
A novel tapjacking method can exploit consumer interface animations to bypass Android’s permission system and permit entry to delicate knowledge or trick customers into performing damaging actions, equivalent to wiping the gadget.
Not like conventional, overlay-based tapjacking, TapTrap assaults work even with zero-permission apps to launch a innocent clear exercise on high of a malicious one, a habits that is still unmitigated in Android 15 and 16.
TapTrap was developed by a group of safety researchers at TU Wien and the College of Bayreuth (Philipp Beer, Marco Squarcina, Sebastian Roth, Martina Lindorfer), and can be introduced subsequent month at the USENIX Safety Symposium.
Nonetheless, the group has already printed a technical paper that outlines the assault and a web site that summarizes a lot of the particulars.
How TapTrap works
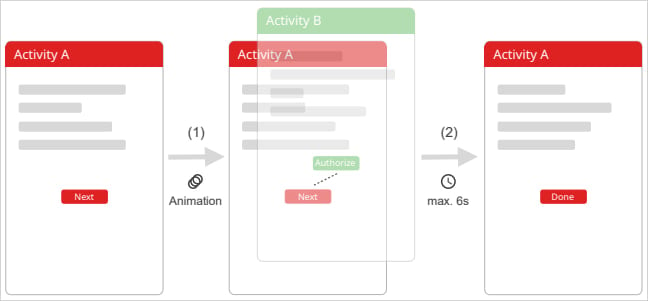
TapTrap abuses the best way Android handles exercise transitions with customized animations to create a visible mismatch between what the consumer sees and what the gadget really registers.
A malicious app put in on the goal gadget launches a delicate system display (permission immediate, system setting, and so on.) from one other app utilizing ‘startActivity()’ with a customized low-opacity animation.
“The important thing to TapTrap is utilizing an animation that renders the goal exercise practically invisible,” the researchers say on a web site that explains the assault.
“This may be achieved by defining a customized animation with each the beginning and ending opacity (alpha) set to a low worth, equivalent to 0.01,” thus making the malicious or dangerous exercise nearly fully clear.
“Optionally, a scale animation might be utilized to zoom into a particular UI aspect (e.g., a permission button), making it occupy the total display and rising the prospect the consumer will faucet it.”
Supply: taptrap.click on
Though the launched immediate receives all contact occasions, all of the consumer sees is the underlying app that shows its personal UI parts, as on high of it’s the clear display the consumer really engages with.
Pondering they work together with the bening app, a consumer could faucet on particular display positions that correspond to dangerous actions, equivalent to an “Permit” or “Authorize” buttons on practically invisible prompts.
A video launched by the researchers demonstrates how a recreation app may leverage TapTrap to allow digicam entry for a web site by way of Chrome browser.
Threat publicity
To verify if TapTrap may work with functions in Play Retailer, the official Android repository, the researchers analyzed near 100,000. They discovered that 76% of them are susceptible to TapTrap as they embrace a display (“exercise”) that meets the next circumstances:
- might be launched by one other app
- runs in the identical activity because the calling app
- doesn’t override the transition animation
- doesn’t look forward to the animation to complete earlier than reacting to consumer enter
The researchers say that animations are enabled on the most recent Android model except the consumer disables them from the developer choices or accessibility settings, exposing the gadgets to TapTrap assaults.
Whereas growing the assault, the researchers used Android 15, the most recent model on the time, however after Android 16 got here out in addition they ran some assessments on it.
Marco Squarcina advised BleepingComputer that they tried TapTrap on a Google Pixel 8a operating Android 16 and so they can affirm that the problem stays unmitigated.
GrapheneOS, the cellular working system targeted on privateness and safety, additionally confirmed to BleepingComputer that the most recent Android 16 is susceptible to the TapTrap method, and introduced that the their subsequent launch will embrace a repair.
BleepingComputer has contacted Google about TapTrap, and a spokesperson mentioned that the TapTrap downside can be mitigated in a future replace:
“Android is continually bettering its present mitigations in opposition to tapjacking assaults. We’re conscious of this analysis and we can be addressing this problem in a future replace. Google Play has insurance policies in place to maintain customers secure that each one builders should adhere to, and if we discover that an app has violated our insurance policies, we take acceptable motion.”- a Google consultant advised BleepingComputer.



