordance with the researchers, the North Korean hackers mix outdated and new instruments with refined modifications to evade detection, and each time npm cleans an an infection, they return by way of totally different npm accounts and bundle names.
“Contagious Interview menace actors will proceed to diversify their malware portfolio, rotating by new npm maintainer aliases, reusing loaders comparable to HexEval Loader and malware households like BeaverTail and InvisibleFerret, and actively deploying newly noticed variants together with XORIndex Loader” – Socket
“Defenders ought to anticipate continued iterations of those loaders throughout newly printed packages, usually with slight variations to evade detection,” the researchers warn.
Socket researchers say that they reported to npm all malicious packages from the most recent marketing campaign however a few of them should be out there within the repository.
You will need to double-check sourced packages to make sure they’re not typosquatting decoys, solely belief well-known tasks and publishers with a confirmed report, and scrutinize latest repository exercise for indicators of automation.
When potential, all the time look at the supply code for obfuscation and execute new libraries in remoted environments to guage their security.



