
A brand new set of vulnerabilities in 5G modems by Qualcomm and MediaTek, collectively referred to as “5Ghoul,” influence 710 5G smartphone fashions from Google companions (Android) and Apple, routers, and USB modems.
5Ghoul was found by college researchers from Singapore and consists of 14 vulnerabilities in cellular communication techniques, 10 of which have been publicly disclosed and 4 withheld for safety causes.
The 5Ghoul assaults vary from short-term service disruptions to community downgrades, which can be extra extreme from a safety standpoint.
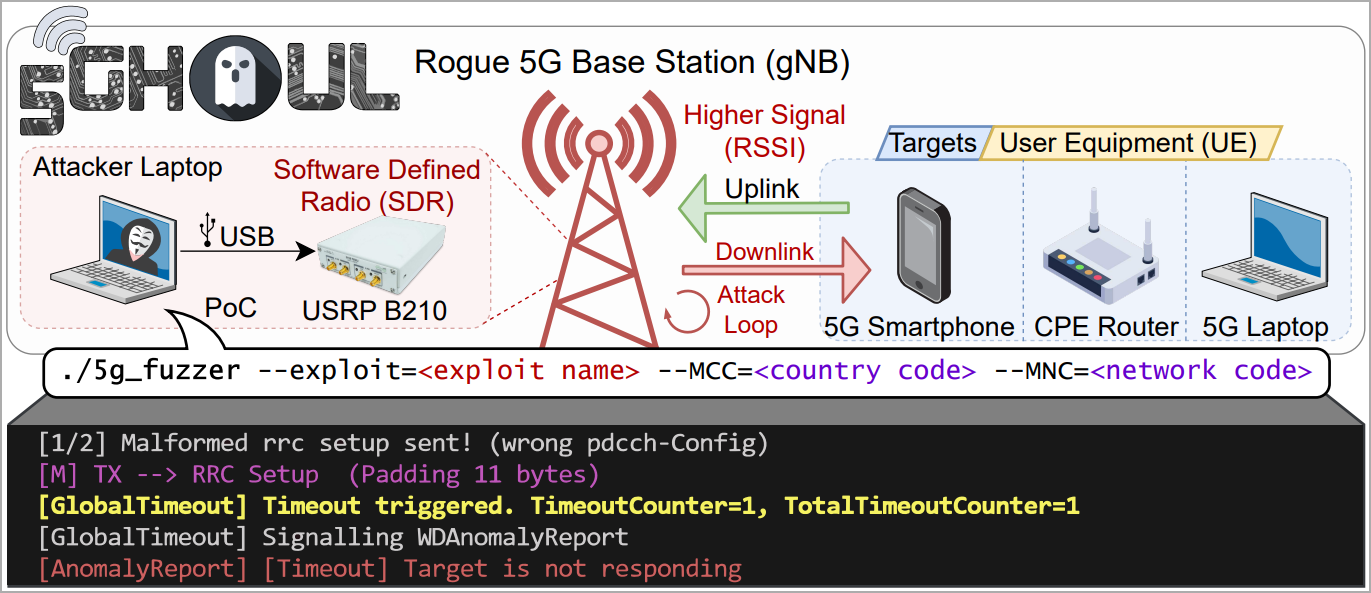
The researchers found the failings whereas experimenting with 5G modem firmware evaluation and report that the failings are straightforward to take advantage of over-the-air by impersonating a respectable 5G base station.
This is applicable even when attackers lack details about the goal’s SIM card, because the assault happens earlier than the NAS authentication step.
“The attacker doesn’t want to pay attention to any secret data of the goal UE e.g., UE’s SIM card particulars, to finish the NAS community registration,” explains the researchers on their web site.
“The attacker solely must impersonate the respectable gNB utilizing the recognized Cell Tower connection parameters (e.g., SSB ARFCN, Monitoring Space Code, Bodily Cell ID, Level A Frequency).”
Supply: asset-group.github.io
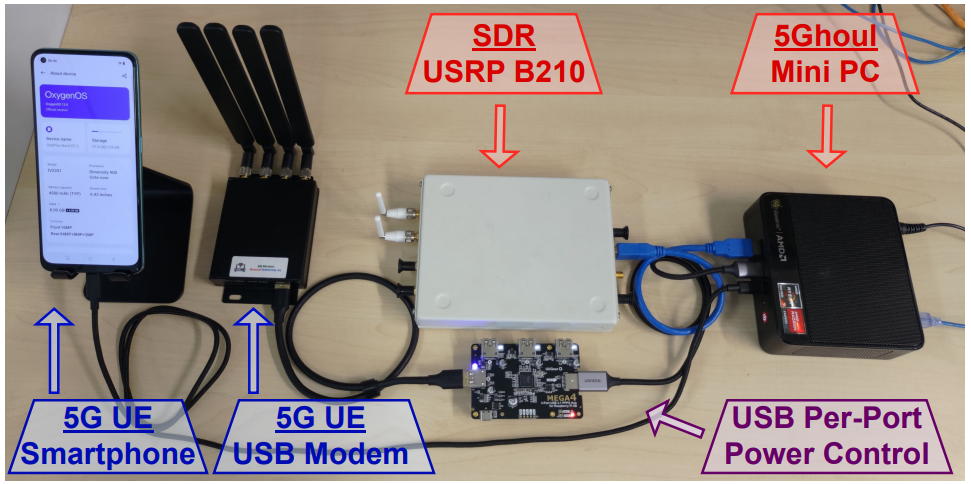
The above is achievable at the price of a number of thousand USD, utilizing open-source software program for community evaluation and fuzzing, a mini PC, a software program outlined radio (SDR), and miscellaneous gear like cables, antennas, energy provides, and so forth.
Supply: asset-group.github.io
5Ghoul vulnerability particulars
The ten 5Ghoul vulnerabilities which have been publicly disclosed to Qualcomm and MediaTek as of December 7, 2023, are:
- CVE-2023-33043: Invalid MAC/RLC PDU inflicting Denial of Service (DoS) in Qualcomm X55/X60 modems. Attackers can ship an invalid downlink MAC body to the goal 5G UE from a close-by malicious gNB, resulting in a short lived cling and modem reboot.
- CVE-2023-33044: NAS Unknown PDU inflicting DoS in Qualcomm X55/X60 modems. This vulnerability permits attackers to ship an invalid NAS PDU to the goal UE, leading to modem failure and reboot.
- CVE-2023-33042: Disabling 5G/Downgrade through Invalid RRC pdcch-Config in Qualcomm X55/X60 modems, resulting in both downgrade or denial of service. An attacker can ship a malformed RRC body in the course of the RRC Connect Process, disabling 5G connectivity and requiring a handbook reboot for restoration.
- CVE-2023-32842: Invalid RRC Setup spCellConfig inflicting DoS in MediaTek Dimensity 900/1200 modems. The vulnerability entails sending a malformed RRC Connection Setup, resulting in modem failure and reboot in affected gadgets.
- CVE-2023-32844: Invalid RRC pucch CSIReportConfig inflicting DoS in MediaTek Dimensity 900/1200 modems. Attackers can ship a malformed RRC Connection Setup, inflicting the modem to fail and reboot.
- CVE-2023-20702: Invalid RLC Information Sequence inflicting DoS (null pointer dereference) in MediaTek Dimensity 900/1200 modems. An attacker can exploit this by sending a malformed RLC Standing PDU, resulting in a modem crash and reboot.
- CVE-2023-32846: Truncated RRC physicalCellGroupConfig inflicting DoS (null pointer dereference) in MediaTek Dimensity 900/1200 modems. Malformed RRC Connection Setup could cause reminiscence entry errors, resulting in a modem crash.
- CVE-2023-32841: Invalid RRC searchSpacesToAddModList inflicting DoS in MediaTek Dimensity 900/1200 modems. This entails sending a malformed RRC Connection Setup, inflicting a modem crash in affected gadgets.
- CVE-2023-32843: Invalid RRC Uplink Config Aspect inflicting DoS in MediaTek Dimensity 900/1200 modems. Sending a malformed RRC Connection Setup may end up in modem failure and reboot in affected gadgets.
- CVE-2023-32845: Null RRC Uplink Config Aspect inflicting DoS in MediaTek Dimensity 900/1200 modems. Malformed RRC Connection Setup can set off a modem crash by setting sure RRC payload fields to null.
CVE-2023-33042 is especially regarding as a result of it might power a tool to disconnect from a 5G community and fall again to 4G, exposing it to potential vulnerabilities within the 4G area that expose it to a broader vary of assaults.
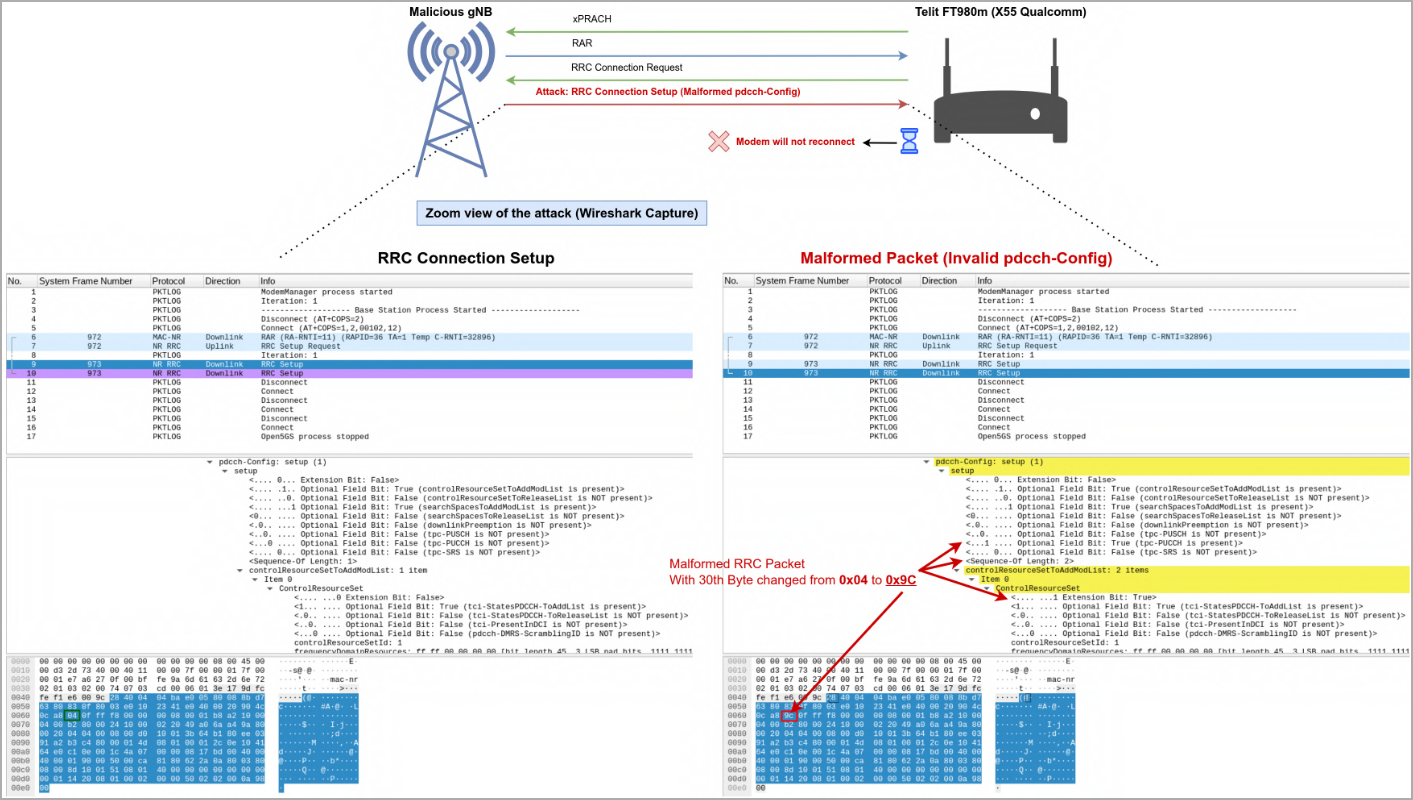
Supply: asset-group.github.io
The DoS flaws in these vulnerabilities trigger the gadgets to lose all connectivity till they’re rebooted. This is not as crucial, though it might nonetheless have important implications in mission-critical environments that depend on mobile service.
You will need to notice that the disclosed flaws aren’t restricted to the gadgets talked about within the above checklist.
Figuring out all impacted fashions is ongoing, however the researchers have already confirmed that 714 smartphones from 24 manufacturers are impacted.
Some susceptible manufacturers embrace telephones from POCO, Black, Lenovo, AGM, Google, TCL, Redmi, HTC, Microsoft, and Gigaset, with the whole checklist within the picture under.
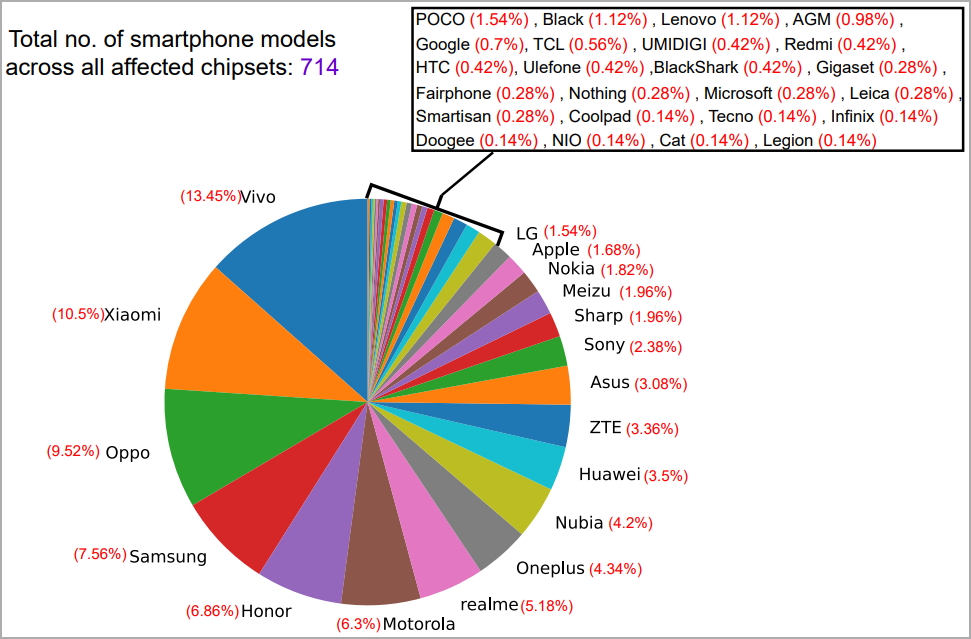
Supply: asset-group.github.io
To study extra concerning the 5Ghoul flaws, their exploitation potential and ramifications, and technical data will be present in the researchers’ whitepaper.
A proof-of-concept (PoC) exploit equipment can be discovered of their GitHub repository.
Vendor response and fixes
Each Qualcomm and MediaTek launched safety bulletins on Monday for the disclosed 5Ghoul vulnerabilities,
The safety updates had been made accessible to system distributors two months in the past. Nonetheless, given the complexity of the software program provide, particularly on Android, will probably be some time earlier than the fixes attain the tip customers through safety updates.
Inevitably, some impacted smartphone fashions and different gadgets won’t ever obtain the fixes as they’ll doubtless attain finish of help first.
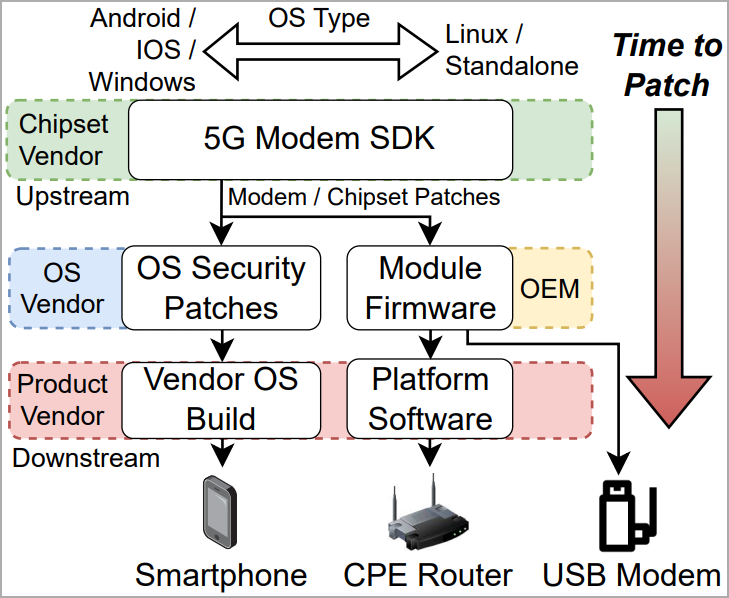
Supply: asset-group.github.io
If you happen to’re overly frightened about 5Ghool flaws, the one sensible answer is to keep away from utilizing 5G completely till fixes can be found.
Indicators of a 5Ghoul assault embrace lack of 5G connections, incapacity to re-connect till the system is rebooted, and constant drop to 4G regardless of the supply of a 5G community within the space.


