
Johnson Controls Worldwide has suffered what’s described as a large ransomware assault that encrypted lots of the firm units, together with VMware ESXi servers, impacting the corporate’s and its subsidiaries’ operations.
Johnson Controls is a multinational conglomerate that develops and manufactures industrial management programs, safety gear, air conditioners, and hearth security gear.
The corporate employs 100,000 individuals by way of its company operations and subsidiaries, together with York, Tyco, Luxaire, Coleman, Ruskin, Grinnel, and Simplex.
A weekend cyberattack
Yesterday, a supply informed BleepingComputer that Johnson Controls suffered a ransomware assault after initially being breached at its Asia places of work.
BleepingComputer has since discovered that the corporate suffered a cyberattack over the weekend that brought about the corporate to close down parts of its IT programs.
Since then, lots of its subsidiaries, together with York, Simplex, and Ruskin, have begun to show technical outage messages on web site login pages and buyer portals.
“We’re at the moment experiencing IT outages that will restrict some buyer purposes such because the Simplex Buyer Portal,” reads a message on the Simplex web site.
“We’re actively mitigating any potential impacts to our companies and can stay in communication with prospects as these outages are resolved.”
Supply: BleepingComputer
You probably have any info on this assault or different assaults, you may contact us confidentially by way of Sign at 646-961-3731
Clients of York, one other Johnson Controls subsidiary, report that they’re being informed the corporate’s programs are down, with some stating they have been informed it was as a result of a cyberattack.
“Their laptop system crashed over the weekend. Manufacturing and every little thing is down,” a York buyer posted to Reddit.
“I talked to our rep and he stated somebody hacked them,” posted one other buyer.
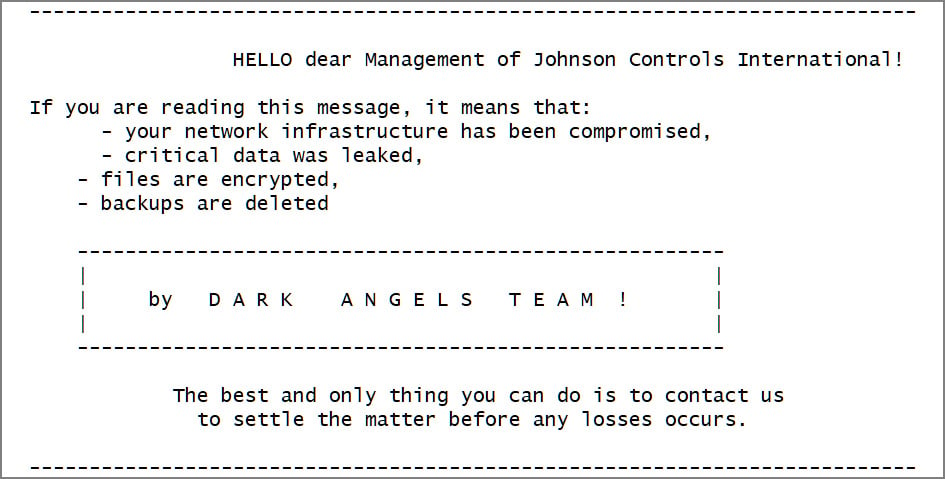
This morning, Nextron Techniques menace researcher Gameel Ali tweeted a pattern of a Darkish Angels VMware ESXi encryptor containing a ransom be aware stating it was used in opposition to Johnson Controls.
Supply: BleepingComputer
BleepingComputer has been informed that the ransom be aware hyperlinks to a negotiation chat the place the ransomware gang calls for $51 million to offer a decryptor and to delete stolen knowledge.
The menace actors additionally declare to have stolen over 27 TB of company knowledge and encrypted the corporate’s VMWare ESXi digital machines throughout the assault.
BleepingComputer has contacted Johnson Controls with questions concerning the assault however has not acquired a response.
After publication of our story, Johnson Controls confirmed the cybersecurity incident in a Kind 8-Ok submitting with the SEC, stating that they’re working with exterior cybersecurity specialists to research the incident and coordinating with insurers.
“Johnson Controls Worldwide plc (the “Firm”) has skilled disruptions in parts of its inside info know-how infrastructure and purposes ensuing from a cybersecurity incident. Promptly after detecting the difficulty, the Firm started an investigation with help from main exterior cybersecurity specialists and can also be coordinating with its insurers. The Firm continues to evaluate what info was impacted and is executing its incident administration and safety plan, together with implementing remediation measures to mitigate the influence of the incident, and can proceed taking extra steps as acceptable. So far, lots of the Firm’s purposes are largely unaffected and stay operational. To the extent doable, and according to its enterprise continuity plans, the Firm carried out workarounds for sure operations to mitigate disruptions and proceed servicing its prospects. Nevertheless, the incident has brought about, and is predicted to proceed to trigger, disruption to components of the Firm’s enterprise operations. The Firm is assessing whether or not the incident will influence its capacity to well timed launch its fourth quarter and full fiscal 12 months outcomes, in addition to the influence to its monetary outcomes.
The Firm’s investigation and remediation efforts are ongoing.”
Who’s the Darkish Angels ransomware gang?
Darkish Angels is a ransomware operation launched in Could 2022 when it started focusing on organizations worldwide.
Like virtually all human-operated ransomware gangs, Darkish Angels breaches company networks after which spreads laterally by way of the community. Throughout this time, the menace actors steal knowledge from file servers for use in double-extortion assaults.
Once they acquire entry to the Home windows area controller, the menace actors deploy the ransomware to encrypt all units on the community.
The menace actors initially used Home windows and VMware ESXi encryptors based mostly on the supply code leak for the Babuk ransomware.
Nevertheless, cybersecurity researcher MalwareHunterTeam tells BleepingComputer that the Linux encryptor used within the Johnson Controls assault is identical as ones utilized by Ragnar Locker since 2021.
Darkish Angels launched an information leak web site in April 2023 referred to as ‘Dunghill Leaks’ that’s used to extort its victims, threatening to leak knowledge if a ransom isn’t paid.
Supply: BleepingComputer
This extortion web site at the moment lists 9 victims, together with Sabre and Sysco, who just lately disclosed cyberattacks.
Replace 9/27/23: Added assertion from Kind 8-Ok submitting.


