
Microsoft warns in regards to the safety dangers posed by default configurations in Kubernetes deployments, notably these utilizing out-of-the-box Helm charts, which may publicly expose delicate information.
In lots of instances, these Helm charts required no authentication, left exploitable ports open, and used weak or hardcoded passwords that had been trivial to interrupt.
A report printed by safety researchers Michael Katchinskiy and Yossi Weizman of Microsoft Defender for Cloud Analysis highlights three instances as examples of a broader safety situation that places Kubernetes workloads in danger.
Ease vs safety
Kubernetes is a broadly used open-source platform designed to automate the deployment, scaling, and administration of containerized purposes.
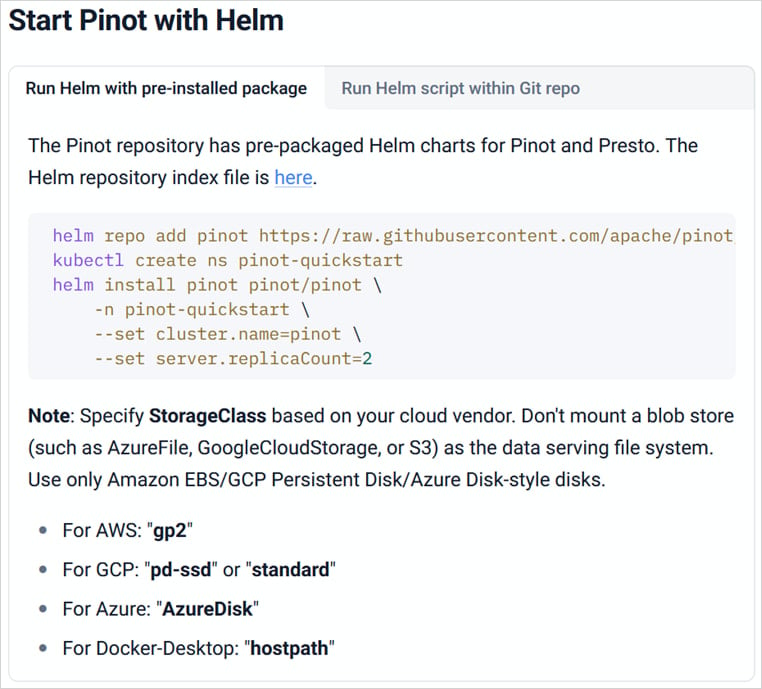
Helm is a bundle supervisor for Kubernetes, and charts are templates/blueprints for deploying apps on the platform, offering YAML recordsdata that outline key sources wanted to run an app.
Helm charts are standard as a result of they simplify and pace up advanced deployments. Nevertheless, as highlighted in Microsoft’s report, in lots of instances, the default settings in these charts lack correct safety measures.
Customers inexperienced with cloud safety usually deploy these Helm charts as they’re, unintentionally exposing providers to the web and permitting attackers to scan and exploit misconfigured purposes.
Supply: Microsoft
“Default configurations that lack correct safety controls create a extreme safety menace,” warns the Microsoft researchers.
“With out rigorously reviewing the YAML manifests and Helm charts, organizations might unknowingly deploy providers missing any type of safety, leaving them absolutely uncovered to attackers.”
“That is notably regarding when the deployed utility can question delicate APIs or enable administrative actions, which is precisely what we’ll shortly see.”
The researchers spotlight three instances of Helm charts that put Kubernetes environments susceptible to assaults, summarized as follows.
- Apache Pinot: Exposes core providers (pinot-controller and pinot-broker) through Kubernetes LoadBalancer providers with none authentication.
- Meshery: Public sign-up is allowed from uncovered IP, permitting anybody to register and acquire entry to cluster operations.
- Selenium Grid: A NodePort exposes the service throughout all nodes in a cluster, relying solely on exterior firewall guidelines for cover. The difficulty would not affect the official Helm chart, however many broadly referenced GitHub tasks.
Regarding Selenium Grid, Wiz and different cybersecurity corporations have beforehand noticed assaults concentrating on misconfigured cases to deploy XMRig miners to mine Monero cryptocurrency.
To mitigate the dangers, Microsoft recommends rigorously reviewing the default configuration of Helm charts to guage it from a safety perspective, making certain that it consists of authentication and community isolation.
Moreover, it is suggested to carry out common scans for misconfigurations that expose workload interfaces publicly and carefully monitor containers for suspicious exercise.



