The most recent variants of the P2Pinfect botnet at the moment are specializing in infecting units with 32-bit MIPS (Microprocessor with out Interlocked Pipelined Phases) processors, equivalent to routers and IoT units.
Attributable to their effectivity and compact design, MIPS chips are prevalent in embedded programs like routers, residential gateways, and online game consoles.
P2Pinfect was found in July 2023 by Palo Alto Networks analysts (Unit 42) as a brand new Rust-based worm that targets Redis servers susceptible to CVE-2022-0543.
Following its preliminary discovery, Cado Safety analysts who examined P2Pinfect reported that it was abusing the Redis replication function to unfold, creating replicas of the contaminated occasion.
Later, in September, Cado warned about spiking P2Pinfect botnet exercise focusing on programs in america, Germany, the UK, Japan, Singapore, Hong Kong, and China.
At this time, Cado stories a brand new growth regarding the botnet, which marks a big evolution within the undertaking’s focusing on scope and skill to evade detection.
New MIPS variant
The most recent assaults noticed on Cado’s honeypots scan for SSH servers that use weak credentials and try and add the MIPS binary by way of SFTP and SCP.
Curiously, propagation for the MIPS variant is not restricted to SSH, because the researchers noticed makes an attempt to run the Redis server on MIPS units via an OpenWRT package deal named ‘redis-server.’
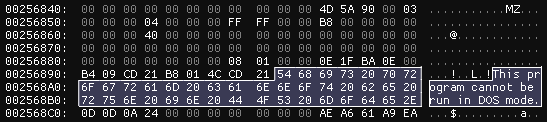
Throughout static evaluation, Cado researchers discovered that the brand new P2Pinfect is a 32-bit ELF binary with no debug data and an embedded 64-bit Home windows DLL, which acts as a loadable module for Redis to allow shell command execution on the host.
Extra evasive
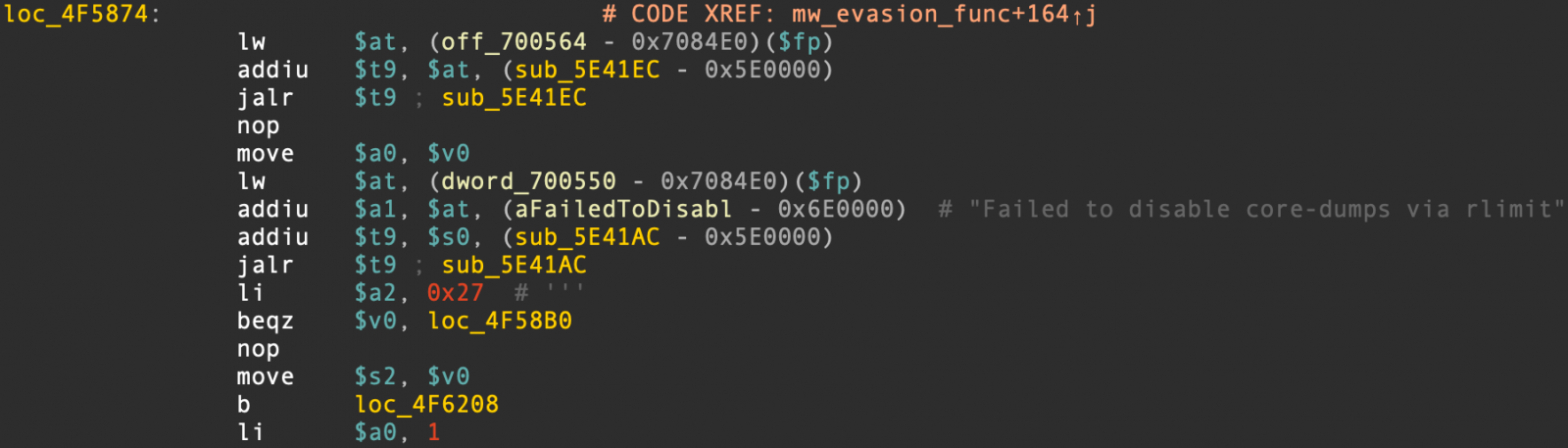
The most recent variant of P2Pinfect implements refined and multifaceted evasion mechanisms that make its detection and evaluation far more difficult.
Cado has highlighted the next evasion mechanisms launched within the newest P2Pinfect:
- Implementation of a verify for the ‘TracerPid’ worth within the course of standing file to find out if evaluation instruments are tracing the malware course of, and terminating whether it is.
- Utilization of system calls to disable Linux core dumps, stopping the dumping of reminiscence contents that include traces of its exercise.
- The embedded DLL accommodates a perform for evading digital machines (VMs)
The continual growth of P2Pinfect and enlargement of the malware’s focusing on signifies a excessive stage of coding abilities and dedication from its authors.
It is essential to focus on that regardless of in depth monitoring of the botnet via numerous campaigns over time, Cado Safety stays unsure in regards to the exact targets of the malware’s operators.
These targets may embody cryptocurrency mining, launching Distributed Denial of Service (DDoS) assaults, facilitating visitors proxying, and executing information theft.


