A brand new evaluation of the delicate industrial spyware and adware referred to as Predator has revealed that its capacity to persist between reboots is obtainable as an “add-on function” and that it will depend on the licensing choices opted by a buyer.
“In 2021, Predator spyware and adware could not survive a reboot on the contaminated Android system (it had it on iOS),” Cisco Talos researchers Mike Gentile, Asheer Malhotra, and Vitor Ventura mentioned in a report shared with The Hacker Information. “Nevertheless, by April 2022, that functionality was being provided to their clients.”
Predator is the product of a consortium referred to as the Intellexa Alliance, which incorporates Cytrox (subsequently acquired by WiSpear), Nexa Applied sciences, and Senpai Applied sciences. Each Cytrox and Intellexa have been added to the Entity Checklist by the U.S. in July 2023 for “trafficking in cyber exploits used to achieve entry to data techniques.”
The most recent findings come greater than six months after the cybersecurity vendor detailed the inside workings of Predator and its harmonious equation with one other loader element referred to as Alien.
“Alien is essential to Predator’s profitable functioning, together with the extra elements loaded by Predator on demand,” Malhotra informed The Hacker Information on the time. “The connection between Alien and Predator is extraordinarily symbiotic, requiring them to repeatedly work in tandem to spy on victims.”
Beat AI-Powered Threats with Zero Belief – Webinar for Safety Professionals
Conventional safety measures will not lower it in as we speak’s world. It is time for Zero Belief Safety. Safe your information like by no means earlier than.
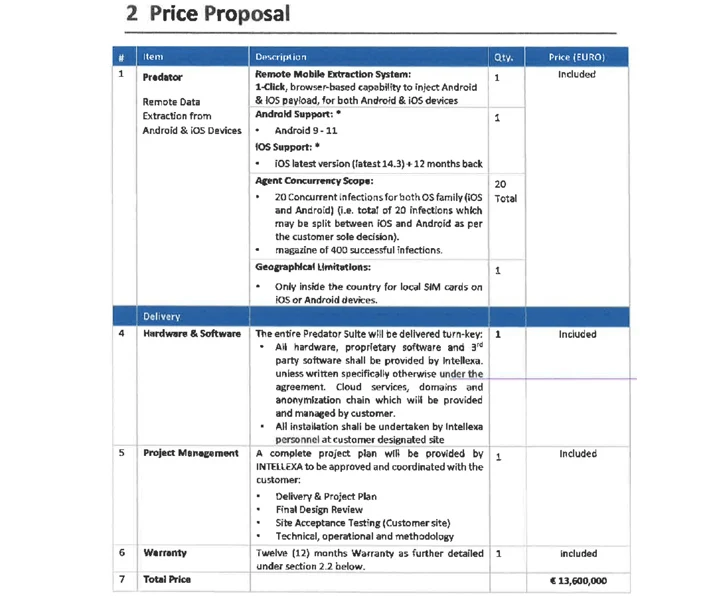
Predator, which may goal each Android and iOS, has been described as a “distant cell extraction system” that is offered on a licensing mannequin that run into hundreds of thousands of {dollars} based mostly on the exploit used for preliminary entry and the variety of concurrent infections, placing them out of attain of script kiddies and novice criminals.
Adware corresponding to Predator and Pegasus, which is developed by NSO Group, typically depend on zero-day exploit chains in Android, iOS, and internet browsers as covert intrusion vectors. As Apple and Google proceed to plug the safety gaps, these exploit chains could also be rendered ineffective, forcing them to return to the drafting board.
Nevertheless, it is value noting that the businesses behind mercenary surveillance instruments may also procure both full or partial exploit chains from exploit brokers and trend them into an operational exploit that may be employed to successfully breach goal units.
One other key facet of Intellexa’s enterprise mannequin is that offloads the work of establishing the assault infrastructure to the purchasers themselves, leaving it with room for believable deniability ought to the campaigns come to mild (because it inevitably does).
“The supply of Intellexa’s supporting {hardware} is completed at a terminal or airport,” the researchers mentioned.
“This supply methodology is named Price Insurance coverage and Freight (CIF), which is a part of the transport business’s jargon (‘Incoterms’). This mechanism permits Intellexa to say that they haven’t any visibility of the place the techniques are deployed and ultimately positioned.”
On high of that, Intellexa possesses “first-hand information” of whether or not their clients are performing surveillance operations exterior their very own borders owing to the truth that the operations are intrinsically related to the license, which, by default, is restricted to a single cellphone nation code prefix.
This geographic limitation, nonetheless, may be loosened for an extra charge.
Cisco Talos famous that whereas public publicity of private-sector offensive actors and their campaigns have been profitable at attribution efforts, it has had little impression on their capacity to conduct and develop their enterprise internationally, even when it could have an effect on their clients, corresponding to governments.
“It might enhance the prices by making them purchase or create new exploit chains however these distributors seem to have seamlessly acquired new exploit chains, enabling them to stay in enterprise by leaping from one set of exploits to a different as a way of preliminary entry,” the researchers mentioned.
“What is required is the general public disclosure of technical analyses of the cell spyware and adware and tangible samples enabling public scrutiny of the malware. Such public disclosures is not going to solely allow larger analyses and drive detection efforts but additionally impose improvement prices on distributors to continuously evolve their implants.”