
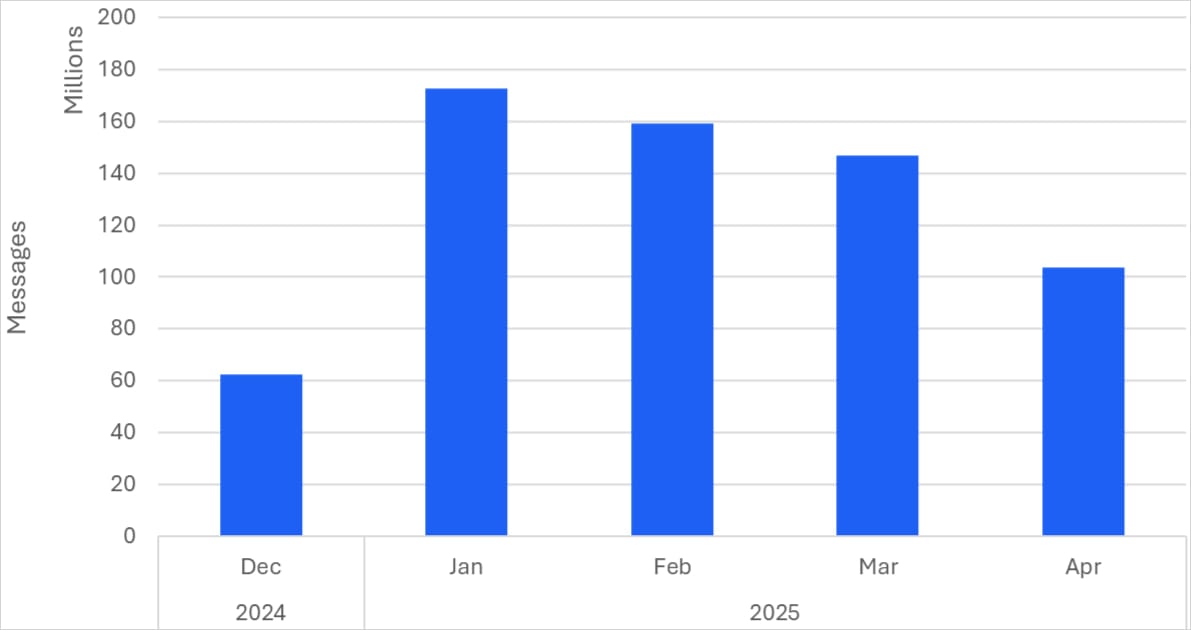
A brand new phishing package named ‘CoGUI’ despatched over 580 million emails to targets between January and April 2025, aiming to steal account credentials and fee knowledge.
The messages impersonate main manufacturers like Amazon, Rakuten, PayPal, Apple, tax companies, and banks.
The exercise culminated in January 2025, the place 170 campaigns despatched 172,000,000 phishing messages to targets, however the next months maintained equally spectacular volumes.
Proofpoint researchers who found the CoGUI campaigns famous that it is the highest quantity phishing marketing campaign they presently observe. The assaults primarily goal Japan, although smaller-scale campaigns have been additionally directed at america, Canada, Australia, and New Zealand.
CoGUI has been lively since no less than October 2024, however Proofpoint began monitoring it in December and onward.
Supply: Proofpoint
The analysts discovered a number of similarities to the Darcula phishing package, which has been linked to China-based operatives, and initially believed that the origin of the CoGUI assaults is similar.
Nonetheless, upon deeper examination, Proofpoint concluded that the 2 phishing kits are unrelated despite the fact that they’re each utilized by Chinese language menace actors.
CoGUI assault chain
The assault begins with a phishing e mail impersonating a trusted model, usually having pressing topic strains requiring the recipient’s motion.
The messages embrace a URL that redirects to a phishing web site hosted on the CoGUI phishing platform, however the hyperlink solely resolves if the goal meets particular standards pre-defined by the attackers.
These standards embrace their IP tackle (location), browser language, working system, display screen decision, and gadget sort (cellular or desktop).
If the factors aren’t met, victims are redirected to the model’s reliable web site that was impersonated to cut back suspicion.
Legitimate targets are redirected to a phishing web page that includes a pretend login type that mimics the design of the true model, tricking victims into getting into their delicate info.

Supply: Proofpoint
Proofpoint has additionally discovered that CoGUI was behind smishing campaigns concentrating on america with ‘excellent toll fee’ lures. Nonetheless, it famous that the majority of that exercise has now migrated to Darcula.
The researchers imagine CoGUI facilitates the operations of a number of menace actors, primarily from China, who predominantly goal Japanese customers.
Nonetheless, the package may very well be adopted by different cybercriminals with a special concentrating on scope at any second, leading to large assault waves hitting different international locations.
One of the simplest ways to mitigate phishing dangers isn’t to behave with haste when receiving emails requesting pressing motion, and at all times log in to the claimed platform independently as a substitute of following embedded hyperlinks.



