
cryptocurrency
View all →

Shiba Inu Coin Price Prediction — Can SHIB Coin reach $1 in 2023
How to Build a Crypto Mining Rig? Bitcoin Mining in 2023

Earn Free 1% Crypto Bonus on Deposit & Withdrawal fees Payback
technology
View all →Anthropic’s too-scary-to-release AI hacking tool is actually coming out — kind of

Google Translate and Meet are getting a big-time language translation boost

AI Mode in Google Search will soon let everyone build interactive diagrams for free
Is your YouTube Shorts ‘Dislike’ button missing? Here’s what’s going on
stock
View all →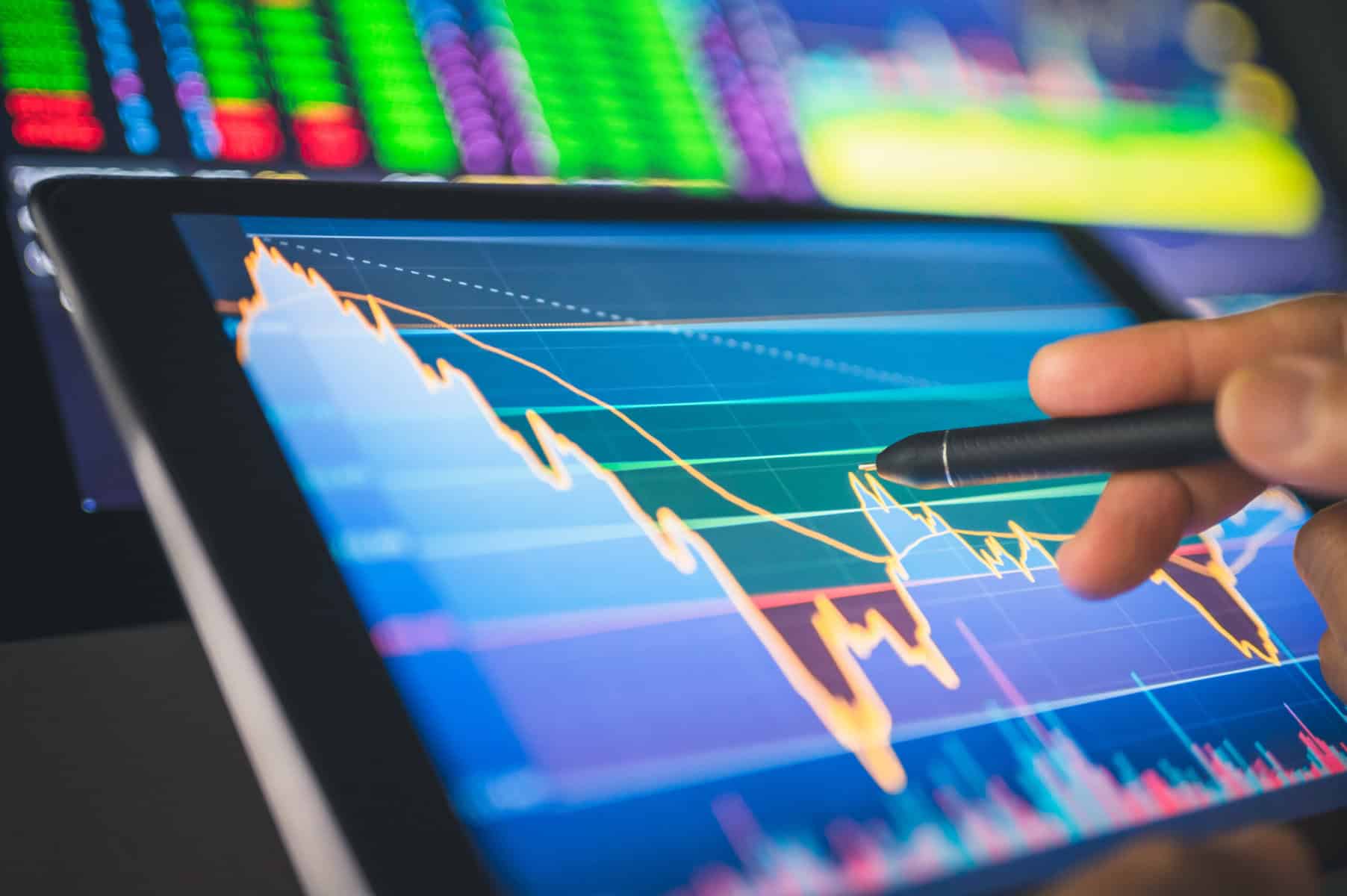
2 Dividend Blue-Chip Giants Looking Ideal After a Recent Pullback

3 Canadian Stocks That Look Undervalued and Worth Buying Right Now

3 Canadian Blue-Chip Stocks to Hold Through 2026 and Beyond

This Canadian Stock is Up 94% and Still a Great Deal
cyber security
View all →Smashing Security podcast #471: This AI worm just rewrote its own rules
Smashing Security podcast #470: This AI security flaw might be impossible to fix
Smashing Security podcast #469: What your Oura ring won’t tell you
Smashing Security podcast #468: High-speed train hacks and homicidal lawnmowers
forex
View all →
28 Motivational Quotes from Top Traders

What Lions Can Teach Us About Professional Trading

10 Reasons You’re Not Making Money Trading

How Simple Maths Can Increase Your Average Profit Per Trade 10-Fold
politics
View all →
Socialism's next test: Swing states

Jill Biden dismisses Democrats’ infighting concerns: ‘Things are going to move forward’

Who watches the watch parties?

Trump ally admits political risk of Iran war at campaign event
latest articles

Why The Bitcoin Price Could Mark A Generational Bottom And Rise Over 200%
Bitcoin’s investor sentiment is in ruins, but buried inside the wreckage, a technical signal that has appeared only at the most consequential...

28 Motivational Quotes from Top Traders
Trading is a lot like riding a roller coaster. Although it obviously is fun and exciting, there will be times when you...

What Lions Can Teach Us About Professional Trading
Any professional trader, whether they realize it or not, shares many traits and behaviors with the ‘King of the jungle’. A lion...

10 Reasons You’re Not Making Money Trading
If you aren’t making money trading yet, the good news is that we can easily diagnose what you’re doing wrong. The reasons...

How Simple Maths Can Increase Your Average Profit Per Trade 10-Fold
You’ve probably read trading articles that talk about how your “winners need to be greater than your losers”, it’s used so much...

AXITrader Million Dollar Trader Competition – Winner Announced
Press Release – Sydney, Australia – 13 May 2016 After several months of live trading, AxiTrader is pleased to announce the winner...

Nial Fuller Wins Million Dollar Trader Competition
Press Release – Gold Coast, Australia, May 16, 2016 Renowned trader Nial Fuller has won the $1 million top prize in one...

Trading Price Action With or Without Confirmation: You Decide
As a price action trader, we basically have two ways to trade; with or without a ‘confirmation’ signal. Now, I put the...

Why The Best Trades Are SO Hard To Pull The Trigger On
Does the following trading scenario sound familiar to you?… A market has broken up through a level and starts trending aggressively, starting...
Watching Charts Intraday Will Harm Your Trading Results
Trading is not the easiest profession in the world to succeed at, as you may well know by now. We need to...
investingLive European markets wrap: A breather while US-Iran tensions linger; ECB up next
Headlines:Iran maintains that Strait of Hormuz is closed until further noticeUS-Iran talks are still on track according to a CNN diplomatic sourceUS...
The Google Play Store can’t stop crashing on Pixel and Galaxy Watches (Update)
Credit: Kaitlyn Cimino / Android Authority TL;DR Pixel Watch owners are having issues with the Google Play Store. Reports claim that the...