A professional-Hamas risk actor referred to as Gaza Cyber Gang is concentrating on Palestinian entities utilizing an up to date model of a backdoor dubbed Pierogi.
The findings come from SentinelOne, which has given the malware the identify Pierogi++ owing to the truth that it is carried out within the C++ programming language in contrast to its Delphi- and Pascal-based predecessor.
“Latest Gaza Cybergang actions present constant concentrating on of Palestinian entities, with no noticed important modifications in dynamics for the reason that begin of the Israel-Hamas warfare,” safety researcher Aleksandar Milenkoski stated in a report shared with The Hacker Information.
Gaza Cyber Gang, believed to be lively since no less than 2012, has a historical past of hanging targets all through the Center East, notably Israel and Palestine, usually leveraging spear-phishing as a technique of preliminary entry.
Beat AI-Powered Threats with Zero Belief – Webinar for Safety Professionals
Conventional safety measures will not lower it in at the moment’s world. It is time for Zero Belief Safety. Safe your knowledge like by no means earlier than.
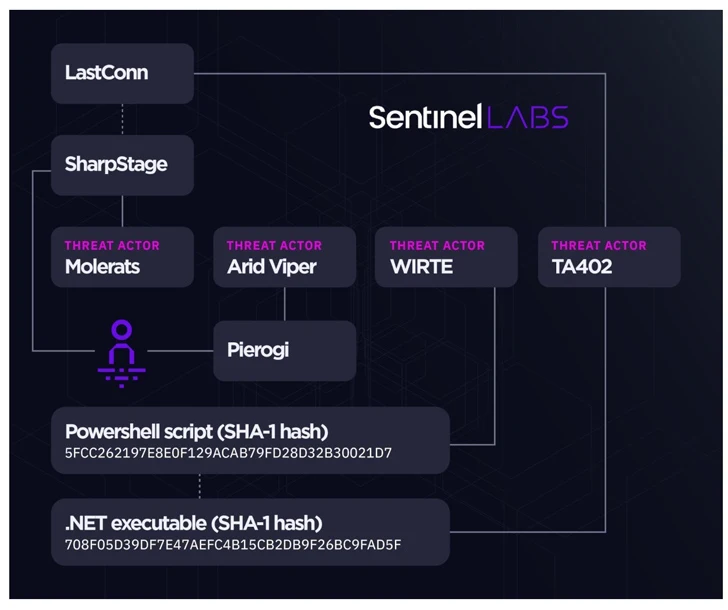
A number of the notable malware households in its arsenal embrace BarbWire, DropBook, LastConn, Molerat Loader, Micropsia, NimbleMamba, SharpStage, Spark, Pierogi, PoisonIvy, and XtremeRAT amongst others.
The risk actor is assessed to be a composite of a number of sub-groups that share overlapping victimology footprints and malware, corresponding to Molerats, Arid Viper, and a cluster known as Operation Parliament by Kaspersky.
In latest months, the adversarial collective has been linked to a sequence of assaults that ship improvised variants of its Micropsia and Arid Gopher implants in addition to a brand new preliminary entry downloader dubbed IronWind.
The newest set of intrusions mounted by Gaza Cyber Gang has been discovered to leverage Pierogi++ and Micropsia. The primary recorded use of Pierogi++ goes again to late 2022.
Assault chains are characterised by way of decoy paperwork written in Arabic or English and pertaining to issues of curiosity to Palestinians to ship the backdoors.
Cybereason, which make clear Pierogi in February 2020, described it as an implant that enables attackers to spy on focused victims and that the “instructions used to speak with the [command-and-control] servers and different strings within the binary are written in Ukrainian.”
“The backdoor could have been obtained in underground communities slightly than home-grown,” it assessed on the time.
Each Pierogi and Pierogi++ are outfitted to take screenshots, execute instructions, and obtain attacker-provided recordsdata. One other notable side is that the up to date artifacts now not characteristic any Ukrainian strings within the code.
SentinelOne’s investigation into Gaza Cyber Gang’s operations have additionally yielded tactical connections between two disparate campaigns known as Large Bang and Operation Bearded Barbie, along with reinforcing ties between the risk actor and WIRTE, as beforehand disclosed by Kaspersky in November 2021.
The sustained concentrate on Palestine however, the invention of Pierogi++ underscores that the group continues to refine and retool its malware to make sure profitable compromise of targets and to keep up persistent entry to their networks.
“The noticed overlaps in concentrating on and malware similarities throughout the Gaza Cybergang sub-groups after 2018 means that the group has seemingly been present process a consolidation course of,” Milenkoski stated.
“This probably consists of the formation of an inside malware improvement and upkeep hub and/or streamlining provide from exterior distributors.”