Hunters researchers famous the vulnerability may result in privilege escalation. Google mentioned the report “doesn’t determine an underlying safety situation in our merchandise.”
Cybersecurity researchers from the agency Hunters found a vulnerability in Google Workspace that might enable undesirable entry to Workspace APIs. The flaw is critical in that it may let attackers use privilege escalation to realize entry that might in any other case solely be out there to customers with Tremendous Admin entry. Hunters named this safety flaw DeleFriend.
Soar to:
Vulnerability uncovered in Google’s domain-wide delegation
Based on the Hunters staff, the vulnerability is predicated on Google Workspace’s function in managing person identities throughout Google Cloud providers. Area-wide delegation connects id objects from both Google Workspace Market or a Google Cloud Platform Service Account to Workspace.
Area-wide delegation can be utilized by attackers in two principal methods: to create a brand new delegation after having gained entry to a Tremendous Admin privilege on the goal Workspace setting via one other assault, or to “enumerate profitable mixtures of service account keys and OAuth scopes,” Hunters mentioned. This second approach is the novel methodology the researchers have found. Yonatan Khanashvilli, risk looking skilled at Group Axon at Hunters, posted a way more detailed clarification of DeleFriend.
Response from Google
Hunters disclosed this flaw to Google in August 2023 and wrote, “Google is at present reviewing the difficulty with their Product staff to evaluate potential actions primarily based on our suggestions.”
An nameless Google consultant advised The Hacker Information in November 2023, “This report doesn’t determine an underlying safety situation in our merchandise. As a greatest observe, we encourage customers to verify all accounts have the least quantity of privilege doable (see steering right here). Doing so is essential to combating most of these assaults.”
Why this Google Workspace vulnerability is especially harmful
Hunters mentioned this vulnerability is especially harmful as a result of it’s long-term (GCP Service account keys would not have expiry dates by default), simple to cover and laborious to detect. As soon as inside an account with Tremendous Admin privileges, attackers may doubtlessly view emails in Gmail, view somebody’s schedule in Google Calendar or exfiltrate information from Google Drive.
“The potential penalties of malicious actors misusing domain-wide delegation are extreme. As a substitute of affecting only a single id, as with particular person OAuth consent, exploiting DWD with present delegation can influence each id throughout the Workspace area,” mentioned Khanashvili within the press launch.
SEE: Overworked IT professionals in Australian small companies have a number of choices for coping with cyber safety. (TechRepublic)
Easy methods to detect and defend towards DeleFriend
Along with making certain privileges are arrange correctly, as Google notes, IT admins may create every service account in a separate mission if doable, Hunters mentioned. Different suggestions from Hunters to guard towards DeleFriend exploitation are:
- Restrict OAuth scopes in delegations as a lot as doable, utilizing the precept of least privilege.
- Keep away from administrative scopes resembling https://www.googleapis.com/auth/admin.
- Focus detection engineering and risk looking practices on suspicious delegations and a number of personal key creations over a brief period of time.
- Preserve safety posture and hygiene greatest practices.
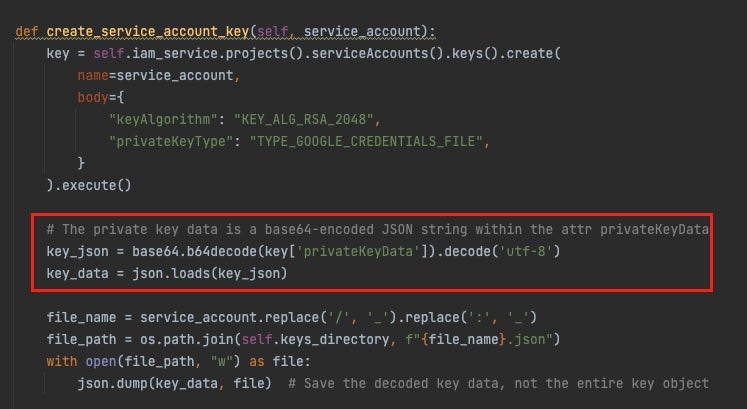
Hunters created a proof-of-concept instrument for working the DeleFriend exploitation methodology manually. The instrument works by enumerating GCP Initiatives utilizing the Useful resource Supervisor API, iterating and enumerating on GCP Service account sources and mission sources, and investigating particular roles and permissions from there, together with extracting personal key worth from a privateKeyData attribute key (Determine A). The top result’s a JWT object, which could be exchanged with a brief entry token to permit entry to Google APIs. Konanshvili’s weblog publish comprises extra element.
Determine A
The instrument is meant for researchers so as to detect misconfigurations, and “enhance consciousness round OAuth delegation assaults in GCP and Google Workspace and to enhance the safety posture of organizations that use the Area-Huge-Delegation function,” Hunters wrote.
Word: TechRepublic reached out to Google for extra info.


