Wing Safety lately introduced that primary third-party threat evaluation is now obtainable as a free product. However it raises the questions of how SaaS is related to third-party threat administration (TPRM) and what corporations ought to do to make sure a correct SaaS-TPRM course of is in place. On this article we’ll share 5 tricks to handle the third-party dangers related to SaaS, however first…
What precisely is Third-Celebration Threat Administration in SaaS?
SaaS is quickly rising, providing companies comfort, swift implementations, and priceless alternatives. Nevertheless, this progress introduces a safety problem the place dangers come up from the interconnected nature of SaaS provide chains. It’s clear that earlier than onboarding a brand new contractor or vendor, we want due diligence, safety checks, and referrals. Nevertheless, we now perceive that within the SaaS area, purposes are, in reality, the go-to vendor of selection.
Let’s clarify: Any worker can very simply join SaaS distributors to firm knowledge, granting them permissions and entry. This straightforward onboarding is essential for effectivity, scalability, and getting work completed. However it additionally introduces loads of safety points as a result of most SaaS purposes, not like conventional distributors, typically bypass or skip safety or IT approval.
Third-party SaaS safety options play a pivotal position in safeguarding a corporation’s SaaS provide chain, and evaluating SaaS distributors turns into a vital factor of complete vendor threat administration. Whereas among the duty for safety falls on the SaaS vendor, organizations should keep vigilant in managing third-party dangers, no matter their measurement, to uphold a safe and sturdy enterprise atmosphere and to make sure they adjust to business requirements.
In easy phrases, Third-Celebration Threat Administration within the context of SaaS is the method of evaluating and managing the potential dangers posed by third-party distributors and repair suppliers within the SaaS area. TPRM helps safety and IT groups establish and perceive varied sorts of dangers coming by means of third-party providers that relate to cybersecurity, together with knowledge privateness vulnerabilities, compliance gaps, operational points, monetary challenges, and reputational issues.
5 TPRM suggestions to make sure SaaS Safety
1. Identification and Categorization:
Figuring out and categorizing third-party connections is a important step for organizations to know the potential threats these connections pose to safety and compliance. An absence of systematic knowledge assortment and evaluation on entry ranges and vendor safety can depart safety and IT groups at midnight, hindering their skill to evaluate and safely use particular third-party purposes appropriately.
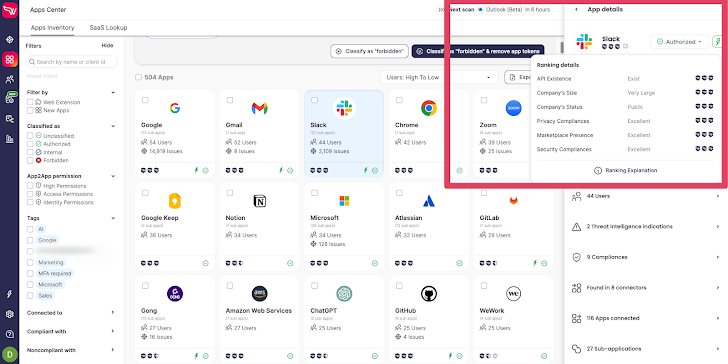
Nevertheless, with SaaS Safety Posture Administration (SSPM) know-how, organizations can overcome this problem by simply discovering all their third-party SaaS purposes. SSPM options present contextual info on the extent of entry these purposes should organizational belongings and particulars in regards to the vendor’s safety degree primarily based on steady evaluation.
 |
| Wing Safety’s TPRM answer for SaaS purposes |
2. Due Diligence and Evaluation:
Conducting due diligence earlier than onboarding purposes is an important step in making certain that dangerous purposes are usually not being launched into a corporation’s SaaS Stack. This maximizes the necessity to assess third-party safety controls, insurance policies, and procedures, making certain they meet the required requirements forward of onboarding them.
To sort out this downside, organizations ought to search for an answer that may present the vital safety and compliance info about related SaaS distributors/purposes. Info akin to safety compliances, privateness compliances, vendor measurement, location, historic menace intelligence alerts concerning breaches or safety incidents that the seller had skilled, and so on. This info is a significant a part of the due diligence technique of third-party distributors.
 |
| Wing Safety’s free discovery answer for SaaS purposes |
3. Ongoing Monitoring:
Steady monitoring is a key facet of efficient TPRM. Third-party threat Administration doesn’t cease solely on the stage of prevention but in addition stresses the significance of usually assessing third-party efficiency and safety practices to make sure ongoing compliance and safety with established requirements. This proactive strategy helps organizations keep forward of evolving dangers.
An efficient approach to cope with that is to have a safety answer that is ready to constantly monitor for updates within the distributors’ info together with modifications in safety and privateness compliances, menace intelligence alerts, and its threat posture.
4. Incident Response:
Within the occasion of a safety incident that pertains to a third-party connection, organizations ought to be sure that a strong incident response plan is in place. It begins by being able to obtain well timed menace intelligence alerts when breaches or safety incidents happen, enabling them to reply promptly and successfully.
5. Documentation and Reporting:
Sustaining detailed information of the TPRM course of is important for demonstrating compliance with safety requirements. Producing complete stories is essential as a result of it gives transparency and facilitates easy audits of the group’s threat administration efforts.
Organizations ought to go for an answer that may handle the stock of the whole organizational SaaS purposes thus far, view all of the related info that helps the TRPM course of, and export the related stories for audit functions.
Penalties of insufficient TPRM practices:
Failing to implement correct Third-Celebration Threat Administration practices can have extreme penalties for organizations. Cybersecurity breaches ensuing from vulnerabilities launched by third-party distributors can result in the publicity of delicate knowledge, monetary theft, and reputational injury. Non-compliance with knowledge privateness rules can entice hefty fines and authorized liabilities.
What’s to realize from TPRM?
Efficient TPRM practices provide quite a few advantages. It empowers safety groups to establish and deal with potential dangers, resulting in improved safety and compliance. Strengthened vendor relationships improve belief and collaboration, whereas the power to show correct due diligence helps navigate regulatory necessities extra successfully.
Finally, Third-Celebration Threat Administration is an important course of that includes figuring out and mitigating potential vulnerabilities launched by third-party distributors. TPRM performs an important position in strengthening a corporation’s total safety posture by making certain adherence to regulatory compliance and finest safety practices all through the whole SaaS provide chain.
This proactive strategy is important for securing organizations in opposition to SaaS threats, because it includes evaluating the cybersecurity practices of third-party distributors to establish potential vulnerabilities and dangers within the provide chain. These assessments facilitate knowledgeable decision-making and threat mitigation and guarantee alignment with the group’s safety requirements, finally fortifying the general safety defenses.
That mentioned, at present, vendor threat assessments are important however not sufficient. It is important to have each the capabilities to evaluate and mitigate threat. By beginning with thorough third-party threat assessments, corporations can achieve the mandatory insights to take the following steps in proactively addressing dangers and making certain a safe and well-protected SaaS provide chain.



