By Lakshya Mathur & Yashvi Shah
Phishing attackers goal to deceive people into revealing delicate info for monetary acquire, credential theft, company community entry, and spreading malware. This technique typically includes social engineering techniques, exploiting psychological elements to control victims into compromising actions that may have profound penalties for private and organizational safety.
Over the past 4 months, McAfee Labs has noticed a rising pattern within the utilization of PDF paperwork for conducting a succession of phishing campaigns. These PDFs have been delivered as electronic mail attachments.
Attackers favor utilizing PDFs for phishing as a result of file format’s widespread trustworthiness. PDFs, generally seen as reputable paperwork, present a flexible platform for embedding malicious hyperlinks, content material, or exploits. By leveraging social engineering and exploiting the familiarity customers have with PDF attachments, attackers enhance the chance of profitable phishing campaigns. Moreover, PDFs provide a way to bypass electronic mail filters that will concentrate on detecting threats in different file codecs.
The noticed phishing campaigns utilizing PDFs have been various, abusing varied manufacturers corresponding to Amazon and Apple. Attackers typically impersonate well-known and trusted entities, rising the probabilities of luring customers into interacting with the malicious content material. Moreover, we’ll delve into distinct forms of URLs utilized by attackers. By understanding the themes and URL patterns, readers can improve their consciousness and higher acknowledge potential phishing makes an attempt.
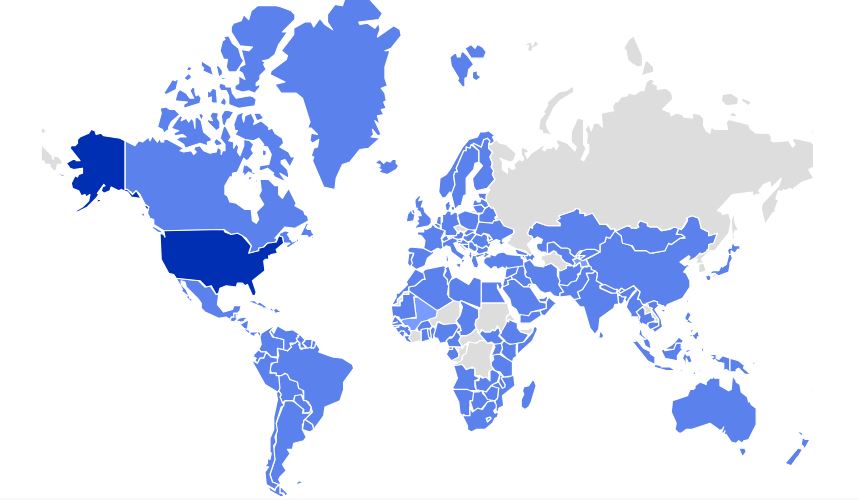
Determine 1 – PDF Phishing Geo Heatmap exhibiting McAfee prospects focused in final 1 month
Completely different Themes of Phishing
Attackers make use of a variety of company themes of their social engineering techniques to entice victims into clicking on phishing hyperlinks. Notable manufacturers corresponding to Amazon, Apple, Netflix, and PayPal, amongst others, are sometimes mimicked. The PDFs are rigorously crafted to induce a way of urgency within the sufferer’s thoughts, using phrases like “your account must be up to date” or “your ID has expired.” These techniques goal to control people into taking immediate motion, contributing to the success of the phishing campaigns.
Under are a few of the examples:
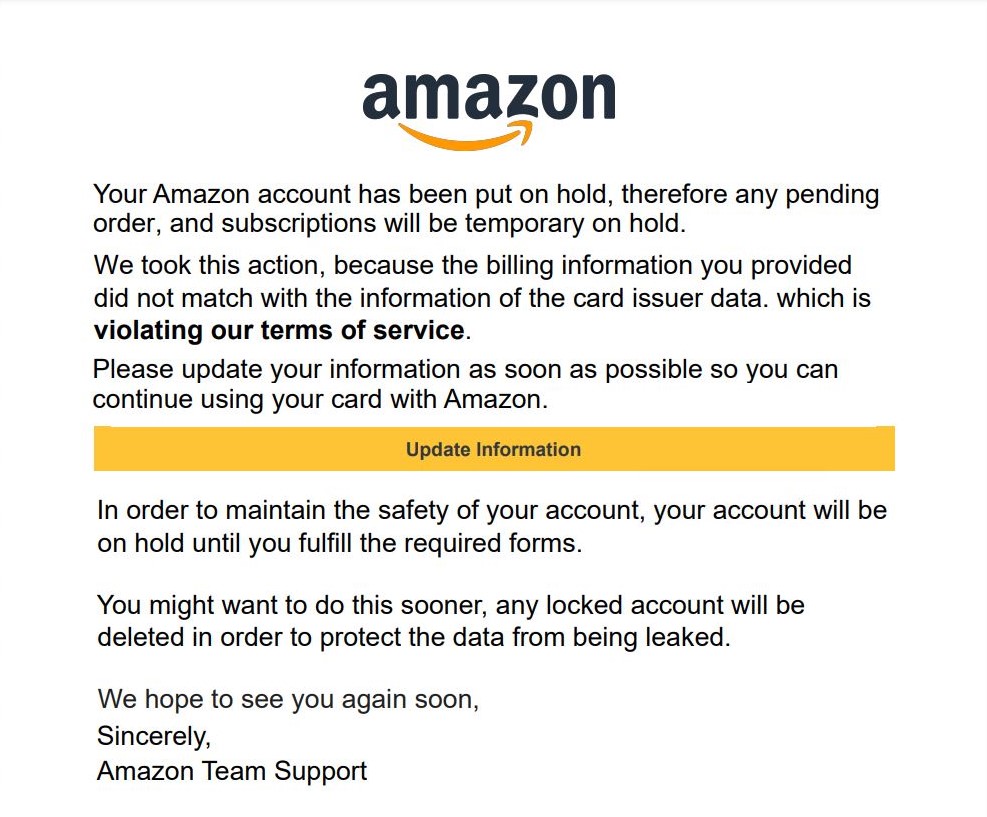
Determine 2 – Pretend Amazon PDF Phish
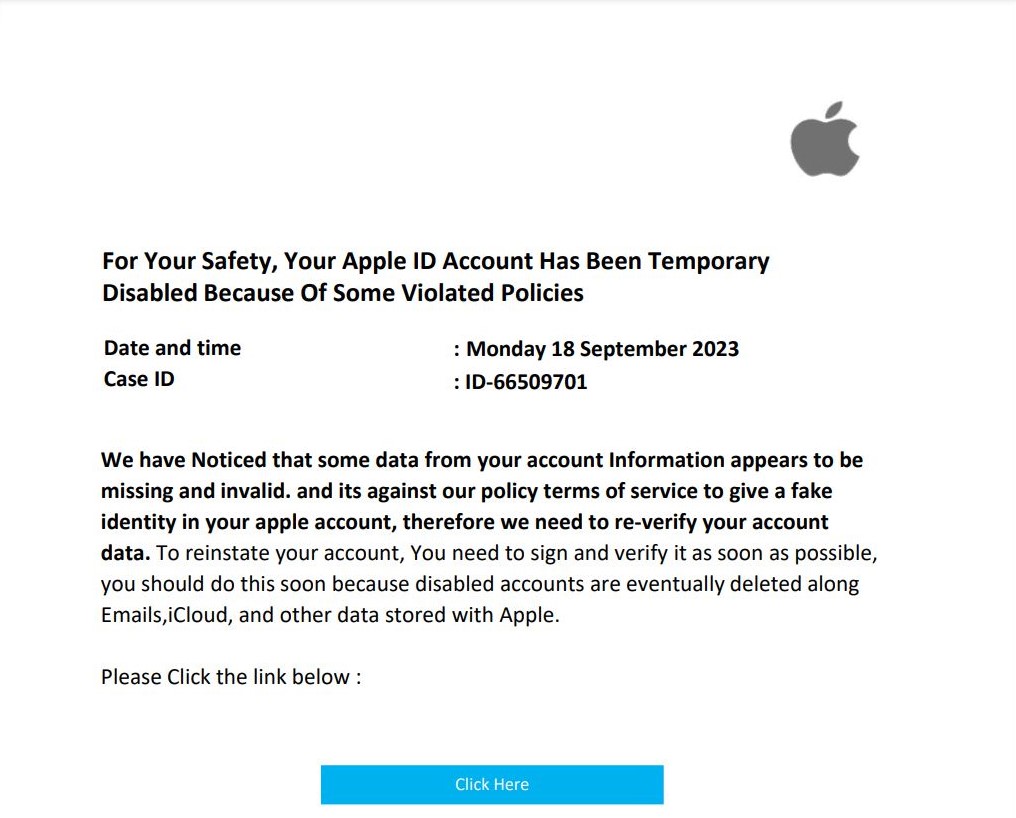
Determine 3 – Pretend Apple PDF Phish
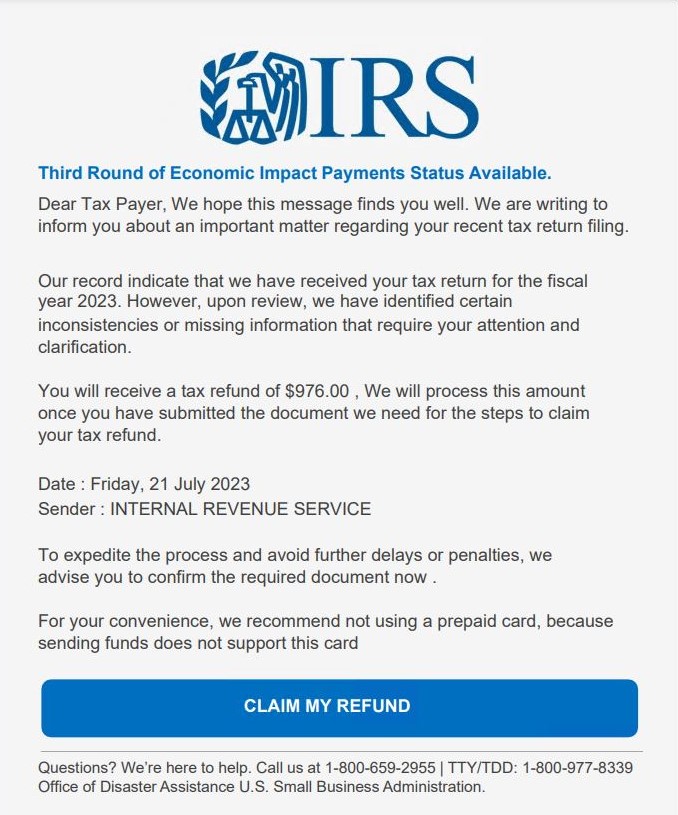
Determine 4 – Pretend Inner Income Service PDF Phish
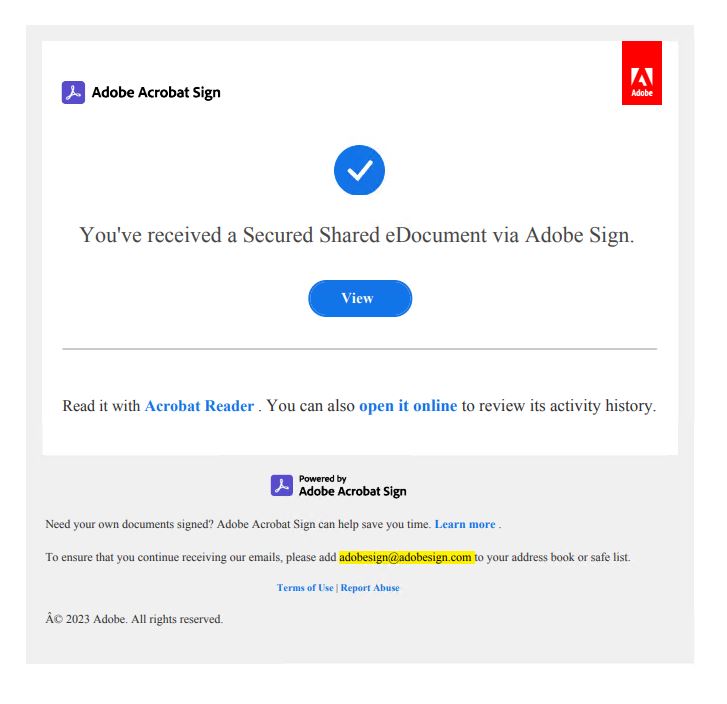
Determine 5 – Pretend Adobe PDF Phish
Under are the stats on the quantity of assorted themes we’ve seen in these phishing campaigns.
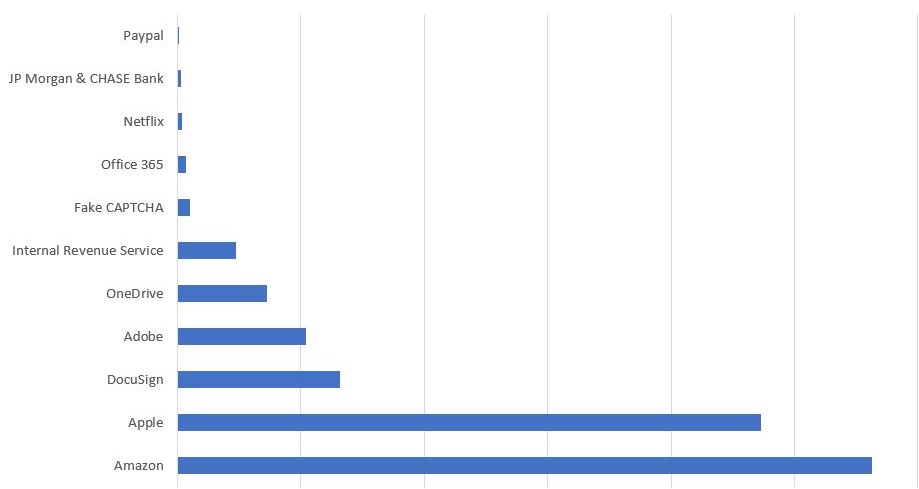
Determine 6 – Completely different themed marketing campaign stats primarily based on McAfee prospects hits in final 1 month
Abuse of LinkedIn and Google hyperlinks
Cyber attackers are exploiting the favored skilled networking platform LinkedIn and leveraging Google Apps Script to redirect customers to phishing web sites. Allow us to look at every technique of abuse individually.
Within the case of LinkedIn, attackers are using good hyperlinks to avoid Anti-Virus and different safety measures. Good hyperlinks are integral to the LinkedIn Gross sales Navigator service, designed for monitoring and advertising enterprise accounts.
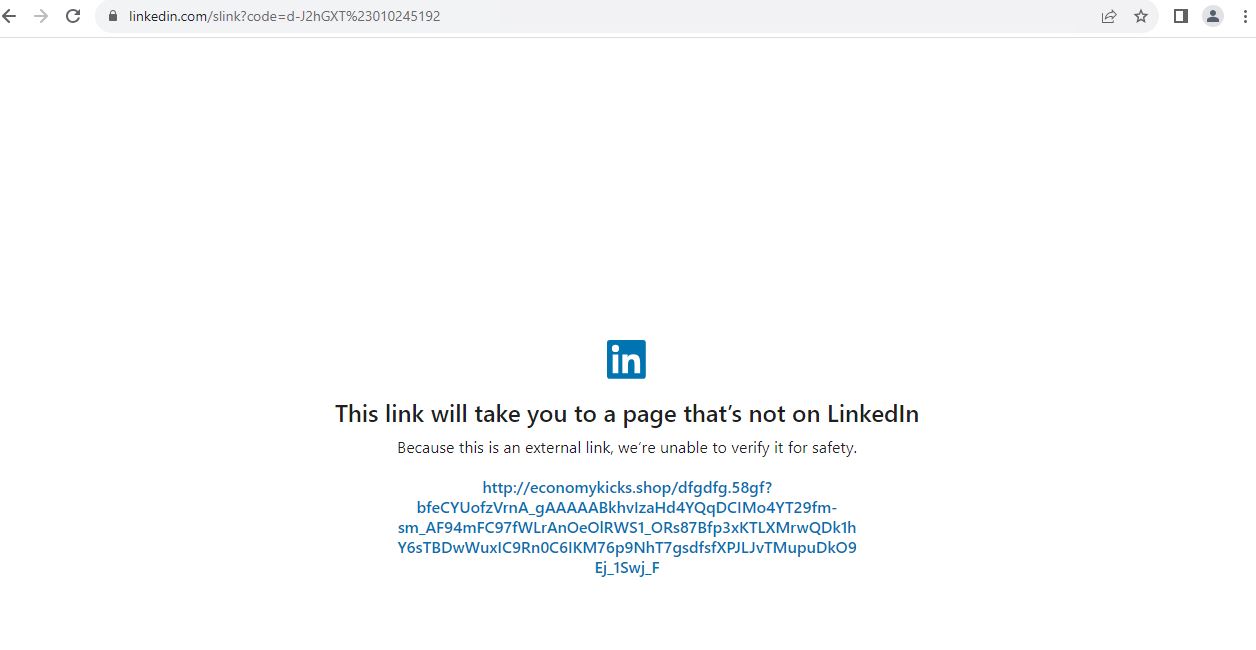
Determine 7 – LinkedIn Good hyperlink redirecting to an exterior web site
By using these good hyperlinks, attackers redirect their victims to phishing pages. This strategic strategy permits them to bypass conventional safety measures, as the usage of LinkedIn as a referrer provides a component of legitimacy, making it more difficult for safety techniques to detect and block malicious exercise.
Along with exploiting LinkedIn, attackers are leveraging the performance of Google Apps Script to redirect customers to phishing pages. Google Apps Script serves as a JavaScript-based growth platform used for creating net purposes and varied different functionalities. Attackers embed malicious or phishing code inside this platform, and when victims entry the related URLs, it triggers the show of phishing or malicious pages.
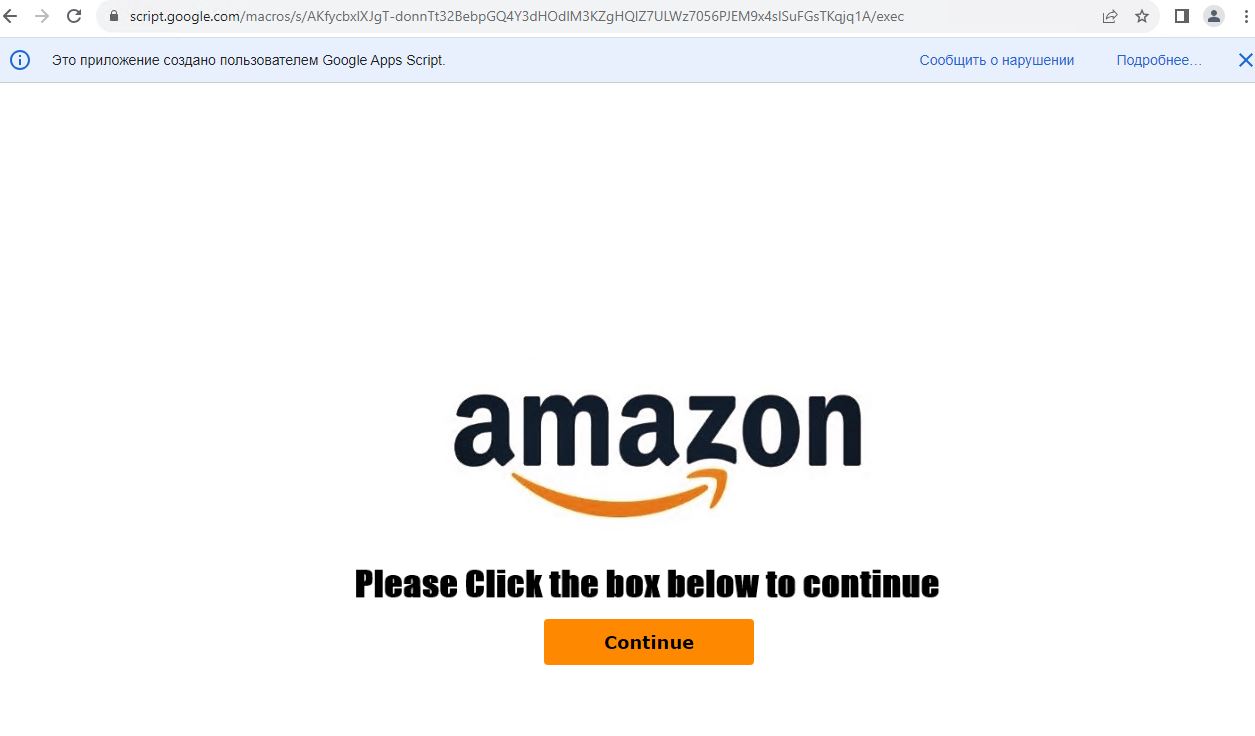
Determine 8 – Amazon faux web page displayed on accessing Google script URL
As proven in Determine 8, when victims click on on the “Proceed” button, they’re subsequently redirected to a phishing web site.
Abstract
Crafting extremely convincing PDFs mimicking reputable corporations has develop into effortlessly achievable for attackers. These meticulously engineered PDFs create a way of urgency via skillful social engineering, prompting unsuspecting prospects to click on on embedded phishing hyperlinks. Upon taking the bait, people are redirected to misleading phishing web sites, the place attackers request delicate info. This refined tactic is deployed on a worldwide scale, with these convincing PDFs distributed to 1000’s of shoppers worldwide. Particularly, we highlighted the rising use of PDFs in phishing campaigns over the previous 4 months, with attackers adopting various themes corresponding to Amazon and Apple to use consumer belief. Notably, phishing techniques lengthen to widespread platforms like LinkedIn, the place attackers leverage good hyperlinks to redirect victims to phishing pages, evading conventional safety measures. Moreover, Google Apps Script is exploited for its JavaScript-based performance, permitting attackers to embed malicious code and direct customers to misleading web sites.
Remediation
Defending oneself from phishing requires a mix of consciousness, warning, and safety practices. Listed below are some key steps to assist safeguard towards phishing:
- Be Skeptical: Train warning when receiving unsolicited emails, messages, or social media requests, particularly these with pressing or alarming content material.
- Confirm Sender Identification: Earlier than clicking on any hyperlinks or offering info, confirm the legitimacy of the sender. Test electronic mail addresses, domains, and phone particulars for any inconsistencies.
- Keep away from Clicking on Suspicious Hyperlinks: Hover over hyperlinks to preview the precise URL earlier than clicking. Be cautious of shortened URLs, and if unsure, confirm the hyperlink’s authenticity instantly with the sender or via official channels.
- Use Two-Issue Authentication (2FA): Allow 2FA each time attainable. This provides an additional layer of safety by requiring a second type of verification, corresponding to a code despatched to your cell system.
McAfee offers protection towards a broad spectrum of lively phishing campaigns, providing safety via options corresponding to real-time scanning and URL filtering. Whereas it enhances safety towards varied phishing makes an attempt, customers should stay vigilant and undertake accountable on-line practices together with utilizing McAfee.



